There's 6 small techniques to improving traffic on your website via web optimization. Improving your SEO (Search Engine Optimization) is the key to getting traffic to your site, especially a small business that needs to compete online. Lincoln explains 6 small business marketing strategies for improving your web traffic and small business SEO. Watch both parts of this video series.

Well, well, well. Uber, we knew you were investing a ton of money into creating self-driving taxis and flying cars, but what we didn't know is that you were already testing out your driverless vehicles on the streets of New York City.
Many marketers are NOT using this powerful strategy to get free traffic and increase their brand exposure. It's as simple as signing up for a free Gravatar account and commenting on blogs in a similar niche. See some good examples and some bad examples...

Chapter 9 of Enslaved: Odyssey to the West, a nice sunset opening with Monkey and his female companion on a motorcycle speeding down the highway. Classic in almost every way. In this two-part video series you will get a full walkthrough of chapter 9 of Enslaved: Odyssey to the West on hard difficulty on the Xbox 360.

In this clip, learn how to tie up your bait like a pro. You will get step by step advice on tying a traffic jam trico cluster for flyfishing. If you would like to catch the big guys, you will need to use this tutorial to get started.

Hyundai Motor Company says it will launch its driverless tech ahead of schedule, but the Korean carmaker will remain behind mainstream rivals, including General Motors (GM), Nissan, and Honda.

Any truck driver who breathed a sigh of relief when US Secretary of Commerce Steve Mnuchin recently stated that driverless cars "will not affect jobs in a meaningful way for roughly 50 to 100 years" can go back to being anxious about job security again.

Diatomaceous Earth may be useful for killing bugs in walls. Light sockets and phone jacks provide a highway for bugs to travel from one infested room to another or one infested apartment or another. They also function as a hide-out for them during daytime hours, when they might be more visible.

Google Analytics is a state of the art barometer of how a website is doing. With this program you can measure traffic, get statistics and anything else you would like to know about your page. This free service is especially useful to business owners and others who depend on site traffic to stay afloat. So, whether you need it for business reasons or are just curious, check out this clip and get started with Analytics.

With rainfall comes unwanted plant growth in the form of weeds. Here's how to identify and control them. First is Nutsage which has a glossy green leaf, triangular stem and the rhizome sends up new plants whenever you cut away at it. Next is jungle rice which is an aquatic weed, from areas where there is a lot of moisture. It can be identified by it red/purple chevrons. Use herbicide to take them out before they get too large. Next is pigweeds, to get rid of it you can use weed killer or a ho...

This instructional video shows how change traffic lights from red to green, using science, and without actually having to know anything about magnetic fields or properties! Save gas, time, and frustration in your car and during your commute! Works great! See the test results! Yay for Kipkay! The trick in this video hacking tutorial will teach you how to get green lights on your bike or motorcycle that is too small or light to trigger the traffic light.

