It's universally known that broccoli, kale, Brussels sprouts, cauliflower, and all cruciferous vegetables (also known as brassicas) are good for you—but you probably don't know exactly how good they really are.
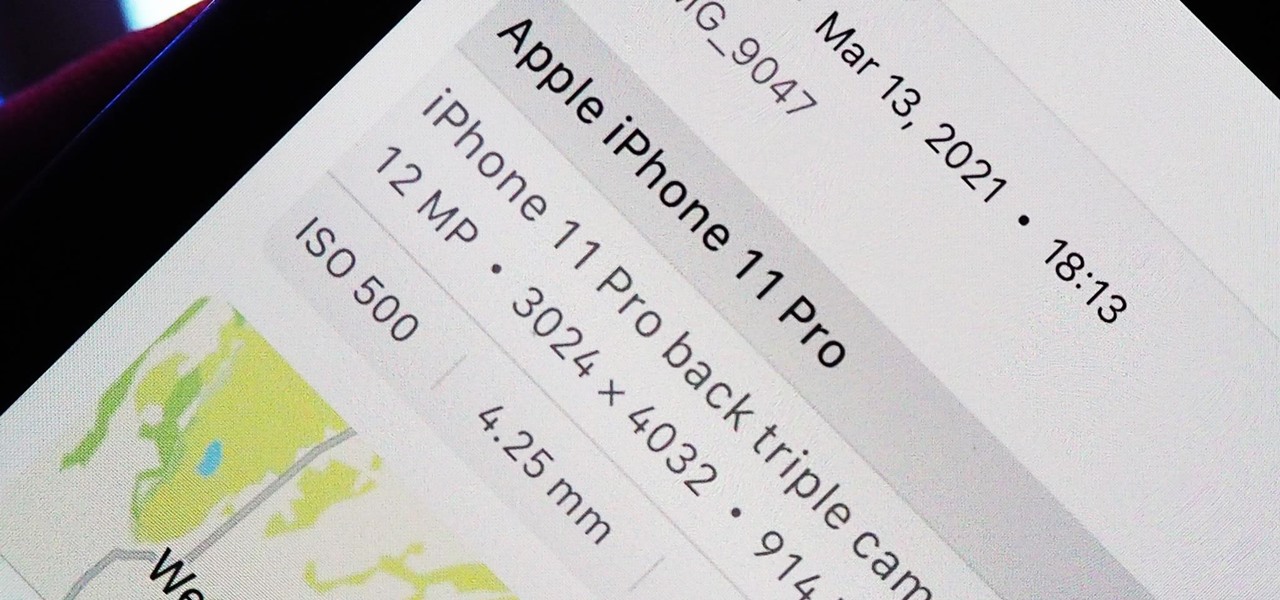
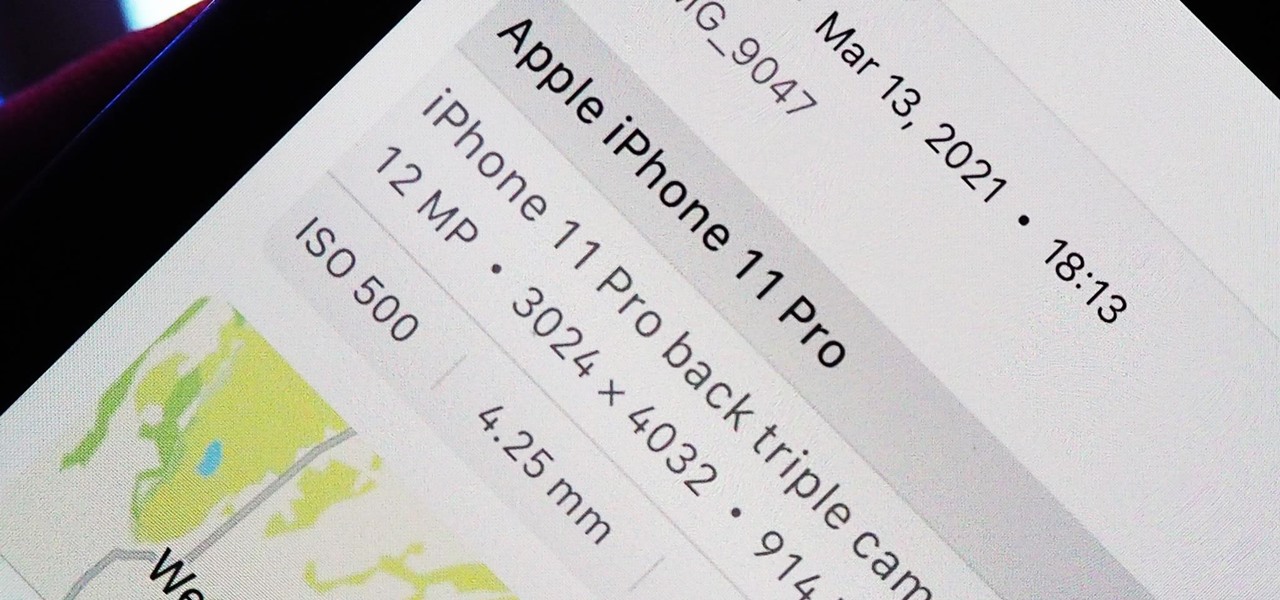
Apple introduces several new privacy settings with iOS 15, including the ability to better manage the metadata in your photos. With just a few taps, you can effectively spoof a photo's geolocation and change its creation date and time, providing a sort of disguise over your personal information. If you constantly take and share photos, it's a welcomed feature, but its results are not permanent and can be reversed.

