In this video, we learn how to use your Mac as a wireless adapter for Xbox Live. You will need: a Mac, monitor, Xbox, and Ethernet cord. Start out by going to system preferences, then going to the sharing folder. Go to internet sharing and make sure the Ethernet box and internet is selected. Then, click the box next to internet sharing and click "start". Now, go to the network option and go to advanced, TCIP, and then write down your sub maps and router IP address. After this, plug the Ethern...

Welcome back, my hacker novitiates! Many of you have probably heard of a man-in-the-middle attack and wondered how difficult an attack like that would be. For those of you who've never heard of one, it's simply where we, the hacker, place ourselves between the victim and the server and send and receive all the communication between the two.

In this video from AppleGenius0921 we learn how to enable a Live/Hotmail account on the Mail application on a Mac. Open Mail. In full name put your full name. Type in your email address and password and continue. Leave the account type on POP and name the description what you'd like. The incoming mail server is pop3.live.com. Type in your live.come username with @live.com in it! Click Continue. The outgoing mail server should be smtp.live.com. Check use only this server and check use authenti...

In this video we learn how to crack WPA using Back Track. The first step is the boot into Back Track using a VMware Virtual Machine Image. Next you need to open a shell console. In the console you will type "airmon-ng" and press enter. This does a check to find the wireless guard interface name. Next, type "airodump-ng wlan0" and press enter. This will tell it what wireless card to use and scan for wireless networks. You are looking for the one that comes up WPA. Copy the MAC address then typ...

In this video tutorial, viewers learn how to automate tasks in a Mac OS X computer. This video will show viewers how to create a simple application, that when double-clicked, will open a new message that's already addressed to a specific person. Begin by clicking on the Macintosh HD and click on Applications. Open Automator. Users will be able to create a template for different work flows. Select Application and click Choose. On the left side of the window, there will be a list programs that ...

In order to transfer files from your iPhone to your mac or pc, you're going to need a little something from www.digidna.net. Open up your web browser and type that into the address bar, here look for DiskAid. Download the version of DiskAid that corresponds to what you want, whether it be for a PC or a Mac. When you've downloaded it, it is time to install it. Once the program is up and running you'll be able to transfer different files like photos and videos from your iPhone or if you wish yo...

You may not know it, but the IPv4 address of your computer contains tons of useful information about whatever Wi-Fi network you're on. By knowing what your IPv4 address and subnet mask are telling you, you can easily scan the whole network range, locate the router, and discover other devices on the same network.

Man-in-the-Middle attacks can prove to be very useful, they allow us to do many things, such as monitoring, injection, and recon.

In this tutorial, you'll learn about the new features made available in version 5 of the Safari web browser — including address bar enhancements, Safari Reader, Bing search, performance enhancements and extensions. For more information, and to get started taking advantage of these new features yourself, watch this Mac lover's guide.

It's no secret that devices leak data, but sometimes they do so in ways you may not expect. Your phone, laptop, printer, and IOT devices leak Wi-Fi information that can (and is) used to track you.

