
How To: Get a copy of a house deed
Looking to move the right way? Owning a piece of property is an important goal for many people. Here’s how to obtain a copy of proof of ownership.


Looking to move the right way? Owning a piece of property is an important goal for many people. Here’s how to obtain a copy of proof of ownership.
Duct tape is versatile and can be used for anything. But did you ever imagine that it can be used for making a book cover? Protect your books with sturdy duct tape. This tutorial shows you how to make a general book cover for a paperback using duct tape, but the process can be extended to cover any type of book. Protect all your books from damage with duct tape.
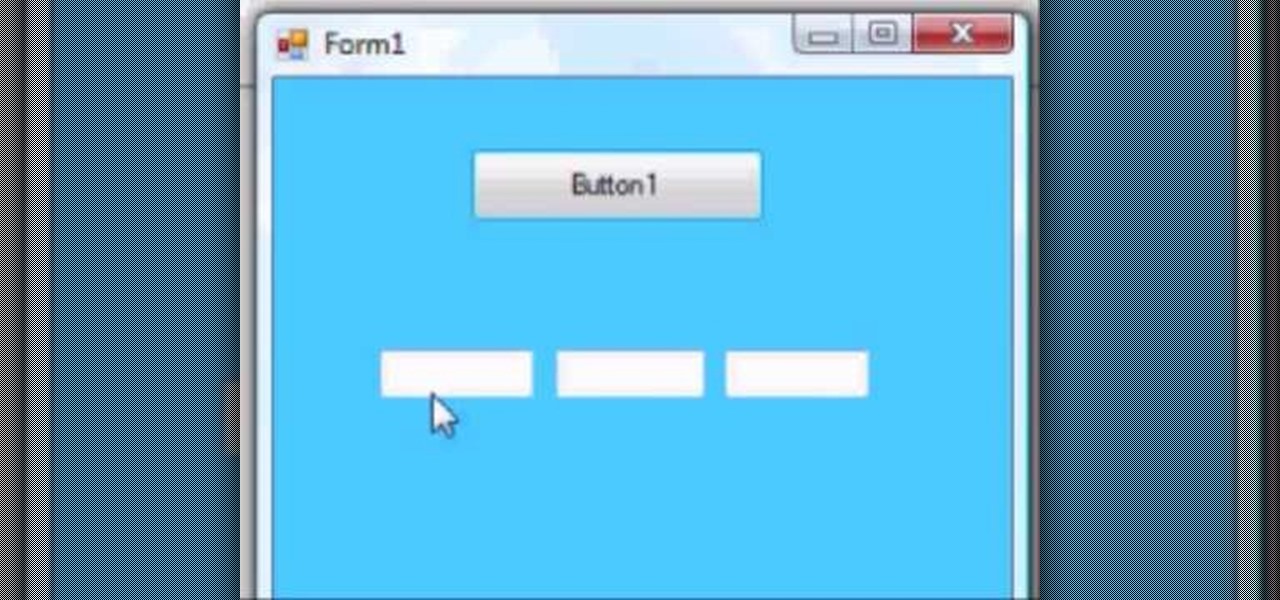
This VB.Net tutorial teaches you some tricks with duel forms and how to do create very basic password protected applications.
STREET POETS INC INVITES YOU TO AN EVENING OF SACRED MUSIC & ILLUMINATING POETRY:

From The LATimes: "Brown, the Democratic nominee, touted talking points — living within California's means, no new taxes without voter approval, returning control to the local level — that could come from a Republican playbook. Whitman, his GOP rival, unveiled her seventh attack ad against Brown, this time enlisting the words of former President Clinton during their contentious 1992 Democratic presidential primary battle. Tellingly, both candidates avoided mention of their political party.

Trusty LifeHacker brings us another helpful HowTo, but this time it's in the travel department.

The Nextbit Robin, the world's first cloud-oriented smartphone, is on sale at Amazon for $299 plus tax, a savings of $100. You'll have to act quick though, as the deal only runs through May 10th while supplies last. Nextbit Robin, an unlocked SIM phone, was just updated last week, and now runs Android Marshmallow 6.0.1. It also has a unique storage system, with 100 GB of cloud space, as well as 32 GB of built-in storage. You can snag it in midnight or mint colors. Amazon Prime members will al...

