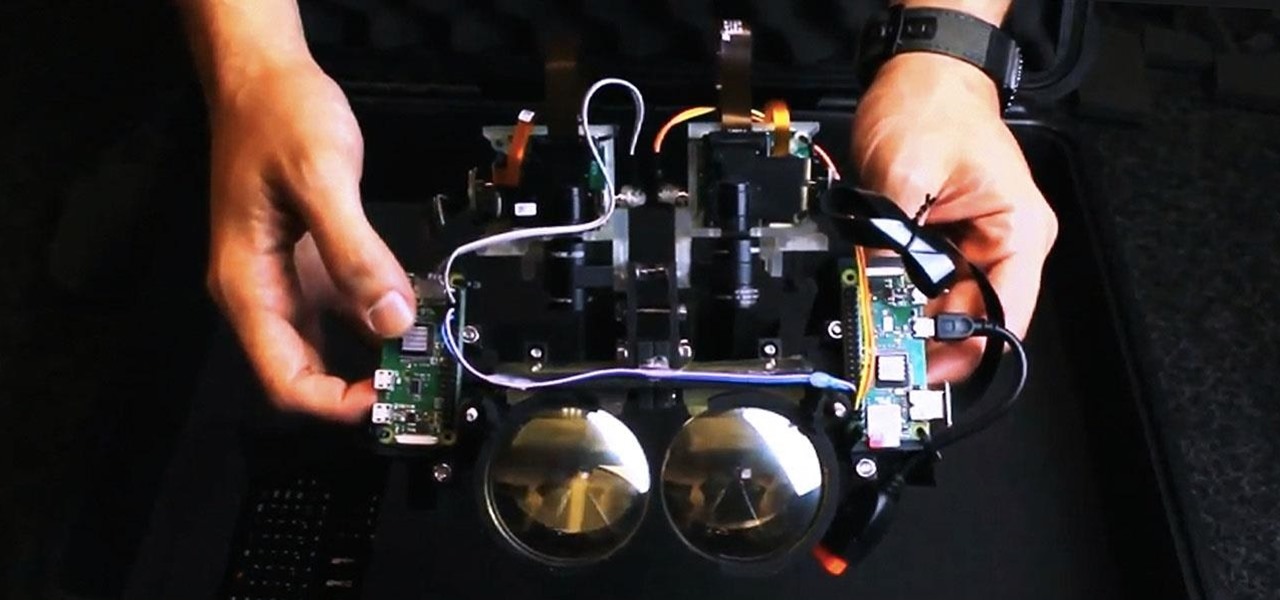
With all the hype around Magic Leap's recent launch, it's easy to forget that augmented reality hardware is still very much in its infancy. While we marvel at what is available now, researchers are still finding ways to design and produce more sophisticated components for next-generation wearables.

