The focus on augmented reality over at Apple is, so far, restricted to the iPhone and the iPad. But if some of the most reliable analysts in the business are to be believed, we'll probably see some kind of AR or VR wearable from the company later this year.

Electronic warfare tactics work by jamming, disrupting, or disabling the technology a target uses to perform a critical function, and IoT devices are especially vulnerable to attacks. Wireless security cameras like the Nest Cam are frequently used to secure critical locations, but a hacker can surgically disable a webcam or other Wi-Fi connected device without disturbing the rest of the network.

It seems like every day now that we see a new headline on a cyber security breach. These headlines usually involve millions of records being stolen from some large financial institution or retailer. What doesn't reach the headlines are the many individual breaches that happen millions of times a day, all over the world.

Foodies and big-time chefs like Thomas Keller go crazy for fleur de sel. This finishing salt appears in fancy eateries and cookbooks the world over, and in the early 2000s, it was not uncommon to see diners in a high-end restaurant sprinkle a pinch of fleur de sel on their plates from their own personal stash.

Many of my aspiring hackers have written to me asking the same thing. "What skills do I need to be a good hacker?"
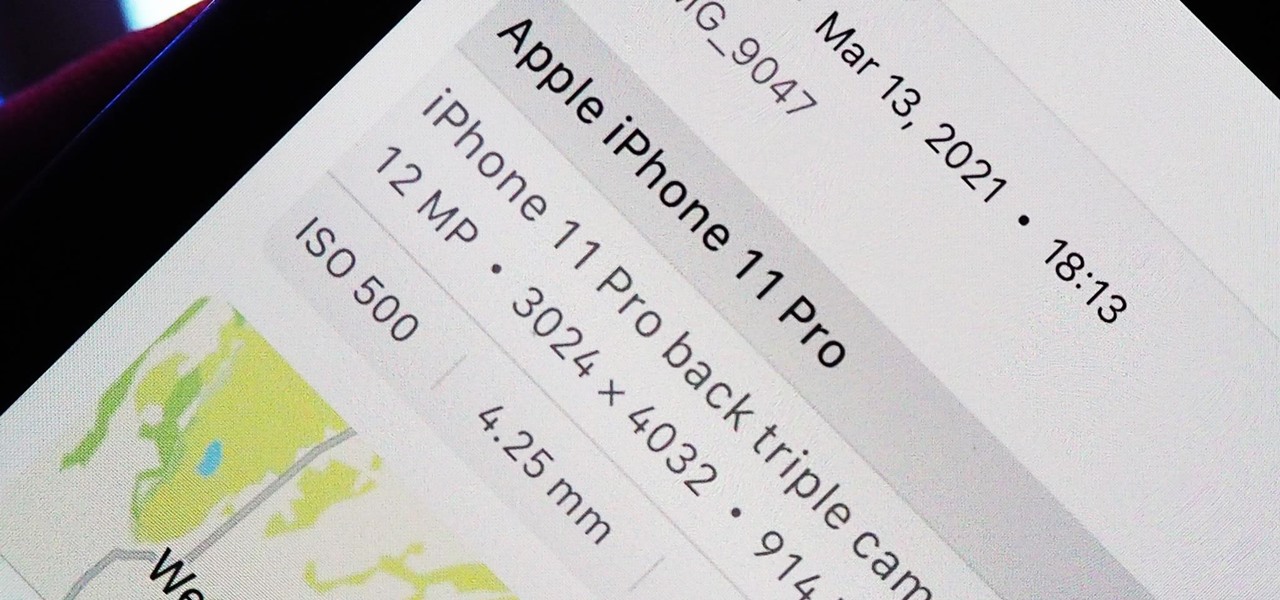
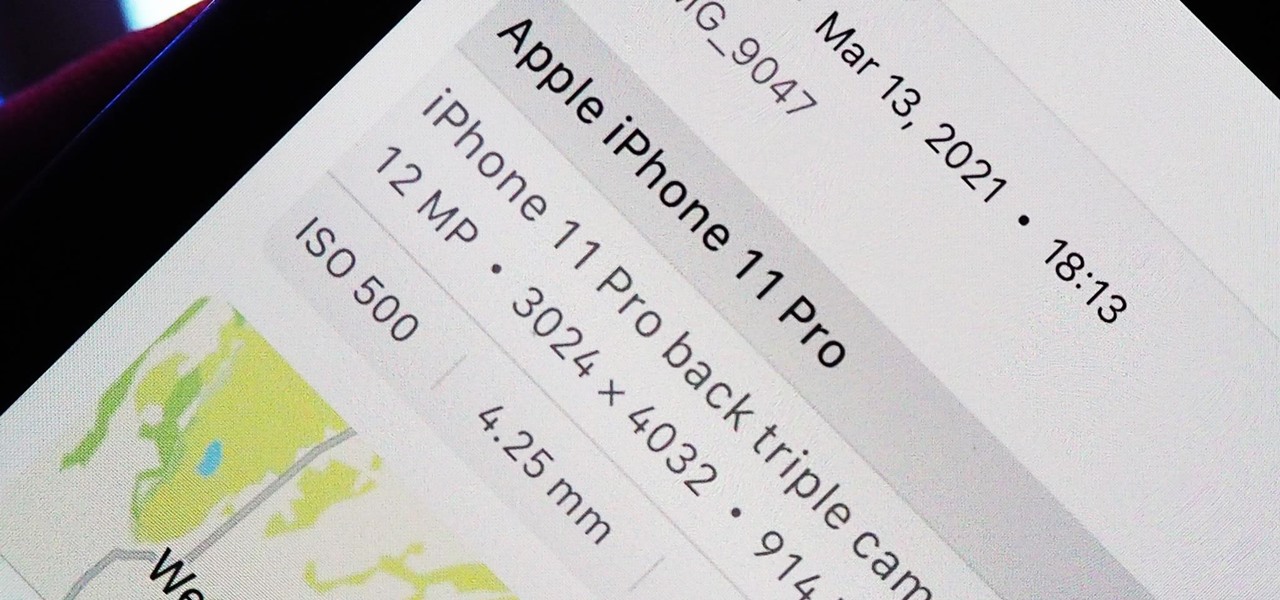
Apple introduces several new privacy settings with iOS 15, including the ability to better manage the metadata in your photos. With just a few taps, you can effectively spoof a photo's geolocation and change its creation date and time, providing a sort of disguise over your personal information. If you constantly take and share photos, it's a welcomed feature, but its results are not permanent and can be reversed.