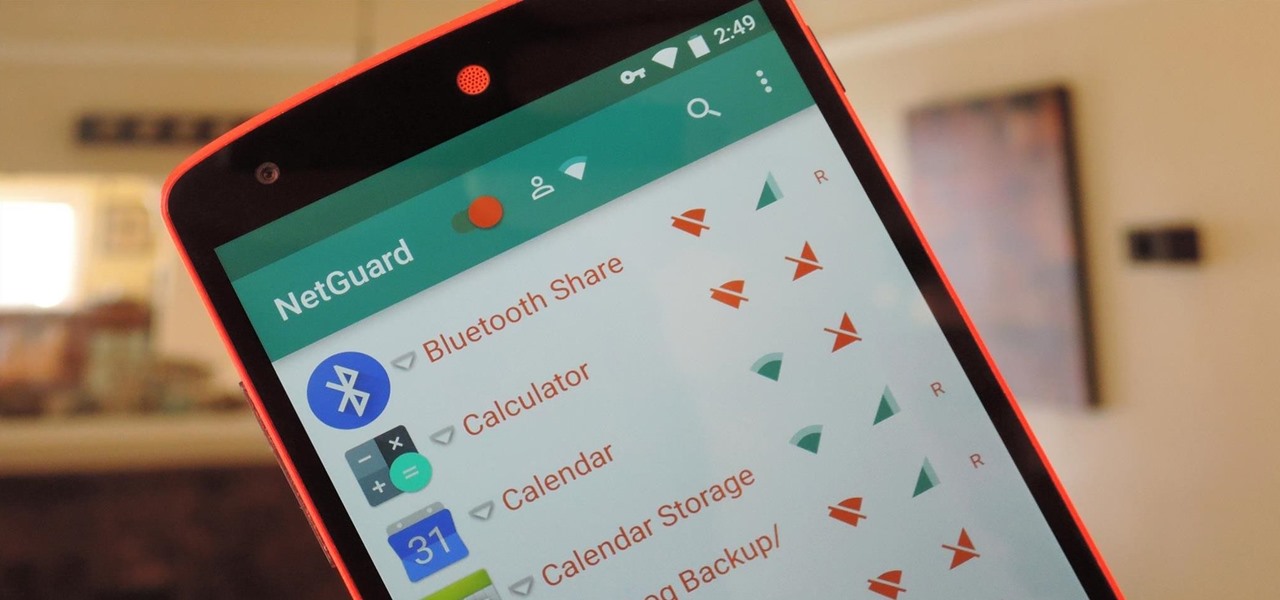
If you exceed your monthly mobile data limit, your cell phone bill can skyrocket pretty quickly. This is why a lot of people vigilantly monitor internet usage and even uninstall apps that use too much background data.

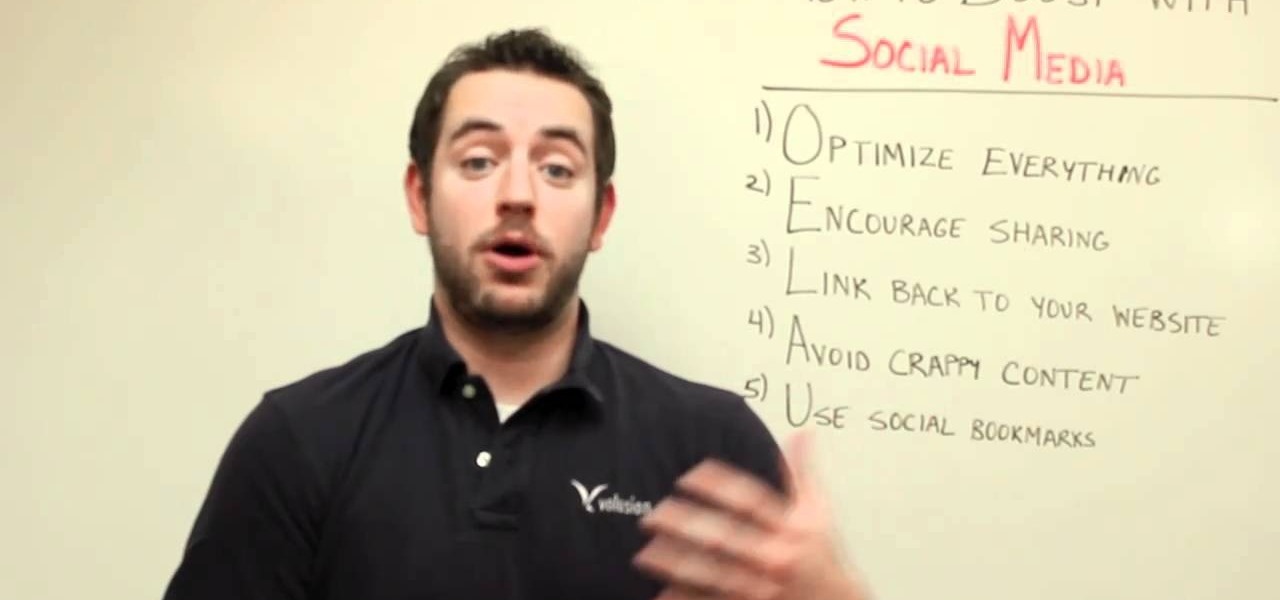
One of the best ways to increase traffic to your web site is to participate in social media. This video will show you how to optimize your social media posts so that they generate the most interest in your site and attract the most visitors.