As you're surely aware, your phone can be used against you. Thanks to our cameras and microphones, a clever hacker can obtain access to your device and invade your privacy. But spying isn't limited to just these two sensors — gyroscopes, proximity sensors, QR codes, and even ads can be used to paint a very clear picture about who you are and what you're currently doing.
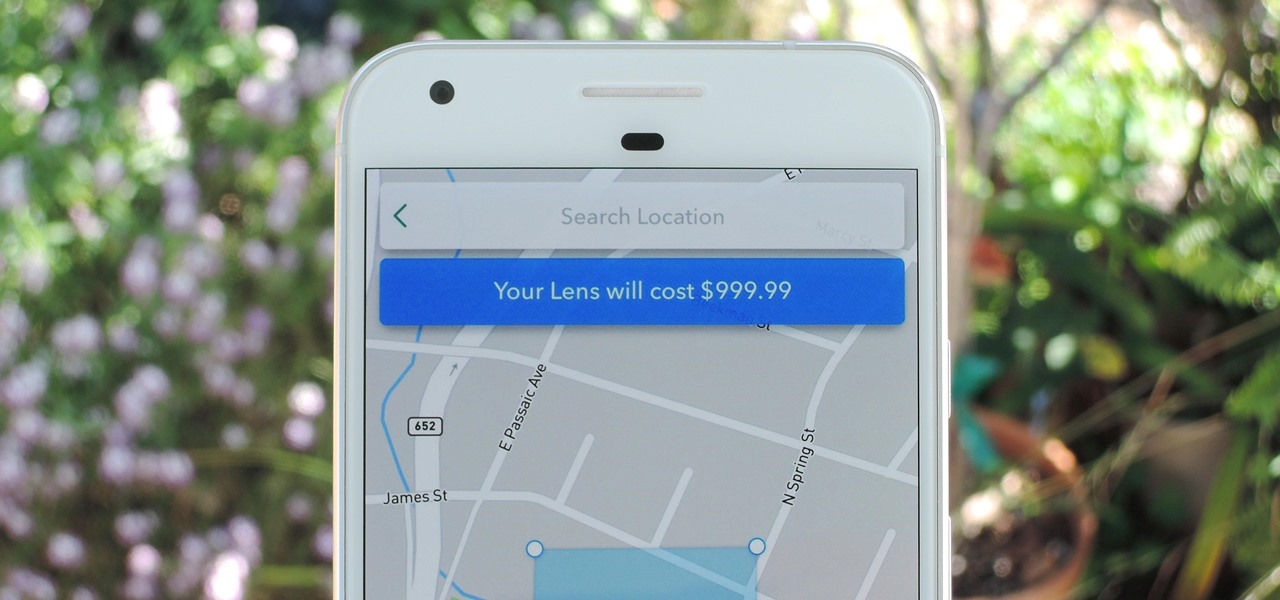
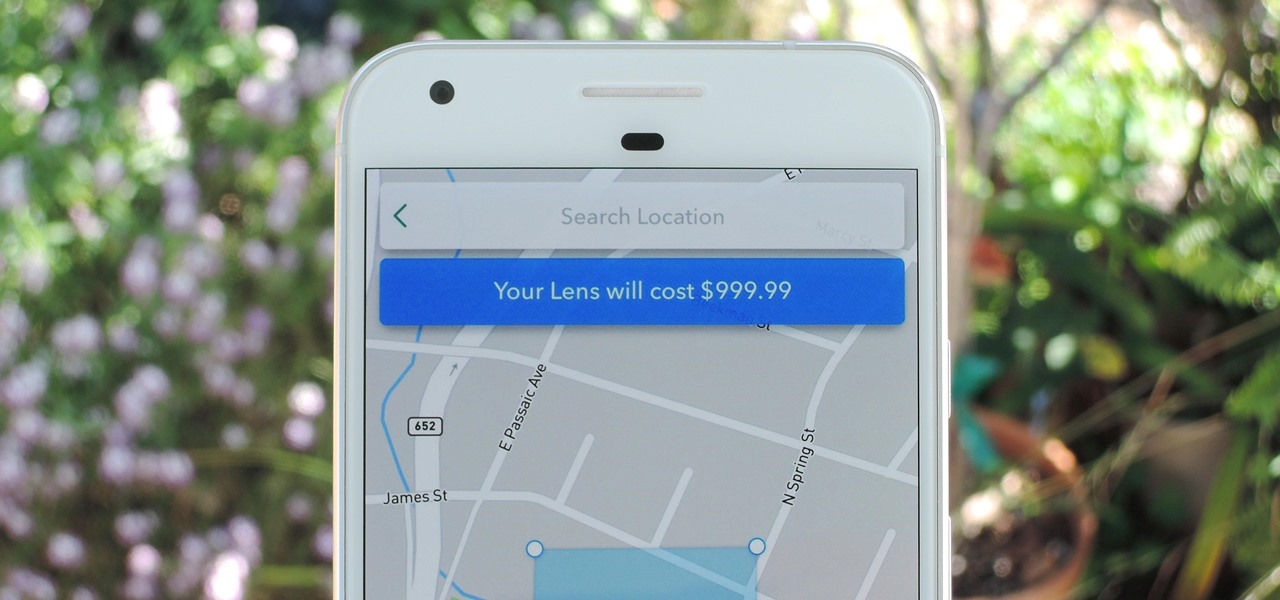
Snapchat just rolled out a feature that lets you create custom Filters and Lenses. While the average Geofilter won't run you more than a few bucks, it's not that hard to exponentially jack up the price. Amazingly enough, Snapchat's latest attempt to monetize their platform can ultimately cost you as much as $999.99. Ignore the penny, let's call that a cool grand.