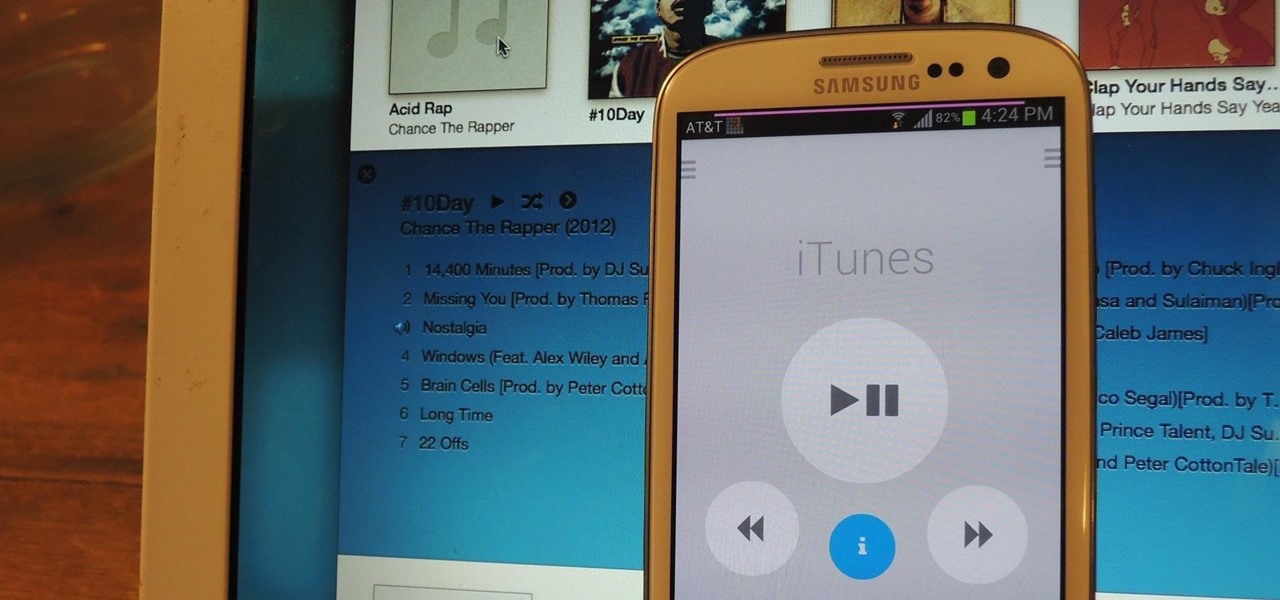
I still remember when I had to get up from my comfy spot on the couch to change the channel on my old television. So for me, the remote control may be one of the most underrated inventions of the last century. These days, remotes take on all sorts of shapes, not just the typical brick, but also in the form of watches and cell phones.

Tired of Windows and Mac OS? You might want to try Ubuntu or some other variation of the Linux operating system. The Lab Rats, Andy Walker and Sean Carruthers, teach you how to install and run Ubuntu on your system. They also address several concerns you may want to be aware of.

iPhoneElite8 teaches viewers how to easily SSH into their iPhone or iPod Touch using Cyberduck! First, open Safari, Google 'Cyberduck Space Mac". Click the very first link you get and download Cyberduck on the right. Now open Cyberduck on your computer. Get your iPhone of iPod Touch and open up settings. Under settings, connect to Wi-Fi, and copy down your IP address that shows. Go back to Cyberduck, go to open connection and click on 'protocol'. Open up SFTP and copy the IOP address you got ...

Android has released a new application called ezNetScan, which is a free app that scans the wireless network you're connected to and gives you a full log of all of the devices connected to that network. This isn't new for smartphone users, let alone Android users. Fing has been around for a while and does practically the same thing that exNetScan does. It gathers information such as the IP and MAC addresses, device vendors, and ISP location. But while Fing is a great program, it does lack a f...

