In most macOS hacks, a non-root terminal is used to create a backdoor into the device. A lot of damage can be done as a low-privileged user, but it has its limitations. Think twice before granting a file permission to execute — an attacker might be able to convert your harmless scripts into persistent root backdoors.

Most users don't realize how much valuable data is in their network traffic. With a few simple tools, an attacker can quickly pick out cookies, passwords, and DNS queries from a macOS device as it covertly streams the victim's network traffic to the attacker's system. Here, we will cover two methods for analyzing packets flowing from a Mac.

Get free self-defense techniques and tips for women's self-defense. Learn to escape an attacker's grasp using self-defense techniques in this free video on women's self-defense.

A DeAuth hack attack against a wireless network, as shown in this how-to video, will disconnect any and all users on a given WiFi network. The attacker does not need to know the WEP or WPA key or be connected to the network. For step-by-step instructions on running a DeAuth hack yourself, watch this simple how-to guide.
The History Channel features great fighting tutorials on their show Human Weapon. Here they go into the ancient Israeli art of Krav Maga. Bursting will counter a surprise attacker by hurling your power into their core and blocking their weapon from striking you.

KeePassX, 1Password, and LastPass are effective against keyloggers, phishing, and database breaches, but passwords managers rely on the operating system's clipboard to securely move credentials from the password vault to the web browser. It's within these few seconds that an attacker can dump the clipboard contents and exfiltrate passwords.

Encrypting payloads and encoding stagers are more effective against macOS than one might think. It's very easy to evade VirusTotal and macOS antivirus software using a few simple tricks.

Screenshots taken from a compromised computer can provide hackers with access to private emails, photographs, and information found in sensitive documents. This data can be used by the attackers to build profiles of a target for social engineering attacks and blackmail or even just to release the information out in the wild.

Welcome back, my budding hackers! As I have mentioned many times throughout this series, knowing a bit of digital forensics might keep you out of a lot of trouble. In addition, digital forensics is a burgeoning and high paying career. Some knowledge and certifications in this field will likely help you land a Security Engineer position or put you on the Incident Response Team at your employer.

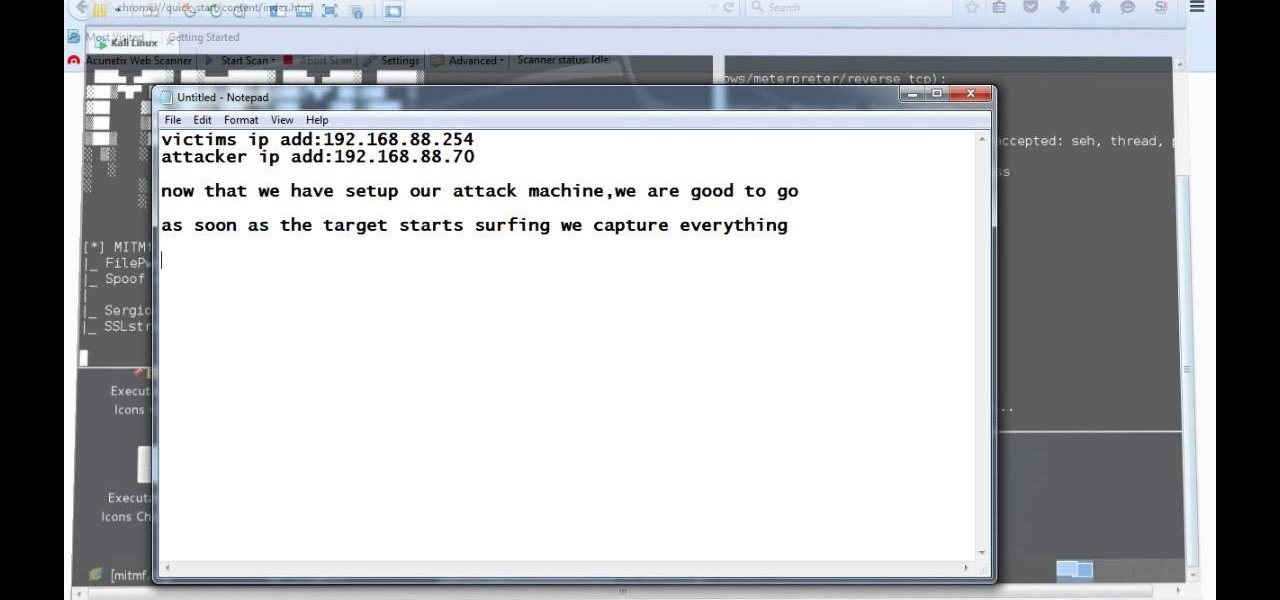
Video: . Hi, this is a quick demo about how to backdoor executables (software) sent over HTTP using MITMF, backdoor factory

Would you want to be able to defend yourself and your loved ones if someone were to physically attack you? This video will show you how to defend yourself against an attacker choking you from the front. It' the best MMA for self-defense, especially for a teenager.

