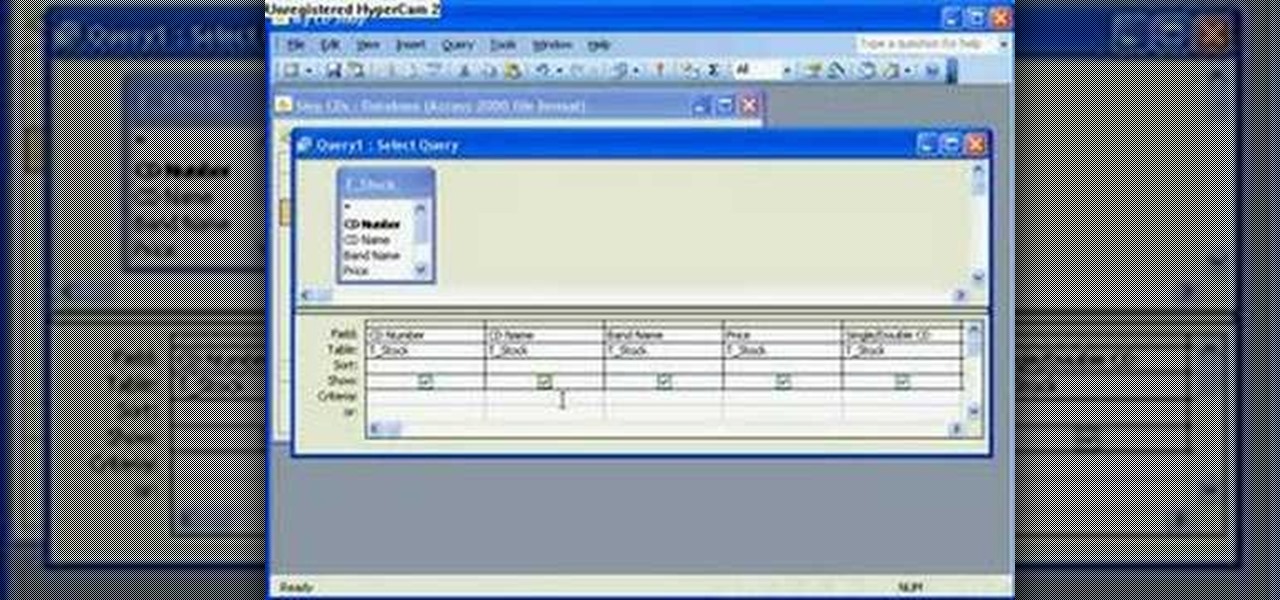
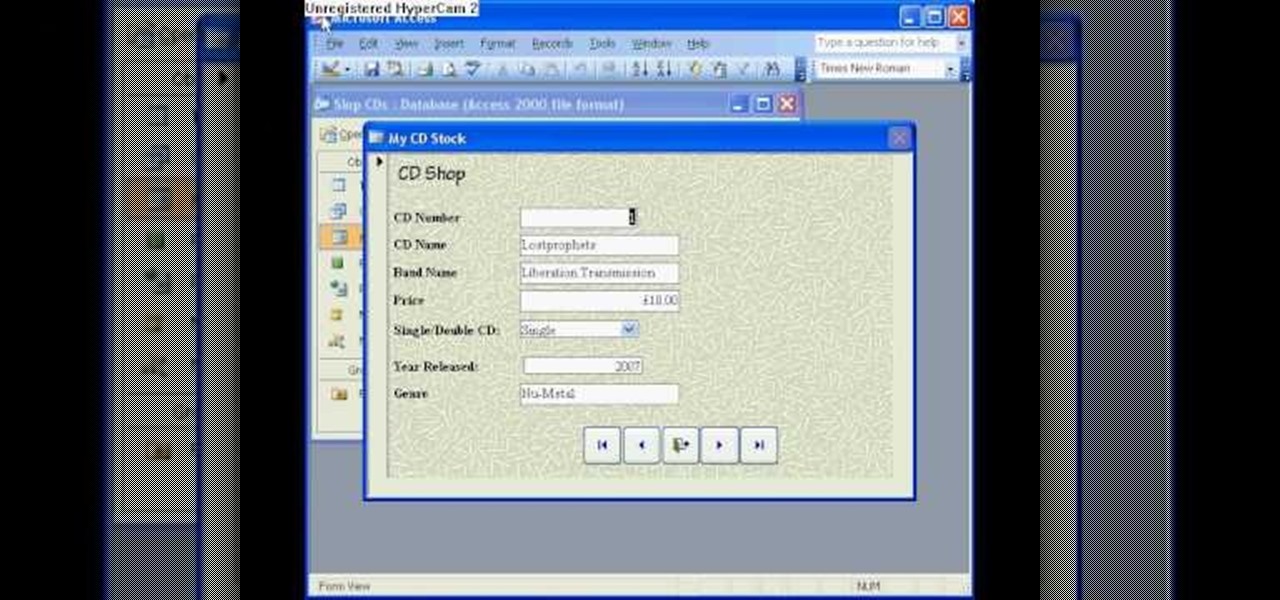
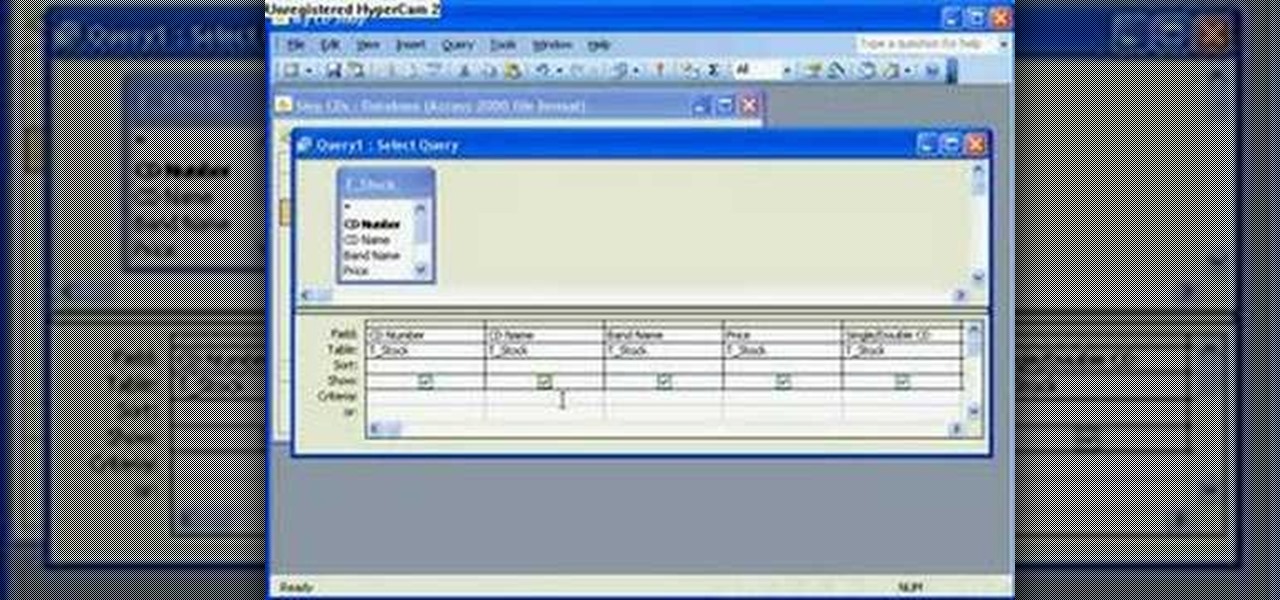
The Microsoft Office Access 2007 relational database manager enables information workers to quickly track and report information with ease thanks to its interactive design capabilities that do not require deep database knowledge. In this Microsoft Access video tutorial, you'll learn about using a query rather than a table to create a form and select records. For more information, and