Open-source intelligence researchers and hackers alike love social media for reconnaissance. Websites like Twitter offer vast, searchable databases updated in real time by millions of users, but it can be incredibly time-consuming to sift through manually. Thankfully, tools like Twint can crawl through years of Twitter data to dig up any information with a single terminal command.

There's no doubt Kali has established itself as the most popular penetration distribution available. However, just because it's the fan favorite of beginners and security researchers doesn't make it right for everyone. Manjaro Linux is a beginner-friendly Arch-based distribution which can be easily weaponized with the Black Arch expansion, creating a friendlier first-time Arch experience.

Equifax reported on Sept. 7 that it discovered a breach on July 29 which affects roughly half of Americans, many of whom don't realize they have dealings with the company. Hackers got away with social security numbers, addresses, and driver's license numbers, foreshadowing a "nuclear explosion of identity theft." Let's explore what really happened and what you and those around you can do to protect yourselves.

This holiday season, give yourself a gift that will keep on giving: a new web development skill. Whether it's to secure lucrative freelance work in the new year, bolster your résumé, or have fun with some frankly outrageous discounts on online course bundles right now (up to 99% off), there's nothing better you can do with your free time. Your future (pro coder) self will thank you.

Windows 10 and macOS have poor reputations when it comes to customer privacy and user policies. Our hacking Windows 10 and hacking macOS articles might make it seem like a reasonably secure operating system doesn't exist. But I'm here to tell you that there is a viable alternative that could provide some sense of security and trust.
Kali Linux has come a long way since its BackTrack days, and it's still widely considered the ultimate Linux distribution for penetration testing. The system has undergone quite the transformation since its old days and includes an updated look, improved performance, and some significant changes to how it's used.

Metadata is data about data. Different file formats store extra data about themselves in different ways. This video will cover metadata that can be used during a forensic investigation, namely MS Word doc metadata and the metadata stored in a Jpeg's Exif data. Find metadata in Word docs and jpegs supporting Exif.

PopSci has compiled an amazing list of 30 college labs that would tempt anybody to re-enroll. If you know any high school juniors or prospective grad students, pass this along. They just might reconsider their initial choices.

Virtual autopsies are the wave of the future in forensic medicine, using three-dimensional x-ray techniques instead of hacking through a mess of blood and guts. The Virtual Autopsy Table allows the cause of death to be determined quickly to aid in criminal investigations. Amazing - straight out of Bones or CSI.

Season 5 of Dexter is set to premiere on September 26th, and it's looking bloody as ever. The trailer for the highly anticipated season debuted at this year's Comic-Con. Things aren't looking so good for Dex... Not a fan (yet)? Instructables user Forkable offers a brief synopsis, and more importantly, an edible party favor for your upcoming premiere party.

Who dunnit? Forensic pathology is an art form we take for granted. Scientists are busy debating why a 5' 5", 5300-year-old man coined Otzi was murdered.

By now, many of you may have heard about iPhone tracking and recording your location data, but is there anything else being extracted from cell phones without our knowledge? If you're a Michigan state resident, the answer is an alarming "maybe".

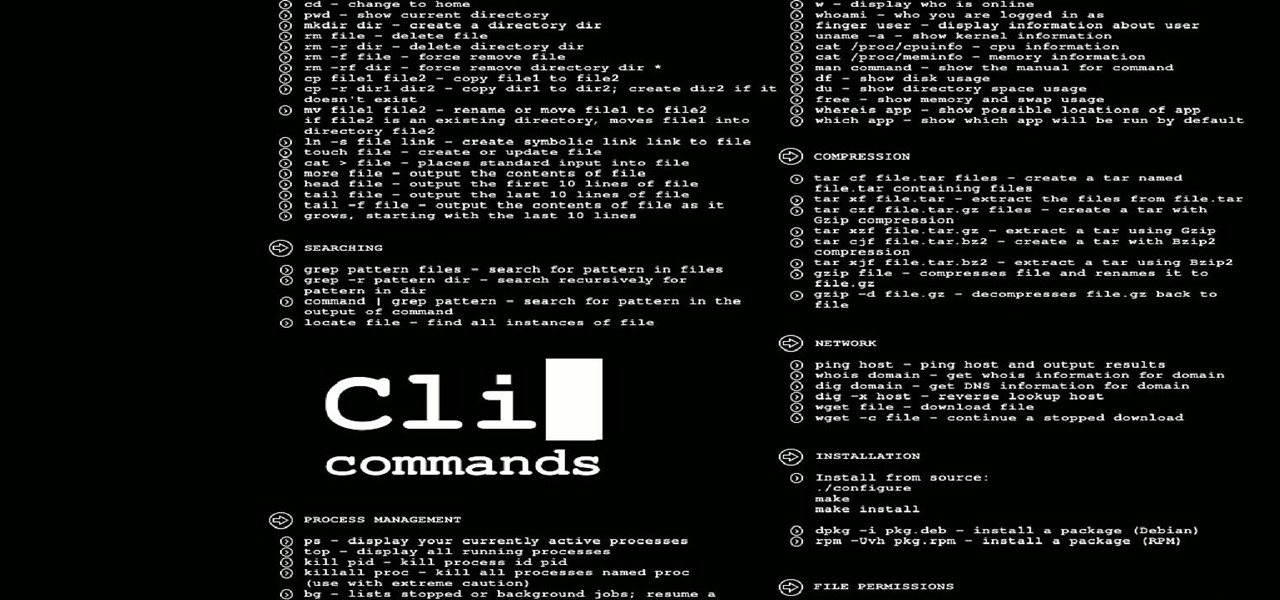
Hello everyone on null byte this is my first tutorial This Tutorial Is on Useful Lesser Known Commands on Linux

Some cops already have the ability to extract data from your cell phone using handheld forensic devices, but soon police officers will have a new mobile data collection toy to play with—an Apple iPhone. Actually, it's an iPhone-based device that connects directly to the back of an iPhone, which is designed to give law enforcement an accurate and immediate identification of a suspect based on their facial features, fingerprints and even their eyes.

Dactyloscopy isn’t going anywhere. Forensic science has much relied on fingerprinting as a means of identification, largely because of the massive amount of fingerprints stored in the FBI’s biometric database (IAFIS), which houses over 150,000 million prints. And thanks to the departure of messy ink-stained fingertips, biometric analysis isn’t just for solving crimes anymore.

In 2007, Nintendo introduced the world to motion control video games with the Wii. Microsoft and Sony built on Nintendo's phenomenal success and released their own motion control products for the XBox 360 and Playstation 3 late in 2010: the Kinect and the Move. The Move is basically an improved Wiimote that looks like a sci-fi Harry Potter wand, but the Kinect just might be the most important video game peripheral of all time.