Follow along through the creation of a fictitious customer portal to learn about master pages, themes, membership, roles, site navigation, user profiles, and the Web Site Administration Tool in this ASP.Net video tutorial.
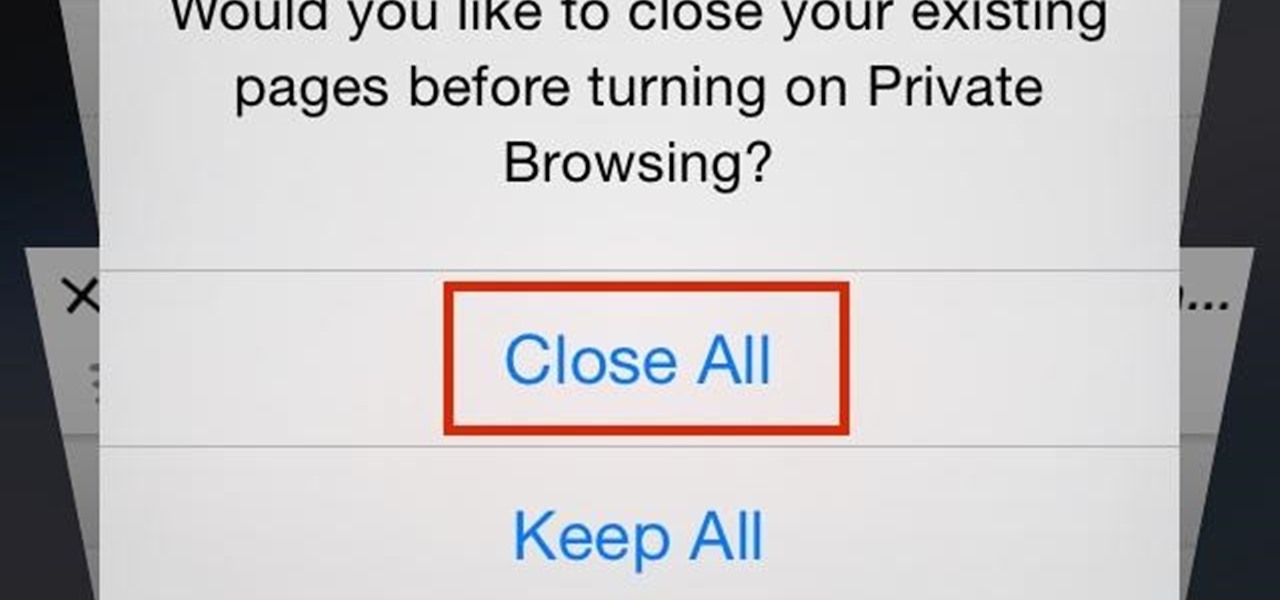
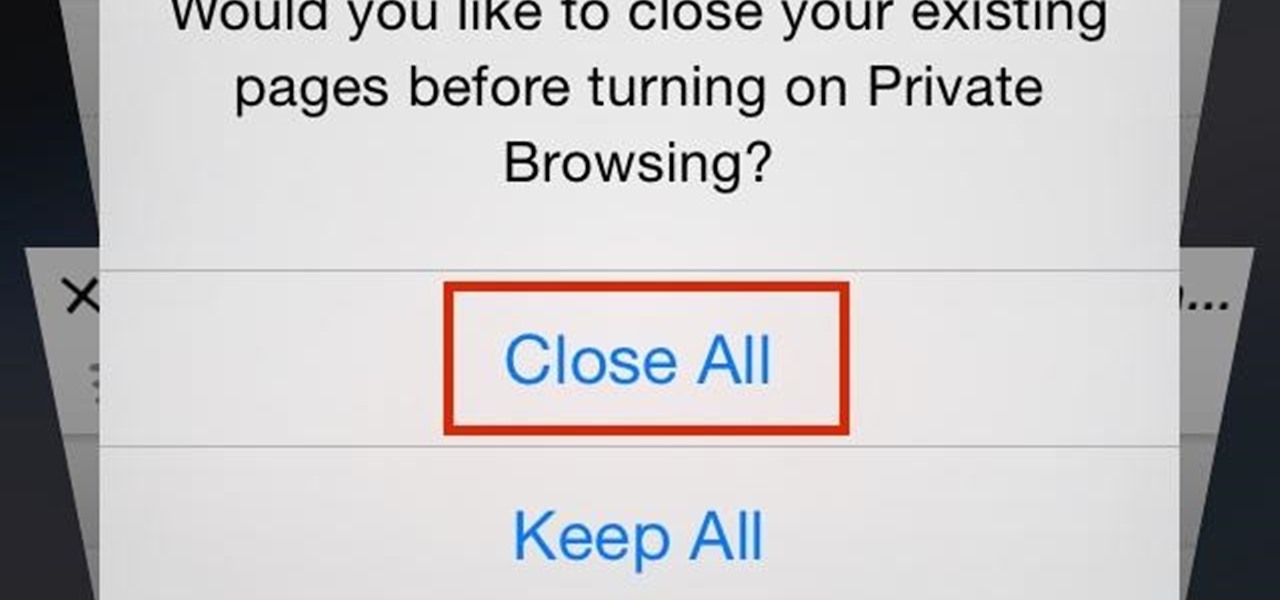
Closing all of your tabs open in Safari is not an exceptionally quick task—you have the choice of either tapping the X on the left edge of each page or swiping each tab to the left of the screen. If you have a load of tabs open, you'll have to swipe or tap through all of them. Instead of wasting time, I'm going to show you the quick way of closing all of the open tabs in Safari.