to learn how to create a form from your own Microsoft Access queries, watch this how-to.
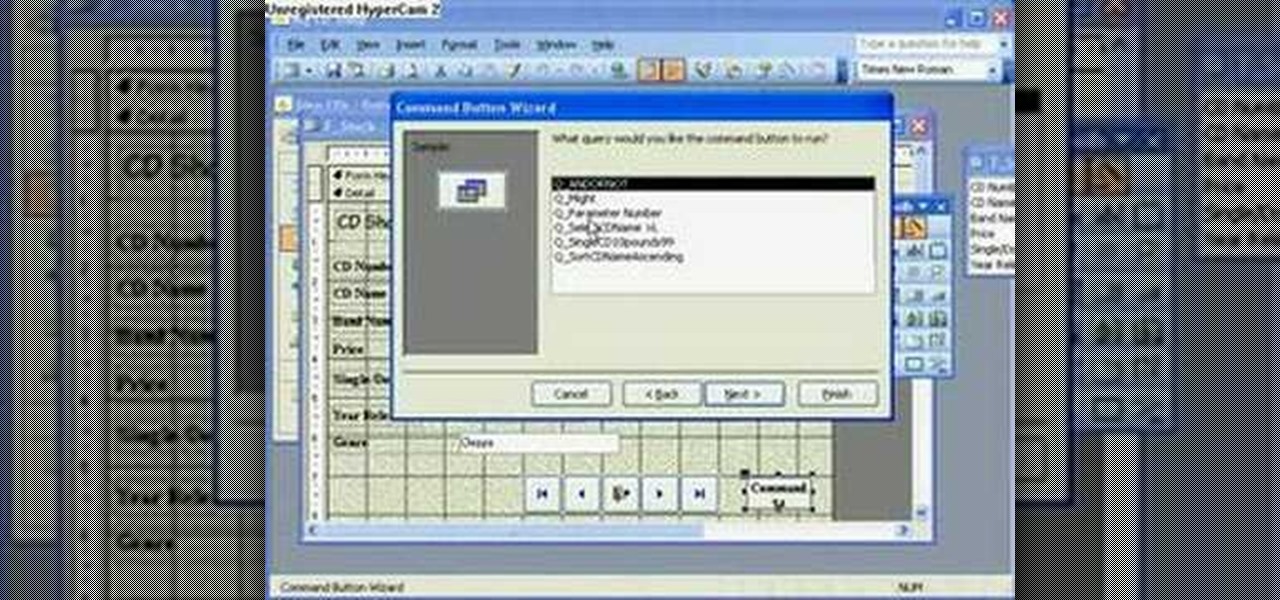
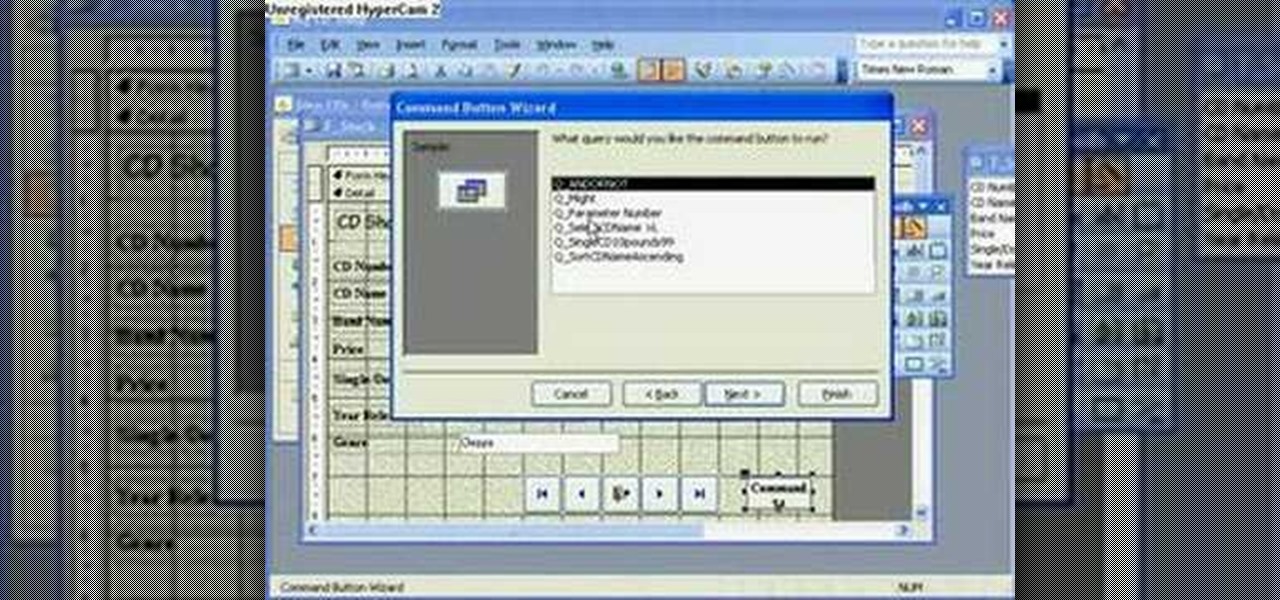
The Microsoft Office Access 2007 relational database manager enables information workers to quickly track and report information with ease thanks to its interactive design capabilities that do not require deep database knowledge. In this Microsoft Access video tutorial, you'll learn about running a query from a form using a button. To get started running queries from forms in Access, take a look.
The Microsoft Office Access 2007 relational database manager enables information workers to quickly track and report information with ease thanks to its interactive design capabilities that do not require deep database knowledge. In this Microsoft Access video tutorial, you'll learn about passing parameters to queries in Microsoft Office Access. For more information, and to get started running your own parameter queries, take a look.

