Below are the official rules and guidelines for submitting content to WonderHowTo. Please look over them before publishing any articles. Ignoring the rules could result in deletion of your article or being flagged as a spammer. Most of these rules apply to comments as well.

Technology is awesome. You can use your iPad to record music or even turn your tunes into a solar system, but sometimes being plugged in all of the time can leave you nostalgic for simpler times. This new concept by Joelle Aeschlimann brings together the best of both worlds by turning your iPad into an old-fashioned, hand-cranked music box. The artist created three different music boxes, each one with its own unique song and visualization. The music boxes were made using wooden cylinders with...
Never being contacted for a job you're interested in interviewing for is a terrible feeling. It might make you feel inadequate as if your qualifications aren't up to par, but the problem might be that your resume isn't even getting read in the first place.
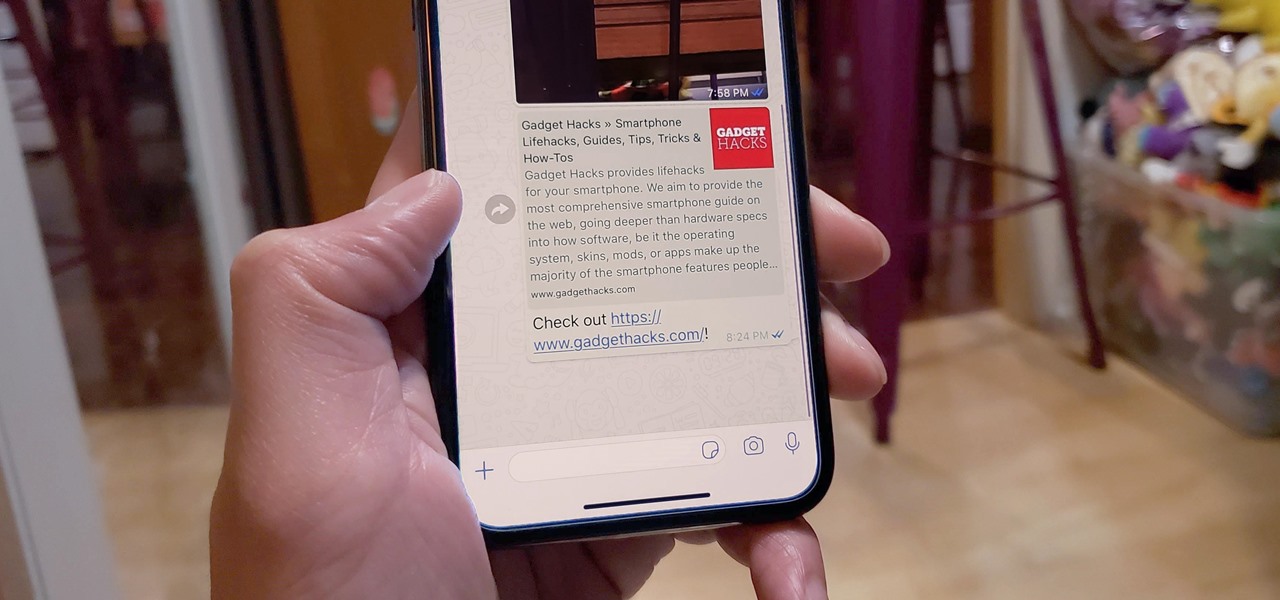
When WhatsApp first came out in 2010, it quickly gained notoriety as a great way to meet new people all over the world thanks to group chats, which allow multiple admins for each group that can all add participants from their own contacts lists.

We already know that Magic Leap is working with Hollywood motion capture legend Andy Serkis on a new immersive content experience but, so far, all we've heard are descriptions of the work. Well, now the mystery is over, and the character of Grishneck, who Magic Leap mentioned just last month, has finally been revealed.

Google updates the Play Store periodically, but the changes are usually subtle. A recent server-side update, however, is shaking things up quite a bit.