When hacking Wi-Fi networks, having the right wireless adapter is essential. But hunting online for one can be a frustrating experience. To see how the handful of Kali-compatible adapters on the market measure up, I ran a series of tests to benchmark and compare their range, signal strength, and ability to enter monitor mode and perform packet injection. This should help you determine which adapter is right for your own hacking needs.

Honeywell recently completed successful testing of virtual window technology that enabled drivers to maneuver an otherwise windowless combat vehicle on rough terrain at speeds exceeding 35 miles per hour.
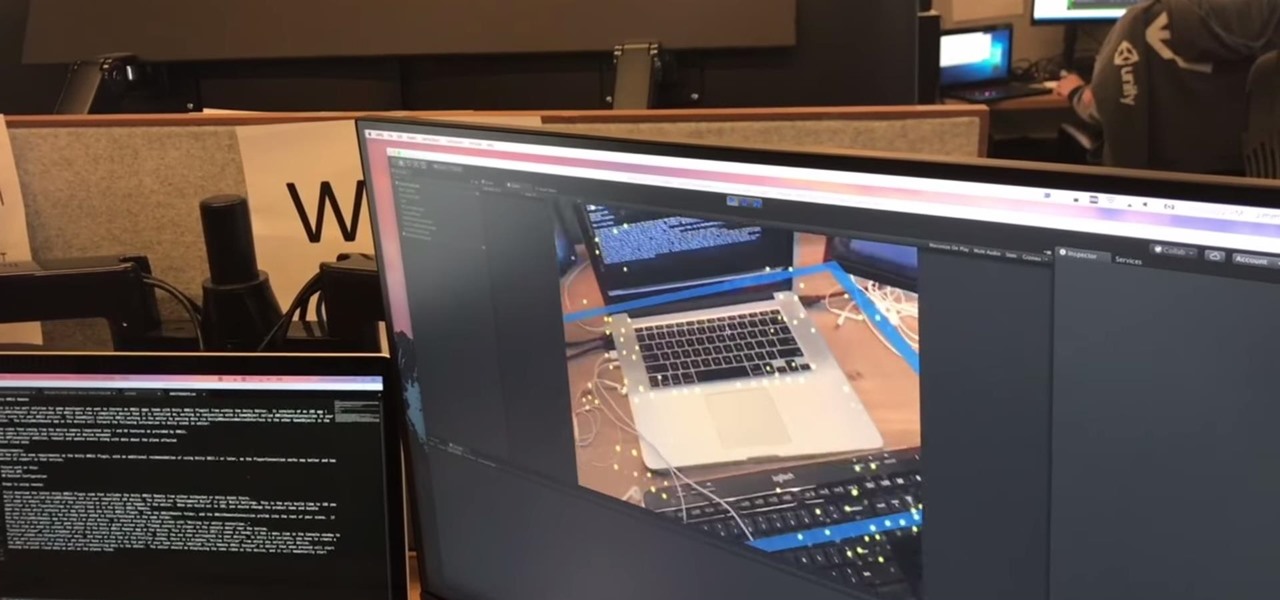
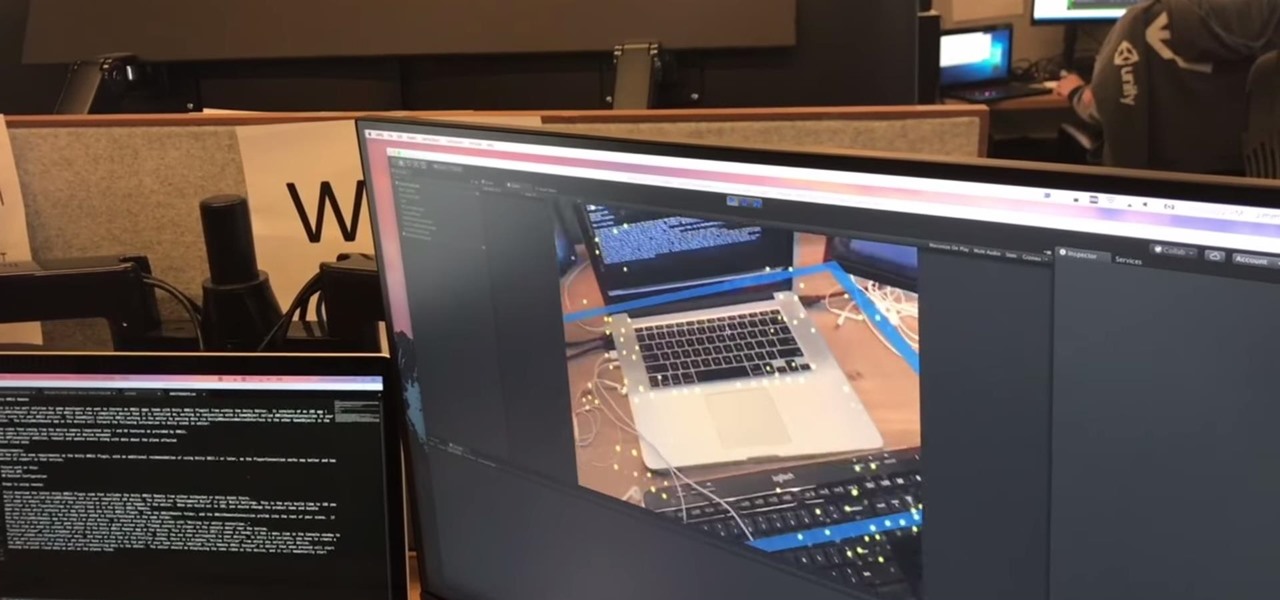
In an early morning blog, Jimmy Alamparambil of the Unity team announced a major new update to their ARKit plugin. Developers now can use Unity and ARKit to create AR experiences and test directly from Unity's editor, without deploying to the device.