The Microsoft Office Access 2007 relational database manager enables information workers to quickly track and report information with ease thanks to its interactive design capabilities that do not require deep database knowledge. In this Microsoft Access video tutorial, you'll learn about using the Boolean logical operators AND OR and NOT in queries in Access. To get started using Boolean operators in your own Access queries, take a look.

The Microsoft Office Access 2007 relational database manager enables information workers to quickly track and report information with ease thanks to its interactive design capabilities that do not require deep database knowledge. In this Microsoft Access video tutorial, you'll learn about using mathematical operands and other logical operators to select data in queries. For more information on using logical operators in your own Microsoft Access queries, take a look.

The Microsoft Office Access 2007 relational database manager enables information workers to quickly track and report information with ease thanks to its interactive design capabilities that do not require deep database knowledge. In this Microsoft Office Access 2007 video tutorial, you'll learn about using wildcards to fill in the blanks in Access. For detailed instructions on using Access yourself, watch this video how-to.

The Microsoft Office Access 2007 relational database manager enables information workers to quickly track and report information with ease thanks to its interactive design capabilities that do not require deep database knowledge. In this Microsoft Access video tutorial, you'll learn about sorting data using queries. For detailed instructions, and to get started using queries to sort data for yourself, watch this how-to.

The Microsoft Office Access 2007 relational database manager enables information workers to quickly track and report information with ease thanks to its interactive design capabilities that do not require deep database knowledge. In this Microsoft Access video tutorial, you'll learn about using a tiny bit of VBA to add a clock to a given form. For step-by-step instructions, take a look!

The Microsoft Office Access 2007 relational database manager enables information workers to quickly track and report information with ease thanks to its interactive design capabilities that do not require deep database knowledge. In this Microsoft Access video tutorial, you'll learn about disabling the close, minimize and maximize control buttons and record selectors as well as adding your own graphical icon and program title. For more information on modifying control buttons in Microsoft Off...

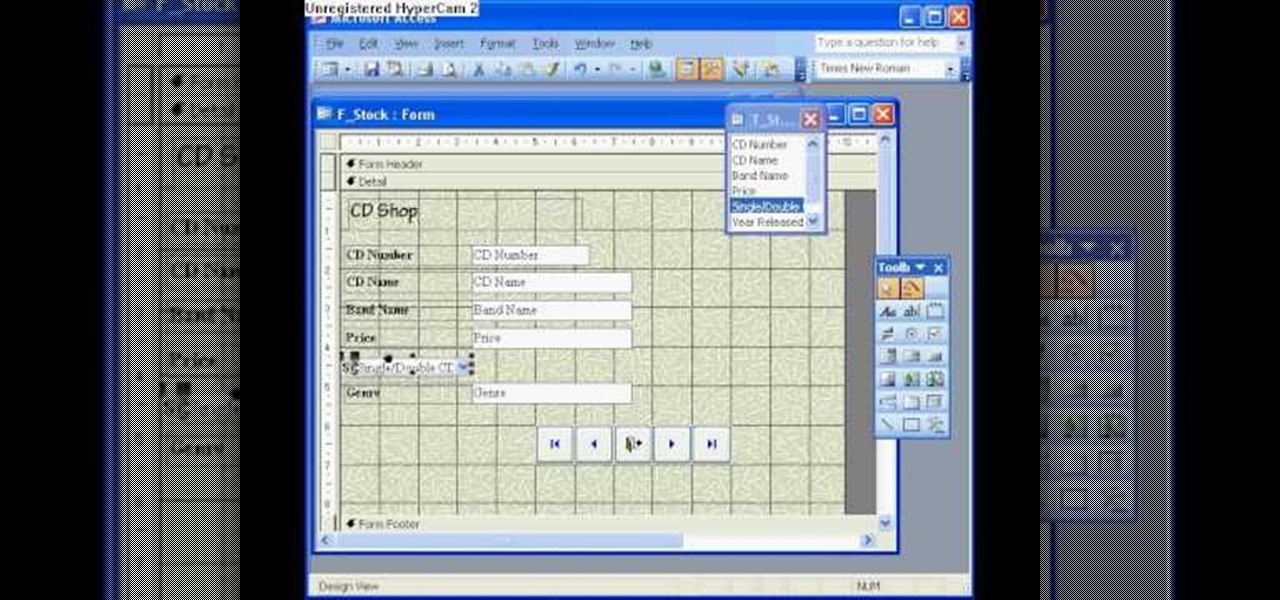
The Microsoft Office Access 2007 relational database manager enables information workers to quickly track and report information with ease thanks to its interactive design capabilities that do not require deep database knowledge. In this Microsoft Access video tutorial, you'll learn how to add and modifying fields to a pre-existing table, and applying these changes to an associated form. To get started adding and modifying fields, tables and forms in Access, take a look!

This tutorial covers installing the WAMP (that is, Windows-Apache-MySQL-PHP) all-in-one package and creating a MySQL database using the import function of phpMyAdmin. For step-by-step instructions on the WAMP installation process, or to get started installing your own WAMP serve, take a look.

If you're new to DreamCoder for MySQL, one of the very first things you may want to do is know how to backup a given MySQL database. Happily, this tutorial will walk you, step by step, through the backup process. Take a look!

Check out this tutorial and learn how to get up to speed with the latest installment of Mircosoft Access 2007. Microsoft Office Access 2007 brings you a new look and new features designed to help you get your work done more easily than ever. You'll see differences right away, starting with the Getting Started with Microsoft Office Access page where you can open a blank or existing database, download a pre-built database template, and check out the offerings on Microsoft Office Online.

