Shodan calls itself "the search engine for internet-connected devices." With so many devices connected to the internet featuring varying levels of security, the special capabilities of this search engine mean it can provide a list of devices to test and attack. In this tutorial, we'll use Python to target specific software vulnerabilities and extract vulnerable target IP addresses from Shodan.

NOTICE: Ciuffy will be answering questions related to my articles on my behalf as I am very busy. Hope You Have Fun !!!

This time it's serious. Really. The largest web security vulnerability of all time went public on Monday, April 7th, 2014, resulting in widespread panic throughout the Internet as system administrators scrambled to secure their websites from the OpenSSL bug known as Heartbleed.
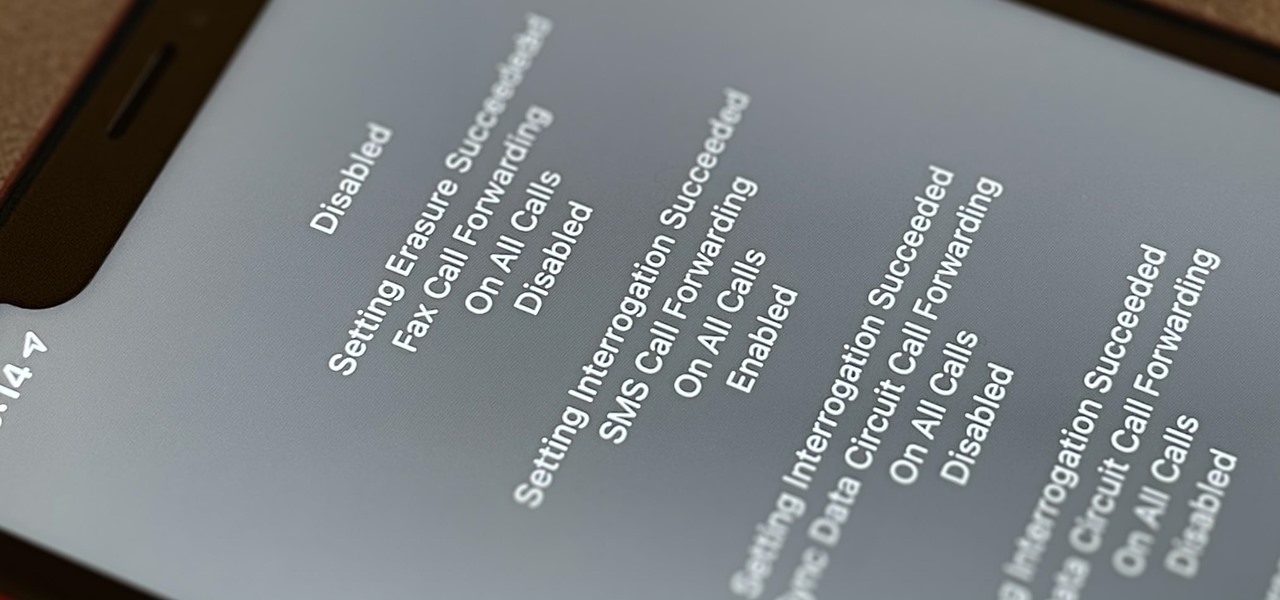
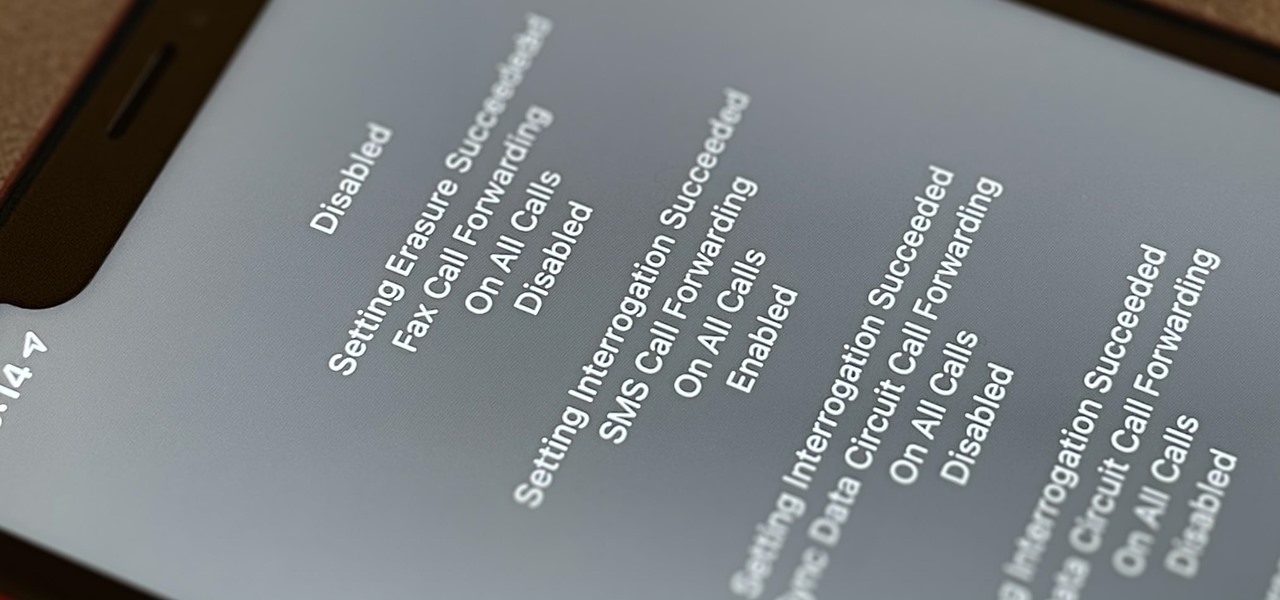
Malevolent hackers can divert your incoming calls and texts to any number they want, and they don't need to be a criminal mastermind to do it. Even friends and family members can reroute your incoming calls and messages so that they know exactly who's trying to reach you, and all it takes is seconds of access to your iPhone or wireless account. These secret codes can help uncover them.