Stay secure on public wireless networks by making your own FREE virtual private network (VPN). This tutorial shows you how to set up an OpenVPN server and connect to it from your laptop.

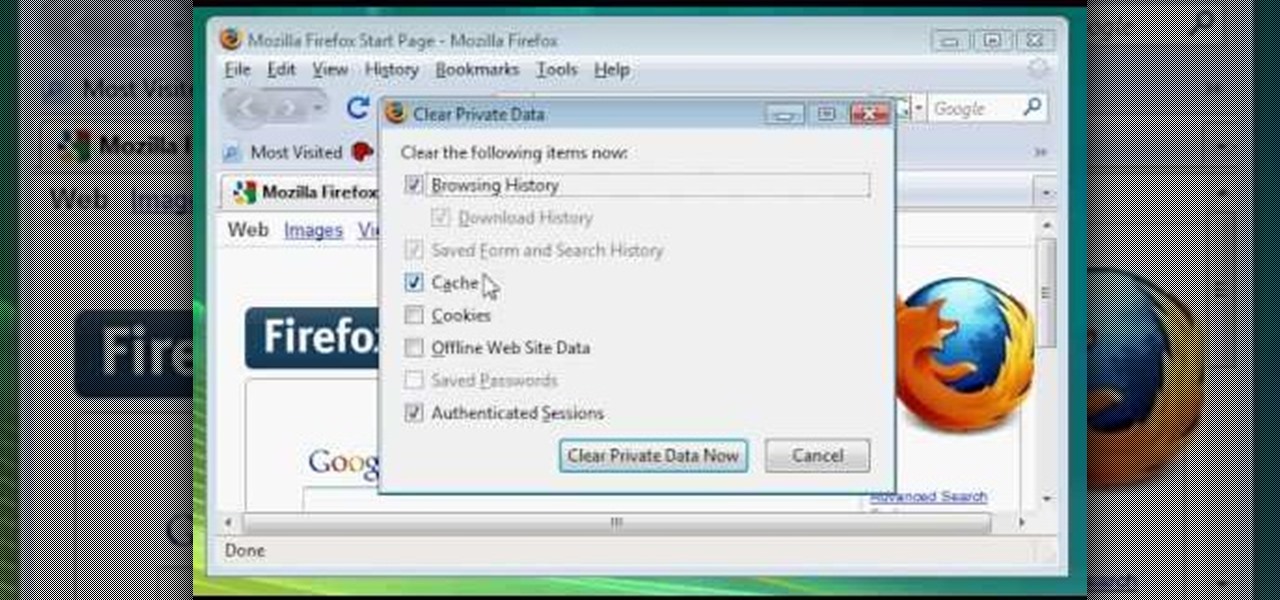
In this video, we learn how to clear browsing history and cache in Firefox and Internet Explorer. First, while in Firefox, go to the tools menu, then click on clear private data. In the new window, click on the items that you want to have cleared, then click "clear private data now". After this, the computer will clear out all the internet files. Next, while you're in Internet Explorer, go to the tools menu, then click on "internet options". Once in here, click the appropriate sections to cle...