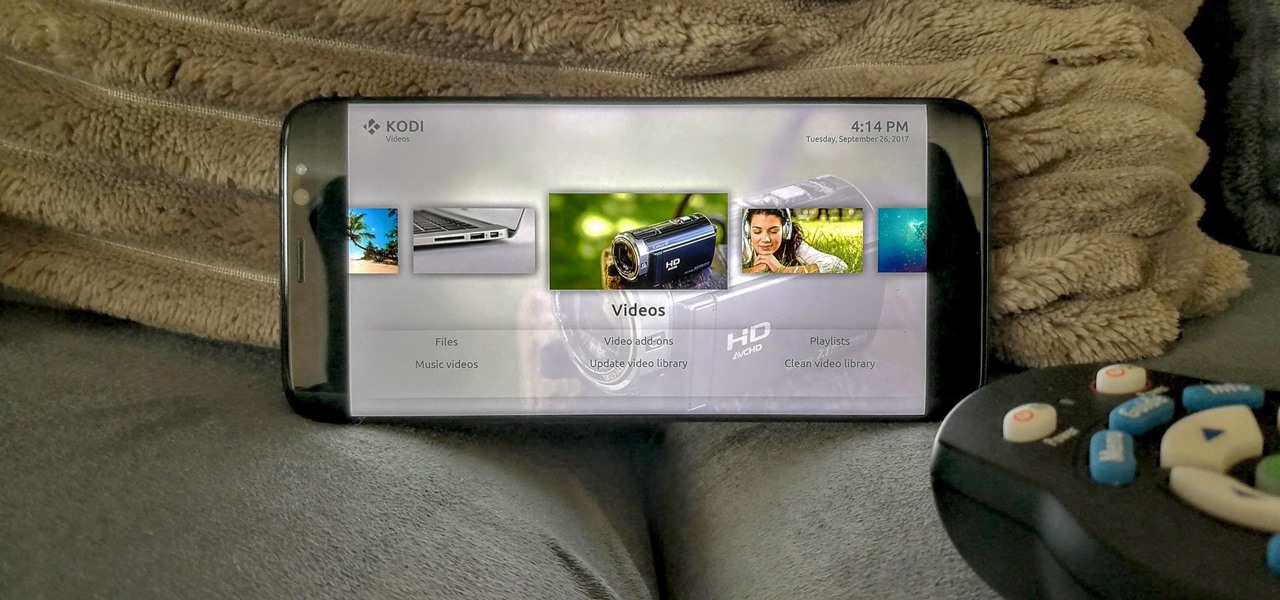
When you first use Kodi, it can be intimidating. The main menu has numerous options for the various types of media Kodi can play back, and the settings menu has a broad array of tools to customize Kodi to your needs. After poking around in theses menus, you might realize that you don't like the default look. But whether it's the color, font, layout, or just the general theme, Kodi skins can change it all.

Zenko Games makes no apologies for its influences. In fact, they cite them explicitly in their own promotional materials for Diamonst AR.

NBA star Andre Iguodala, of the Golden State Warriors, got to try out a Magic Leap demo in Florida and started dishing out some pretty revealing details about the upcoming mixed reality headset to CNET's Brian Tong.

The Google Calendar app hasn't really changed much over the years. As a pre-installed staple on most Android devices, the interface is definitely lacking in some areas. Google knows this, and has plans in the pipeline to completely revamp Calendar's UI alongside Android 5.0's official release.

The Galaxy S5's screen is truly a feat of modern technology. It uses what is known as an AMOLED display—an acronym for Active-Matrix Organic Light-Emmitting Diode. In short, this technology means that every individual pixel on your phone's screen emits its own light. This is a break from the traditional LCD technology that requires a backlight for any pixels to be visible.

Buying and drinking wine can be intimidating. There's so much to know, and so many ways to reveal your ignorance. If you're completely befuddled by wine and how to describe it, don't worry, you're not alone.

There are plenty of apps on Google Play for customizing your Samsung Galaxy S3 with wallpapers and new lock screens, but to be honest, you're not really customizing until you root.

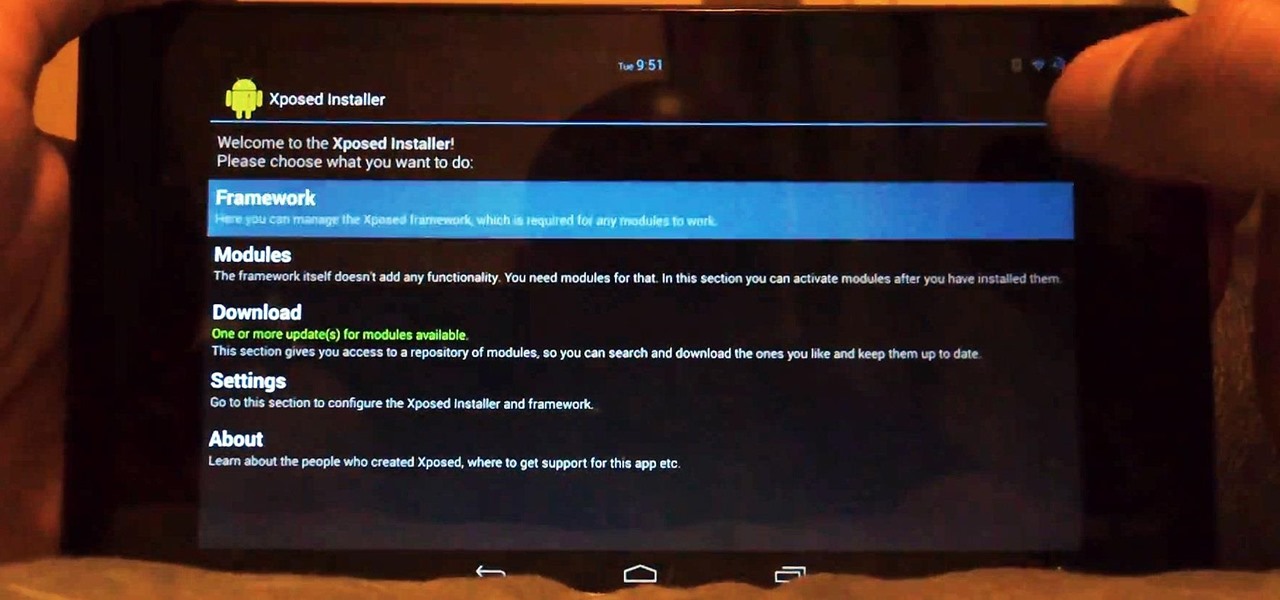
Customization of our Android devices, outside of what Google and mobile carriers allow us to do, used to mandate that our devices were rooted and running a custom ROM.