Video: . This map requires the 12w37a snapshot or better, and you must turn on command blocks to use it.

Losing weight can be a battle, but why not be realistic about your goals rather than kill yourself striving for a size 0? A happier alternative to the cycle of weight loss and gain is to achieve a weight you and your doctor can both live with. In this tutorial, learn how to calculate your BMI and ways to figure what your "happy weight" is.

COD4 Pro Nade Tutorial See how to do a pro nade attack in Crossfire on COD4. For this grenade throwing tutorial, you need to be in Multiplayer mode, Search and Destroy, on Call Of Duty 4: Modern Warfare.

Shooting in water polo is a basic skill for attackers. Water polo shot requires good height out of the water, arm position, shoulder rotation, and head stall. Shot strategy is important to building your water polo game. Concentrate on improving your rotation to follow through and speed up the shot. This is an attack focused water polo drill.

Protecting the ball in water polo is key to playing a solid game. This water polo instructional includes many drills designed to improve 1-1 play. It includes tips for both the water polo defense and attacker on how to protect the ball in play. This also refers to TV clips of league and pro games to connect it to actual game play.

If knocked to the ground by an attacker, it's important to know how to fall correctly. Learn how to do the forward fall roll and the backwards fall roll in this free video series about self defense moves for women.

This video will teach you how to properly use the sleeper hold in order to subdue an attacker, but not damage their larynx. This is a real way to protect others and yourself. It is meant to help Police Officers from choking people and avoid law suits from performing the wrong maneuver.

This martial arts/self defense video will show you how to break a choke hold using a pressure point, from a seated position. These are nerve points that you use to disrupt your attackers nervous system. Remember that in using these forms you must always keep a calm mind. It is also important to know when your opponent is disabled after using this chokehold.

While the victim is in this head hold they should wiggle enough to make sure their windpipe is free. Turn your head into the side of the attacker, hit him in the groin and with the other hand bring it up under his chin. Do more blows as you run away.

You don't have to buy buttons - just crochet your own! These buttons are naturally much softer than regular buttons, making them ideal for blankets or baby clothes. They also can add a cute accent to nearly any crochet project.

This set up will show you how to use just one light to create a setting that's ideal for cosmetic, fashion and beauty shots. Great for a photographer who only has so much money to spend on studio equipment and accessories.

Want to break into the video game industry? Dream of a career as a game designer? This video shows you how you can become a game designer, in specific for the large game studio Electronic Arts. Find out what's in store for you and the ideal path of study.

Edward Scissorhands is one of the most instantly recognizable characters in all of film, which of course makes him an ideal Halloween costume choice. Watch this video to learn how to do perfect hair and makeup to go along with a store bought Edward Scissorhands costume bought online.

Want to shoot video in low-light conditions with a HTC Evo 4G smartphone? Whether you're the owner of an HTC Evo 4G Android phone or just covet one, you're sure to enjoy this Evo owner's guide from HTC Evo Hacks, which presents a complete, step-by-step walkthrough of how to turn on the camera's built-in LEDs to illuminate subjects in less-than-ideal lighting conditions. For complete details, take a look!

This recipe for corn, avocado and tomato salad is an ideal salad to serve in the summer at your next barbecue. It offers a lighter alternative to the piles of meat without leaving people pining for something hearty and filling. The corn and avocado are plenty filling and the tomato adds a great zest to the dish.

In this two-part science tutorial, learn how to make a cartesian diver, easily & inexpensively. A Cartesian diver, sometimes known as a Cartesian devil is a classic science experiment, named for René Descartes, which demonstrates the principle of buoyancy (Archimedes’ principle) and the ideal gas law.

There's something magical about stop-motion animation made with clay, it's an ideal medium for depicting strange transformations. In this short tutorial you'll learn how to make a simple claymation movie of your own. The video introduces you to some of the materials you'll need, shows you a little about animating and takes you through some of the steps to upload your animation onto your computer for editing.

A gift is doubly special when the box it arrives in is also a gift. In this video, we'll see how to transform a single sheet of paper into an elegant gift box. This project isn't ideal for beginners, but if you have a little origami experience this shouldn't be too challenging.

This web development software tutorial shows you how to slice a site design in Photoshop, and then export the resulting images and HTML to Dreamweaver. This is an ideal method for creating newsletters, as the resulting HTML is tables-based, and better suited to email clients. Learn how to create HTML pages with this Photoshop and Dreamweaver tutorial.

Watch this video to learn how to use glove molding systems. Glove molding systems are ideal for working on medium and large projects, this process involves creating a thin layer of flexible material and backing it up with a stronger, rigid material.This process can be used in automotive, mechanical, fine art and film special effects uses.

This video covers creating a detailed professional surface cast mold for creating mechanical parts. Ideal for working on medium-sized projects, this process of pouring a high quality material around a lower quality core creates a highly accurate, yet economical part. This process can be used in automotive, mechanical, fine art and film special effects uses.