Social engineering makes headlines because human behavior is often the weakest link of even well-defended targets. Automated social engineering tools can help reclusive hackers touch these techniques, but the study of how to hack human interactions in person is often ignored. Today, we will examine how to use subtle, hard to detect persuasion techniques to compromise a human target.

Kuru is called the shaking disease, its name derived from the Fore word for "to shake." Caused by an organism that infects the part of the brain that controls coordination, people afflicted with kuru shake uncontrollably.

In response to the flurry of doubtful headlines about Magic Leap today, set off by an unflattering article from The Information, Magic Leap CEO Rony Abovitz released a short blog post quickly detailing what to expect from the company over the next year. The gist comes down to this: big things are happening in 2017.

Hello everyone! Hope everyone having good day!! I wanted to share an easy way to locate an appropriate exploit from the EDB, get it compiled, and run it all from inside the terminal.

To say we're a nation of coffee-lovers is putting it mildly. Americans consume 400 million cups of joe in one day alone, but how well do we actually know our morning BFF? We know it comes from a bean, and that more coffee drinks exist than there are ways to skin a pig, but what else?

Having your phone ring loudly in a quiet environment could be potentially embarrassing for you, but also quite annoying for everyone else that didn't forget to put their smartphone on silent. Whether it's in class, at work during a meeting, at the library, or a movie screening—you can bet that someone's phone is going to ring loudly, pissing some people off. You don't really want to be that douchebag that interrupts a movie or the middle of a lecture with their annoying ringtone just because ...

Learn to Zoom to page, drawing, selection, previous, 100% and scale by numerical factor using zoom tool in Xara Web Designer. The zoom to page option is great for when you need to see all the web design elements that are shown on your web page at once.