With the spread of smartphones and free online games, the "Freemium" model of product distribution and monetization has become prevalent over the last several years. At it's essence, it is handing out software products for free and then allowing customers to pay for in-software services using microtransactions. This video features some businessmen who do business in iPhone apps discussing how they use "Freemium" systems in their apps to make the most money possible while providing great servi...
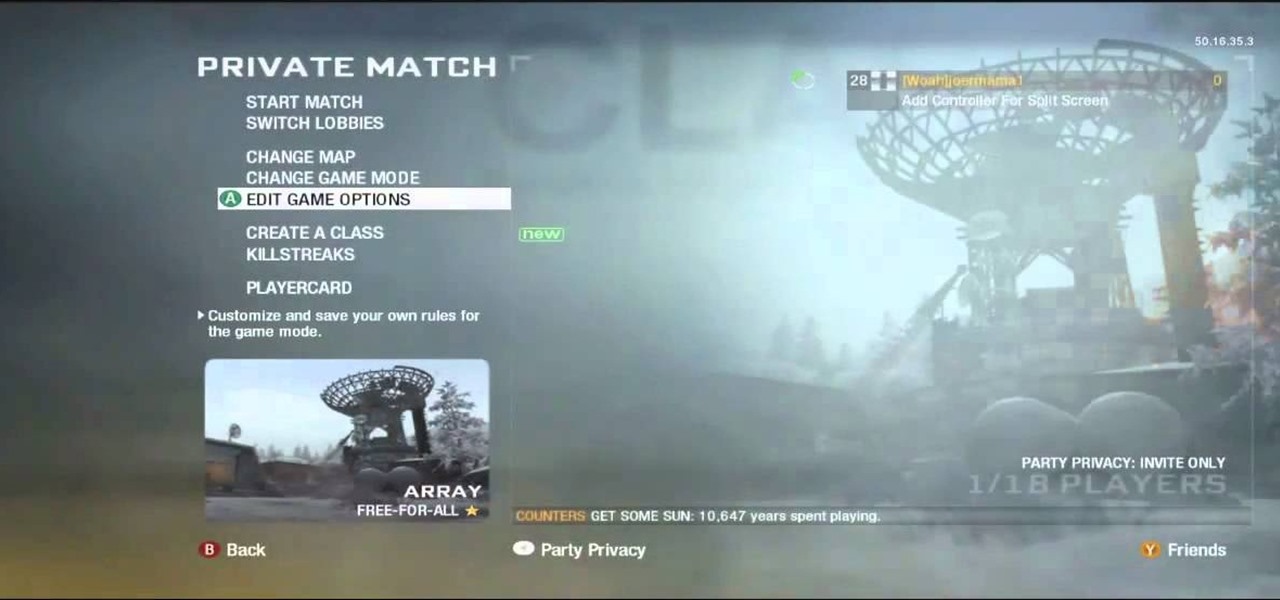
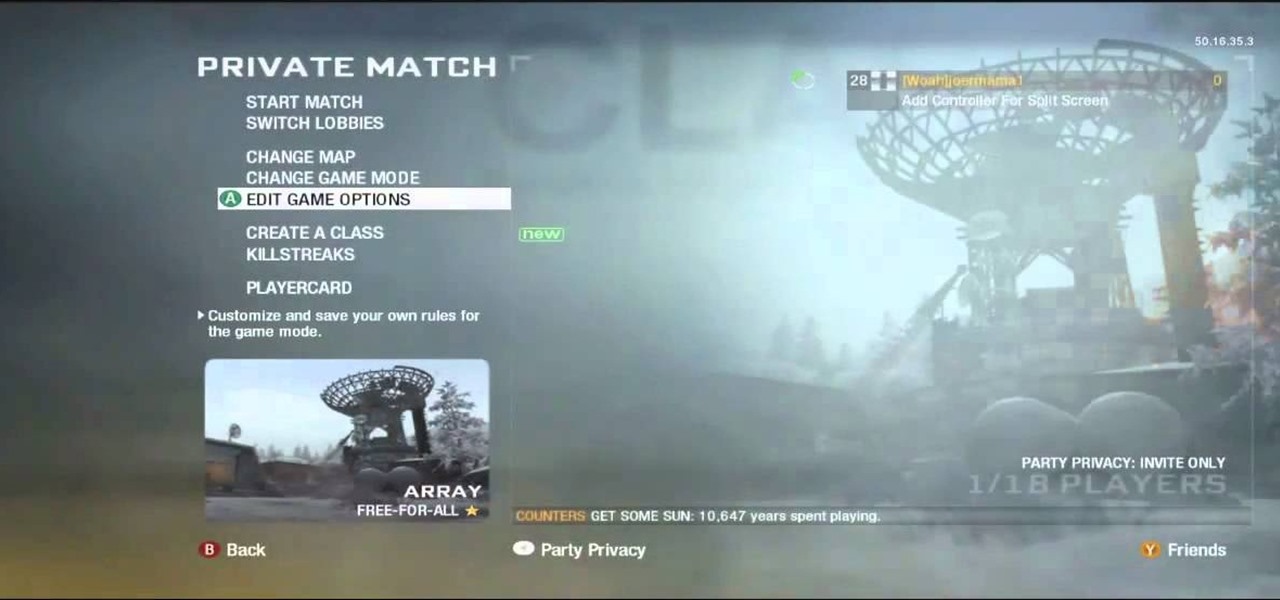
There aren't a lot of games with 3D maps where you can't break out of the levels in some way, and Black Ops is not different. This video will teach you a barrier breaker that you can use to get out of every multiplayer map in the game. Only use this in private matches unless you want it to go away!

Ever wish there were a way to upload a video to YouTube without making it available to anyone with an Internet connection? While you might know about the option to make your uploaded clips private, limiting their viewing to 25 users of your choosing, you might not know about the newly introduced "Unlisted" status, which allows your videos to be viewed by only those people who know the video's direct URL. For more information, watch this free video guide from Tekzilla.