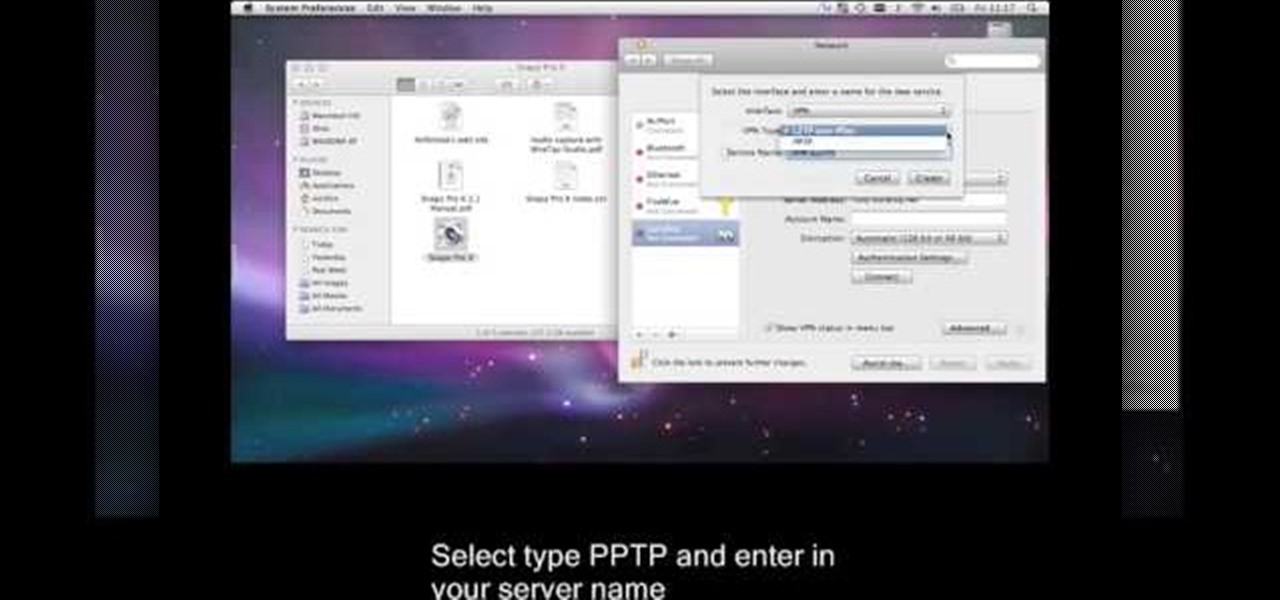
This is a video tutorial that is showing its audience how to set up your own VPN client on your Mac computer. The first step in setting up a VPN client is to go to your system preferences on your computer. Next select network and then select the plus button and type in that you will be making a VPN network. Next you should select the type PPTP and enter your server name. Then you can click on create and it will create a new network for you. Next you should enter your service address and your ...

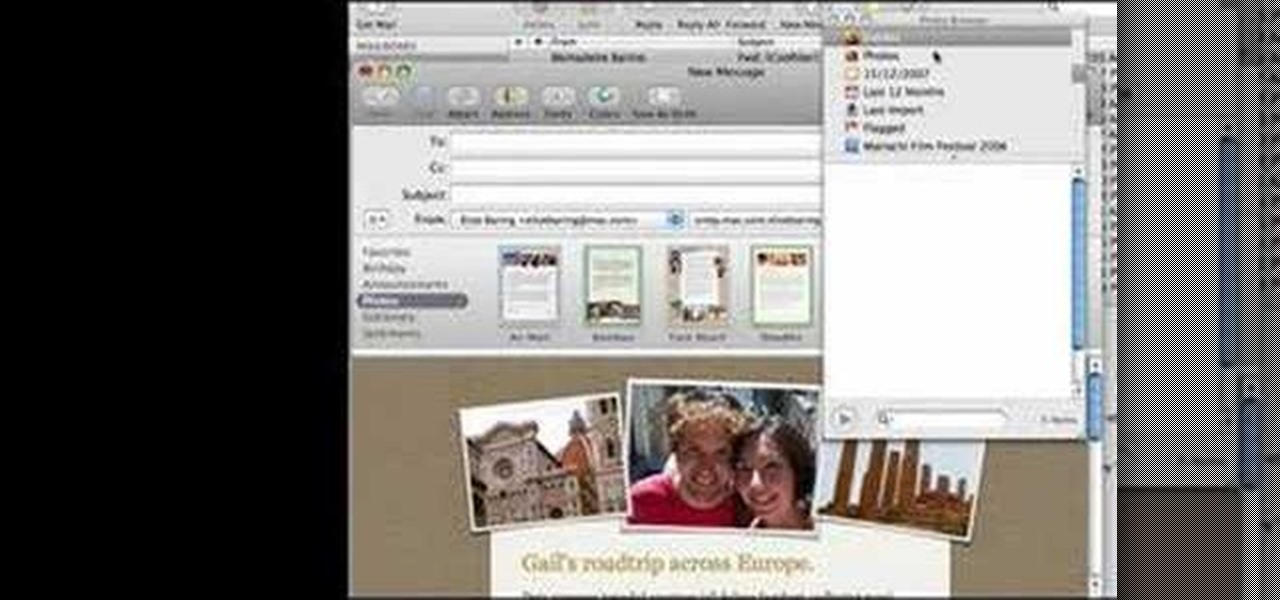
How to make artistic emails using Mac.First open up email then click on new message, then on top right hand corner we can see ‘Show stationary’ button. Click it to see the templates made by apple. He selects the template of vacation to make up an email about his trip to Sydney. Then the template of vacation to Europe appears with photos. He clicks on the photo browser and opens his trip to Sydney folder by double clicking and dragging the required photo to set the photo for the photo in the t...