With an inconspicuous Android phone and USB flash drive, an attacker can compromise a Windows 10 computer in less than 15 seconds. Once a root shell has been established, long-term persistence to the backdoor can be configured with just two simple commands — all while bypassing antivirus software and Windows Defender.

It's the icing on top of your cake (or whipped cream on top of your Android Pie) of despair. You may have not had the easiest time rooting your device, but you feel like you overcame all of the obstacles. Only now to discover that those very apps and mods you were rooting for still won't work — and the signs point to a lack of root access. Don't lose hope, because we have some tricks up our sleeve.

The newest version of macOS has arrived. While everyone's mind is being blown by Mojave's groundbreaking new Dark Mode, we'll be taking advantage of its insecure file permissions to establish a persistent backdoor with a self-destructing payload that leaves little evidence for forensics.
Look, tests are no fun, and doing poorly on them is rarely an option. Whether you're studious or a slacker, everyone needs a little boost now and again. While students have found ways to cheat as long as tests have existed, the invention of smartphones has greatly enhanced the potential to get ... creative.

Russian cyber disinformation campaigns have many missions, but one of particular interest is using technology to monitor, influence, and disrupt online communications surrounding culturally sensitive topics or protests. The ability to watch these events, and even filter positive or negative tweets to amplify, gives rise to the ability to execute a number of disinformation campaigns.

The latest Star Wars movie, Solo: A Star Wars Story, has grossed almost $350 million worldwide during its first month in theaters. This is a good opportunity to discuss how hackers can use media hype (in this case, Hollywood movie hype) to disarm an unsuspecting Windows user into inserting an evil USB stick into their computer.

After finding and monitoring nearby wireless access points and devices connected to them, hackers can use this information to bypass some types of security, like the kind used for Wi-Fi hotspots in coffee shops, hotels, and in flights high above the ground. By swapping their MAC address for that of someone already connected, a hacker can bypass the MAC filter and connect freely.

Fight me all you want, but it ain't a party without alcohol—whether it's a Halloween party, Christmas party, dinner party, or even a damn wedding. (If you think that people will stick around after dinner for a dry wedding, then you're sorely mistaken.)

Say whatever you want, but Steampunk is primarily a maker culture. Consider that Steampunk has existed since the 1960s and yet more or less languished in obscurity until approximately 2005, which is when it made the leap to costuming. That costuming was what provided the leap to the tangible, despite the fact that Steampunk art had also existed for years.

