
How To: Build your self confidence
No matter who you are, a little self-confidence can go a long way toward making your dreams come true.


No matter who you are, a little self-confidence can go a long way toward making your dreams come true.

It's not uncommon for hackers to attempt to move laterally between devices in proximity of a compromised device to maintain a prolonged presence in the network. Malware utilizing USB flash sticks to self-replicate and compromise air-gapped machines isn't a new concept.

With just one line of Ruby code embedded into a fake PDF, a hacker can remotely control any Mac computer from anywhere in the world. Creating the command is the easy part, but getting the target to open the code is where a hacker will need to get creative.

DJ applications aren't anything new, but recently, algoriddim GmbH has teamed up with Spotify to open the floodgates for DJs—amateurs and pros alike. The partnership will bring Spotify's 20 million+ tracks to your fingertips while mixing, and also help introduce you and your listeners to new music.

If you're a musician, Google wants you on Google+ Hangouts. In an effort to make it easier to stream your concerts, performances, and impromptu jam sessions, they've revealed their latest feature: Studio Mode. Enabling the new Studio Mode optimizes your Hangouts On Air for music, and the quality difference is massive.

Welcome back, my rookie hackers! Many newbie hackers focus upon the technical aspects of hacking and fail to give enough attention to social engineering. In fact, I would say that technical hacks should ONLY be attempted if social engineering attacks fail. Why bother spending hours or days trying to hack a password if someone will simply give it to you?

Welcome back, my hacker wannabees! Most of my recent posts have addressed using Metasploit’s Meterpreter and what we can do once we have embedded it on the victim’s system. This includes remotely installing a keylogger, enabling the webcam, enabling the microphone and recording, disabling the antivirus software, among many other things. The list is almost unlimited.

In my last hack blog on crashing your roommates Win7 system, we started looking at client- side attacks. As promised, we will be looking at some more client-side attacks.

Backdooring a powered-off MacBook is easy when a few minutes of physical access is allowed. That attack works well if the hacker also shares a Wi-Fi network with the victim, but this time, I'll show how to remotely establish a connection to the backdoored MacBook as it moves between different Wi-Fi networks.

Hello everyone Today I will show a different way to exploit a windows machine with a reverse https payload..."wait...why https? Isn't tcp good anymore?"

Hello My Fellow Hackerzz.. This is my first How-to and i'll be updating the “Hacking Android Using Kali” to msfvenom and some FAQ about known problems from comments. So Here we GO!!

One of the more talked-about features of Android Lollipop is a new Priority Mode that allows you to mute all notifications except for those coming from starred contacts. As simple as that sounds, this can still be a bit confusing—or at least lead to some unwanted interruptions.
Welcome back my social engineers/hackarians! Today we'll be looking into a fantastic piece of software, The Social-Engineer Toolkit or just SET for short. SET is designed, Developed and used by several Social-engineers. So... Let's get started!

Complete silence or a non-stop Pandora playlist? People are often divided on what type of work environment they prefer. Whether you're a frequent loud music listener or you can't stand any kind of background noise, chances are you're pretty set in your ways.

Unless you're someone who's terrified of social situations, chances are you love to talk. But no matter how much you want to share you life story or take over the conversation, you shouldn't. Your socially awkward coworkers that keep their mouth shut might actually have a leg up on you at work, and here's why.

In this video tutorial, viewers learn how to get the attention of women. Before approaching the woman, walk by her and have a feel and sense of what she's really like. She may look beautiful, but she may also not be your type. Objectify and thinking about the woman is not going to help you to approach the woman. To get a woman's attention, always smile and be full of life. Appreciate your life and don't be afraid or nervous. This video will benefit those viewers who are single and are looking...

The presenter, Ms. Jennifer explains how compound words are formed from phrasal verbs. With examples she explains how the meaning and pronunciation differs when compound words are formed from phrasal verbs. She explains the difference between 'show' and 'show off' by showing her collection of fans, and showing off with one of her beautiful fan from Japan. Then she explains the difference between 'show off' and 'show-off', giving examples and makes the listeners clear about compound nouns also...

Systm is the Do It Yourself show designed for the common geek who wants to quickly and easily learn how to dive into the latest and hottest tech projects. We will help you avoid pitfalls and get your project up and running fast. Search Systm on WonderHowTo for more DIY episodes from this Revision3 show.

In The Netherlands, Gabber Hardcore is the music of choice for rebellious young people, much like punk and underground hip-hop in the US. It is a blisteringly fast style of electronic music which might seem hard to dance to at first. Enter the hakken, the dance of choice for the Gabber listener. Watch this video to learn how to do the hakken, and you will know what to do next time you're at a hardcore club in Holland.

Popping a shell is often the main goal of a hacker, and it can be exciting when executed properly, but sometimes they do have their limitations. Metasploit's Meterpreter probably needs no introduction, but this powerful, dynamic payload can offer a leg up over normal shells. To prove it, we'll show how to take a normal command shell and elevate it to a Meterpreter session.