How to adjust a sliding door. Sliding doors are great when they are sliding but can be a real pain in the bum when they don't. Today's video will concentrate on adjusting the wheels to help alleviate some of these annoying issues. It doesn't matter if it's a robe sliding door, a closet sliding door, a glass sliding door or a patio sliding door, the principle is still the same. Obviously there can be other factors like the sliding door track or the sliding door wheels being in a state of disre...

People fundamentally distrust magicians. And they should. The illusions they proffer are just that, illusions meant to astound rather than tangible interactions and results that have weight and meaning in our real world. Our lizard brains know this, and, no matter what the outstanding feat of "magic" presented, we nevertheless hold fast to our survival-based grip on the truth: we just saw simply "can't be real."

So you've been playing Call of Duty Mobile for some time but can't seem to get MVP at the end of the battle. Well, since the game is a competition of players and bots, you're in an uphill battle. But you don't have to languish at the bottom. With the help of these tips, you might just nab your first MVP.

It's easy to have your password stolen. Important people like executives, government workers, journalists, and activists face sophisticated phishing attacks to compromise their online accounts, often targeting Google account credentials. To reduce this risk, Google created the Advanced Protection Program, which uses U2F security keys to control account access and make stolen passwords worthless.

Smartphones are inherently bad for privacy. You've basically got a tracking device in your pocket, pinging off cell towers and locking onto GPS satellites. All the while, tracking cookies, advertising IDs, and usage stats follow you around the internet.

The top five apps of the 2010s were all social media apps of some kind, and the fact that's not surprising to you says a lot. We may use them for other reasons here and there, but our phones are social media machines at their cores. The thing is, some make better machines than others.

Following on the heels of the announcement that ThirdEye's Gen X2 MR glasses began shipping in September, ThirdEye has revealed it has developed an app that helps soldiers aim their weapons during battle situations.

It's finally out. After months of testing, iOS 13 is available to install on your iPhone, which means over 200+ new features you can use right now. The update, released on Sept. 19, can be installed over the air or from a restore image using iTunes in macOS Mojave and older or Finder in macOS Catalina. Ditto for the 13.1 update issued on Sept. 24.

A company whose sole product line is smartphones might be worried about early proclamations that the smartphone is dead with the advent of augmented reality wearables.

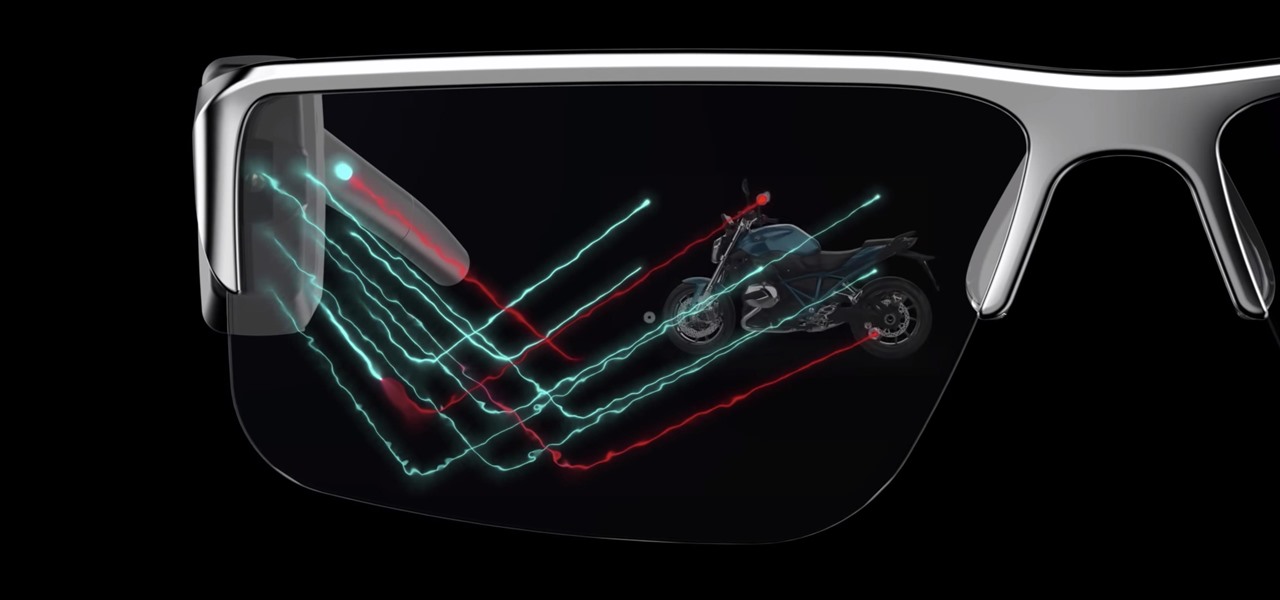
Smartglasses are the future of augmented reality, and Samsung is betting on waveguide maker DigiLens to emerge as a leader in the growing AR wearable industry.