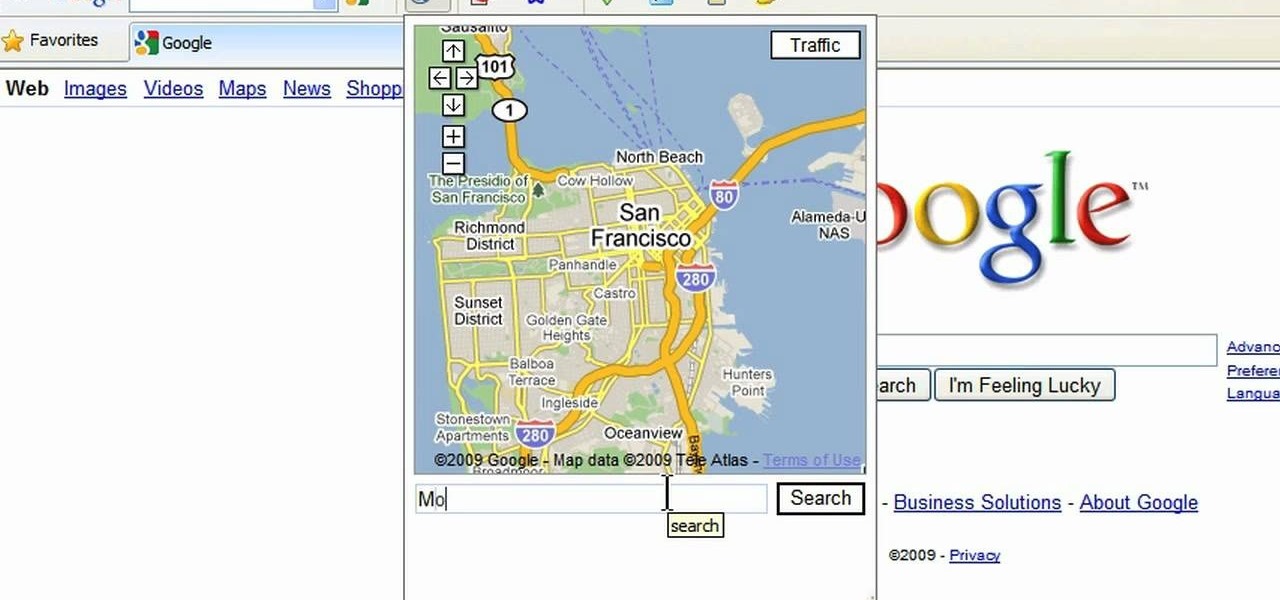
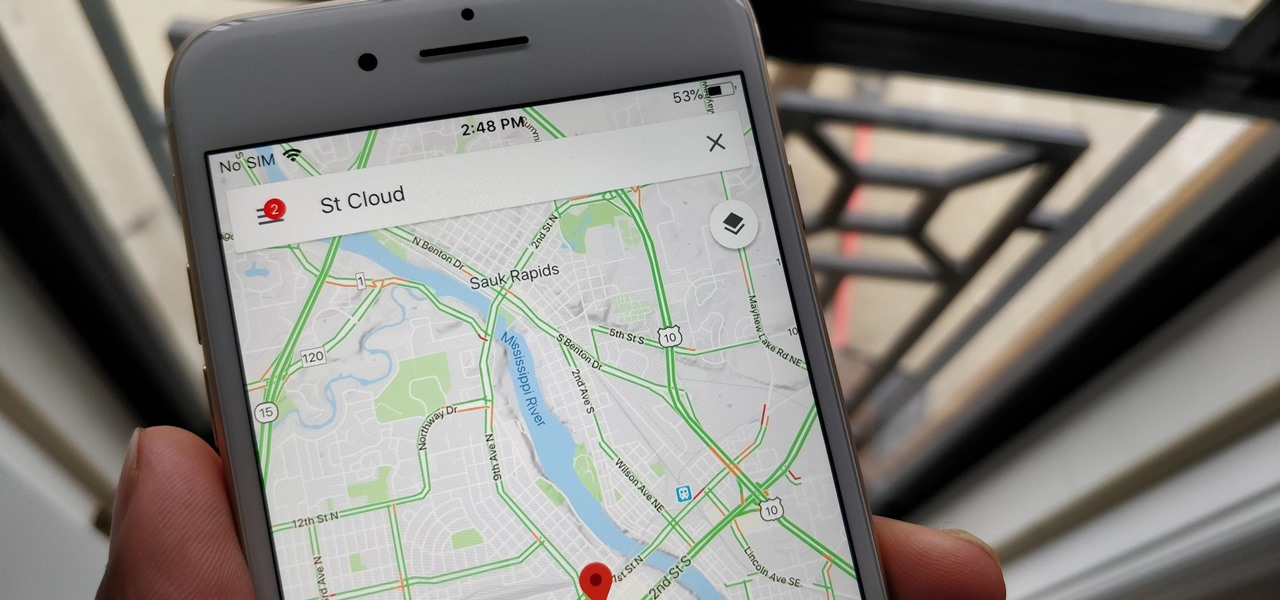
This is a video tutorial in the Computers & Programming category where you are going to learn how to avoid traffic jams using the Google Maps button on the Toolbar. Click on the Google Maps button on the toolbar. This will bring up the maps window. Here you type in the area in the search box, for example, "mountain view, ca" and click 'search'. On the next window click on the 'traffic' button and the map will then show you the roads that are clear of traffic jams in green color. There you go!

