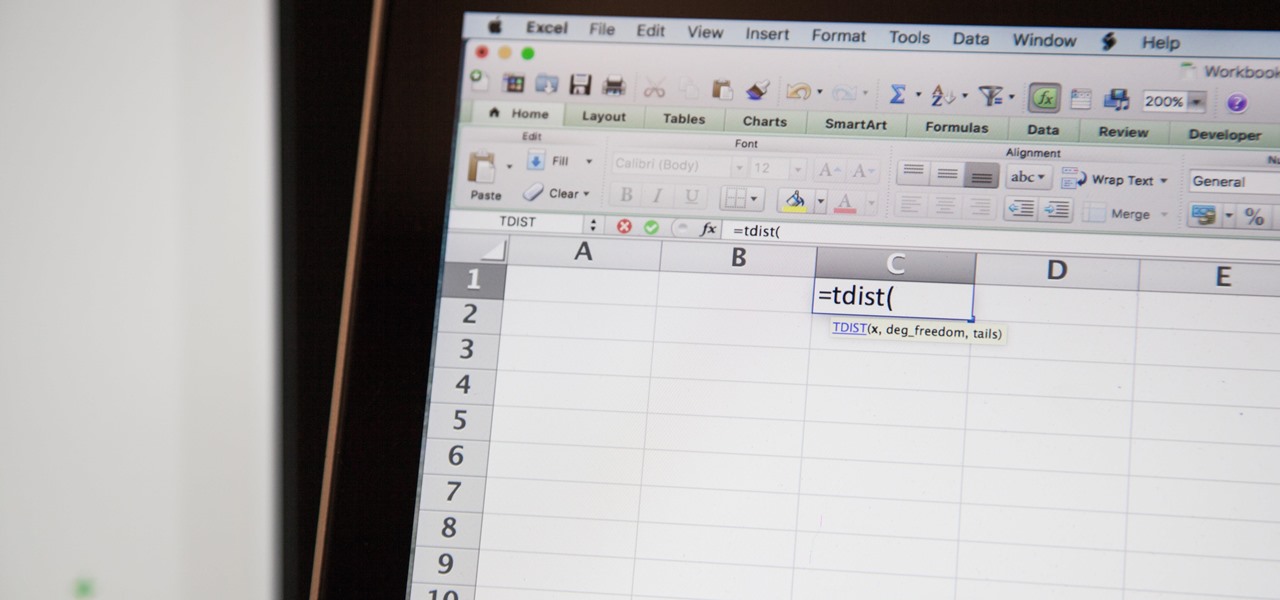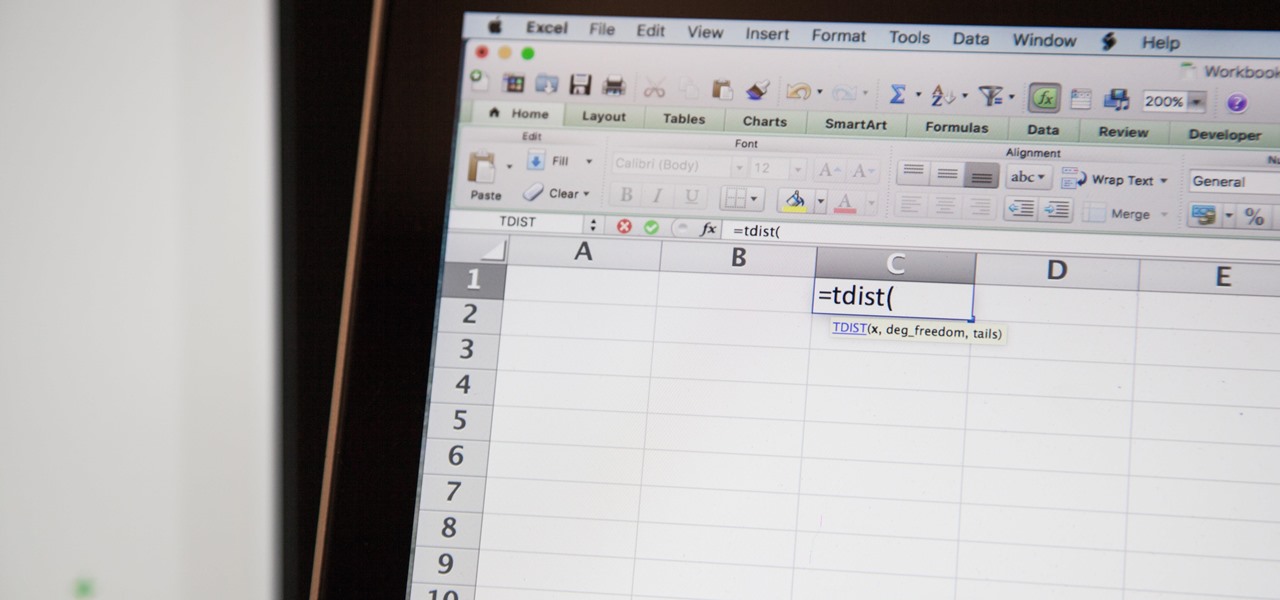
So you need to find the p-value for your hypothesis test. To do so, employ the spreadsheet program Microsoft Excel. Using a simple formula, you can easily determine the p-value for your tests and thereby conclude strong or weak support of the null hypothesis.

