How to adjust a sliding door. Sliding doors are great when they are sliding but can be a real pain in the bum when they don't. Today's video will concentrate on adjusting the wheels to help alleviate some of these annoying issues. It doesn't matter if it's a robe sliding door, a closet sliding door, a glass sliding door or a patio sliding door, the principle is still the same. Obviously there can be other factors like the sliding door track or the sliding door wheels being in a state of disre...

The recent announcement that Facebook will begin inserting advertisements into its VR experience on its Oculus Quest headset has set the VR and augmented reality industry into a frenzy.

Now that the NCAA Basketball Tournament is underway, 7-Eleven has decided to launch an augmented reality experience to remind basketball fans where they can quench their thirst throughout March Madness.

If $200 was too much for you to get in on some Star Wars augmented reality action, Best Buy is now selling refurbished Star Wars Jedi Challenges sets for $79.99 and new ones for $99.99.

On Thursday, Snapchat opened up its walled garden of World Lenses to the masses of creators with the launch of Lens Studio.

The Oreo Beta for Samsung's Galaxy S8 and S8+ is official and available to download on your device. Now that we have the update in hand, we've started detailing several of the changes and features. We've already looked at the new Notification Channels functionality, so in this post, we'll take a look at several improvements to Samsung's stock keyboard. While some Android users prefer to install third-party keyboards on their device, Samsung's default keyboard has a loyal following among Galax...

ARKit and ARCore generate excitement among various segments of the tech industry for spurring adoption of augmented reality with consumers via mobile devices.

Converting files from one format to another can be a pain. Sometimes you have to download software that you'll only end up using once. Other times you have to use a shady third-party conversion site that's riddled with ads. Not to mention that after a while, unless you're extremely organized, your converted files will be scattered all across your hard drive.

One of the most rewarding things about jailbreaking is theming. Unlike Android, iOS doesn't allow you to make small changes to certain aspects like the icons or the lock screen, so jailbreaking facilitates the ability to make some of these desired changes happen.

As carriers finalize their variations of the Android 4.4.4 update, we're left with only brief glimpses of what the new "Eye Experience" holds in store for us while we wait. However, thanks to a system dump of an updated European HTC One M8 and some clever hackery by donmarkoni, we can now install the new camera app on any variant of the HTC One M8.

How to remove and replace a door handle / door knob. How to install a door knob. This is a job that can be done quickly and easily without any special tools (a cordless drill with a Phillips bit or a hand held Phillips Head screw driver). Follow the steps outlined below for a hassle free experience.

During my early elementary school years, origami was my go-to pastime. When it came to learning about it in art class, I ventured out well past the basics that were being taught.

With Avatar, Facebook's personalized stickers for use on its social and messaging platforms, those who aren't on Facebook or have otherwise dumped the social network may feel left out.

I was today years old when I first heard of Bhad Bhabie, but I'm told she is apparently a rapper with a rags-to-riches story.

In this week of Snapchat lenses, there was a significant increase in ones that involve Marvel superheroes (the Infinity War effect), as well as ones with YouTubers. Classic sitcoms will also always do well, as evidenced by some of my previous roundups. Overall, lenses are doing well and only continuing to grow.

Tardigrades are some of the toughest but least well-known creatures on our planet. These tiny animals, also called moss piglets or water bears, are definitely of this earth, but some can boast that they've also traveled to space.