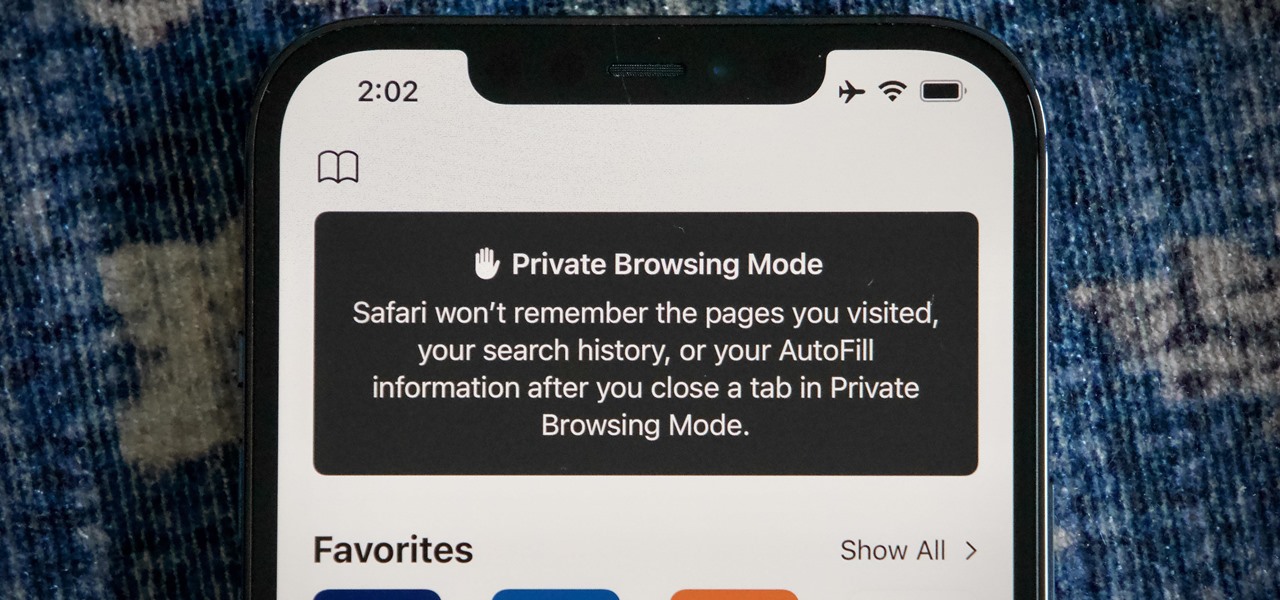
When you open Safari for the first time after updating to iOS 15, you'll instantly notice its search bar is now at the bottom, and its Page Settings menu has moved with it. For tabs, moving between them is as easy as swiping on the Tab Bar or selecting one from the new grid view, but you may get confused whenever it's time to open a private window.

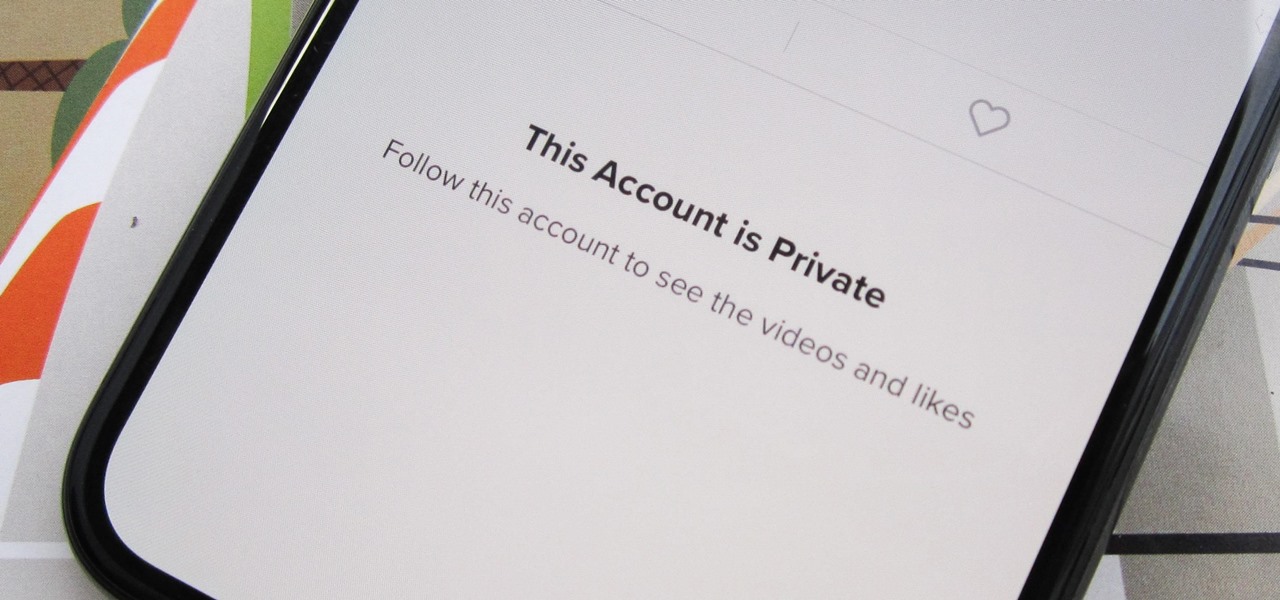
Can you trust every user you come across on TikTok? The answer to that may depend on how use the service, but the real question is — can you trust every user that sees your content? Not everyone on TikTok is someone you want viewing or interacting with your content, and there's a way to prevent them from doing so.