Second Class Boy Scouts work on building their outdoor survival and camping skills. Compass work, nature observation, camp tools, and swimming are areas where new skills are mastered and demonstrated. A second class scout, having completed all the requirements, should be able to lead a hike, care for his own equipment, set up a campsite, and perform basic first aid.

As a Boy Scout, when the First Class rank is attained, a scout has learned all the basic camping and outdoors skills of a scout. He can fend for himself in the wild, lead others on a hike or campout, set up a camp site, plan and properly prepare meals, and provide first aid for most situations he may encounter. A First Class scout is prepared.

Seldom in recent history has a cyber security event caused so much media stir (maybe because it happened to a media company?) and international relations upheaval. Cyber security breaches seem to take place daily of major corporations, but the Sony hack seems to have captured the American imagination and, for that matter, the whole world's attention.

Zombies have followed hot on the heels of vampires as the monster du jour in modern America, and this has been particularly pronounced in video games for some reason. Gamers dig zombies, we suppose. The zombie game folks are even developing some camaraderie amongst themselves, as evidenced by the easter eggs exchanged in Left 4 Dead 2 and Dead Rising 2: Case West. This video will show you where and how to find a Left 4 Dead 2 reference / easter egg in Dead Rising 2: Case West.

In this video tutorial two-parter, you'll see how to dissect the female reproductive tract of a mature laying hen for an anatomical look.

In this language tutorial, you will learn how to use the definite article in biblical Greek (Koine). This is a perfect lesson for those scholars wishing to study this ancient language of Greece. Watch this how to video and you will be speaking biblical Greek in no time.

Humans clearly demonstrate altruistic tendencies towards other members of groups with which they identify.

Stay tuned for this knitting instructional video on the gusset stitch. When you knit the heel flap, you slipped a stitch at the beginning of each row. This made a very nice chain through which you can pick up the gusset stitches. You can either pick up stitches through the whole chain stitch, or through the back loop of the chain stitch. Picking up stitches through the whole chain stitch creates a rather definite seam on the inside which could be uncomfortable to wear. I prefer to pick up the...

Part of the beauty of summer is the stark contrast between day (hot, sunny, bright) and night (chilly, starry). While loads of makeup tutorials can be found that will teach you how to get the "summer glow" and infuse your face with more bronzer than Mr. Armani has ever encountered in his lifetime, gorgeous summer nights are often neglected as a beauty inspiration.

When you have to find the average of two or five numbers then you have to add all the numbers and then divide then by two or five respectively. However in the case of the function you have infinite many values over any interval. But it is not possible to add all and then divide by infinity. Therefore you have to calculate in a different way. Imagine that you have to find the average of y=f(x). Then you have to average it from the interval from ‘a’ to ‘b’. The inner area under the curve shall ...