As a hacker, the final stage of exploitation is covering their tracks, which involves wiping all activity and logs so that they can avoid being detected. It's especially crucial for persistence if the target will be accessed again in the future by the attacker.

Cases and stickers are always great, but they aren't the only way to customize an iPhone. The software on your device is full of customization options, from a better-looking home screen and cooler lock screen wallpapers to app icon changes and a system-wide dark mode. There's literally over 100 ways to make iOS on your iPhone genuinely unique, some of which are hiding in plain sight.

Follow along with this Terraria gameplay video to learn how to walk through walls in Terraria. Walking through walls is impossible you say? Let this video show you how to do it in Terraria by exploiting a glitch in the game.

Ever wonder how you get debug mode in the classic Sonic and Knuckles game? It's not directly possible, but, by exploiting a class 7 bug (very severe as it'll crash the game) with Sonic 3 & Knuckles, you can. There's only one requirement: you've obtained all the emeralds and have the ability to transform. Take a look at this instructional video and learn how to get this mode in the game.

Check out this science video tutorial on how to apply a C. elegans dopamine neuron degeneration assay for the validation of potential Parkinson's Disease genes.

With the recent release of both Watchmen and X-Men Origins, convincing a drunken buddy at the bar that you've got slightly super human lifting abilities isn't completely out of the question.

Null Byte is looking for moderators! In today's Null Byte, we're hacking Netflix. As most of you know, Netflix is a subscription service that streams movies and TV shows to your devices over the internet. A common stance amongst my Xbox Live friends is that Netflix isn't worth the cost. The instant movies predominantly consist of old titles, and new movies aren't added often enough.

Security awareness seems to be a hot topic these days on the web, with developers making apps and devices that can hack networks and machines with just a few clicks. But these applications aren't only exploiting security flaws in systems and networks, they're being used by amateur and wannabe hackers who want to have a little fun, but don't want to learn how to actually "hack" anything.