The iPhone's "Accessibility" menu is one of those options that's very easy to overlook but incredibly handy in certain situations. You can set AssistiveTouch to help navigate your device, use a Bluetooth mouse when your screen is acting up, and enable the red screen filter for nighttime escapades. For as long as the menu has been available, it's been in the "General" settings, but not in iOS 13.

If Google hasn't already demonstrated that it is serious about augmented reality, then it made it abundantly clear at the Google I/O keynote on Tuesday.

Although next week will mark the late David Bowie's 72nd birthday, his fans and admirers are the ones receiving a gift in the form of an augmented reality app that explores the artist's career

I hate folder names, especially the one Apple shoves down our digital throats. On a computer, they make total sense, but on my iPhone, it's just more clutter on the home screen. You can tell what folder is what just by looking at the app icons within it, so why are we forced to label them? Technically, we're not, since there is a workaround in iOS 12 and iOS 13 to make those labels disappear for good.

With April coming to a close, there's a fresh group of augmented reality Snapchat lenses you should try out while they're still hot. We've got a prank lens, gamer-oriented ones for Fortnite and Fallout, and ones for the memesters out there.

Just days after Bose did its best to frame a pair of glasses frames with spatial audio as "augmented reality," a patent application from Magic Leap, surfaced on Thursday, March 15, offers a similar idea, but with real AR included.

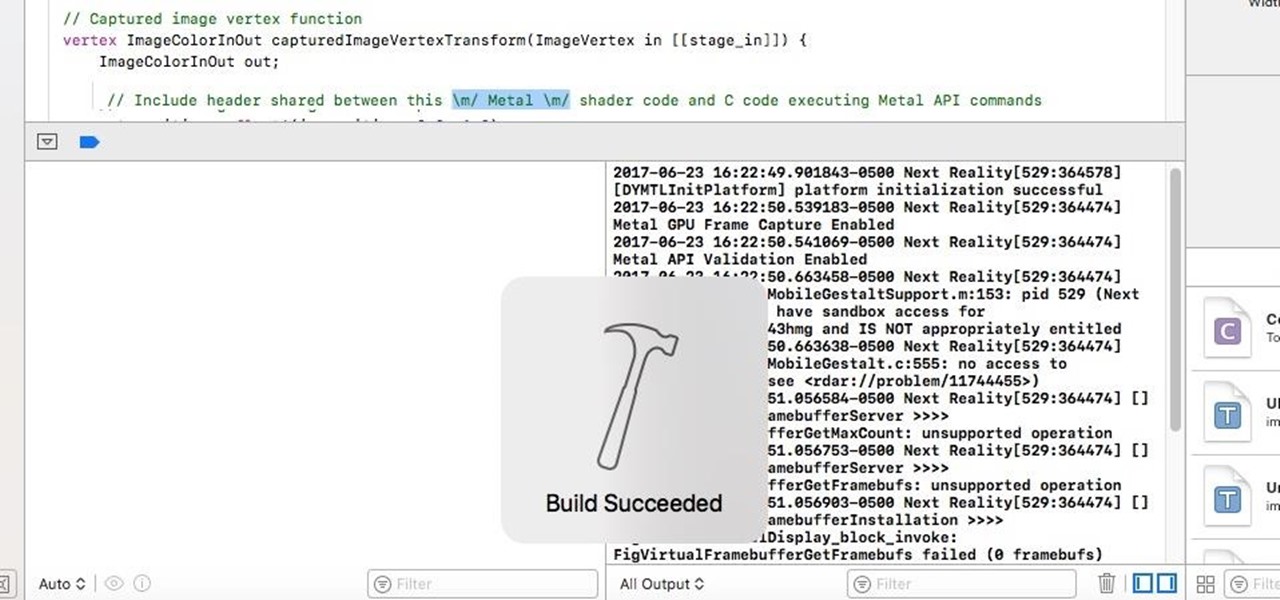
In the first part of this series, we looked at the surface detection that is provided by the ARKit. We looked at how it worked and covered some of the tools that could help us determine what is not working; when it doesn't. Now let's take this to the next step.