This video shows the procedure to draw a face. The video shows various stages to draw a face. These include drawing an egg on the paper, dividing the egg into various parts by horizontal lines, drawing the nose and lips, drawing the eyes and ears. The video cleverly deals with issues relating to the evidence of not being a professional. The video shows the various choices that can be made by the artist in drawing the face like the pencils to use.

In this "Math Made Easy" geometry episode, you learn how to prove that two triangles are congruent (equal) by using the "side-side-side" evidence. By using "side-side-side" to prove that two triangles are congruent, you are stating that all the respective corresponding sides of two triangles are equal in length thus proving the triangles are congruent. The narrator in this tutorial provides you with definitions about statements, proofs, and congruency. This becomes useful when setting up a ta...

Having a bed bug infection in your car is extremely rare. However, if you suspect bed bugs in your automobile, check all of the cracks and crevices for any bed bug evidence. However, even if you don't find anything that doesn't rule out that they are there. What you can do is take your car to get fumigated. Other than that, the only thing that will absolutely kill the bugs is to let your car get very hot on a sunny, summer day.

Austin Paranormal Investigations shows how

In the wake of Google Glass' failure, we can expect other companies to fill the void in due time. Perhaps unsurprisingly, Snapchat may be one of the first.

Welcome back, my aspiring hackers! As I mentioned in earlier posts, the best hackers (or at least those not behind bars) have a keen understanding of digital forensics. If I am tasked to intrude upon an enemy's file server to retrieve war plans, such as in this tutorial, it is essential to my country's (and my own) well-being that it not be traced back to me. Understanding digital forensics helps us to leave without a trace and never have a trail back to us or our employer.

Welcome back, my fledgling hackers! It's been awhile since we did a Metasploit tutorial, and several of you have pleaded with me for more. I couldn't be happier to oblige, as it's my favorite tool. For the next several weeks, I'll intersperse some new guides that'll help expand your Metasploit skills and keep you abreast of new developments in Metasploit, so look for them in the near future.

Welcome back, my budding hackers! Previous to this tutorial, we've focused mostly on hacking the target system. If we're successful in owning the target system, we'll then want to make certain that the system administrator doesn't know we were there, and that he or she cannot track us.

Security researcher and iPhone hacker pod2g has brought attention to a flaw in Apple's iOS that allows the user to change the reply address of an SMS message. This bug has been a part of the iPhone's SMS since the first iPhone in 2007, but Apple has yet to address it. Basically, there's a section in the text payload called User Data Heading (UDH) that controls some advanced features, one of which is the reply address. By changing the reply address of a text message, you can make someone send ...

The main complaint for this 1999 Jeep Cherokee, 4.0L, is that the Low Coolant Light keeps flashing on and that it keeps needing coolant. Nothing seems to be leaking on the ground, so where's the leak going? After doing the normal pressure test to spot the leak, and the combustion gas leak, and the overnight test, nothing seemed to work. The coolant leak could not be identified. So, it must be the cylinder head, right? But you need evidence of that first. Watch and learn how to prove your theo...

In this tutorial, we learn how to get a Canadian Permanent Resident card. The residence card will identify you and your name as a resident of Canada. If you do not have a card when entering Canada, you have to obtain a new PR card within 30 days and have a new Canadian address. If you need to replace or renew your PR card, you must file an application as soon as you lose it. This information will need personal information and residency information. The fee is 50 Canadian dollars. If you need ...