It's easier than you might think to hack into Wi-Fi routers using just one unrooted Android phone. This method doesn't require brute-forcing the password, a Windows OS for converting PowerShell scripts into EXE format, a reliable VPS for intercepting hacked Wi-Fi passwords, or Metasploit for post-exploitation tricks.

In the previous article, we learned how to set up our VPS, configure our PHP server, and developed an in-depth understanding of how the payload works. With all that taken care of, we can get into disguising our payload to appear as an image and crafting the note in the greeting card being delivered to our intended target.

The latest film addition in the American-produced Millennium series, The Girl in the Spider's Web, was just released on Blu-ray a few days ago. As you could expect, the movie has many hacking scenes throughout, just like the previous English and Swedish language movies centered around hacker Lisbeth Salander. Of course, with the quick pace of some scenes, the hacks can be hard to follow.

Cases and stickers are always great, but they aren't the only way to customize an iPhone. The software on your device is full of customization options, from a better-looking home screen and cooler lock screen wallpapers to app icon changes and a system-wide dark mode. There's literally over 100 ways to make iOS on your iPhone genuinely unique, some of which are hiding in plain sight.

Will the predicted apocalyptic date — December 21st, 2012 — really be the end of the world? In this ongoing five-part series, we examine what would happen if zombies, nuclear weapons, cyberwars, earthquakes, or aliens actually destroyed our planet — and how you might survive.

This software tutorial shows you how to morph or change the voice of a song in AV Voice Change. Learn how to morph a voice using the voice morpher tool in Voice Change 6.0. Change voice pitch to disguise someone or imitate voices and more with the real-time voice morpher in AV VCS 6.0.

You Will Need an artificial flower

Bored at the office? Try out the practical joke in this how-to video. Rick Roll your friends and co-workers. The more you do it, the funnier it gets. You can disguise the link by typing in any random url into the e-mail, right clicking and clicking 'edit hyperlink' then paste the url to the video in the box there and click 'OK.' Check out the video computer pranks tutorial and learn how to Rick Roll. Perfectly Rickroll a friend or co-worker.

Back in November I visited The Hollywood Wax Museum on Hollywood Blvd. After pacing through the entire museum, I was bothered deep down in the guch area that there were no Jackass wax mannequins! So I took the liberty of making my own Johnny Knoxville mannequin. The plan was to make one, fly it down to LA(couch of course) and then try to actually get it into the Hollywood Wax Museum as a joke. Now the joke/prank has evolved!...

Nothing is more relaxing than the sound of moving water in the garden. Here's how to build a one-of-a-kind water feature in a weekend.

Wee-man is in a baby carriage. (Carriage is on a huge hillside going down hill, busy sidewalk) “Daddy” (Jack-Ass character in disguise) asks for directions from someone.

How to play Spy, my personal favorite class What do Spies do?

Duhhhh. How to disguise that Spitzer face. Hell. Spitzer used an alias of a hedge fund buddy George Fox. Eliot should have gone one logical step further. Make a compelling disguise.

Welcome to Minecraft World! Check out our tutorials, post to the community corkboard, and come play on our free server!

Welcome to Minecraft World! Check out our tutorials, post to the community corkboard, and come play on our free server!

Welcome to Minecraft World! Check out our tutorials, post to the community corkboard, and come play on our free server!

Welcome to Minecraft World! Check out our tutorials, post to the community corkboard, and come play on our free server!

Welcome to Minecraft World! Check out our tutorials, post to the community corkboard, and come play on our free server!