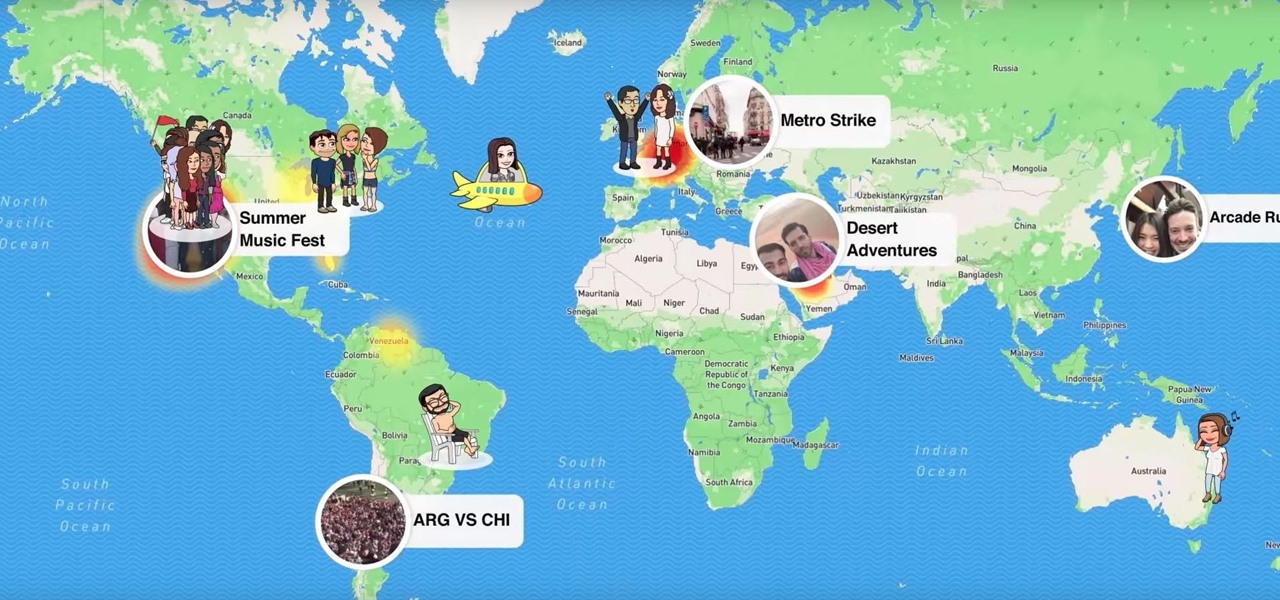
Snapchat's newest feature will allow you to see where your friends are posting from around the world. Called Snap Map, this easy-to-use update gives users the ability to view your friends' stories and locations on a map.

In 2012, VideoLan published a beta release of their wildly popular desktop media player, VLC, for the Android platform. However, because the non-profit development team did not have access to popular North American Android devices, they opted to exclude the USA and Canada from their initial release. That is, until now.

If you thought humans were reading your résumé, think again. Robots do, and their one solitary objective is to systematically crush the hopes and dreams of those who don't make the cut. Instead of paying a few humans to read thousands of résumés over a couple weeks, many companies use computer programs that can do the job in less than an hour. In fact, at least 90 percent of Fortune 500 companies use what they call an applicant-tracking system, aka rejection machines.