Mystery is a tricky thing. Used correctly, it can give onlookers the impression that wondrous and perhaps valuable things are afoot. However, once the veil of suspension of disbelief is removed in any significant way, that same mystery can quickly turn into not just skepticism, but outright anger at what may have seemed like an attempt to dupe trusting onlookers.

Armis Labs has revealed eight vulnerabilities, called "BlueBorne", which put 5.3 billion Android, iOS, Windows, and Linux devices that use Bluetooth at risk. With it, hackers can control devices, access data, and spread malware to other vulnerable devices through networks. In this post, we will learn about the vulnerabilities, then look at how to find devices that have them.

Making a good pie crust can seem intimidating to the uninitiated, but once you master this skill, a whole world opens up to you. Not only can you make all manner of fruit, custard, and cream-filled pies once you know all the tricks, you can branch out into the world of quiches, savory pies, and flaky, crispy turnovers, too. We've already told you how to get perfect, firm fruit pie fillings, so now, let's learn about crust.

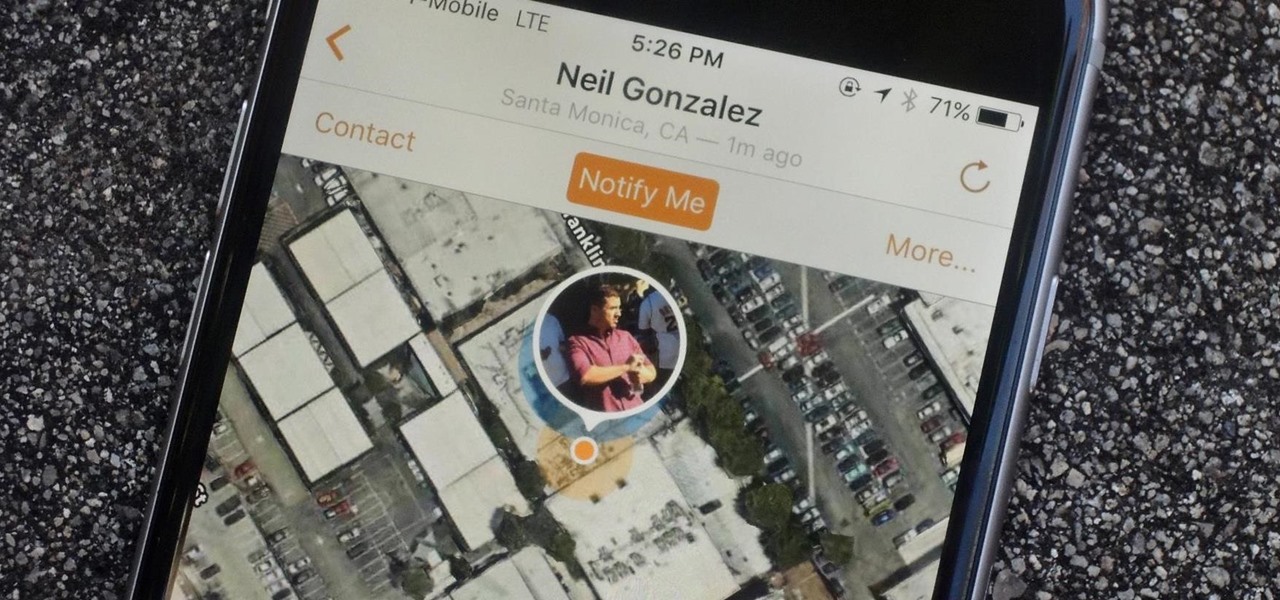
Apple designed Find My Friends in 2012 as a means for better-connecting with friends and family. It's pretty useful for scenarios when you need to keep tabs at an amusement park or to get a live ETA when your buddy is coming to pick you up from the airport. You can even share your location with others so they can track your whereabouts as you go about your day.

There are countless tutorials online that show how to use Netstat and Tasklist to find an intruder on your computer. But with a few PowerShell functions, it's possible for a hacker to evade detection from the almighty command line.

Rich Dad, Poor Dad author presents commentary on how money can manipulate or be manipulated. Make money work for you.

Do you perform magic or stand-up comedy routines and often find yourself talking to yourself on stage? Do you envy Jeff Dunham and his elaborate selection of puppets that he can interact with onstage in order to have a conversation with himself without sounds TOO deranged? This video is here to help. It teaches you how to make a simple paper puppet out of only a piece of paper, scissors, and a pen who's face can be manipulated to make it looks like it's talking. Kind of. Talk to the hand!

Looking for another Angry Birds fix? Well, drop the lame birds and pick up the zombies—Stupid Zombies, that is. You'd think that killing "stupid" undead beings would be easier than knocking off a few "angry" vertebrates, but it's actually more challenging—and more fun! Who wouldn't enjoy killing zombies with a shotgun blast and watching their heads roll? Armed with a shotgun and a strategic mind, your goal is to take out all the living dead with as few bullets as possible, trying to achieve t...

Check out this educational science video tutorial to learn the steps to properly culture myeloid dendritic cells from bone marrow precursors.

Manipulated with Big Lens for iPhone, which I ultimately like the best out of all the apps reviewed here.

One of the appealing things about PMC is the way it can be manipulated like clay, but for some of us, the real fun is carving the PMC after it is dry. This short video demonstrates how to form a ring blank then carve it with files, just as we would carve wax. In this case, though, there are no sprues, no investing, and no casting. Carve dry precious metal clay.

This Null Byte is the first part in a mini-series on the art of Social Engineering. I will be teaching you how to effectively defend yourself against it.

The footage you're about to watch may look CG, and while it is indeed animated, the 5,600 frames used to composite this fly by glimpse of Saturn aren't fabricated—they are real hi-res photographs taken by the Cassini orbiter. Outside In—an "IMAX in a basement"—is a DIY not-for-profit IMAX project-in-progress by filmmaker Stephen Van Vuuren.
3,000 soldiers to serve in Africa next year A brigade will deploy to Africa next year in a pilot program that assigns brigades on a rotational basis to regions around the globe, the Army announced in May.

When the much buzzed Facebook profile page redesign was released back in December, French artist and co-director of ad agency La Bande Originale Alexandre Oudin came up with an innovative way to maximize the visual possibilities of the page. His clever "hack" created a ripple effect of copycats across the web.