Major banks and the financial global elite are now confirmed to have as much as $32 trillion in hidden assets stashed away in offshore accounts that are subject to little or no taxation. As a result, around $280 billion is estimated to be lost in tax revenues. In other words, the multi-trillion dollar banks and elite families are avoiding any taxation while forcing United States citizens to foot the bill. Amazingly, the $32 trillion stashed away represents the overall GDP of the United States...

In just a few months, Binance has experienced explosive growth, overtaking its rivals to rank among the top three cryptocurrency exchanges in the world by trading volume. Without a doubt, Binance is now among the best sites for trading alt-coins like Ripple (XRP), Stellar (XLM), and NEM (XEM) to name a few.
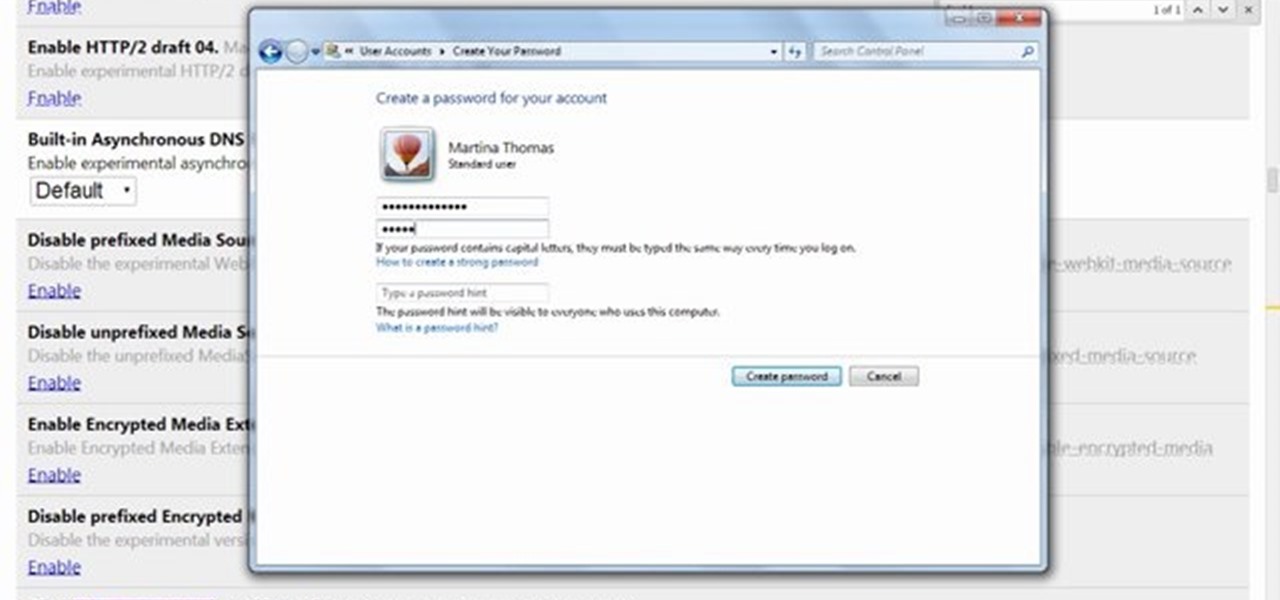
This video will show you how to protect others from accessing saved password on Google Chrome. Saving account passwords in browsers are useful for time saving as well as threatening for malicious activity. This is dangerous for security. So you must protect your accounts detail from others to secure your browsing. Watch the video and follow all the steps carefully.
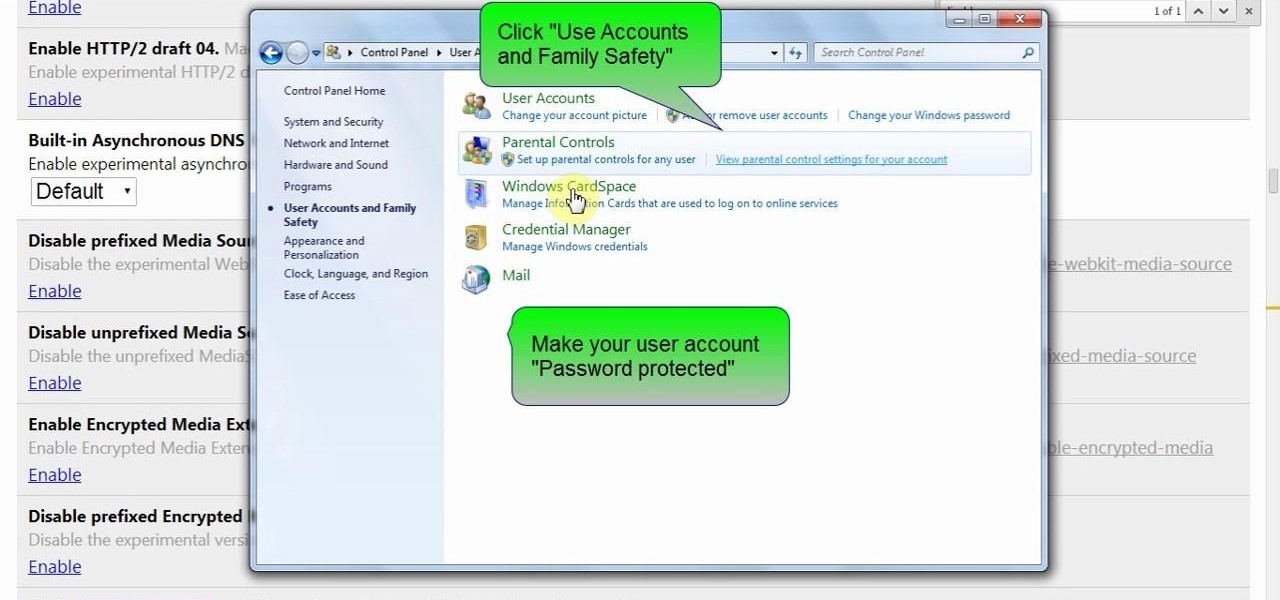
This video will show you how to protect Google Chrome password from others. If you don't protect them from others anybody using your PC could access all your account detail. Now you can realize this is dangerous. Watch the video and employ the technique in your PC.