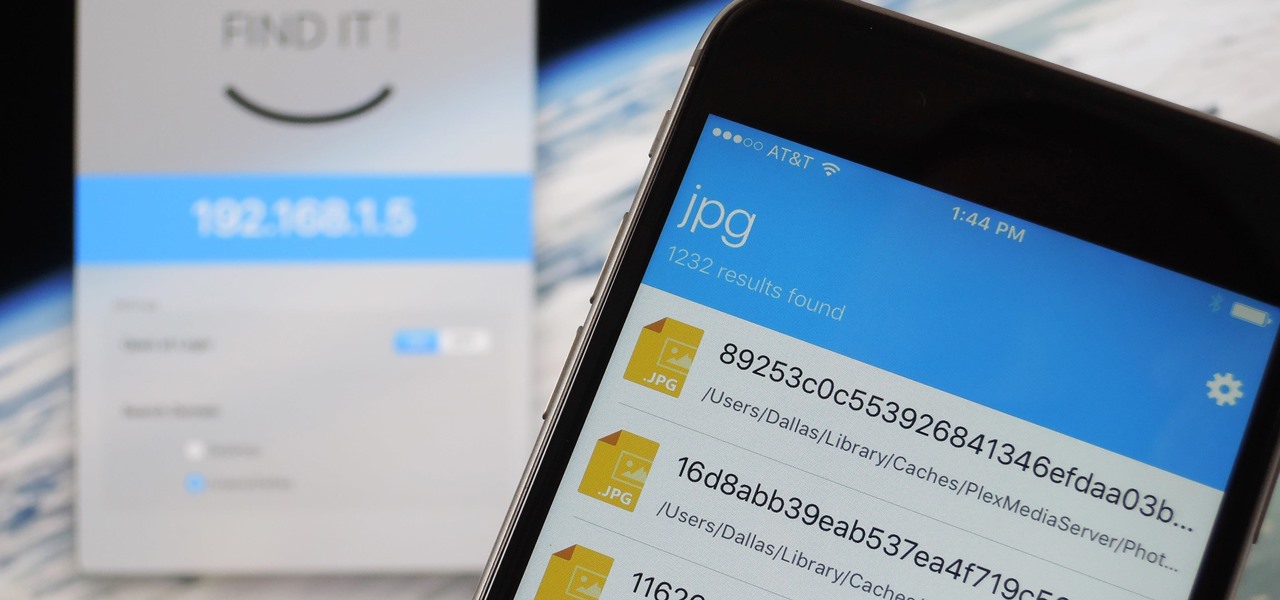
When it comes to sharing files between a smartphone and a computer, there are several solutions available for a Windows and Android pairing. But for those of us with Apple devices, the selection of apps in this category isn't quite as great. You can use AirDrop to quickly share files, but searching for files is not so easy.

Welcome back, my nascent hackers! In previous tutorials for my Wi-Fi Hacking series, I have shown you how to crack WEP and WPA2 passwords, break a WPS PIN, and create Evil Twin and Rogue access points. In this continuation of the series, let's look at slightly different approach to attacking wireless.

You need a good microphone on your computer in order to make audio recordings, voice chat, or use speech recognition. However, not every computer comes with a built-in mic, and not every built-in mic works great.

Welcome back, my novice hackers! Episode 6 of Mr. Robot has come and gone and, as usual, it did not disappoint. Once again, our hero, Elliot, has used his extraordinary intellect and hacking skills to awe and inspire us.