In just a few weeks, on May 29, the annual AWE (Augmented World Expo) conference will take place once again in Silicon Valley (Santa Clara, California, to be exact).

Despite the hype and potential of immersive computing, the augmented reality industry is showing that it is not invincible, as another AR hardware maker, this time Osterhout Design Group (ODG), is reportedly going out of business.

Designing and manufacturing waveguides for smartglasses is a complex process, but DigiLens wants us to know that they have a software solution that partially solves that problem.

A sizzle reel just released by augmented reality cloud company 6D.ai shows off what kind of hyper-realistic AR experiences developers can build with its SDK.

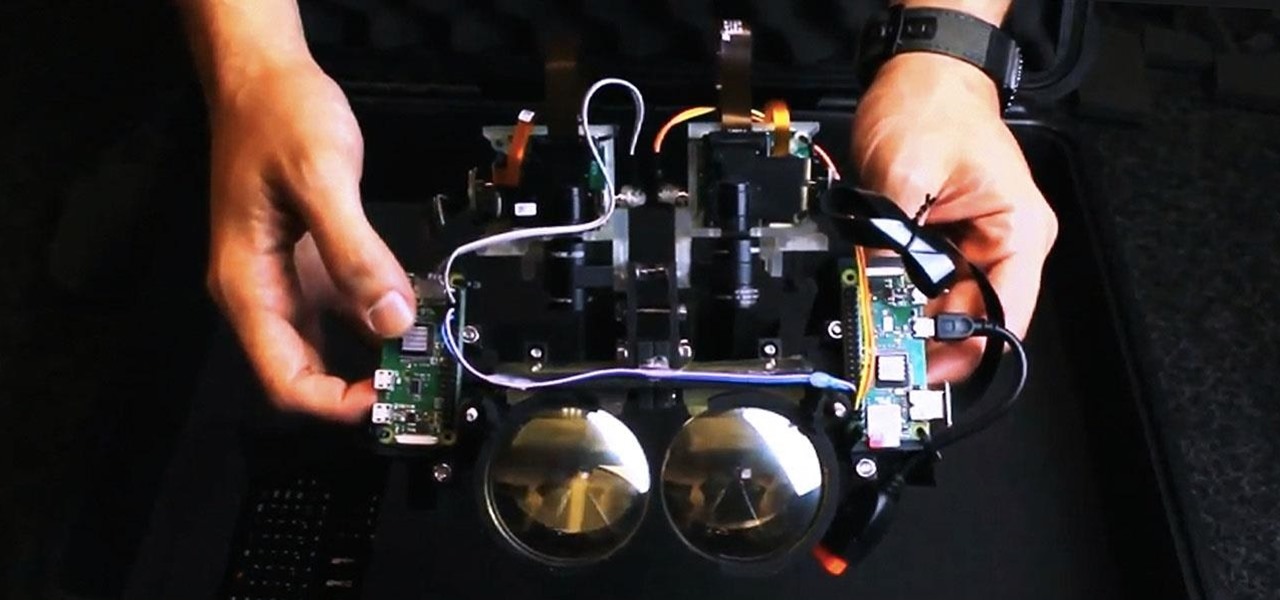
The display is one of the most critical components in augmented reality hardware, and on Tuesday, one of the companies making that component, Avegant Corp., closed a funding round of $12 million to support development of next-generation AR displays.