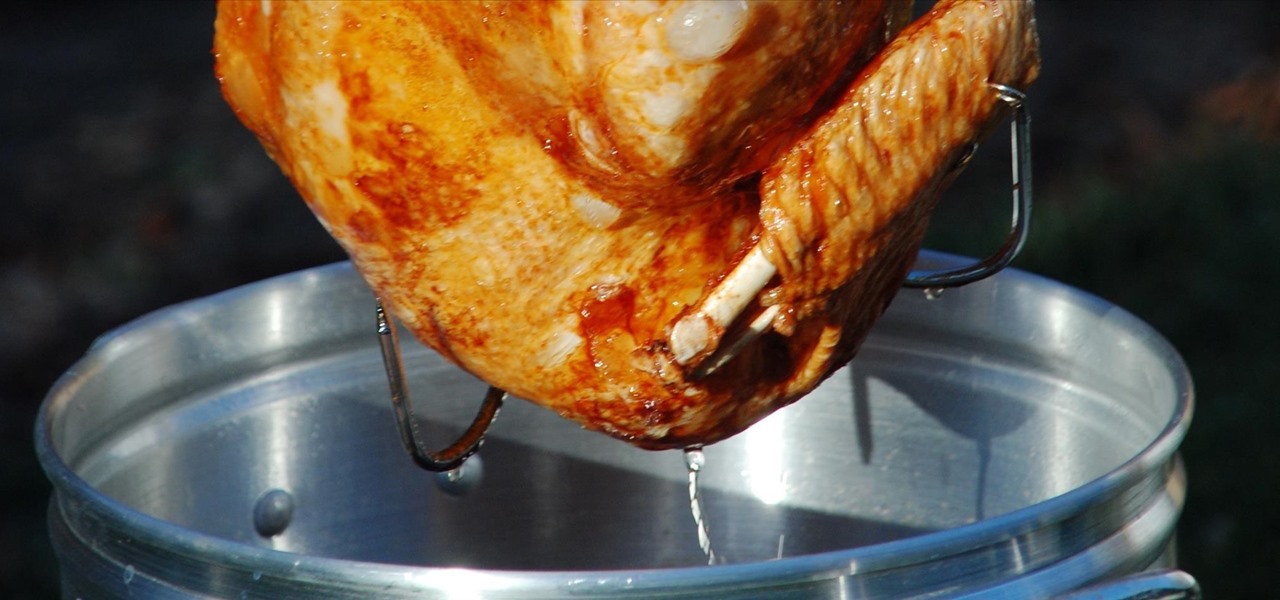
Roasting turkey is a topic that inspires endless debate among cooks. How do you get the perfect mixture of juicy meat, crispy skin, and flavor? Everyone has a favorite technique, whether it's brining the bird or spatchcocking it. However, if you're ready to move onto Ph.D. levels of turkey cooking, you might just want to look beyond these methods and get genuinely wild.

Mobile carriers have been the bane of my existence for as long as I've had a phone. First, they take away unlimited data, and then when you try and switch carriers, they hold your phone hostage for a up to a week before unlocking it from their network.

One booze hack that's been making the rounds for years is that inserting a spoon by the handle in a champagne bottle's neck will preserve its carbonation. This is one of those tips that I wish were true. Champagne is a great thing to have around on a special occasion, and it seems a shame to pour any leftovers down the drain once its lost its fizz. While there's lots of anecdotal evidence surrounding this trick, Harold McGee and Stanford University chemist Richard Zare debunked this myth as d...

You've had your Xbox 360 for a few years now and your game collection is pretty extensive. Maybe it's not that extensive, but it's still substantial. Now imagine that you live in Europe and you're moving to the United States. I don't know why—maybe your dad got a job offer. Don't ask me, ask your parents. They're the ones that are making you move. Anyways, as most Xbox users know, games are coded by region. Games that work in Europe might not work in the United States. Does this mean you shou...