Welcome back, my hacker novitiates! There are many ways to hack databases, and most of these techniques require SQL injection (SQLi), which is a way of sending SQL commands back to the database from a web form or other input. In this tutorial, we will use SQL injection to get access to the underlying server. So instead of getting access to the database and its data, we will use the database as an intermediary to gain access to the underlying server.

Welcome back , my fledgling hackers! Lately, I've been focusing more on client-side hacks. While web servers, database servers, and file servers have garnered increased protection, the client-side remains extremely vulnerable, and there is much to teach. This time, we'll look at inserting a listener (rootkit) inside a PDF file, exploiting a vulnerability in Adobe's Reader.

Looking for an easy way to tell if someone's just not that into you romantically? In this clip, you'll learn how to tell whether someone dislikes you by paying attention to his or her body language. Get a grasp on basic body language with this free video tutorial from body-language expert Lillian Glass. For more information, including detailed, step-by-step instructions on what to look out for, take a look.

So many cooking shows focus on how to perfect food - preparation, cooking, and presentation. But often, so much attention and focus goes into the food itself that the utensils which produce the food, like pans, spatulas, and thermometors, get almost no attention at all.

In this tutorial, we learn how to find the best wedding dress for your body type. The rectangle or oval shape body doesn't have a well defined waist line, so you will need a dress that draws attention to the hair and face. A pear shaped body is where the bust and wast are smaller than the lower half of the body. You will want to select a wedding dress with ruffles or shoulder pads to draw attention to the top half of your body. A triangle shaped body has a large bust. You will want to select ...
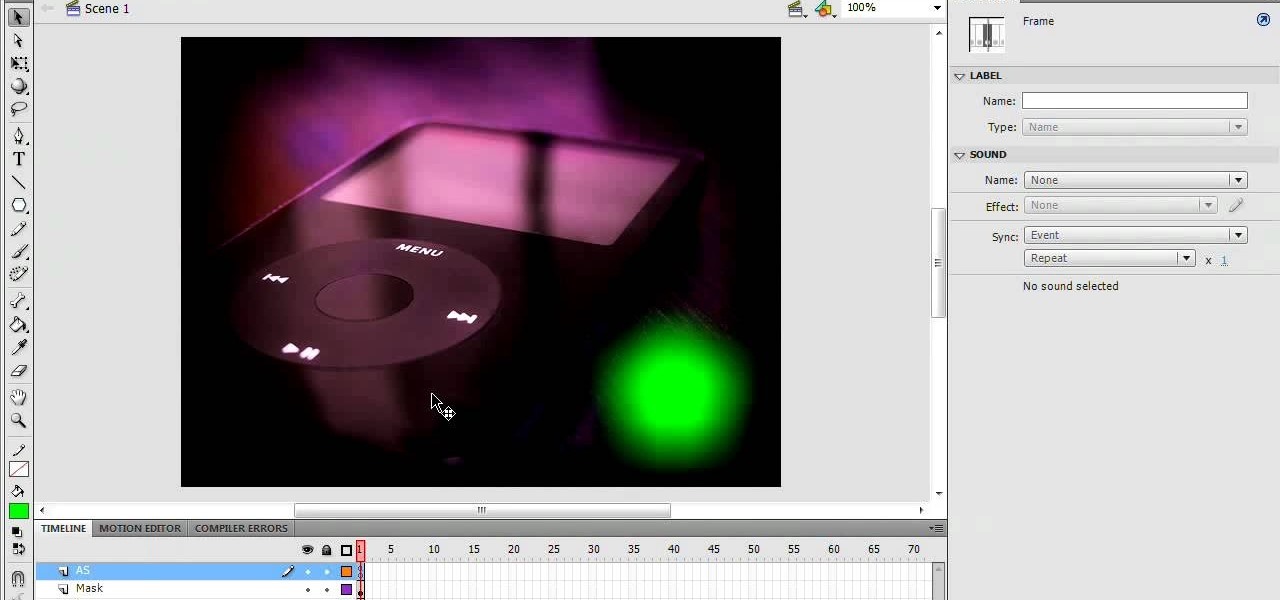
1. In the Flash Application go to new and select Flash File ActionScript 3.0. 2. Change the stage size to 600*450(width and height) in the property section. 3. Then goto file import image and select the background image. 4. Rename the layer1 to image and go to modify->convert to symbol and name that as mac-clip 5. Create two new layers namely Mask and As. 6. In the Mask layer draw a poly star image and convert it to movie clip symbol 7. Select As layer go to windows-> action, then add the eve...

They say you have to be in the right place at the right time... how about an elevator? If you happen to run into your ideal employer or business partner, in an elevator – or anywhere else for that matter – you'll have about 30 seconds or less to wow them. Here's how to do it.

Have a date and looking to impress? First dates can be nerve racking and totally awkward. Watch this video on how to impress a man on the first date and stay calm.

Curious to know what she's thinking? These tips will help you figure out if your girlfriend wants to get married.