There are many threats to be wary of when playing Terraria. If you'd like to be able to feel safe from a couple of them, watch this video and learn how to protect your house during Red Moon events and Goblin Invasions.
As you may know, your iPhone stores data on your location from time to time. If you'd rather that information be kept private, watch this video for some helpful instruction on how to protect your location information. Encrypt the information being gathered by iPhone tracker.

Even if there's a giant block of obsidian, you can figure out a way to exploit a glitch that will let you easily break into it. You're also shown a way to easily break into protected chests on shared servers in Minecraft.

Learn how to password protect your Motorola Droid Google Android smartphone. Whether you're the proud owner of a Froyo Motorola Droid or are just considering picking one up, you're sure to be well served by this video guide. For more information and detailed step-by-step instructions, watch this phone hacker's how-to.

If you have a big beautiful lawn and live somewhere with cold winters, you probably already know about how to winterize your lawn and how doing so can protect your lawn in the winter and make it grow better in the spring. If you don't, watch this video.

If you live somewhere with harsh winters, you know that they can be hell on your garden and the flower pots therein. Watch this video for tips on protecting different kinds of flower pots from the elements during the winter.

During the winter and freak weather events in spring and fall your garden can take a beating from frost and excess cold. Watch this video to learn how you can protect your plants and flowers during the cold so they are healthy and ready to grow when the weather improves.
In this clip, you'll learn how to secure a new Microsoft Windows desktop or laptop computer. For more information, including a complete demonstration, and detailed, step-by-step instructions, as well as to get started protecting your own new Microsoft Windows PC, take a look.
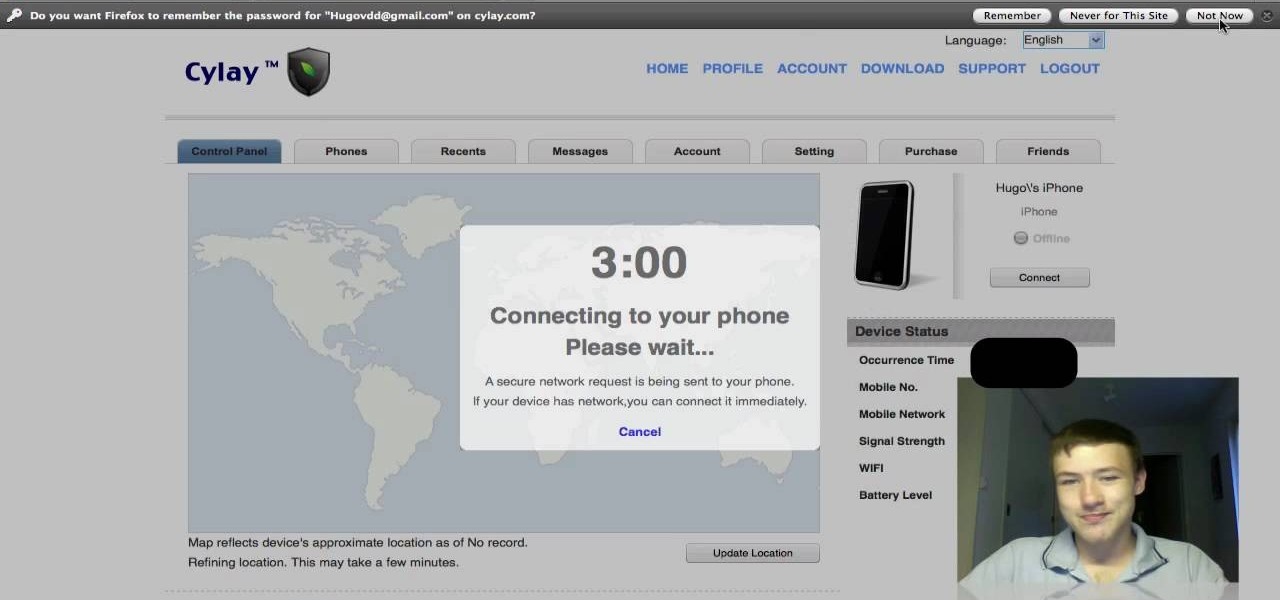
This app will only work on Apple devices that have already been jailbroken. Once you have, you can set up an account with Cylay. And once you have an account with Cylay, you can protect your phone or mp3 player against theft.
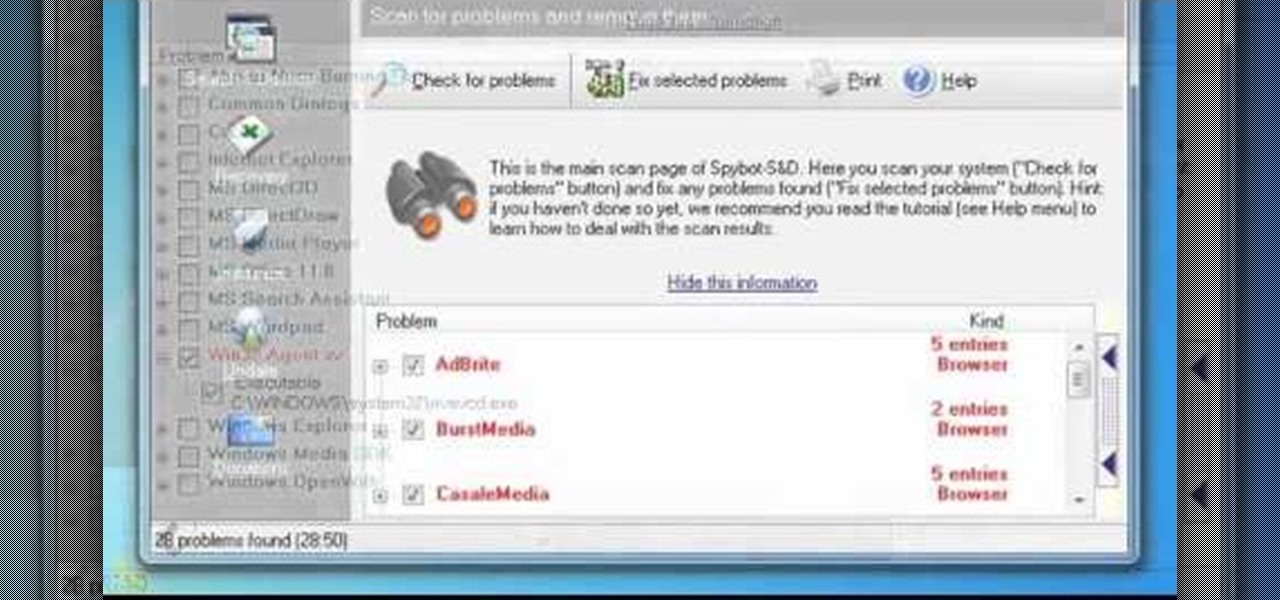
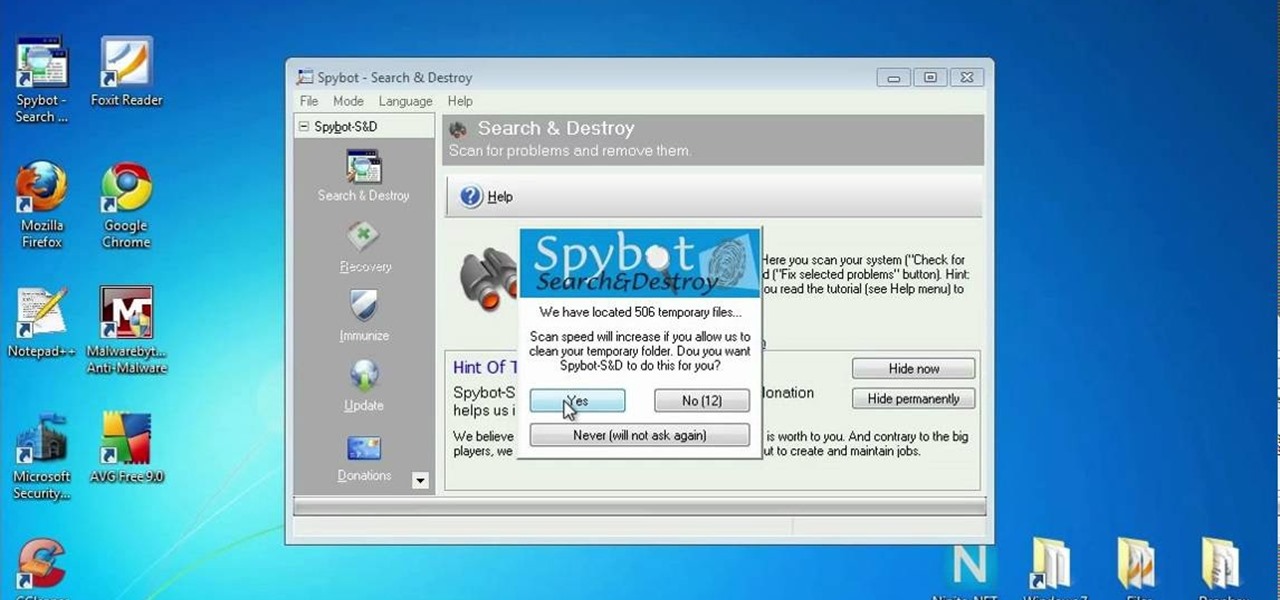
In this clip, you'll learn how to use the free Spybot Search & Destroy tool to protect against and remove malware on a Microsoft Windows PC. For more information, including detailed, step-by-step instructions, and to get started using Spybot on your own Win PC, take a look.