Pretty soon, every restaurant and store you walk into will know exactly what you're doing. Retail analytics companies like Euclid, ShopperTrak, RetailNext, and Prism Skylabs have penetrated hundreds of food shops and retail stores across the country, installing sensors that track and log customers' moves while they dine and shop.

There are hundreds of keyboard shortcuts out there, but these 7 are the ones you'll definitely want to remember. I use them every day, and you should too. Step 1: Tab Domination

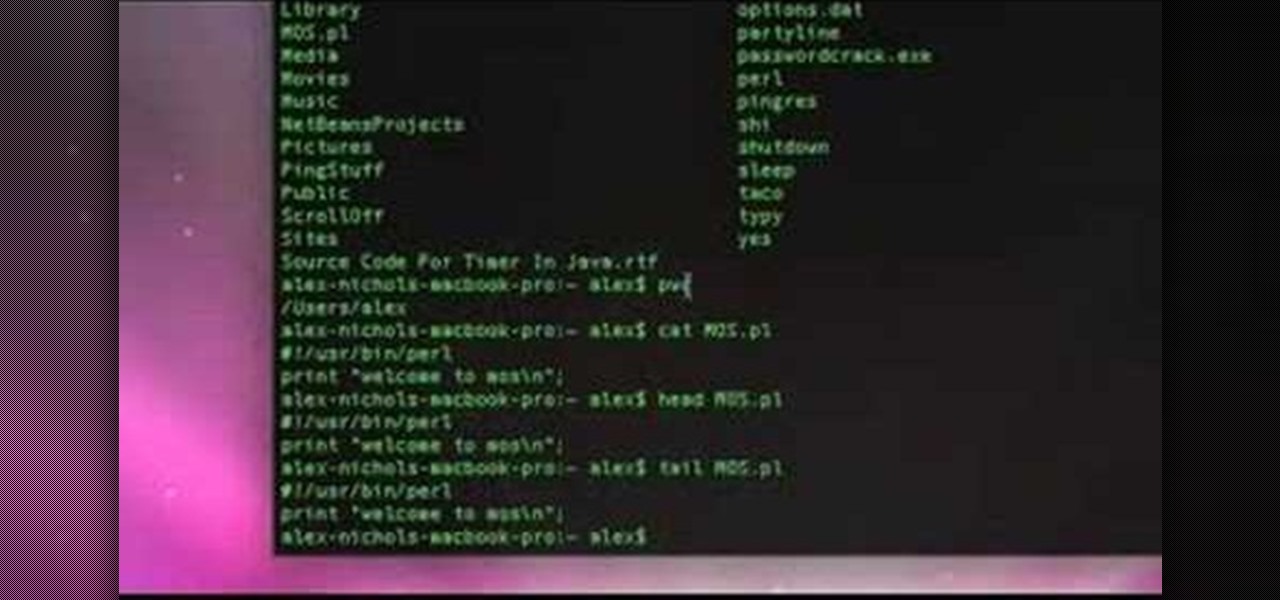
Every Apple computer running Mac OS X comes with a handy application called Terminal… MacBooks, MacBook Pros, Mac Pros, iMacs, etc. They all have Apple Terminal, and it can be found in your Utilities folder in Applications. Which means you can use it.

In her music video for "Not Myself Tonight," Christina Aguilera engages in some, er, racy antics, such as humping a guy with minimal clothing and practicing bondage/bdsm. All in a day's work for shock queen Aguilera, right?

This beauty video demonstrates how to do a MAC brunette blonde redhead makeup look.

This beauty video demonstrates how to do a MAC danger zone makeup look: red and black .

A flaw in WPS, or WiFi Protected Setup, known about for over a year by TNS, was finally exploited with proof of concept code. Both TNS, the discoverers of the exploit and Stefan at .braindump have created their respective "reaver" and "wpscrack" programs to exploit the WPS vulnerability. From this exploit, the WPA password can be recovered almost instantly in plain-text once the attack on the access point WPS is initiated, which normally takes 2-10 hours (depending on which program you use).

In order to set up a secure wireless router, you will need to use the security that is available with your wireless routing. You will need to change the default ID names and password on your computer. Try to make sure that your passwords are difficult. Also, turn on the encryption: e.g. WEP.