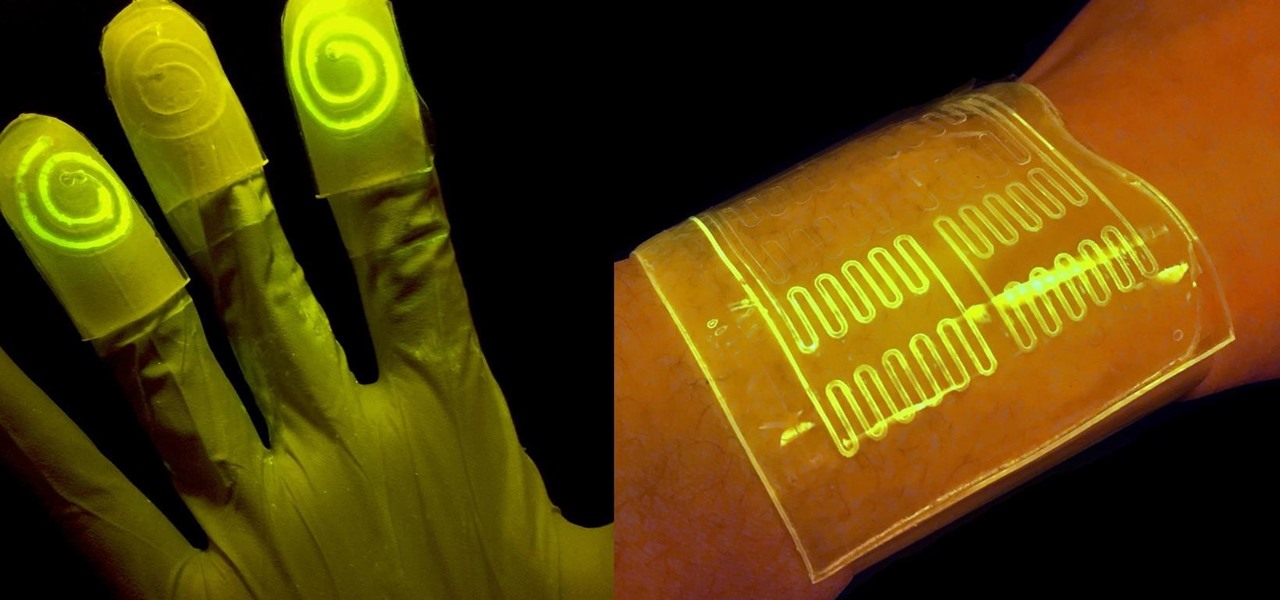
While at work, you notice your gloves changing color, and you know immediately that you've come in contact with dangerous chemicals. Bandages on a patient signal the presence of unseen, drug-resistant microbes. These are ideas that might have once seemed futuristic but are becoming a reality as researchers move forward with technology to use living bacteria in cloth to detect pathogens, pollutants, and particulates that endanger our lives.

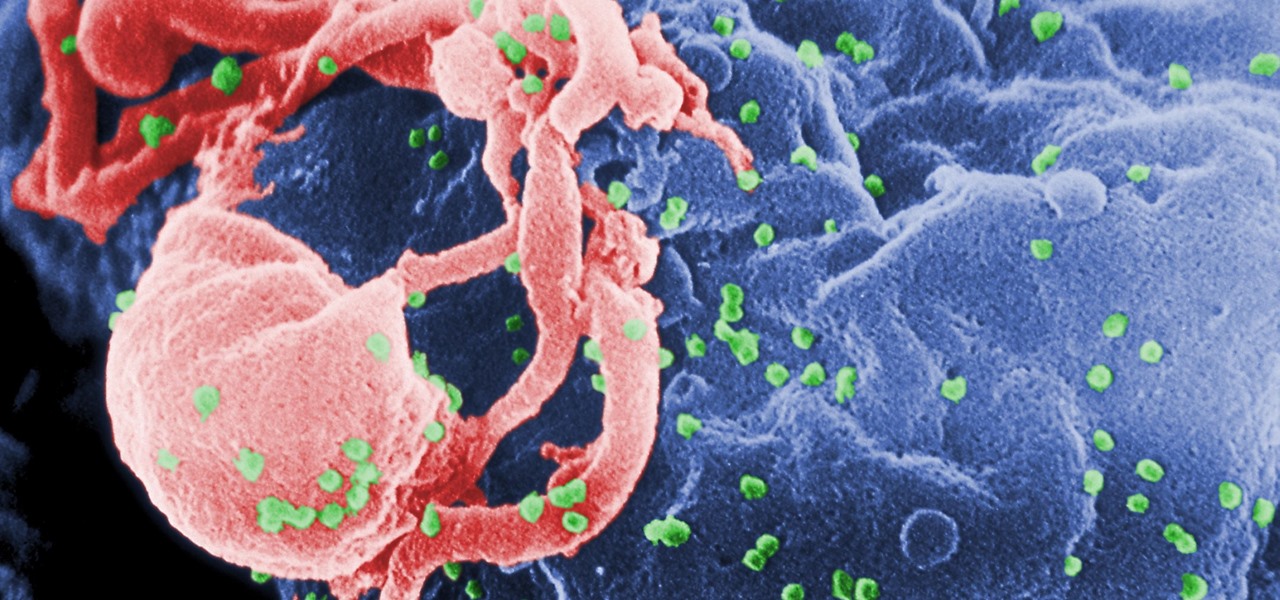
Being infected with HIV means a lifetime of antiviral therapy. We can control the infection with those drugs, but we haven't been able to cure people by ridding the body completely of the virus. But thanks to a new study published in Molecular Therapy by scientists at the Lewis Katz School of Medicine (LKSOM) at Temple University and the University of Pittsburgh, all that may change.