Looking for an easy way to protect your privacy when using Google Search? With the right habits, it's easy. So easy, in fact, that this home-computing how-to from the folks at CNET can present a complete overview of the process in just over a minute. For more information, including detailed, step-by-step instructions, take a look.

In this clip, you'll learn how to use the Backtrack 3 Linux distro and Aircrack-ng WiFi security app to crack the password to a WEP-protected wireless network. The process is simple. For more information, including step-by-step instructions, and to get started testing the security of your own WiFi networks, watch this hacker's how-to.

Interested in finding out just how secure your WEP-protected wireless network is? Let this video be your guide. It's a simple process and this home-networking how-to will teach you everything you'll need to know. For specifics, including detailed, step-by-step instructions, and to get started cracking WEP networks with BackTrack yourself, watch this helpful video guide.
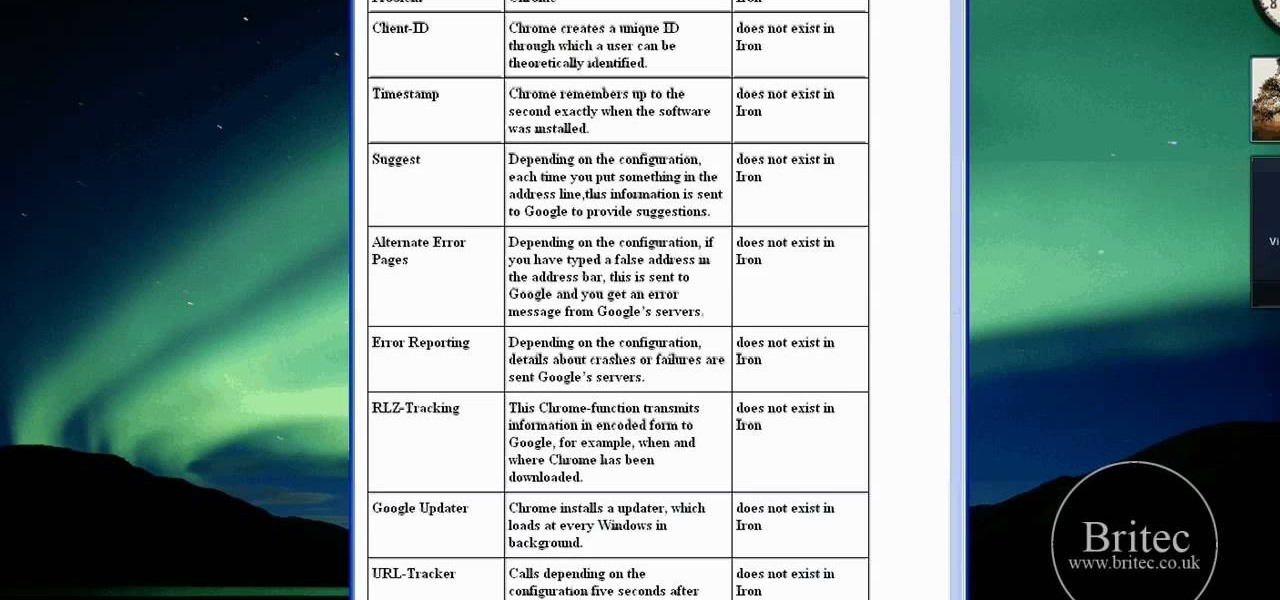