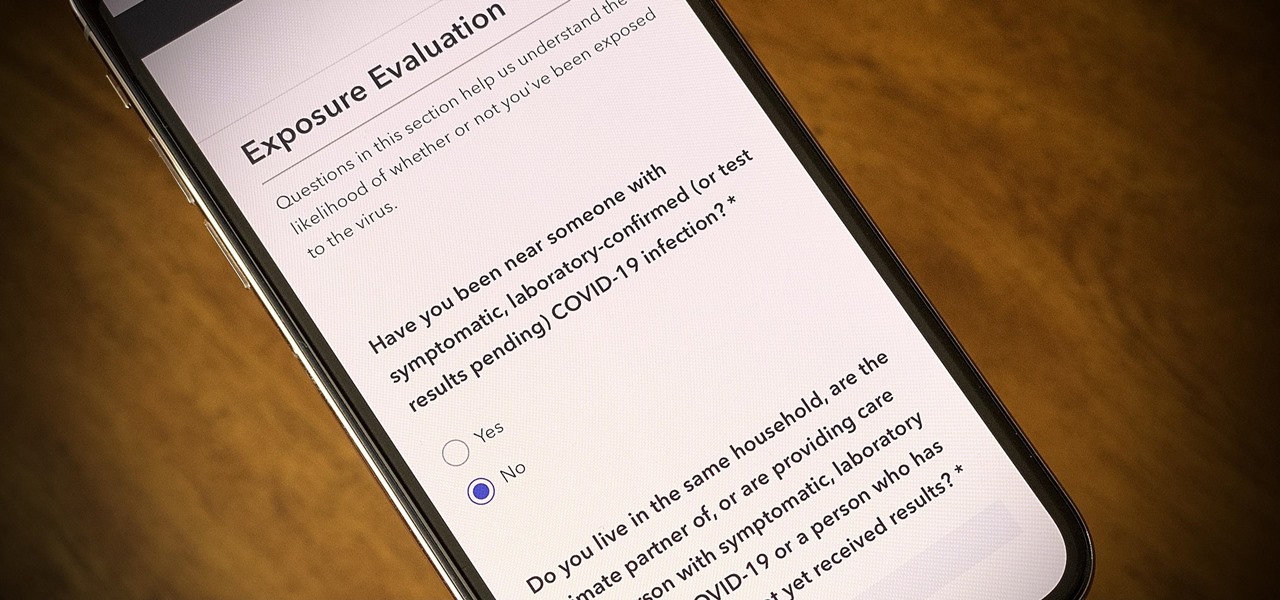
One of the scariest things about the COVID-19 virus is that you can show no symptoms but still be infected (and contagious). Naturally, we all want to know whether we're carrying the new coronavirus, but if you're showing signs of COVID-19, how can you be tested to know for sure? Websites are popping up to help with that, screening for symptoms, and directing you to a testing site if needed.

Websites are often misconfigured in ways that allow an attacker to view directories that are not ordinarily meant to be seen. These directories can contain sensitive information such as private credentials or configuration files that can be used to devise an attack against the server. With a tool called Websploit, hackers can scan targets for these hidden directories without difficulty.

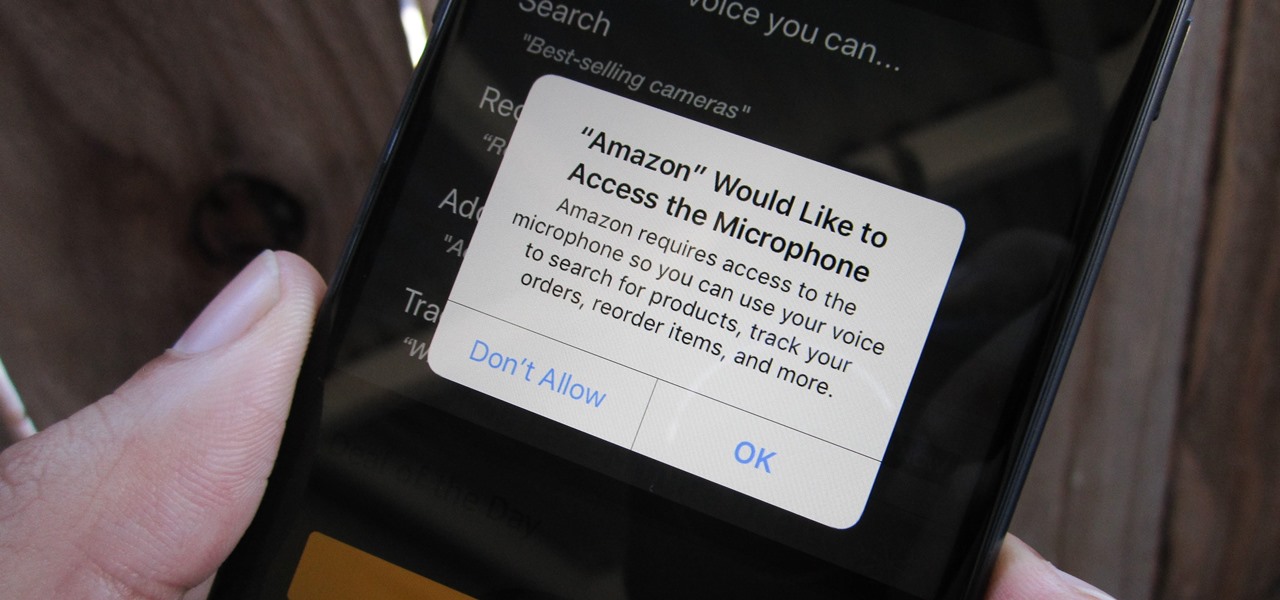
Any app on your iPhone could potentially listen in on your conversations and use that information to target you with tailored ads. Although most companies, including Facebook and Apple, have come out and vehemently denied these claims of spying on consumers, who's to say they're telling the truth? The only way to be sure you're safe is to take matters into your own hands.