In the past, infection with human immunodeficiency virus (HIV) commonly led to dementia as the virus made its way to the brain. Even in effectively treated people, HIV can hide out and replicate in places like the brain, where it's tough to detect. That's why it's very concerning that half of all HIV-infected patients still report cognitive problems.

Almost every bread recipe will tell you to look for a golden brown crust or to tap on the bottom of your loaf and listen for a hollow sound. That visual and sound technique will work most of the time, but it can still come up short, leaving you with a soft and gooey spot in the middle of your loaf.

Hello everybody Joe here. Today I will be demonstrating how you can find XSS vulnerabilities in a website and what you can do with them

Welcome back, my tenderfoot hackers! One of the issues we often encounter with Metasploit is how to add new modules. Although Rapid7 (Metasploit's owner and developer) periodically updates Metasploit with new exploits, payloads, and other modules, at times, new modules appear that are not added to the Metasploit repository.

Airports are terrible germ-infested purgatories where people sit around for hours without Wi-Fi while they anxiously await to get wherever they really want to go. Unfortunately, there isn't much we can do about waiting, but this little Wi-Fi hack could help make the waiting a little less boring.

The lengths people will go to for a grilled cheese sandwich are amazing. They'll use irons, wafflemakers, or whatever appliance that produces enough heat to produce the perfect combination of golden, grilled bread and oozy, melting cheese. I personally favor my cast-iron skillet or the oven for making a really great grilled cheese sandwich. If I'm feeling lazy, then a toaster oven will do. But what if you're at work or in a dorm and the break room only has a toaster?

Welcome back , my fledgling hackers! Lately, I've been focusing more on client-side hacks. While web servers, database servers, and file servers have garnered increased protection, the client-side remains extremely vulnerable, and there is much to teach. This time, we'll look at inserting a listener (rootkit) inside a PDF file, exploiting a vulnerability in Adobe's Reader.

A low-key iPhone feature that's been around since iOS 10 can make the iMessages you send to family and friends more exciting overall. One particular element is, if you'll forgive my decades-old slang, "da bomb" for emoji.

People use browsers for all types of things, and in general, we trust a lot of personal information to them. That's why browsers are a perfect attack surface for a hacker, because the target may not even know they are infected and feed you all of the information you could want.

One of the ultimate goals in hacking is the ability to obtain shells in order to run system commands and own a target or network. SQL injection is typically only associated with databases and their data, but it can actually be used as a vector to gain a command shell. As a lesson, we'll be exploiting a simple SQL injection flaw to execute commands and ultimately get a reverse shell on the server.

Cross-site scripting can be one of the easiest vulnerabilities to discover, but to be successful with this type of attack, it is essential to learn how to get past filters. In the previous guide, we explored some ways to do this, such as abusing attributes and event handlers and tricking the application into accepting unusual characters. Now, let's take a look at more techniques used to defeat filters.

As penetration testers, we sometimes need to securely store customer data for prolonged periods. Bruteforce-resistant, vault-like containers can be created with just a few commands to protect ourselves from physical attacks and unintended data disclosures.

With just one line of Ruby code embedded into a fake PDF, a hacker can remotely control any Mac computer from anywhere in the world. Creating the command is the easy part, but getting the target to open the code is where a hacker will need to get creative.

The misconception that macOS is more secure than the Windows operating system is far from the truth. With just one small command, a hacker can completely take over a MacBook and control it remotely.

After spending a good portion of 2017 teasing us with images and bits of news, Lenovo, in a partnership with Disney and Lucasfilm, has finally released its Mirage AR headset along with the Star Wars: Jedi Challenge game collection.

This is a very exciting time for mixed reality developers and fans alike. In 2017, we have seen a constant stream of new hardware and software releases hitting the virtual shelves. And while most of them have been in the form of developer kits, they bring with them hope and the potential promise of amazing things in the future.

To shine light on the future of the relationship between humans and viruses, a team of researchers from the University of Oxford looked into the dim and distant past.

So this is my methodology for this project of writing a rootkit. Please leave feedback on what is right/wrong. I tried to simplify concepts the best I could however...