You know he cares more about you than his precious video games; he just needs a little help showing it. This video gives tips for luring a boyfriend away from video games, by compromising his love of competition and skill-based games with other activities you can enjoy together as a couple. Watch this video dating advice tutorial and learn how to compete with a video game for your boyfriend's attention.

Using Netcat to backdoor a macOS device has its short-comings. If the compromised Mac goes to sleep, the Netcat background process will occasionally fail to terminate correctly; This leaves Netcat running infinitely in the background and the attacker with no new way into the device. As an alternative, we'll use the lesser-known Tcl shell which can handle abrupt backdoor disconnections.

In my last tutorial, I talked about creating a virus inside of a Word Document in the scenario of a mass-mailer attack. In this post, however, I'm going to be covering creating a fake image or screenshot with a meterpreter backdoor hidden inside to be used in a similar scenario. Step 1: Creating the Virus

When performing something such as a mass mailer attack on a company, sending executables usually isn't the best option. That's why, in this tutorial, I'll be teaching you how to code a VBA script macro into a Word document in order to compromise a system. Combined with a little social engineering, this can be a very effective technique.

Welcome back, my neophyte hackers! Many newbie hackers seem to be confused regarding the process or methodology to employ a successful hack. Most want to simply go straight to the exploit without doing the due diligence to make certain that the hack will work and you won't get caught.

This tutorial follows the same idea as my original tutorial for windows, but I've redone it to work with Mac OS X. Here's how to get a meterpreter session from your victim opening a malicious word document:

Hi I am a new member of null byte(although I am reading this website from the beginning) and this is going to be my first post.
Do you remember my last article on how to hook any web browser with MITMf and BeEF? Well, we are using the tool once again, but this time for auto-backdooring....

First, I want to give credit to the author where I first found how to do this: Astr0baby's Blog. This article was dated, so I took the script on his page and reworked it to make it work today. (I also included the way to make it hide the cmd line popup.) Requirements
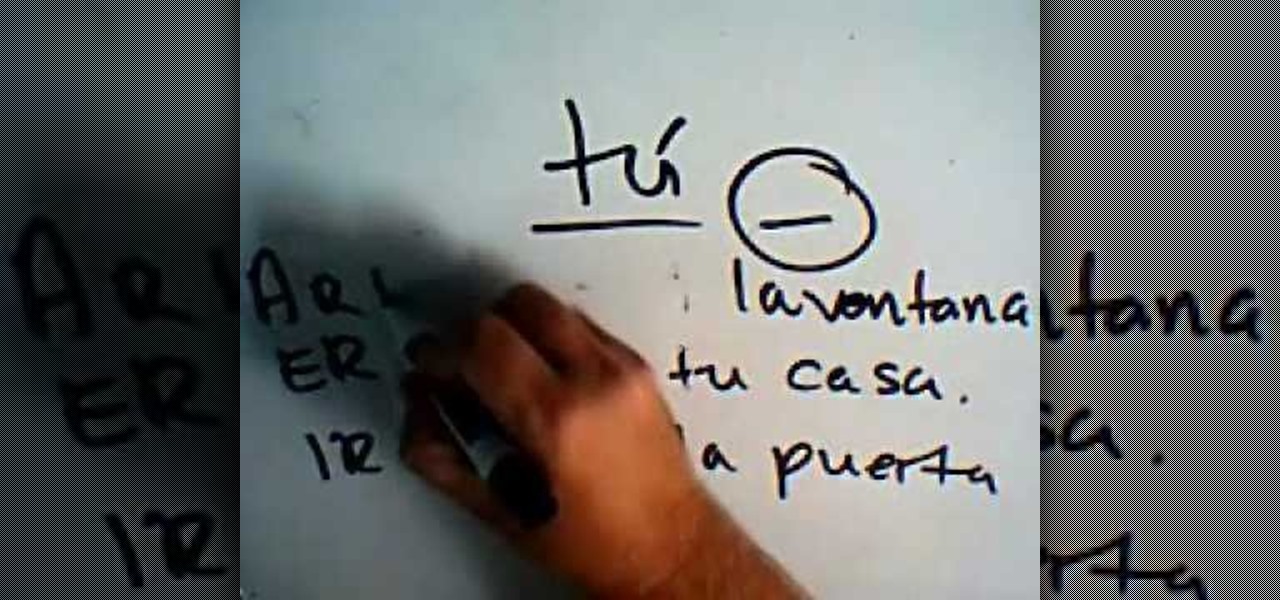
In this video, we learn how to make Informal and formal commands in Spanish. When you speak in first person singular, you will say "yo" when you speak in plural, you will say "nosotros". These are both informal or familiar forms of the word. When you are speaking to someone that is a elder, you will want to speak in formal instead of informal. Use informal mode when you are talking with friends, family, children, and anyone else you talk to in a daily basis. Pay attention if you are talking a...

Okay, let's admit it: most guys and gals who are looking at pictures of Playboy bunnies probably aren't paying the most attention to their faces. But whether other assets of the Playboy bunnies are more fascinating or not, Playboy bunnies always pay lots of attention to perfecting their makeup.