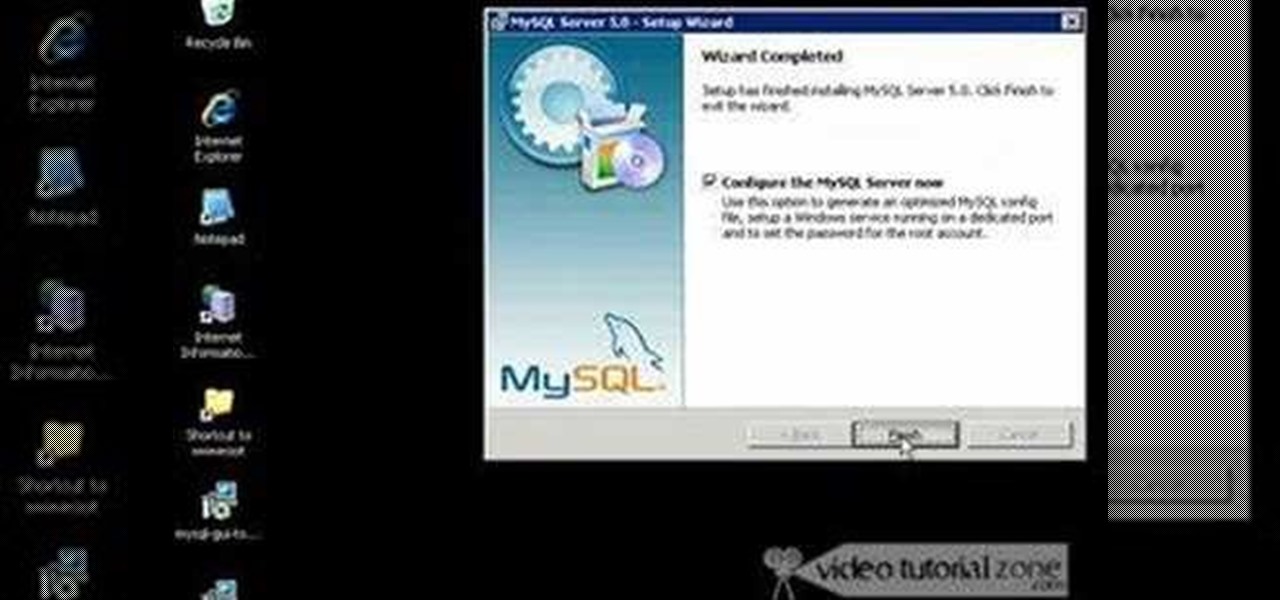
MySQL is a multithreaded, multi-user SQL database management system which has over 10 million installations. It runs as a server providing multi-user access to databases. It is by far the most popular and common database used in web applications throughout the world, and almost all hosting companies provide it free of charge to their users. MySQL AB makes MySQL Server available as free software under the GNU General Public License (GPL). For this tutorial we are going to download and install ...

The key to becoming a competent white hat is knowing how the technology that you are trying to exploit actually works. SQL injection is one of the most common methods of attack used today and also one of the easiest to learn. In order to understand how this attack works, you need to have a solid grasp of ... you've guessed it ... SQL.

Welcome back, my hacker novitiates! If you have been following this new Snort series, you know that Snort is the world's most widely used intrusion detection/protection system. Now a part of the world's largest network equipment company, Cisco, it is likely to be found everywhere in one form or another. This makes a compelling argument for learning how to use it, as it will likely be a necessity in any security-related position.

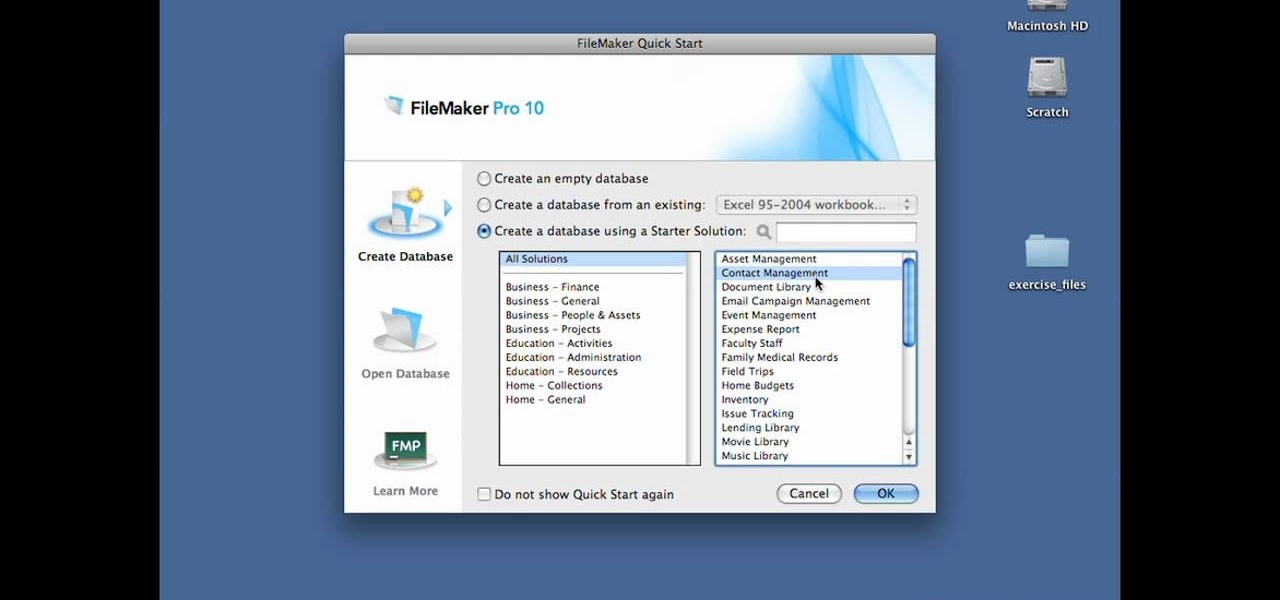
In this Lynda video tutorial, learn how to use FileMaker Pro 10 software to create databases with pre-made templates. FileMaker offers these templates in a package called Starter Solutions. To access these options, click open FileMaker. Then, go to New Database under the File menu. Click the option "Create a database using a Starter Solution." The templates are grouped according to the nature of their use. Some are for the home, while some are for business. All you do is open the template you...

