A hacker with privileged access to a Windows 10 computer can configure it to act as a web proxy, which allows the attacker to target devices and services on the network through the compromised computer. The probes and attacks appear to originate from the Windows 10 computer, making it difficult to detect the attacker's actual location.
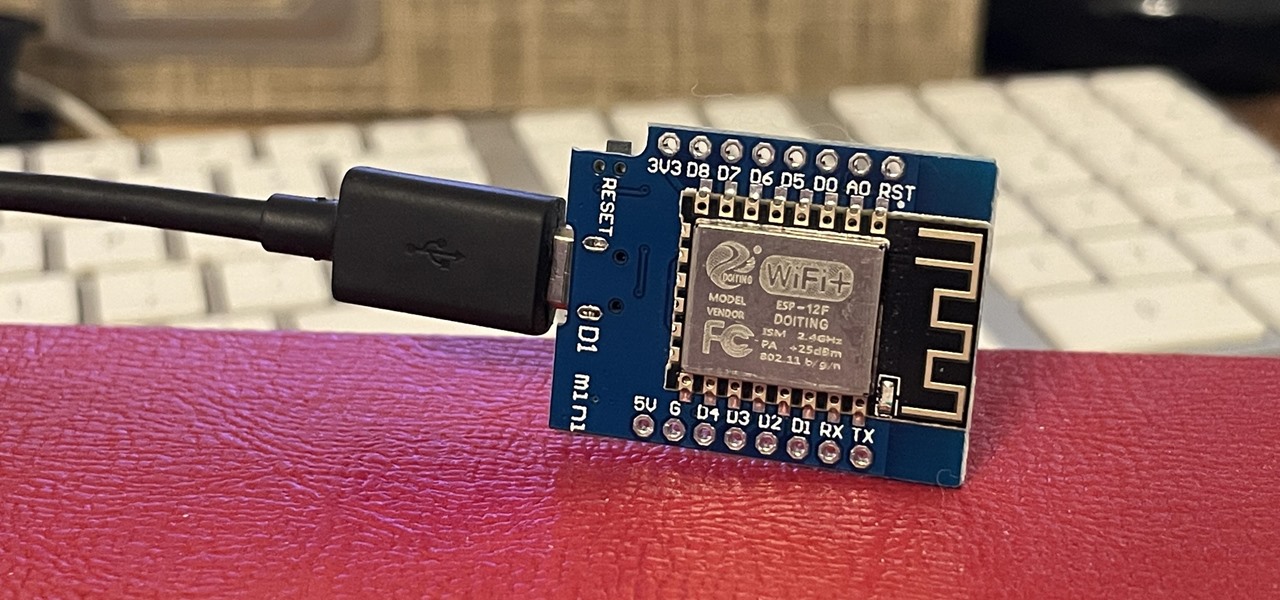
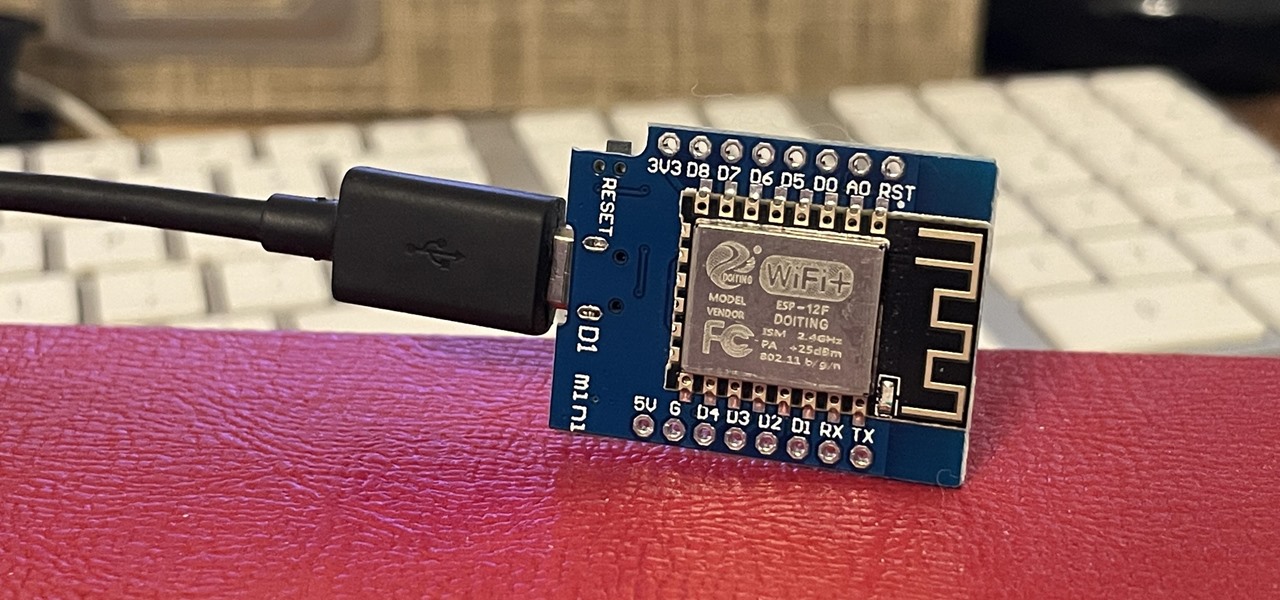
If you've wanted to get into Wi-Fi hacking, you might have noticed that it can be pretty challenging to find a safe and legal target to hack. But you can easily create your own test network using a single ESP8266-based microcontroller like the D1 Mini.