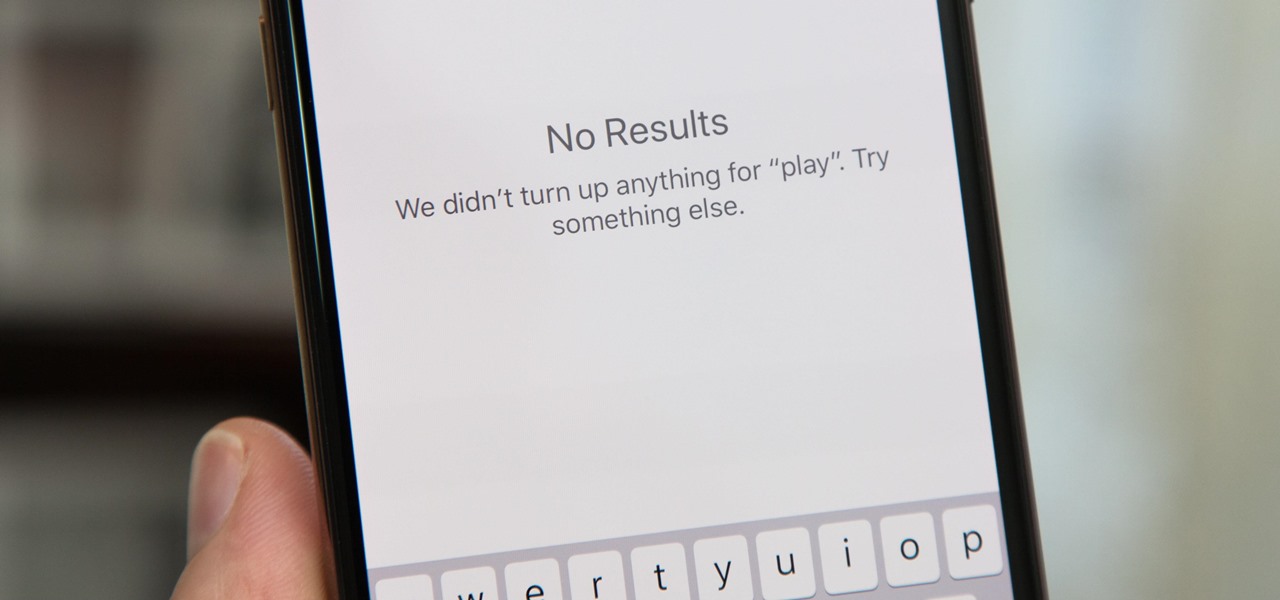
There's something seriously wrong with Apple's new Shortcuts app, and it's severely limiting the number of shortcuts users can install on their iPhones.

One of the things that sets a seasoned hacker apart from the script kiddies is the ability to effectively sneak past antivirus defenses when executing an attack. One way to do this is to use custom shellcode in an exploit. Not everyone is an expert at writing shellcode, but luckily there's an easy way to do this that is both quick and effective.

Having an efficient workflow is an integral part of any craft, but it's especially important when it comes to probing apps for vulnerabilities. While Metasploit is considered the de facto standard when it comes to exploitation, it also contains modules for other activities, such as scanning. Case in point, WMAP, a web application scanner available for use from within the Metasploit framework.

Great ideas often strike at random times, but messaging friends and loved ones at an inopportune hour not only risks their wrath, but also increases the chances of your message not being paid proper attention to. Thankfully, there's an app that lets you create and post WhatsApp messages at the time you wish for maximum effect.

Another piece of Magic Leap's mysterious story has been uncovered thanks to a new patent application revealed on Thursday, March 15.

OnePlus has now officially upgraded both the 5 and 5T to Android 8.1 Oreo. As implied by the version number, this isn't a huge update from Android 8.0 Oreo. However, OnePlus has included a few of their own features as well.