On your iPhone, your phone number and Apple ID email address are the default ways in which somebody can contact you on FaceTime. While you can't remove your phone number as an option, you can withdraw your Apple ID email account. More importantly, you can add any other email addresses you'd like to the list, so you never have to worry about a friend, family member, or coworker not being able to audio or video chat with you.

Welcome back my networking geeks. In this part we are going to keep discussing about IP Addressing and I hope after you finish reading it you will become an IP wizzard.

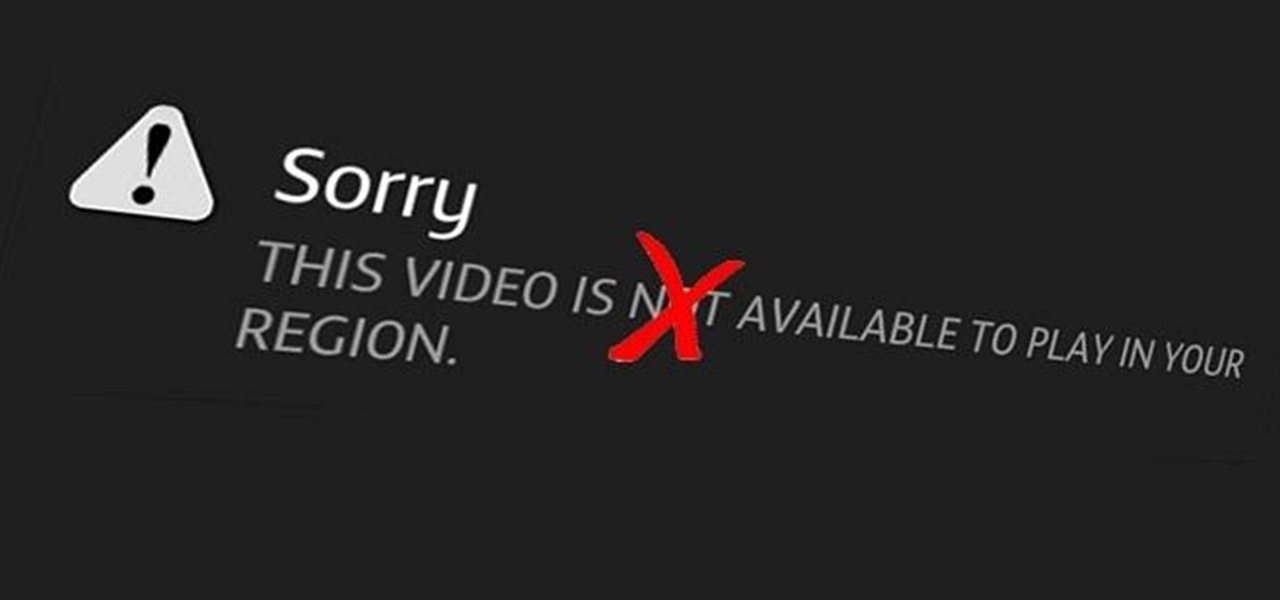
For people that live outside of the United States, how many times has this happened when surfing through U.S. streaming services? If you're outside of the U.S. market and want to stream stateside services like Hulu, MTV, CBS, Pandora, and others—you're in luck. Tunlr is an application that re-addresses certain data envelopes, tricking the receiver into thinking the data originated from within the U.S. by using its own DNS server's IP address. You can even watch some non-US shows stateside, li...

More than her bootylicious derriere, Kim Kardashian is famous for her luminous, bronzy skin that smiles for the cameras and is the perfect accessory for any outfit.

Need to fix your Power Mac? Disassembling the Power Mac could be tricky, but not now. See how to remove the side case and fan from the G5 Power Mac desktop computer.

Lauren, AKA QueenofBlendingMUA has joined the ranks with the other YouTube makeup gurus. Lauren is a makeup artist with a large collection of eye makeup video tutorials. Her eye makeup look span from everyday makeup to creative, more expressive party looks. Check out this makeup tutorial video to learn how to create a shimmery turquoise blue eye makeup look. Search QueenofBlendingMUA on WonderHowTo for more beauty videos.