This video is a tutorial on how to ride a bike in traffic. The first rule is to obey the law. You would need to follow the laws of traffic as though you were driving a car. If there is a bike lane, use it. It is not a good idea to use the sidewalk as that is reserved for walkers and runners. Ride predictably by signaling your turns. The video tells the viewer which side of the road to ride on, and also provides tips. He also discusses how to ride with another cyclist. This is a very informati...

Hak5 isn't your ordinary tech show. It's hacking in the old-school sense, covering everything from network security, open source and forensics, to DIY modding and the homebrew scene. Damn the warranties, it's time to Trust your Technolust. In this episode, see how to set up SSH tunneling to securely transmit HTTP traffic.

If you're looking to increase the ranking of your website in Google, and so increase your traffic, you'd do well to at least a rudimentary understanding of what Google looks at when considering the relevance of a web page to a given query. This SEO tutorial offers a cursory explanation of how the Google search robot sees, or spiders, your website. Drive more traffic your website with this SEO how-to.

Right out of the box, iPhone is incredibly easy to use. If you want to get the most out of every feature, you’ve come to the right place. This video tutorial straight from Apple will teach you how to use GPS maps and the compass on the Apple iPhone 3G. The iPhone redefines what a mobile phone can do.

For quite some time, Netflix and Verizon have been duking it out, and it seems that things have just a little saltier between the two:

Welcome back, my hacker novitiates! Many of you have probably heard of a man-in-the-middle attack and wondered how difficult an attack like that would be. For those of you who've never heard of one, it's simply where we, the hacker, place ourselves between the victim and the server and send and receive all the communication between the two.

Welcome back, my hacker apprentices! In recent weeks, the revelation that the NSA has been spying on all of us has many people up in arms. I guess I take it all in stride as I just assume that the NSA is spying on all of us—all of the time. Don't get me wrong, I don't condone it, but I know the NSA.

Accidents are the worst. They're costly, time consuming and an all around pain in the butt. Rear-end collisions are among the most common types of accidents on the road. Take these simple precautions to avoid a rear-end collision.

Welcome back, my novice hackers! Previously in my "Spy on Anyone" series, we used our hacking skills to turn a target's computer system into a bug to record conversations and found and downloaded confidential documents on someone's computer. In this tutorial, I will show you how to spy on somebody's Internet traffic.

This video tutorial is about using Google Maps and the features in it. Google Maps help us to find the geography and even the traffic situations of a city. Google maps also provide a street view option that helps us to see how a place actually looks like from the ground. Neither of these views are real time. But now, Google Maps has added in a new option, which is the webcam. Just click on the more option in between traffic and map option. In the list that appears, just tick the webcam option...