The year is 2018. You just received your own Magic Leap One: Creator Edition. What now? Rewinding back to today, we know of one specific app that will be available for Magic Leap's device, along with two others that could be tagged as highly likely. Paired with Magic Leap's own experiments and demonstrations, we can get a sense of what the playground for this new toy will offer.

One of the best new features in Android Oreo is the new Adaptive Icons system. Starting now, developers can create a single icon for their apps, then your launcher can stylize those icons in a broad range of shapes to match your system theme. Most home screen apps haven't added support for this feature yet, but Nova Launcher just threw its hat into the ring.

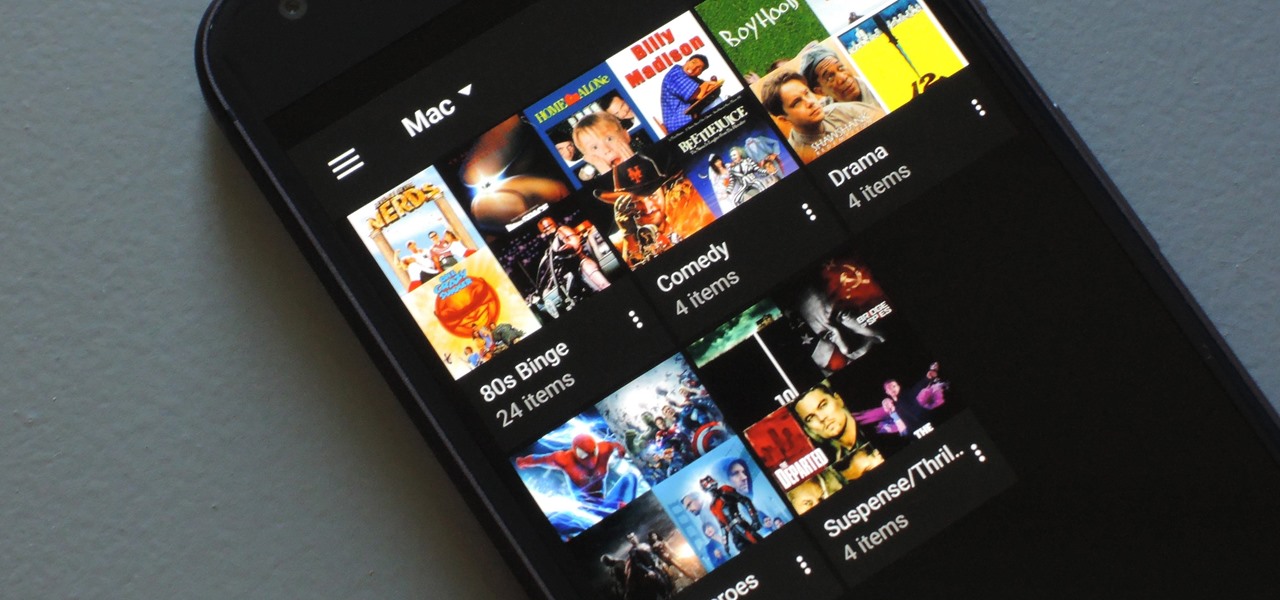
If you have a large media library, you should definitely have the Plex server installed on your computer. If you do, you can just install Plex for Android or iPhone, then you'll have access to all of your music, movies, and TV shows anywhere.

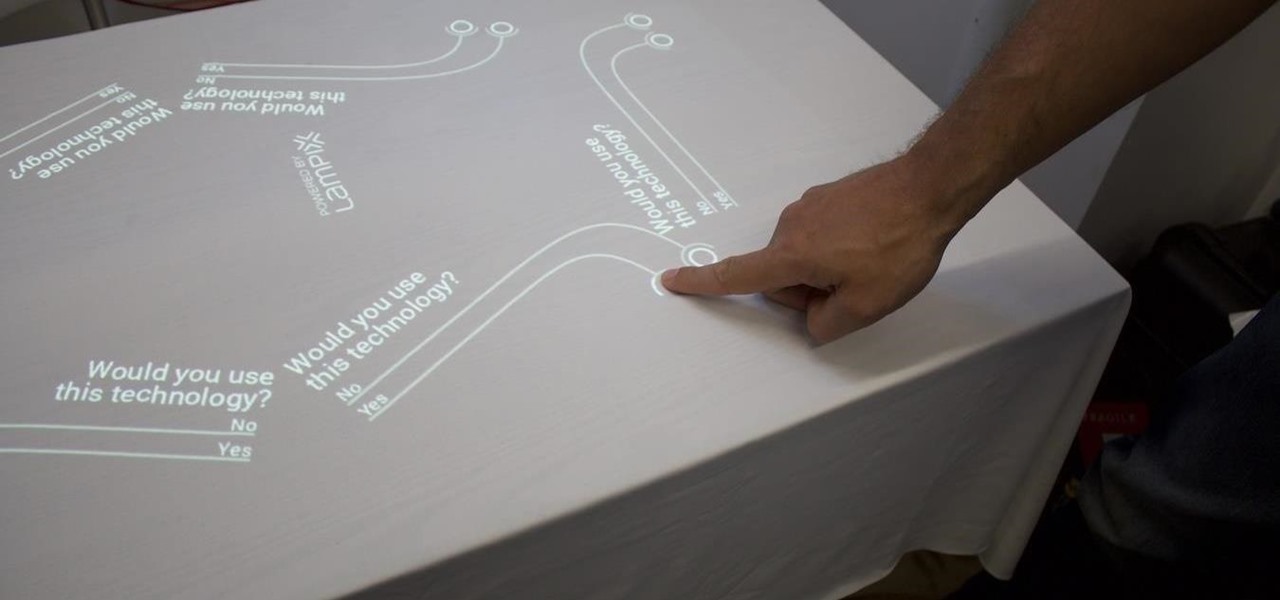
Over the past week, companies took a variety of approaches to investing in augmented reality. Lampix is backing its own effort to build an ecosystem for augmented reality platforms. Nokia and Xiaomi are teaming up on numerous fronts, potentially including augmented reality.