Apple has billed ARKit as a means to turn millions of iPhones and iPads into augmented reality devices. The refrain is similar for Kaon Interactive, a developer of product catalog apps for businesses.

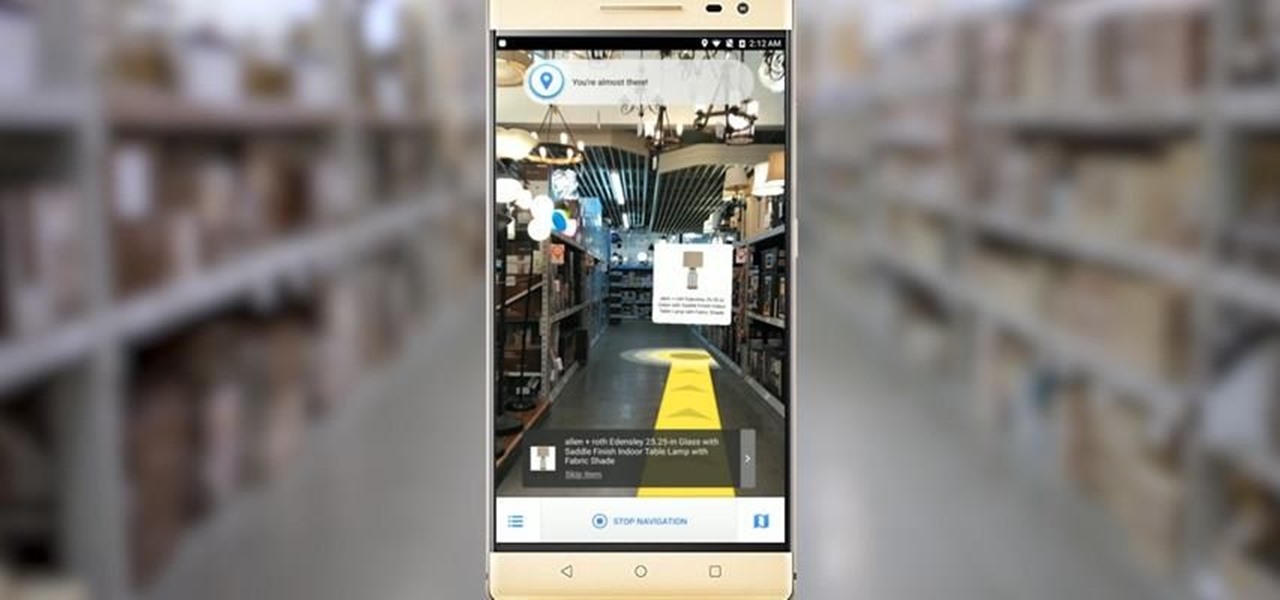
Lowe's Home Improvement laid another brick in their augmented reality foundation with today's announcement of a new app for Tango-enabled smartphones.

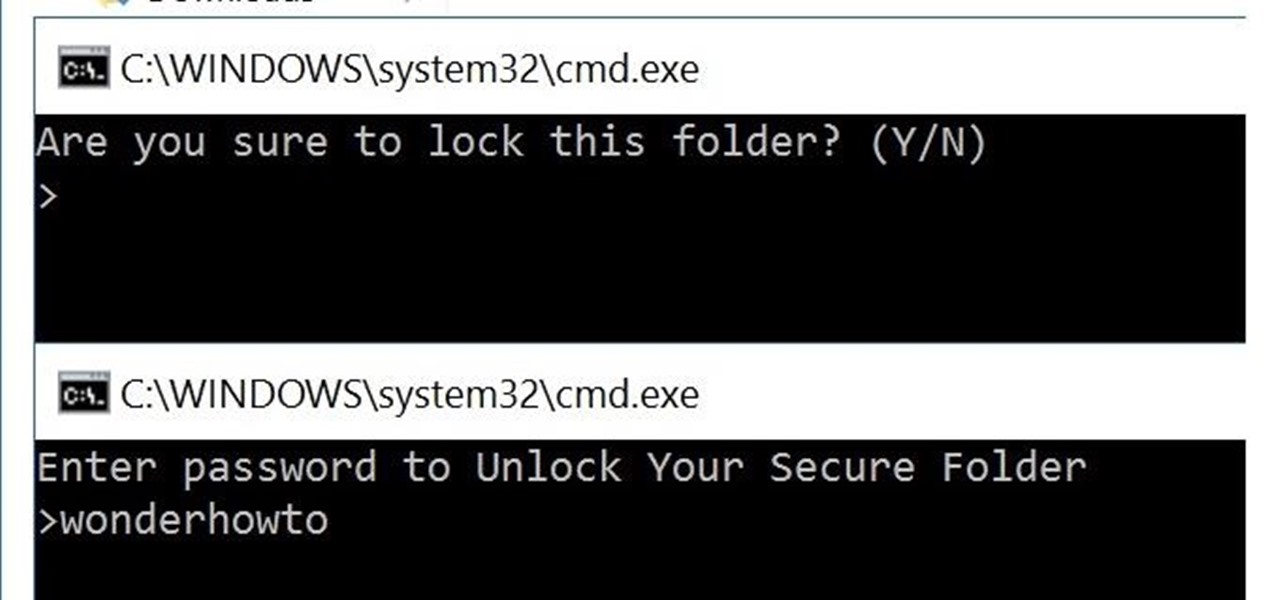
You can easily lock any folder on your Windows computer with a simple Notepad hack. By creating a batch file, you can hide a folder and require a password be entered before it becomes visible and accessible. This is a great tool for locking sensitive information, like pictures, financial statements, and a lot more.
I've noticed that a few people using the crypto-currency, Bitcoin are having issues importing private keys to their Bitcoin wallet. This is easy to do and doesn't require anything other than your Bitcoin client/daemon (as of ver0.6.0 ) and the command line.