Hak5 is at it again, with a plethora of somewhat accessible solutions to your technological problems. If you've ever needed to get through your school's firewall, or secure traffic tunneling, or try out applications in a fast, efficient manner? This video has it all and more.

It's common for IoT devices like Wi-Fi security cameras to host a website for controlling or configuring the camera that uses HTTP instead of the more secure HTTPS. This means anyone with the network password can see traffic to and from the camera, allowing a hacker to intercept security camera footage if anyone is watching the camera's HTTP viewing page.

The Chinese government's tight restrictions on gathering data by foreign firms for 3D mapping, the lifeblood of machine-taught driverless systems, could at least slow down access to the market by Waymo, Tesla, General Motors (GM), Ford, and other players hoping to make inroads there.

The National Transportation Safety Board (NTSB) said it is still investigating the circumstances of a fatal Tesla crash last year to determine if the car or Tesla's Autopilot driverless system was at fault, but revealed more details about the circumstances of the crash.

It's been an exciting week for Tesla. First, Elon Musk offered a preview of the nearly complete Model 3, then China tech giant Tencent invested $1.78 billion in the company. Now, Tesla has officially updated its Autopilot software today for Tesla owners with Autopilot 2.0 hardware.

Yes, you read that right—you can now get Google Maps back on your iPhone again. It may not be officially replacing Apple's notorious Maps app, but it sure is a sight for sore eyes.

In this video, we learn how to use the iPhone map app. First, go to Google Maps and click on the bottom to find your current location. This will show up in a blue button, which you can tap on to find out more information. The map will go in the direction your iPhone is facing and you can zoom in on information about places around you. You can also type in a place you are searching for, and get directions, then save them to your phone if you prefer. The key is the button on the bottom right wh...

I have came across a lot of members on the forum that didn't have a clear idea of what port forwarding is and what it does. So...Let's get started...

Welcome back, my hacker apprentices! I recently began a new series on digital forensics to show aspiring hackers what the forensic investigator can do and see while investigating a cyber attack. This is the second installment in that series and will focus upon network forensics. In other words, what can a network forensic investigator learn about the attacker during an investigation and how.

Ever since the FBI took down the Silk Road and Dread Pirate Roberts last month, many questions have been raised about whether Tor still provides anonymity or not, and if it's now broken. I'll try to address that question here today succinctly from multiple angles, keeping it as simple and plain-language as possible. The Closing of Silk Road

In this tutorial, we learn how to drive traffic to your website using Twitter. To get started, you will sign up for an account and then go to your profile. Start to follow people and have them follow you back as well. If someone mentions your name then all of their followers will see your name and can click on you to see your profile. If you have something interesting on your profile, then they will want to follow you! It's important to have your main website link on your website and a bio wi...

Want to make an Inverted Traffic Light cocktail like a champion bartender? This clip will show you how it's done. With the proper technique, mixing the perfect drink can be easy. So easy, in fact, that this free video bartenders' guide can present an overview of the process in about a minute's time. For more information, including a full list of ingredients and complete instructions on how to mix this drink yourself, take a look.

Collin teaches us how to race at Laguna Seca raceway in this tutorial. When coming out of the pit lane, wait for the workers to wave you on. Make sure there is not traffic around you because you will be doing over 100mph. Once you are sure there is no traffic, turn in the late turn so don't dual apex it as you are turning. By this time you will turn four and then turn five after this on the right hand side of the track. Next, turn six with a small amount of braking bringing the car out and ru...

With the rise of website encryption (TLS), sniffing passwords from network activity has become difficult. However, it's still possible to quietly exfiltrate a target's network traffic in real time to extract passwords and sensitive information. Pertaining to macOS, there are two methods for retrieving traffic from a backdoored Mac.

With over 1 billion downloads on the Play Store alone, Google Maps has become a staple for those traveling. Its popularity is the result of Google consistently improving its accuracy and adding new functionality. And this was only achieved with help of you — specifically, your data.

We all know we shouldn't be using our smartphones while driving. But we also know many people do it anyway. Soon, however, the addicts among us may not have a choice but to kick their habit. A new app announced today by Samsung will block all calls and texts while you drive, stopping those who text and drive right in their tracks.