Rumors about the 2022 iPhone series stirred well before the iPhone 13 models were even released. While Apple remains quiet on the next big iPhone, as it always does, we're seeing more and more leaks and reveals for the iPhone 14 series as we lead up to a likely fall release.

Can you name what they all are?
1.) If you do not know something, keep our mouth shut.* No-one, I repeat no-one, is interested in your uneducated guesses about why something is the way it is, or why someone did something a certain way. At best, you will trick them into temporarily thinking you know what you’re talking about. At worst, you will convince them that you are speaking the truth and they will perpetuate your bullsh*t to others. Do not contribute to making the world a more foolish place just because you had to say ...

The battle between first-person shooters is officially underway with the release of Battlefield 3 today. Who will win? Most experts are already declaring Call of Duty: Modern Warfare 3 the champ of the holiday retail clash between EA and Activision, despite MW3 not coming out until November 8th.

Android names each major OS version according to the alphabet, but N presented a dilemma. Sticking with their sweet-strategy, the folks at Google weren't left with many options for the 14th letter of the alphabet. In fact, they even opened up suggestions for the name, asking fans to pitch in their ideas.

Whoa, presenting the world's hugest, tallest, largest Treehouse built by Horace Burgess of Crossville, Tennessee.

Here's something fun for the Null Byte community to do—a coding competition! This week, I wanted to get everyone involved by offering you all a nice library of possible program types to choose from and try to code. At the end of this competition, all of the submitted programs will be reviewed by the community and myself. The coder that receives the most votes will be dubbed THE BEST.

In my Wireshark article, we talked a little bit about packet sniffing, but we focused more on the underlying protocols and models. Now, I'd like to dive right back into Wireshark and start stealing packets.

Since the internet is becoming more and more important all the time in regards to overall marketing plans for many companies, it’s imperative that the company website be up to the task of attracting visitors and converting them into customers. There are many methods and techniques to do this and for that reason it’s usually preferable to hire a company that focuses on online marketing or search engine optimization (SEO) to do this work.

Briefing Playing cards are used to play Killer but Killer is not exactly a card game. You cannot play this game if you do not know how to wink. I do not recommend that you go about winking at men and women to practice for this game.

If you're like me, you were disappointed when NASA cut their human space flight program. No longer could children and adults in dead-end jobs dream of someday walking on the surface of the Moon or drinking floating globules of water through a straw. Homo sapiens as a species are still making it up there, but I will never be one of the chosen ones.