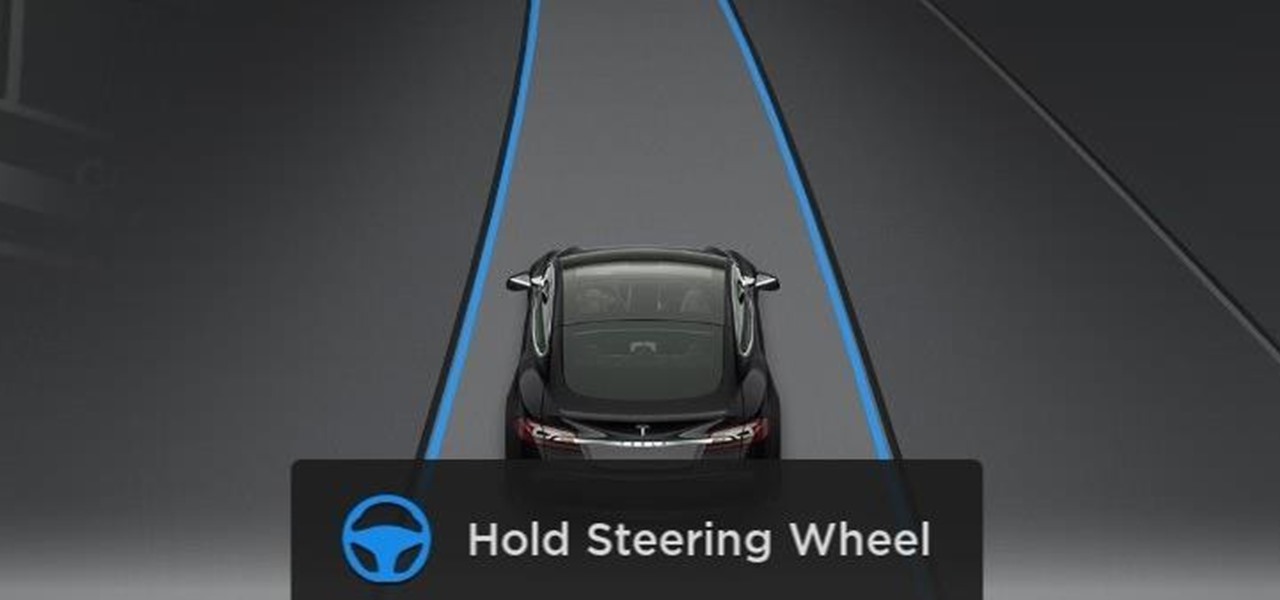
Tesla hopes high-level personnel changes will help it gain an edge in neural network knowhow for its models' self-drive features, following the replacement of its Autopilot chief and the appointment of a recent Stanford grad to head its AI and Autopilot vision research.

There are two types of Halloween lovers: Those who like culturally-relevant costumes and serving precious ghost cupcakes, and those who live to freak their friends the hell out in the most disgusting way possible.

Welcome back, my aspiring hackers! As I mentioned in earlier posts, the best hackers (or at least those not behind bars) have a keen understanding of digital forensics. If I am tasked to intrude upon an enemy's file server to retrieve war plans, such as in this tutorial, it is essential to my country's (and my own) well-being that it not be traced back to me. Understanding digital forensics helps us to leave without a trace and never have a trail back to us or our employer.