In this video from apexcctv we learn how to find your public IP address and then use dynamic DNS to keep it updated in regards to your security needs. If you go to Whatismyip.com you will see your IP address. You can also go to Google and search for "find my IP address." A service called Dynamic DNS keeps track of your customers IP address. It will map a name to an IP address. Static DNS entries do not change. To set up DNS you can go to CCTV tutorials on the ApexCCTV website. You should set ...

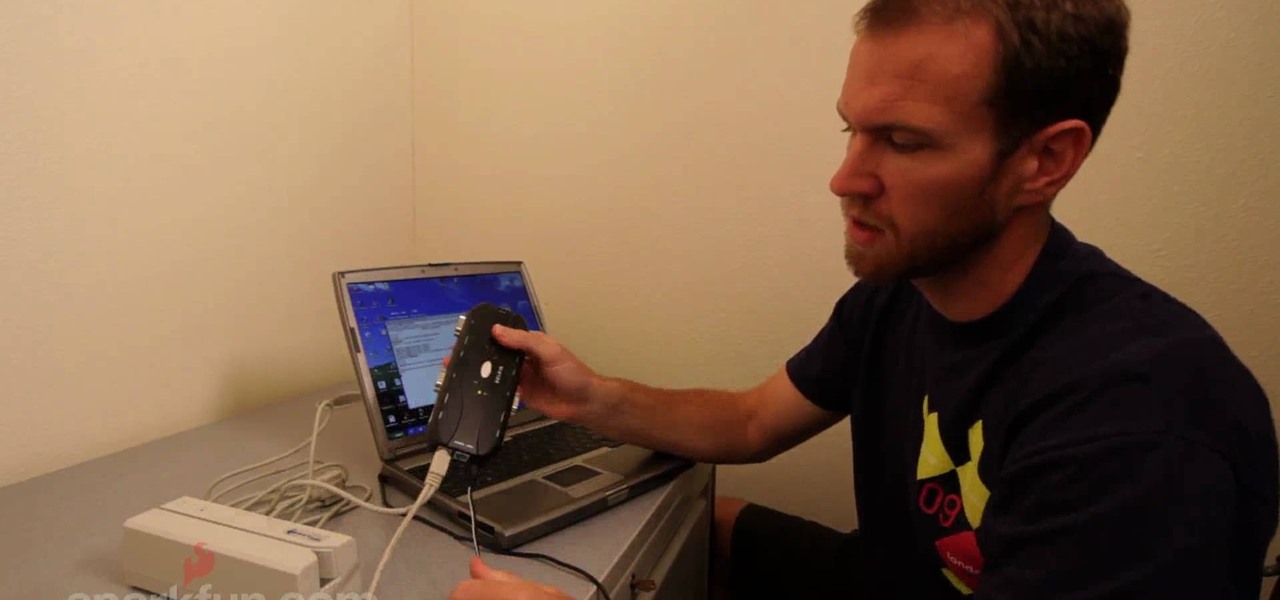
Magnetic card readers can make e-transactions far simpler, especially for people who are running their own small business. You can also watch this video to learn about card writers, which can let you create your own magnetic cards (such as a membership card) to track your customers' activity.

In this tutorial, Brian teaches us how to make your wireless network secure. First, go to the start menu, then go to run and type in "cmd", then type in "iconfig /all". Now a new window will pop up and you will look for the default gateway. Find the IP address to log onto the routers you have. Now, type in your IP address into your address bar on your internet browser. You will be asked to log into your account with your password and user name, which you can find at the manufacturers website....

Lady Gaga is one of the most secretive women in show business, hiding behind her stage performer mask and outrageous costumes so often that we can hardly believe there's a real person underneath all that fluff.

If you're worried about having your private information taken away from you by hackers and other malicious people, this tutorial may help you. This tutorial will help show you how to easily use and understand the phishing filter in Internet Explorer 8. It only takes a couple of clicks to activate and can be the difference between making sure your private information is secure or out in the open for others to use. Good luck and enjoy!

This video tutorial from ChaminadeENN shows how to set your Facebook account to private mode. First what you need to do is to sign in to your Facebook account.