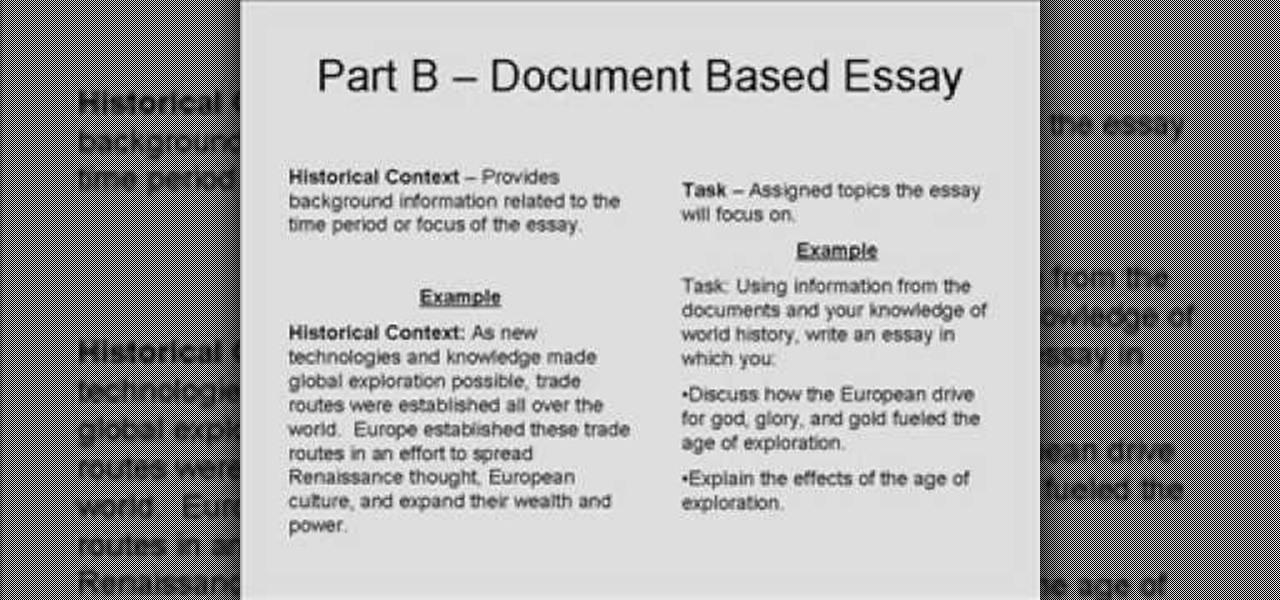
In this video tutorial, viewers learn how to write a document-based question essay. Data base question essays evaluates student ability to formulate and support an answer of documentary evidence. Each document based question is broken into 2 parts: short answer and essay. The short answer assess student ability to analyze student documents individually. The essay assess the student ability to synthesize and create an essay based on an assortment of documents. The essay should contain an intro...

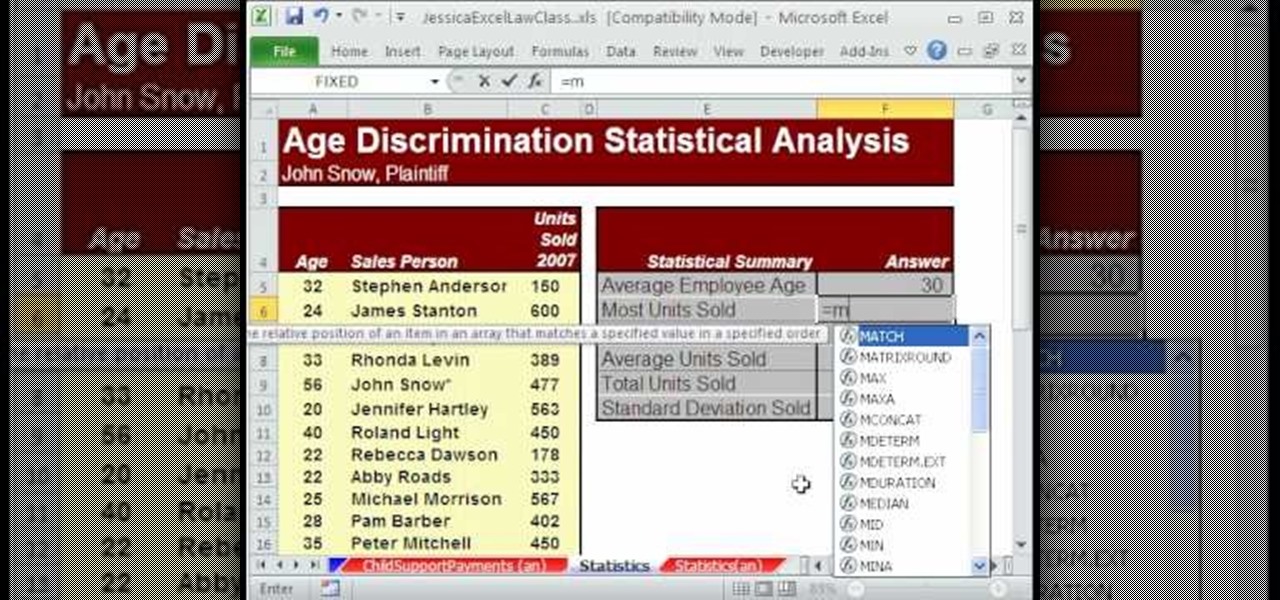
New to Microsoft Excel? Looking for a tip? How about a tip so mind-blowingly useful as to qualify as a magic trick? You're in luck. In this MS Excel tutorial from ExcelIsFun, the 532nd installment in their series of digital spreadsheet magic tricks, you'll learn how to use the AVERAGE, STDEV, MAX, MIN and SUM function to add statistical data. Specifically, this video lesson discusses how to sum and average evidence in an age discrimination case.