Augmented reality experiences created in Lens Studio now have a permanent home in the Snapchat app. On Tuesday, Lens Explorer will begin giving users access to a scrollable screen full of a variety of new Lens Studio creations.

Less than two months after launching its augmented reality platform for casual gaming and shared experiences, Snapchat is ready to make Snappables available to advertisers.

When you first update to iOS 12 on your iPhone, notifications on the lock screen and in the history will be grouped automatically into stacks based on a variety of factors for each app. For example, articles from Apple News will be stacked together based on sites. But you can also change this so that all alerts from a particular app will be grouped in one bundle, not separate ones.

The Android version of Google Chrome only shows a home button on some devices. Unfortunately, this feature isn't available to all Android phones due to several factors. But thanks to a simple workaround, you can now enable this button and set a home page regardless of what device you have.

As advanced as the Galaxy S9 is, it can still be susceptible to the occasional hiccup. Several factors can cause your smartphone to behave erratically or become unresponsive, such as buggy apps or updates that didn't properly install. Luckily, most of these issues can be easily resolved with a press of a button — or two, to be exact.

Rabbit ears and dog noses are fun and all, but Kay Jewelers is here to class up Snapchat.

According to a new study from the Reuters Institute and the University of Oxford, people are getting their news from ... unexpected sources. Put away your CNN app and stop checking the New York Times because a familiar app is now keeping you up to date on current events: WhatsApp.

Traces of bacteria at a precinct in East Harlem created an all-out scare after doctors diagnosed an NYPD officer with Legionnaires' disease, a deadly infection caused by Legionella pneumophila.

When you think of high quality music, your phone isn't the first thing to pop into your mind, even though 68% of US smartphone owners stream music on a daily basis. Most of us tolerate the audio quality from our devices simply because music is something we can't live without — but we shouldn't have to put up with poor quality, and as it turns out, we don't.

While music may not technically be a "universe language," it is the one language listened to by all. There are over 1,500 music genres today—rap, classical, rock, jazz, trap, hip-hop, house, new wave, vaperwave, charred death, nintendocore... and the list goes on. And if you're like most people, you now probably listen to the majority of your music on your phone.