Interested in using Google Chrome but concerned about protecting your privacy while surfing the web? Meet Iron Browser, a secure but otherwise identical clone of the Google Chrome web browser. This clip from Britec will teach you where to find it, how to install it and how to get started using it.
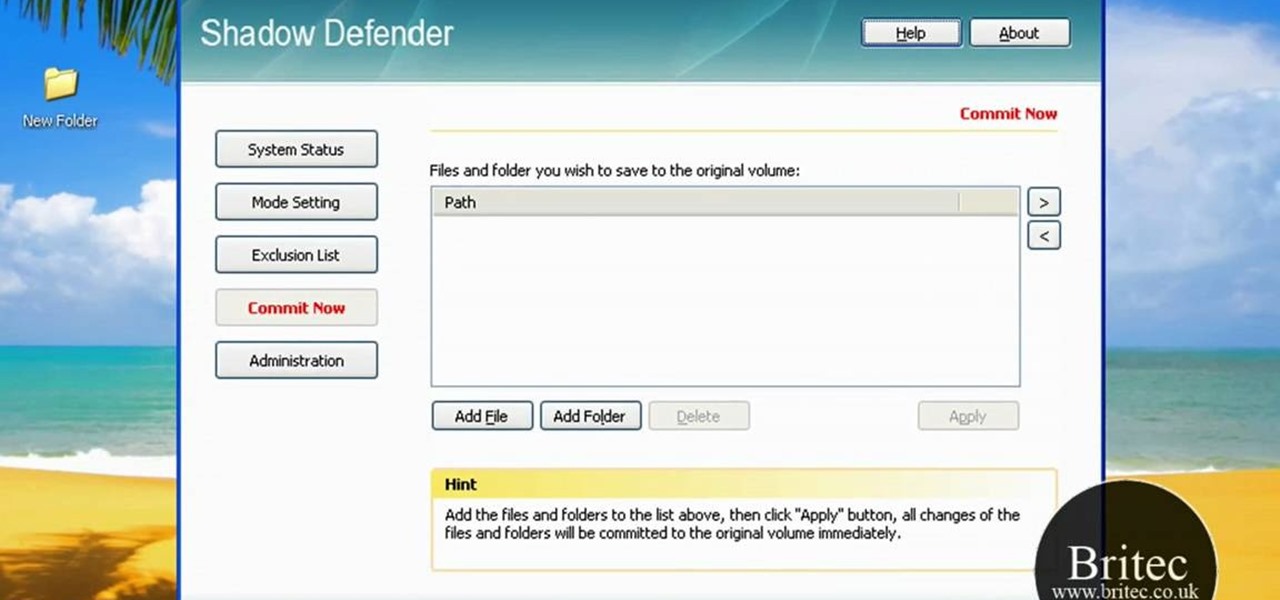
Looking for a security solution for your Microsoft Windows PC? With Shadow Defender, it's easy! So easy, in fact, that this home-computing how-to from the folks at Britec can present a complete overview of the process in just under ten minutes. For more information, including step-by-step instructions on how to get started using Shadow Defender to protect your own desktop computer or laptop, take a look.
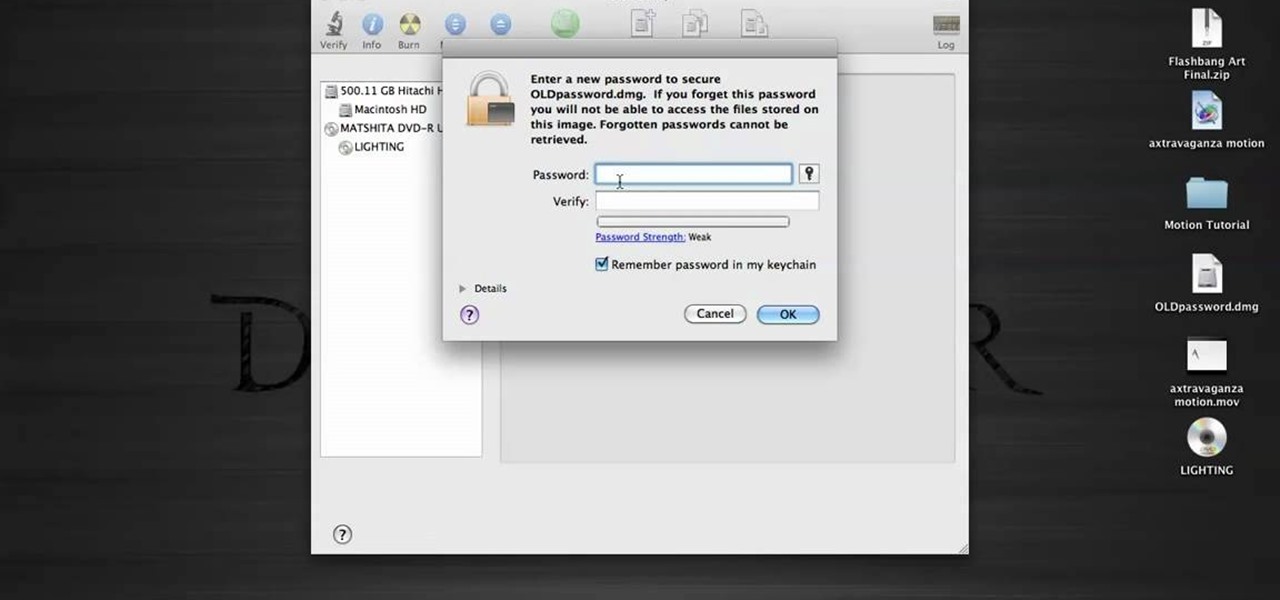
In this tutorial, we learn how to password protect a folder in Snow Leopard on your Mac. First, go to the finder and click on "utilities". Now go to "file, new, disk image from folder". Now, you can select the folder you want and then click "image". Make it a read/write folder so you still can edit the files and enable the encryption. Save this, then it will ask you for a password. Create a password and then verify it. When finished, uncheck the "remember my password", then click on "ok". Now...