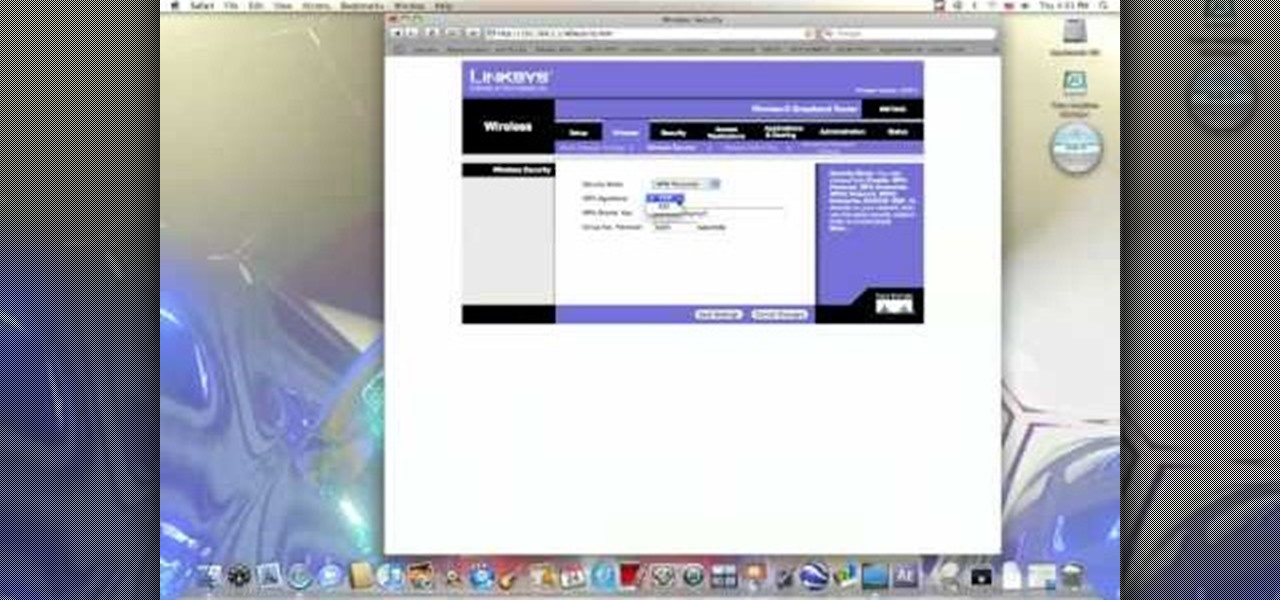
In this video from benjamoon we learn how to secure a linksys wifi network from a Mac. First type in your IP address in your browser bar which is 192.168.1.1 then press enter. If it asks for a password it is admin. Click on Wireless and here you can edit your name and who can access your wifi network. Under wireless security, go to WPA personal from the drop down menu. When you make your password, make it very challenging. He recommends just banging your hand against the keyboard, as long as ...

Welcome back, everyone. In the previous part of this rapid-fire miniseries, we built the victim portion of the shell. Today, we'll be building the attacker portion. This script will initialize interaction with the victim portion of the shell, send commands, and receive the output.

Want to scare the living daylights out of all your friends and family this Halloween? Then dress up like a clown or a doll. Either one will do. Watch this makeup tutorial to learn how to get a "sexy" doll/clown look that's reminiscent of those creepy dool eyes crafted so exquisitely they make the doll almost look...alive (cue spooky music).

Learn the important steps necessary for the best printing experience when printing to the Epson 3800. This tutorial is specifically designed to address some of the issues with the Epson 3800 and the MAC OS X Leopard operating system. Here is a detailed explanation of the changes that were made to the 10.0.1 update to Adobe Photoshop CS3. Remember, having all the current versions of Adobe Photoshop, and the Epson drivers is critical to success when printing.

There's a reason witches are a timeless costume costume choice worn year after year on Halloween. They're sexier than fairy costumes and far more lurid than ketchup bottle costumes.