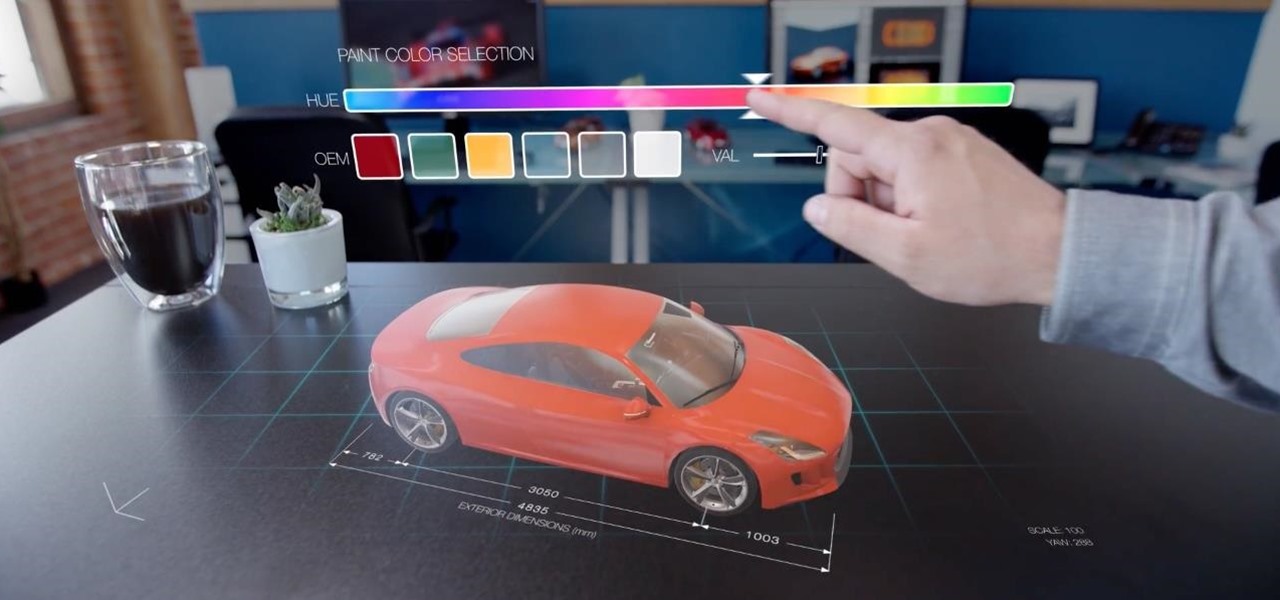
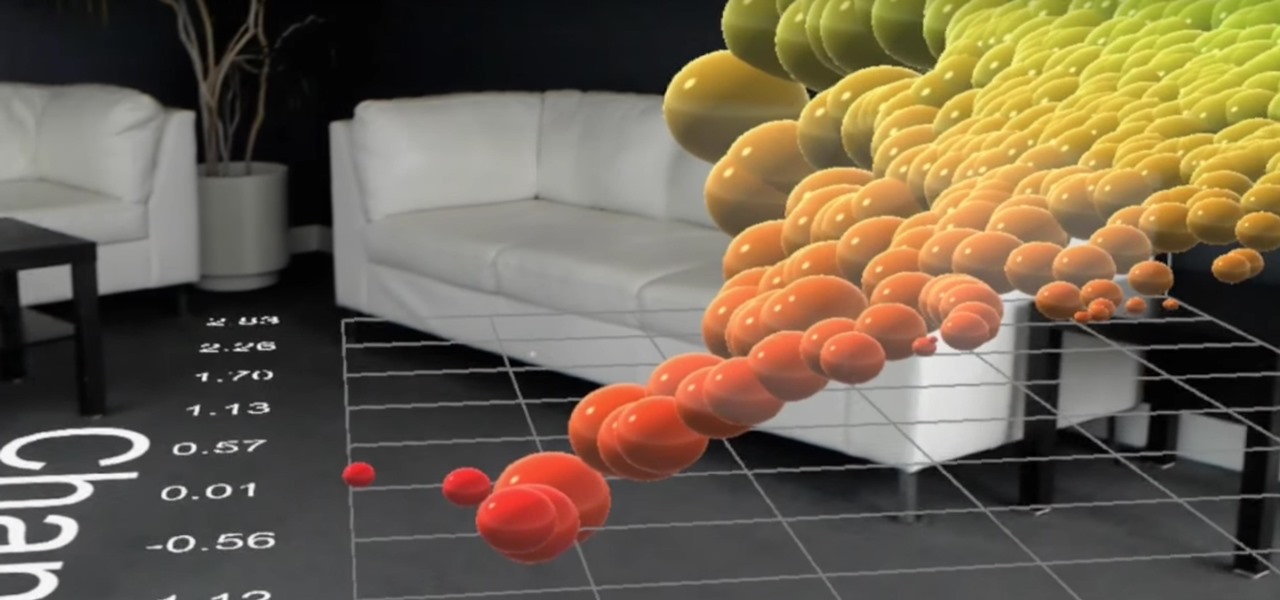
HoloLens developer Michael Peters of In-Vizible has released quite a few videos since receiving his HoloLens last year. Many of his experiments are odd and funny, but some include serious potential approaches to data visualization. In the videos embedded below, you'll specifically see stock market information beautifully rendered in different ways to help understand the data.

When it comes time to buy a new smartphone, the sheer amount of options on the market can make you feel overwhelmed. There are Android devices of all shapes and sizes with different functionalities and price points, and now, even Apple has three unique iPhone models to fit various budgets.