If you're restoring an old vehicle, it's always important to make sure you take the necessary precautions for preventing any damage. In this particular video tutorial, you'll find out how to protect your door panels on a classic VW Beetle Bug without any problems. So good luck, pay attention, and enjoy!

My Blackberry TV demonstrates how to protect your Blackberry device with a password. Protecting your Blackberry with a password will help to stop people from accessing your personal information on your device. From the home screen, press the Blackberry menu key. Then, select the options choice. Next, scroll down to the password choice on the options menu. Select password and then select the set password button on the password screen. Enter your desired password and then press the enter key. V...

As any SLR or DSLR owner knows all too well, the price of lenses can often approach or even exceed the cost of your camera. As such, it's important that you take the necessary precautions to protect them. With this free photographer's guide, you'll learn about using UV (that is, ultra-violet) filters to protect your single lens-reflex camera lenses from sun damage.
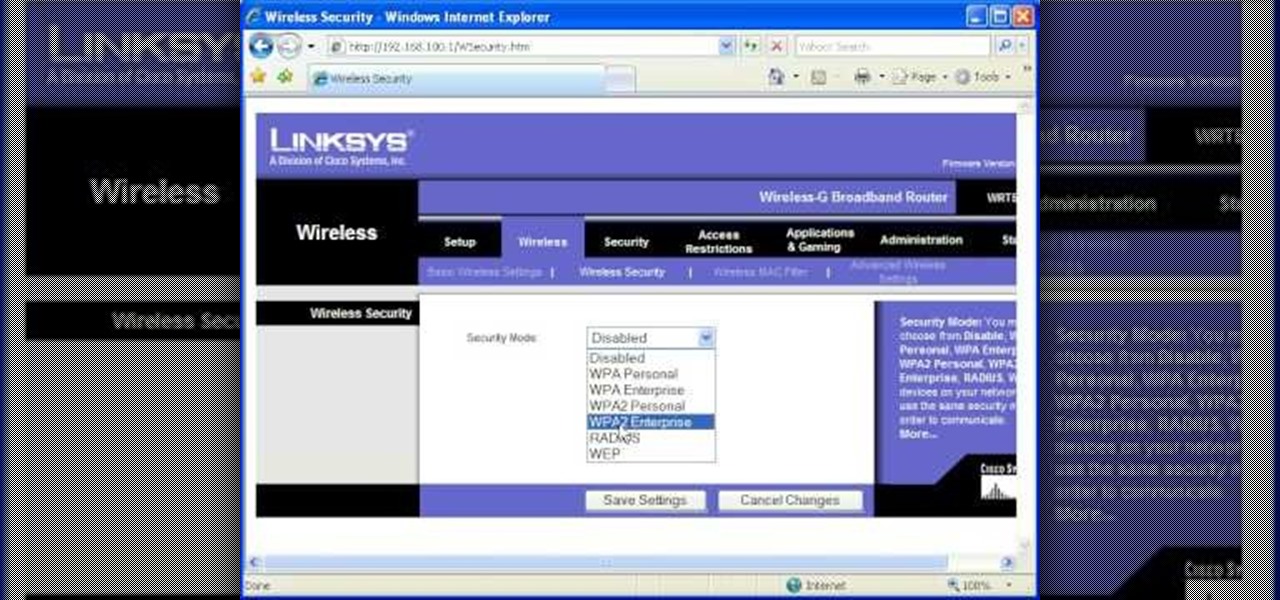
Most of the home wireless networks are not set up by professionals and hence they might lack in security features. People just set up the wireless networks by connecting the devices and powering them up and never care to apply security settings to the network. This may result in your wireless network being compromised by unwanted external entities. How ever you can do a web based configuration settings and secure your wireless network by password protecting it. This settings differ from the m...

If you live in a hurricane prone area, it is a good idea to protect your windows with security film. This video will teach you how to install hurricane security window film on your own and protect your home and assets.

Ron Hazelton explains how to protect your foundation or basement wall from being affected by water that is discharged from your downspout. He explains how downspout extenders can be used to carry the water away from the foundation. Ron will show you three variations of downspouts that you can use. You'll learn how to install each kind of downspout so you can decide which is right for you. If you follow the advice given in this video, you're sure to further protect a very important part of you...

In this video a professional boxer demonstrate the basics of boxing so that you can protect yourself. First of all, you should stand in such a manner that your left foot is in front and the right foot is in back (if you are right-handed). Make a fist, put both hands in front of your face. The distance between both the hands should not be much so that in any case, you can cover and protect your face. Your left hand should always turn up and pull back. For punching, take your right hand fist ne...

Watch this video for a helpful tip on how to use secret folder application and protect folders in your MAC PC by hiding it. you could download secret folder application from version tracker.com for free go to the Website and click download button to download the application on your Mac PC open the secret folder application. click on the required password button, put your desired password and re enter to confirm. to access your file, click the plus button at the lower left. choose the desired ...

Need to unlock your music? Want to save Rhapsody or Napster files on more than your own computer? This is how to unlock, remove drm and convert protected wma files from napster and rhapsody to mp3 without having to pay for them. Also how to put napster and rhapsody files in iTunes and on your iPod.

The Microsoft Office Access 2007 relational database manager enables information workers to quickly track and report information with ease thanks to its interactive design capabilities that do not require deep database knowledge. In this Microsoft Access video tutorial, you'll learn about protecting your VBA code from snoopy little trolls. For more information on keeping your VBA code secure, watch this MS Access how-to.

Sadly, into each life at least one mean, nasty, low-down, no-good boss must fall. When it's your turn, you'll want these survival tips. Trying to remain calm and protecting yourself are important strategies to protect your career. Watch this video job skills tutorial and learn how to cope with an unfair boss.

In this video Bob Schmidt shows you how to protect yourself when working with fiberglass insulation when insulating or doing removals during your home improvement projects.

Watch this video to learn how to make a password protected video.