IMAGINE you are an experienced martial arts referee. You are asked to score a number of taekwondo bouts, shown to you on video. In each bout, one combatant is wearing red, the other blue. Would clothing colour make any difference to your impartial, expert judgement? Of course it wouldn’t.

Type: All photography styles and themes Theme: Open to traditional, contemporary, alternative process, digital, mix processes, manipulated and experimental works

This is it! That last basic mission. Last Friday's mission was to accomplish solving HackThisSite, basic mission 11. This final mission in the basic series was made to give us the skills and a place to apply our Apache server knowledge. This will teach us how to traverse through awkward and custom directory structures.

The already robust and ingenious Nmap tool has received a whole slew of new scanning scripts that can be used to do all sorts of naughty endeavors. Notably, the SQLi module, since it is a necessary evil that we must cover here at Null Byte. This major update is going to fuel today's lesson.

JavaScript is the language of the internet. It is what allows us to create dynamic, interesting webpages that are fast, web-based applications and so much more. The primary use of JavaScript is to write functions that are embedded in or included from HTML pages and that interact with the Document Object Model (DOM) of the page. This is the magic that allows all of what we see to happen, and for our browser to be manipulated.

David Talley, a 19-year-old fine art photographer, has been widely praised for his surreal self-portraits. Many of them take hours to set up and shoot, and even more time to post-process through Photoshop or any other photo editing program.

Lost the product key for your game? If you have to reinstall the game and don't have that key anymore, you're out of luck, especially if you didn't "buy" the game. But never be in fear of losing product keys again with today's Null Byte, where we'll be practicing a little bit of mind-kung fu.

If you've ever wondered how software pirates can take software and crack it time and time again, even with security in place, this small series is for you. Even with today's most advanced methods of defeating piracy in place, it is still relatively easy to crack almost any program in the world. This is mainly due to computer processes' ability to be completely manipulated by an assembly debugger. Using this, you can completely bypass the registration process by making it skip the application'...

Cross-Site Request Forgery (CSRF, pronounce "sea-surf") is a common web exploit. However, for unknown reasons it's not used very often. It plays on a given website's trust in a web browser by executing another website's form action, for example, sending money to another person. It's usually placed in abnormal places like HTML image tags.

JavaScript is one of the main programming languages that the Web is built on. It talks directly to your browser and exchanges information with it in ways that HTML simply cannot. With JavaScript, you are able to access browser cookies, website preferences, real-time actions, slideshows, popup dialogs and calculators, or you create entire web-based apps. The list goes on nearly forever.

Simple as the title, someone will particpate as a crash test dummy. The funny part of course the prank is the "particpate" will not know he is a crash test dummy. Its kinda like the prank that was pulled on Ryan Dunn in the addtional footage in the DVD of Jackass Number Two where an airbag was suppose to go off in his face. Well i hust thought of the same concept but add a 30 or if you want to go crazy, 40 mph crash into wall or whatever it may be. You would tell the person being pranked that...

Take the best RPG of all time. Combine with the only instrument with invisible strings. And you have pure elf-worthy magic!

Founded by Zach Kaplan, a "serial entrepreneur" with a B.S. in mechanical engineering, Inventables is a futuristic online hardware store based out of Chicago. The company sells innovative materials at much smaller quantities than typically available—largely to artists, inventors, developers, and researchers. If you've got a brilliant idea and cash to spare, careful, you just may go hog wild. My premature "Dear Santa" wishlist-in-progress:

By Ethical Traveler As the world becomes ever more interconnected, being an ethical traveler becomes both easier and more urgent. Travelers today have access to far more information than we did even 10 years ago. We can observe–almost in real time–the impact that smart or selfish choices, by governments and individuals, have on rainforests and reefs, cultures and communities.

Find two people that dislike each other the most (inevitably someone and Brandon Novak). These will need to be two people that are likely to drink enough to be manipulated without their knowledge. While sleeping, superglue one part of one to the other. It can be a hand to a bare ass, a cheek to a bare ass, lips to cheek (make sure they can breathe!), etc. Or, superglue someone to themselves, in an awkward position (hand down the pants, one lip glued upwards in a permanent “Elvis,” etc). An in...