It's been said time and time again: reconnaissance is perhaps the most critical phase of an attack. It's especially important when preparing an attack against a database since one wrong move can destroy every last bit of data, which usually isn't the desired outcome. Metasploit contains a variety of modules that can be used to enumerate MySQL databases, making it easy to gather valuable information.

Hello NullByte! This will be my first How To series.

Welcome back, my tenderfoot hackers! Have you ever wondered where the physical location of an IP address is? Maybe you want to know if that proxy server you are using is actually out of your local legal jurisdiction. Or, maybe you have the IP address of someone you are corresponding with and want to make certain they are where they say they are. Or, maybe you are a forensic investigator tracking down a suspect who wrote a threatening email or hacked someone's company.

Welcome back, my hacker novitiates! When we are trying to find vulnerabilities in a website to attack, we need a solid web server vulnerability scanner. Internet-facing web apps can open enormous opportunities for us as they are often riven with vulnerabilities and can often offer an entire point to the internal network and resources.

Attacks against databases have become one of the most popular and lucrative activities for hackers recently. New data breaches seem to be popping up every week, but even with all of that attention, databases continue to be a prime target. All of these attacks have to start somewhere, and we'll be exploring a variety of methods to gather information on PostgreSQL databases with Metasploit.

Welcome back, my budding hackers! In my continuing effort to build your basic Linux skills for hacking, I want to show you how to build a secure "tunnel" to MySQL.

Welcome back, my fledgling hackers! The database is the hacker's "pot-of-gold," as it contains information that is very valuable to both the business and the hacker. In this, the second of my series on hacking databases, we're on the "hunt" for Microsoft's SQL Server. Although far from the most commonly used database (Oracle hold's that title), Microsoft's SQL Server is very often found in small-to-medium sized businesses. Even a few big businesses use it.

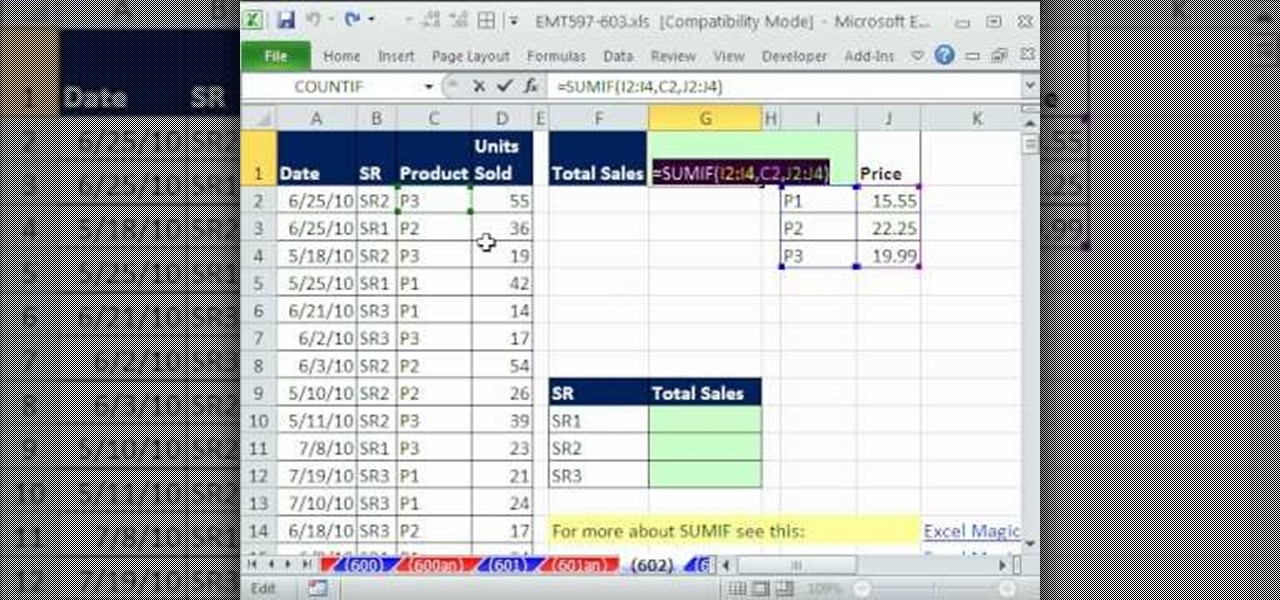
New to Microsoft Excel? Looking for a tip? How about a tip so mind-blowingly useful as to qualify as a magic trick? You're in luck. In this MS Excel tutorial from ExcelIsFun, the 602nd installment in their series of digital spreadsheet magic tricks, you'll learn how to create a compact array formula that can total sales with 1 criteria when the database does not have a price or total sales column. See how SUMIF can be used to lookup values and simulate a missing column from a database.