This video shows how to make a 3D five point paper star. First cut a pentagon using a sharp flat blade and a ruler. Folding halfway between each two corners to the opposite corner. These folds are the points of the star. Make a mark half-way between the edge of the paper and the center point created by the folds. Using the ruler and X-acto knife, cut straight along the fold from the mark to the edge. Cut two small triangles off of each side 1/4" up from the middle of the edge, cut a line stra...

In this Education video tutorial you will learn how to avoid wrong answers on the SAT critical reading area. Five principles to keep in mind are rephrase the question and predict the answer, answer the question being asked, find evidence in the passage, extreme answers are suspicious and finally remember a little wrong is all wrong. To rephrase the question, read 2 lines before and after, ask the question in your own words and find the answer choice that best matches your prediction. Now comi...

This video describes the art of writing argumentative essays. In other words it narrates how to improve arguments of an essay. It starts with an analysis of classic examples. The speaker begins by criticizing the style of paragraph and how to improve the suggestions. He explains how to omit errors and form your arguments in commanding manner. Finally, he says how to come a conclusion by adding solid evidence. At the end of course he will show you how to transfer a old matter into a classic ex...

No matter who you are, a little self-confidence can go a long way toward making your dreams come true.

One of the ironies of gardening is that often some of the smallest pests can create the biggest nuisance. White flies can drain the life out of your plants. You can see the evidence of white fly damage in the lack of vigor in the plant and the discoloration of the leaves. Before they were a rich green and now they've turned a sickly yellow. Learn how to get rid of these pesky white flies with this gardening tutorial.