This excellent detailed video demonstrates how to create rigid molds with a fast cast urethane. Ideal for smaller models/molds with a flat side, fast-cast urethanes are widely used for their ease of use, low cost, and quick de-mold times. However, their use requires careful application of release agents. This process can be used in automotive, mechanical, fine art and film special effects uses.

Microsoft.com is one of the most extensive domains on the internet with thousands of registered subdomains. Windows 10 will ping these subdomains hundreds of times an hour, making it challenging to firewall and monitor all of the requests made by the operating system. An attacker can use these subdomains to serve payloads to evade network firewalls.

Using Netcat to backdoor a macOS device has its short-comings. If the compromised Mac goes to sleep, the Netcat background process will occasionally fail to terminate correctly; This leaves Netcat running infinitely in the background and the attacker with no new way into the device. As an alternative, we'll use the lesser-known Tcl shell which can handle abrupt backdoor disconnections.

Identifying vulnerable devices and services on a target router can be difficult without leaving logs and other traces of an active attacker on the network. However, there is a way to covertly decrypt and view Wi-Fi activity without ever connecting to the wireless network.

Welcome back, my novice hackers! You have probably heard of the Panama Papers hack by now. This was a hack of the servers at Mossack Fonseca, a major law firm in Panama. This law firm specializes in assisting the rich and powerful to hide their wealth from taxes and scrutiny by creating tax havens overseas.

One of the coolest features on the Samsung Galaxy Tab is the in-built Readers Hub. It's ideal for reading all of the newspaper, books and magazines within the Android tablet. All you need to do is go to the Reader Hub and start reading! Watch and see how easy it is!

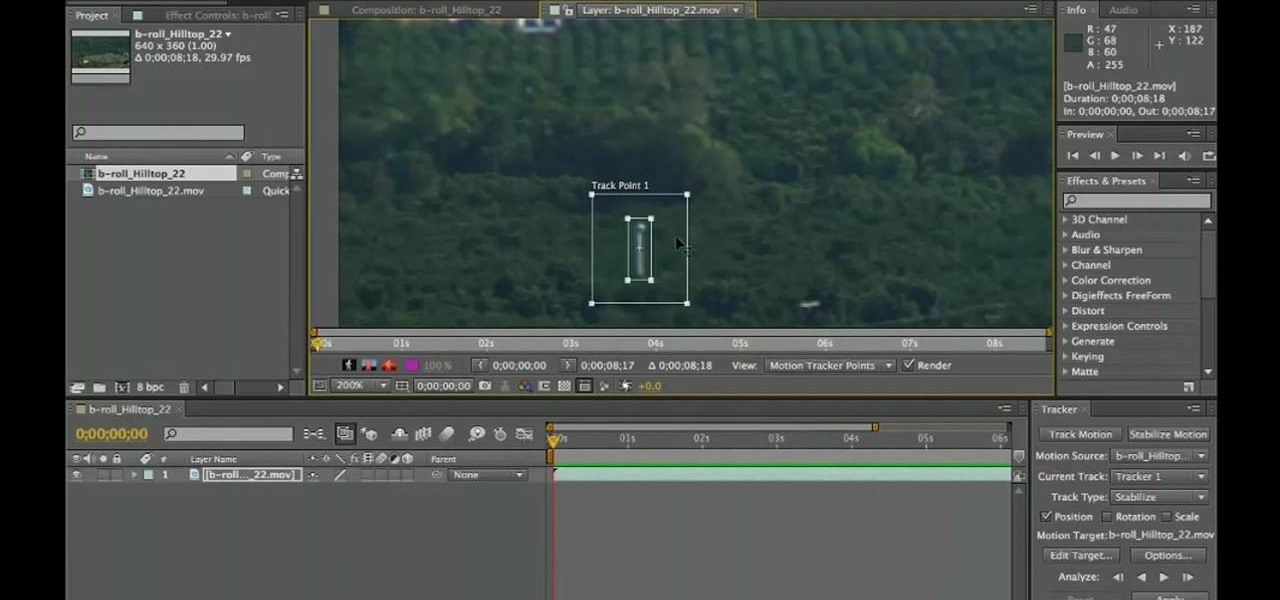
Want to fix shaky video after the fact? With After Effects CS5, it's easy. Whether you're new to Adobe's popular motion graphics and compositing software or a seasoned video professional just looking to better acquaint yourself with CS5's new features, you're sure to be well served by this video tutorial. For more information, and to get started stabilizing sub-ideal clips in your own After Effects CS5 projects, watch this free video guide.

With a manual log splitter, splitting logs doesn't have to be such a chore. But a manual log splitter isn't ideal for every job. In this video, Tim Carter, of Ask the Builder, will teach youu about the manual log splitter and what sort of jobs you can use it for.