In this installment from the Unorthodox Hacking series of computer security videos, you will explore a few of the areas in Windows that most Sysadmins don’t even know exist. See how to become Local System through the Task Scheduler and abuse long filenames. Take a look at some of the features within Windows—registry—that many system administrators don't know exist with this hacking how-to.

This PHP newbie video with teach you what a Singleton Pattern is and how to use it in your PHP programming. PHP OOP Singleton is great for a database connection when you only want one consistent connection in your application. So, to prevent wasting space accidentally by calling it twice in different areas, this is good way to protect it. Singleton is very popular and used often in Database Connections.

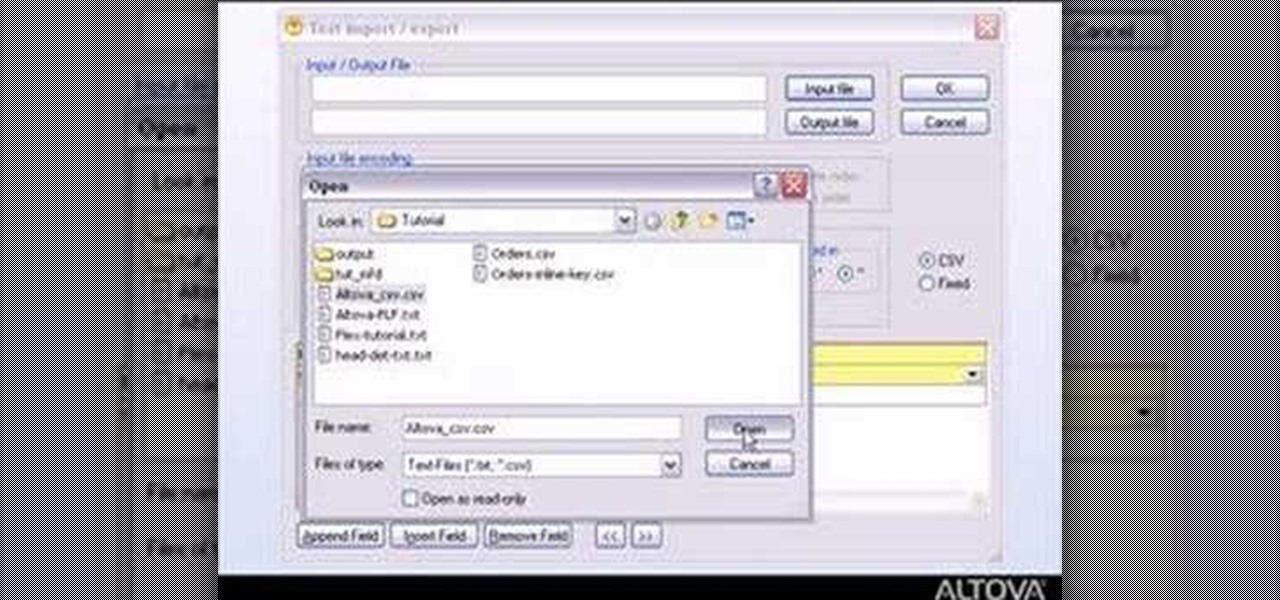
MapForce supports flat files as the source and/or target of any mapping involving XML, database, EDI, web services or other flat file data. In this how-to, you'll find instructions for mapping data from arbitrary text files (such as log files, CSV, fixed-width, and other legacy data sources) to databases and XML files.

If you're new to DreamCoder for MySQL, one of the first things you may want to know how to do is export data from a remote MySQL database. Happily, this tutorial will walk you, step by step, through the process. To get started exporting MySQL data with DreamCoder, take a look!

The ability to stay organized and be resourceful with data gathered from recon is one of the things that separates the true hackers from the script kiddies. Metasploit contains a built-in database that allows for efficient storage of information and the ability to utilize that information to better understand the target, which ultimately leads to more successful exploitation.

Trying to focus on studying for your Stats final in the library but getting a serious ADD spell? Then make use of your time - while having a little fun with whoever else is in the library - by hacking into your computer's command prompt.

A great tool for any system administrators, the iPhone (or other Apple wifi device) app Ping a Majig allows you to enter in the IP addresses of websites. Then you can keep checking on them to make sure they are running smoothly and operating correctly. You can click on the website for more data regarding pings and site health.