Meet Newstweek, a hidden device engineered to hack news items being read at public WiFi hotspots (cafes, libraries, airports, etc.). Both nefarious and tech-saavy, the ingenious mechanism wasn't fathered by a group of web hackers, but rather a pair of Berlin artists, Julian Oliver and Danja Vasiliev. The duo are interested in exploiting the "trustworthiness" of big media outlets in order to demonstrate the vulnerability of relying on just a few dominant networks.

If you're a believer in the power of logic, may as well skip the game tomorrow. Two math professors at the University of London have supposedly determined who will win the World Cup, and have displayed their findings as a sophisticated infographic:

Uproxx recently posted a guide to making popular YouTube video, and I have to say, I'm not surprised that the models of success include web culture faves such as babies, cats and zit popping.

If you saw my last tutorial on retiring early and wealthy, you now know how anyone can invest a small amount of money over the course of their life, and by exploiting compound interest, achieve an extremely comfortable and easy going retirement. In Part 2, we are going to dive into something a little more risky: Tax liens.

The already robust and ingenious Nmap tool has received a whole slew of new scanning scripts that can be used to do all sorts of naughty endeavors. Notably, the SQLi module, since it is a necessary evil that we must cover here at Null Byte. This major update is going to fuel today's lesson.

The very people this humanitarian mission seeks to help are outraged at the portrayal of their problems and lands. In my previous post, I talked about how this new internet sensation is most probably a hoax designed to force us into a new war. Guess what? It was.

Only so much data can be passed through the network and to your computer's networking interfaces. This is limited by the amount of bandwidth you have. The more bandwidth you have, the faster your network connections will be. Not only this, but your transfers will be more parallel and distributed so that all of your speed isn't taken up by one transfer. When all of your bandwidth is sapped and unable to be used, this is called a denial of service, or a DOS.

This morning, I received a message from a friend who was reading a hack log, and she had some questions about the commands used. This got me thinking, as Linux has a ton of commands and some can be archaic, yet useful. We are going to go over everything you need to know to read a hack log and hopefully implant the steps in your head for future use.

Pull up outside any construction site and you'll see tools scattered about—hammers, jigsaws, nail guns, hydraulic pipe benders—these are the tools of the trade. You would be hard-pressed to build a home or office building with just your hands! On that same page, security professionals also have their own go-to tools that they use on the job site, only their job site is your server.

Hello, everyone. My friend and I recently released a Defense of the Ancients (DotA) map that went viral and thought I should share it with Minecraft World on WonderHowTo since you guys helped me out when I first started making videos! We were featured on Kotaku, RockPaperShotgun, Gamespy, The Verge, Joystiq and many more websites!Exciting!You can see the full details below are head straight here for the downloads.

Big brother is watching when you're playing around on another system—and big brother is that system. Everything from operating systems to intrusion detection systems to database services are maintaining logs. Sometimes, these are error logs that can show attackers trying various SQL injection vectors over and over. This is especially so if they are using an automated framework like sqlmap that can spam a ton of requests in a short time. More often than not, the access logs are what most amate...

Remember that scene in The Matrix when Trinity uses a realistic Nmap port scan, followed by an actual SSH exploit (long since patched) to break into a power company? Well, believe it or not, but that scene is not far fetched at all. If you want to exploit vulnerabilities and root boxes, you'll need to learn how to perform the necessary reconnaissance first. In fact, you will spend far more time researching your target then you will exploiting it. In this article, I am going to show you the fi...

This is a two-part series to locking down the computer to provide maximum protection. Even though this guide will sound intrusive, we are talking about reality here. Extreme measures must be taken to protect our computers, especially when we have confidential documentation or do internet banking, which many people do. We all have to use electronic devices at some stage, whether it be for business or personal use.

The DIY industry is booming, despite the desperate blackmailing of society by finance capitalists. Companies like Adafruit and Makerbot are grossing well over a million dollars a year, and Evil Mad Science Laboratories just recently dedicated themselves to running a full-time kit business. Making kits is fun, but starting a business can be scary. If you already enjoy making gadgets and want to take the plunge into selling your own kits online, this article is for you.