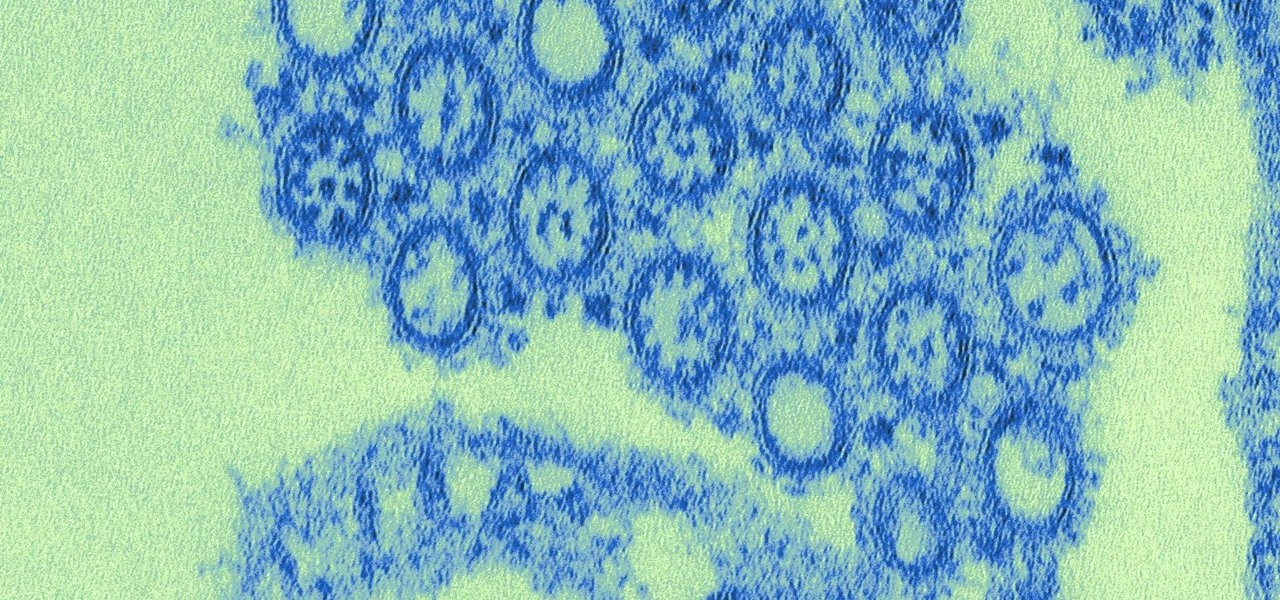
Growing evidence suggests that neurodegenerative diseases like Parkinson's may develop in part due to environmental factors, including infections that can cause inflammation in the nervous system. New research from investigators from Jude Children's Research Hospital and Thomas Jefferson University has strengthened that connection.

There are all kinds of theories—many supported by science—about what causes Alzheimer's disease. Tangles of protein called ß-amyloid (pronounced beta amyloid) plaques are prominently on the list of possible causes or, at least, contributors. An emerging theory of the disease suggests that those plaques aren't the problem, but are actually our brains' defenders. They show up to help fight an infection, and decades later, they become the problem.

New Android versions have always been released on a fairly regular schedule—in late Fall, Google debuts a new Nexus device, while simultaneously publishing the next iteration of the world's leading mobile operating system. But things are different this year, as we now have numerous indications that Android Nougat could be released as early as August or September.

A raw video shot by Jason McMinn, using a GoPro mounted to a helicopter drone, gives us a look at Apple's new campus, currently under construction in Cupertino.

In its latest feature with an assist from augmented reality in storytelling, the New York Times shows readers the virtual crime scene it constructed to prove that the Syrian military conducted chemical warfare against its citizens.

Can you tell when your friends are serving up a bunch of BS, or are you constantly oblivious, unsure if they're spinning a valid story? With so many ways to lie and fake information floating around, it can be impossible to tell what's the truth from what's complete BS. Here's how to sort through what you hear and find the real truth.

Apple released the first developer beta for iOS 13.5.5 on Monday, June 1. The update comes on the same day Apple released iOS 13.5.1 to the public, which patched the unc0ver jailbreak, and 12 days after iOS 13.5, which introduced COVID-19 exposure notifications, in addition to other new features.

Recently released accident reports by the state of California's Department of Motor Vehicles show humans did a lot of dumb things to cause accidents with General Motors' (GM) Cruise Automation driverless vehicles in San Francisco this year.

Uber and Waymo's lawsuit is starting to pan out. Following a ruling on Monday, May 15, Judge Alsup, who called Waymo's patent infringement claims "meritless," ordered Uber to perform a series of actions and duties for Waymo. Without further ado, here's what Uber must do to begin to put this lawsuit behind them (well, maybe):

It has been a long road for Uber throughout the duration of its lawsuit with Waymo, especially with a judge who seemed significantly against Uber with almost every argument made. Monday's ruling was, while not necessarily a win for Uber, less punishing than many would have thought.

Welcome back, my aspiring hackers and those who want to catch my aspiring hackers! As most of you know, this series on digital forensics is inspired by the motivation to keep all of you all out of custody. The more you know about the techniques used by law enforcement and forensic investigators, the better you can evade them.