You can use surveillance skills to pursue a career as an investigator or to spy on whoever you like. You will need to have a mobile means of making observation and this might include things like pen and paper, camcorder or camera.

Here Danny Beales shows you how to quickly clear your Firefox cache and cookies. To clear your Firefox cache, do the following: Go to Tools Clear Private Data Select which data you would like to have cleared, and click on Clear Private Data. Your cookies and/or cache has been cleared. Remember to do this from time to time, because it will help speed up your browser's performance as well as keep harmful cookies from tracking your browsing.

This video shows you how to easily delete cookies from your browser. First thing you have to do is open the web browser you usually use (the video shows how to delete cookies from Firefox) and go to the Options tab in the upper menu. Then choose the Clear Private Data or Clear Recent History item. In the pop-up window, check Cookies and Cache and then press the Clear Now button. The Clear Private Data/ Clear Recent History window also can be opened by pressing CTRL+SHIFT+DEL. That's it! Good ...

The SATs are a very valuable college entrance test and could determine if you're accepted or denied to your favorite university. So, once you've learned to ace the SATs and have already taken your test, get your scores as soon as they're out! Don't sit in dreaded anticipation— go to College Board and get your SAT test results now!

When you need a website to showcase your product or service, it can be quite confusing. Follow these easy steps to gather everything you need to have a successful website. Start your search for a domain name in the domain name registrar. (Example: www.companyname.com) Rent space from a hosting company to hold the files for your website. Set up an email account for your company. Create the content for your website (example: products, prices, services, etc). Get internet security to protect sen...

If there's one company that is a fan of the TrueDepth camera on Apple's iPhone X devices, it's the popular eyeglasses retailer Warby Parker.

As penetration testers, we sometimes need to securely store customer data for prolonged periods. Bruteforce-resistant, vault-like containers can be created with just a few commands to protect ourselves from physical attacks and unintended data disclosures.

Hi all, Pro Hackers/Crackers, Let's see how we can use batch for our own Protection instead of exploiting someone with it.

This time on the show, bypassing restrictive firewalls with a free and open source virtual private network server for Windows and Linux that will have you connecting back to the home or office with just a web browser! Best of all? It's free! Check out this video for detailed information on how to build an SSL VPN.

Data thieves don't have to be programming wizards to get their hands on your personal information. They often find hard drives that contain financial and other sensitive data at flea markets, charity shops, the city dump—even on eBay. In this video tutorial, PC World explains how to completely erase sensitive data from old drives before recycling or discarding them. Wipe your old hard drives with this how-to.

Circular breathing will enable you to play your didgeridoo continuously. In this movie we'll show you how easy it is by breaking the process down in to small simple steps.

If you prefer to use Google or another search engine for everyday browsing in Safari but would also like a more secure browsing experience for all your secret searches, there's a simple way to switch between them quickly while also adding additional layers of security on top of your already clandestine browsing.

It's a good sign for any emerging technology when one of the leaders of an industry adopts it. So when Mastercard, a brand so recognizable that it dropped its name from its logo at CES last year, decides to develop a mobile augmented reality app, the moment is a milestone for the AR industry.

There's nothing wrong with indulging in guilty pleasures on Spotify every once in a while — we all need a little Coldplay and Creed in our lives. The only problem is, all of your friends and family might be watching. Anyone that is following your Spotify account can potentially see what you're listening to, but there are several ways to hide this shameful and embarrassing activity from the world.

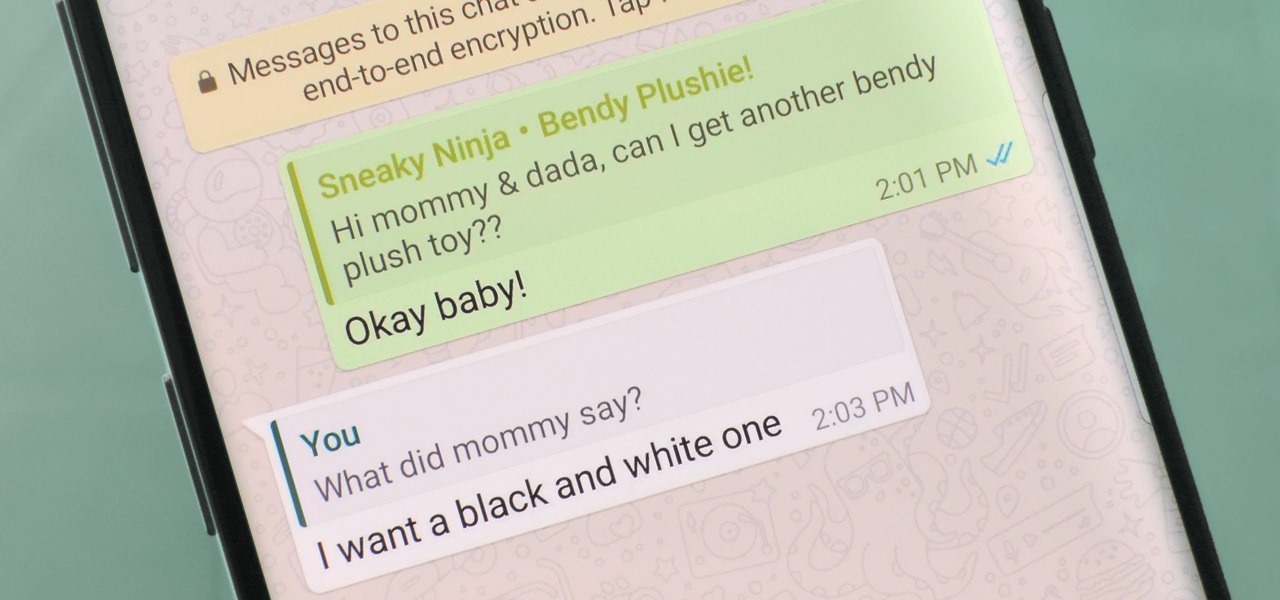
Group chats in WhatsApp are great for communicating with multiple people at once, but that can be a blessing and a curse — any message you send will be seen by everyone, and that's not always ideal. Thankfully, there's a new feature that lets you respond to group messages privately.