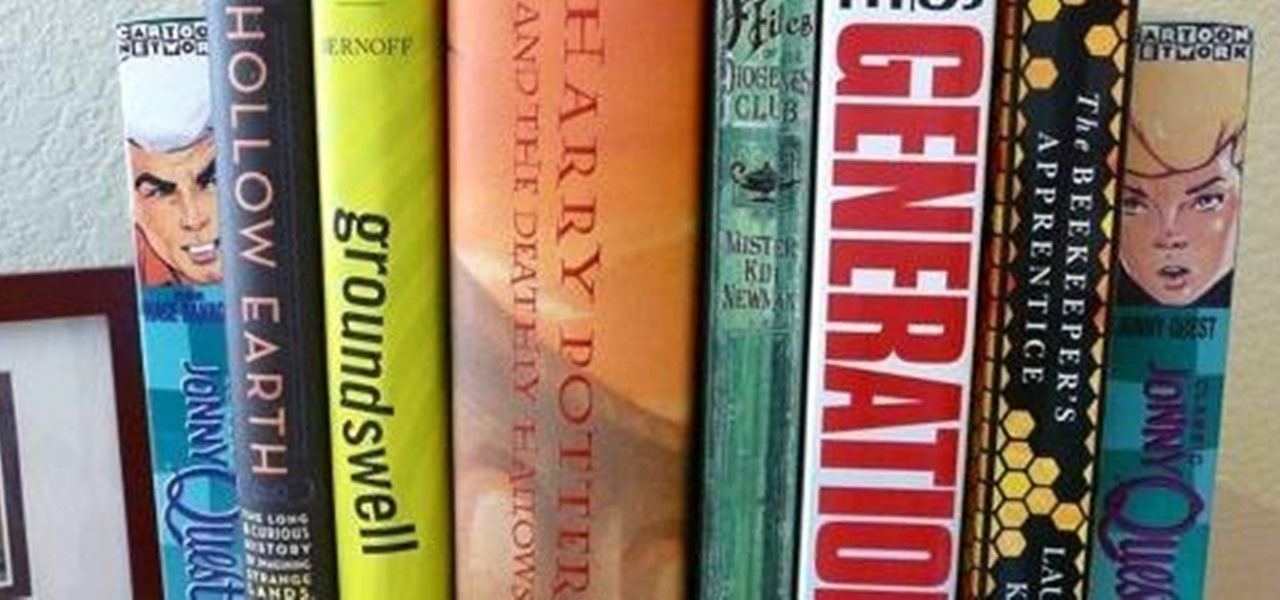
Check out this awesome tutorial that shows you how to make a useful bookend using recycled materials. I think this is cool because you could even disguise the VHS tape to look like a book. Crafting with VHS Tapes - CraftStylish.

Welcome to Minecraft World! Check out our tutorials, post to the community corkboard, and come play on our free server!

Welcome to Minecraft World! Check out our tutorials, post to the community corkboard, and come play on our free server!

Welcome to Minecraft World! Check out our tutorials, post to the community corkboard, and come play on our free server!

Welcome to Minecraft World! Check out our tutorials, post to the community corkboard, and come play on our free server!

Welcome to Minecraft World! Check out our tutorials, post to the community corkboard, and come play on our free server!

You see before you the humble block: This single, unassuming block couldn't possibly hold anything of value, right?
We need 8 of the best redstoners to come out for this. This is a redemption style tournament. What that means is that if you lose to your first opponent you go to the losers bracket and fight the losers for a chance to battle the top redstoner.

For those of you behind on their international politics, Vladimir Putin has once again been elected as President of Russia. And right now, there are over 20,000 protesters in Moscow yelling about election fraud. Now, whether or not you think they're right, or whether or not you think Putin is a badass (he is, for the record), you have to admit he is an amazingly interesting cultural figure. And what do we do with amazing cultural figures? Why, we make fun of them with Impact-laden photos, of ...

GUISARD n pl. -S a masker 59 points (9 points without the bingo)

White criminal Conrad Zdzierak has committed the ultimate crime of racial stereotyping, plus multiple counts of aggravated robbery after robbing four banks and a CVS pharmacy. The robberies took place on April 9th of this year, but Zdzierak wasn't caught until now, thanks to an incredibly realistic, $650 silicon mask named “The Player”.