Need to know how to run a program as an admin in Windows 7? This tutorial will show you how it's done! It's easy! So easy, in fact, that this home-computing how-to can present a complete overview of the process in just over a minute's time. For more information, including detailed, step-by-step instructions, watch this Win 7 user's guide.

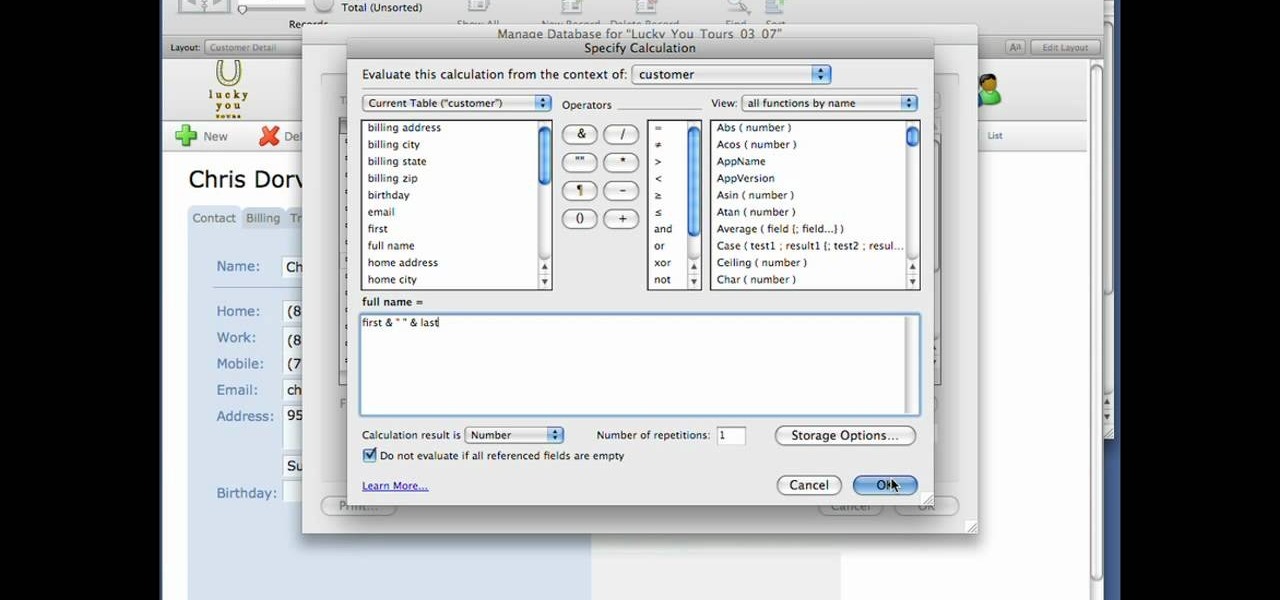
If you are a user of FileMaker Pro then this video teaches you how to use calculation and summary fields in it while making new files. In Filemaker you can create a various kind of fields that you want your file to contain. In Filemaker a calculation is a data that gets computed depending up on the formula that is set in the Filemaker database settings. Calculations are very critical in file management. Open the Manage Database and there you can find some of the calculation fields. There in t...

This video demonstrates how users of the FileMaker Pro 10 software can easily start using this software from the quick start menu. It is demonstrated to users how to create a database or open an existing database from this quick start page. Also demonstrated is how users might be able to find further information using the "Learn More" option at the bottom of the menu. This option shows users the basics via videos, tours, and tutorials. A must see for those new to this software.

For an easy way to lookup and connect with people and companies across the web (and all of its many social media outlets) check out the Firefox extension Tabble. Tabble provides you with access to all of an individual's relevant online information and can even show you relevant e-mails in your Gmail account if applicable.

Google is one of the most powerful forces on the Internet, and their technology can be the key to helping you find success in whatever your online endeavor might be, from web design to filmmaking. This video is a part of their Google Webmaster Series, offering help to webmasters the world over on how to best utilize Google in their work. This video will show you how to optimize your deep web content, like databases and forms, to be crawled by Google using a few simple tricks.

Nmap is possibly the most widely used security scanner of its kind, in part because of its appearances in films such as The Matrix Reloaded and Live Free or Die Hard. Still, most of Nmap's best features are under-appreciated by hackers and pentesters, one of which will improve one's abilities to quickly identify exploits and vulnerabilities when scanning servers.

This is a short explanation and tutorial on how to grab saved passwords from Google Chrome, ideally from a meterpreter session. The idea behind this is to understand how saved passwords work and how to keep them safe. Let's have some fun :D Understanding Google Chrome Saved Passwords

Check out this video to learn how to use Seas0nPass to jailbreak your Apple TV 2G. This mod works on either Mac or Windows. This jailbreak is for Apple TV with firmware 4.2.2. Once you've jailbroken your Apple TV2 you'll have administrator access to all files on it.