If you're playing word association with the terms "augmented reality" and "automobiles," your first thoughts probably center on navigation displays in cars or virtual models of exotic vehicles.

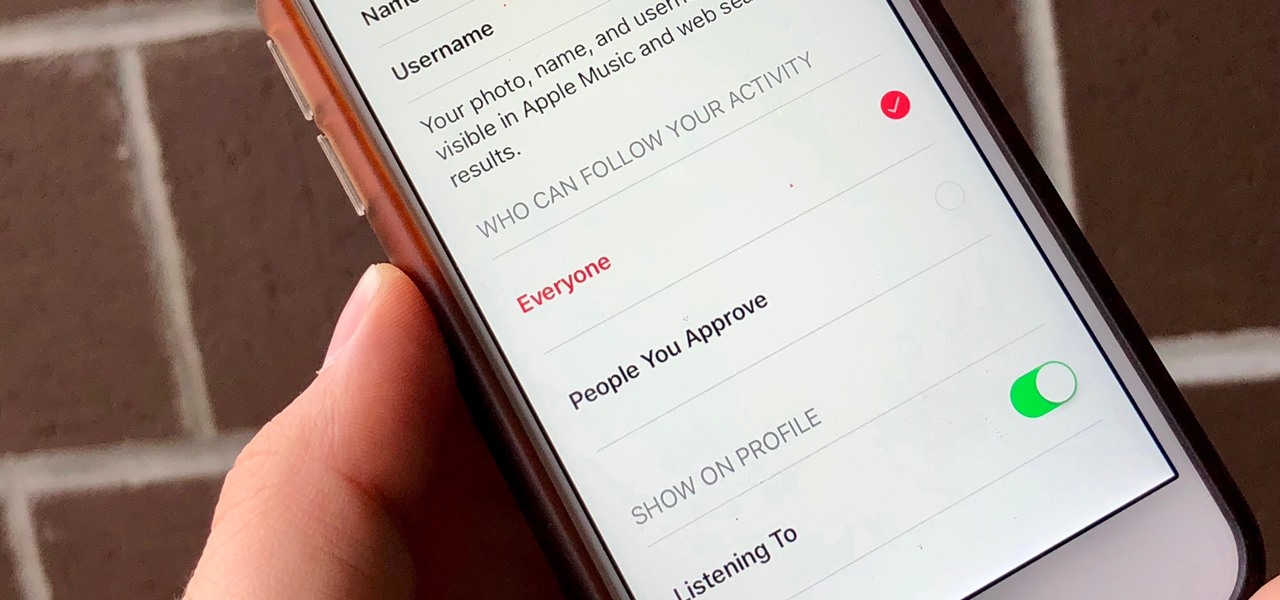
Apple Music, Apple's answer to Spotify, has many interesting features packed in to make that $9.99/month price tag as attractive as possible. One of those features is geared towards social listeners — those who want to follow other Apple Music users and who want to be followed back. But here's the thing: how do you know if your account is public or private?

Verizon has long been king in the wireless provider market, but recently it has had to step up its game in the data department. A limited data plan — with supposedly superior service — was no longer cutting it for customers. Many of whom left to take up the sweet, sweet offers of competitors like Sprint and T-Mobile. This past fiscal year, Verizon had a net loss of customers in the first quarter. Something that has never happened to them before.

Apple made headlines last month when it announced it would acquire the popular application Workflow. Now, the company should be making waves again with the news that they will reimburse customers who purchased the app.

Ideally, wine would stay as perfect and delicious as the day it was first uncorked forever. But, thanks to a pesky process called oxidation, re-corked wine (no matter how you do it) pales in comparison to a fresh's bottles original magic.

When it's most important for me to browse the web incognito, I always seem to forget to enable private browsing. If that sounds like you, it's time you stop making that mistake for good. Manually deleting the cache and browser history is a thing of the past, and as it turns out, so is manually switching to incognito mode.