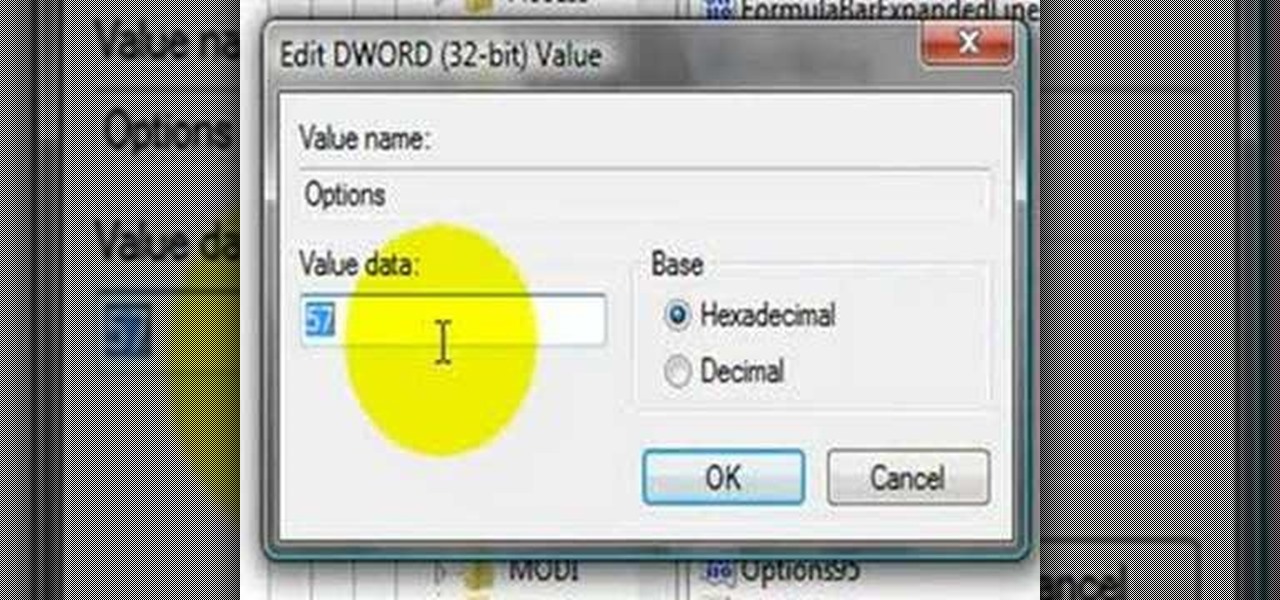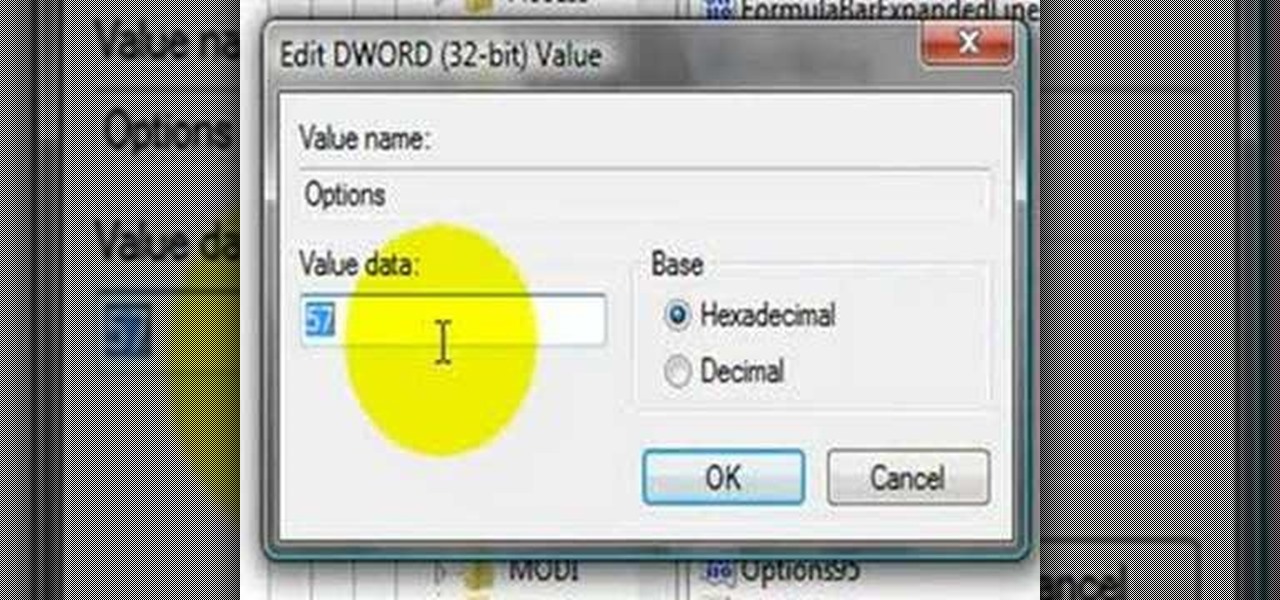
This video shows us the method to block the formula bar, scroll bars and the status bars in Excel. Click on 'Start' and type 'regedit'. Click on 'regedit' and go to 'HKEY_CURRENT_USER'. Open it and go to 'Software' and 'Microsoft'. Expand it and go to 'Office' and open the version of Office on your computer. Expand it and go to Excel. Choose the options folder. Go to the 'Options' item and right click on it. Go to 'Modify' and type 150 in the text box. Click on 'OK'. Now restart the Excel and...
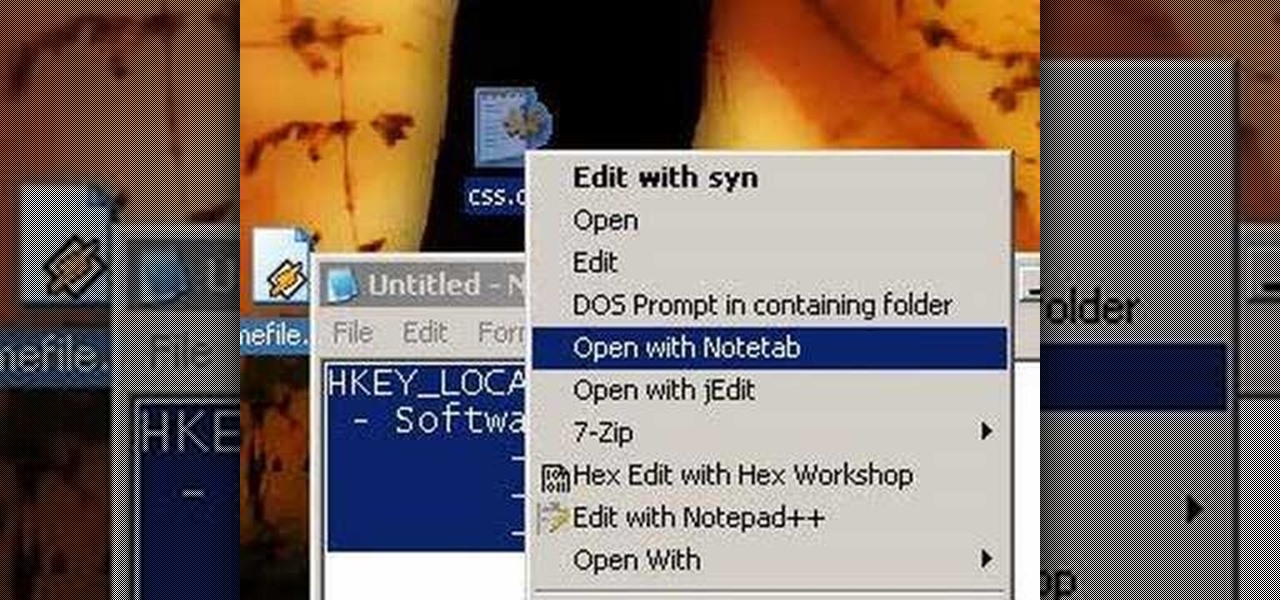
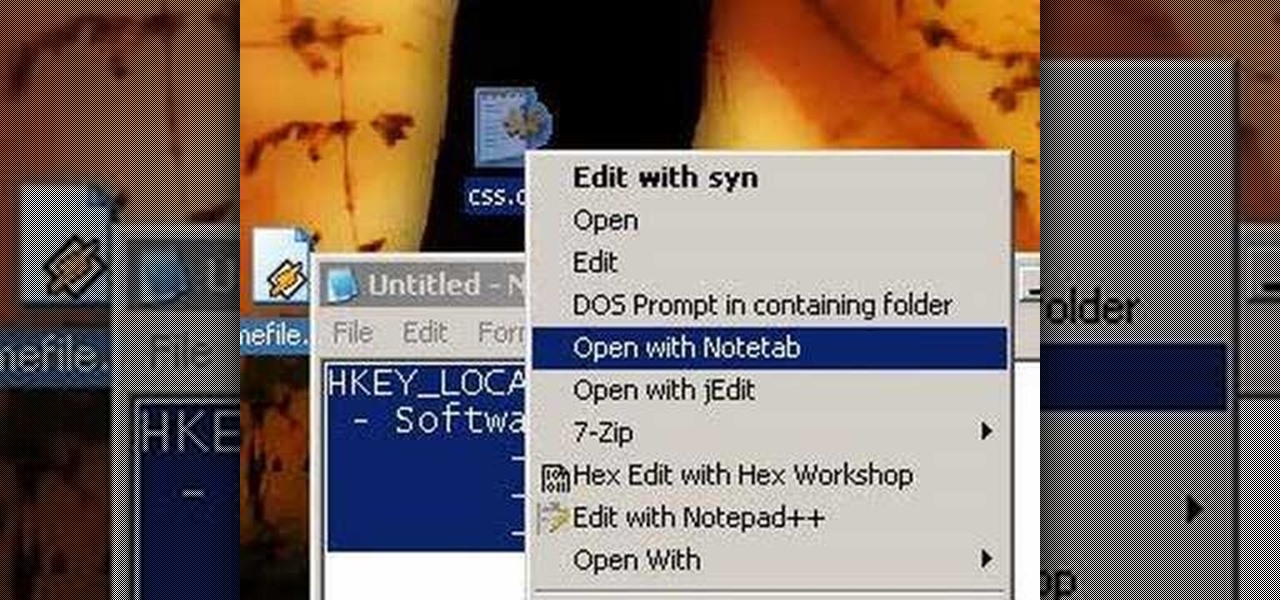
Whenever you right click a file in Windows it opens up the context menu, which gives you options of what to do with the file. Learn how you can add your own custom options to the context menu by editing the Windows registry.

In most cases, when the free trial of software is over, that's it—you're left to either pay for it or find an alternative. But what happens if the trial wasn't long enough to sell you on the product? It'd be nice if there was a way to test it out again without having to whip out your credit card.

Baby showers are fun ways to celebrate new mommy-hood. You won't want to forget the traditions though. Check out this video before you start planning and make sure you have an nice balance of etiquette and fun.
IS THIS ANNOYING? Would you rather not subject others to the virtual VITUPERATION implied by CAPS LOCK? This video will show you how to use these registry tweaks to disable caps lock on your Windows 7 or Vista PC.

Why can't you play DVDs in Windows Media Player? Who knows, but this video tutorial will help you tweak the settings in Windows XP to start watching DVD movies in Windows Media Player 11 in no time. It's a simple registry tweak that enables DVD usage, so you don't have to buy or download another program to play them.

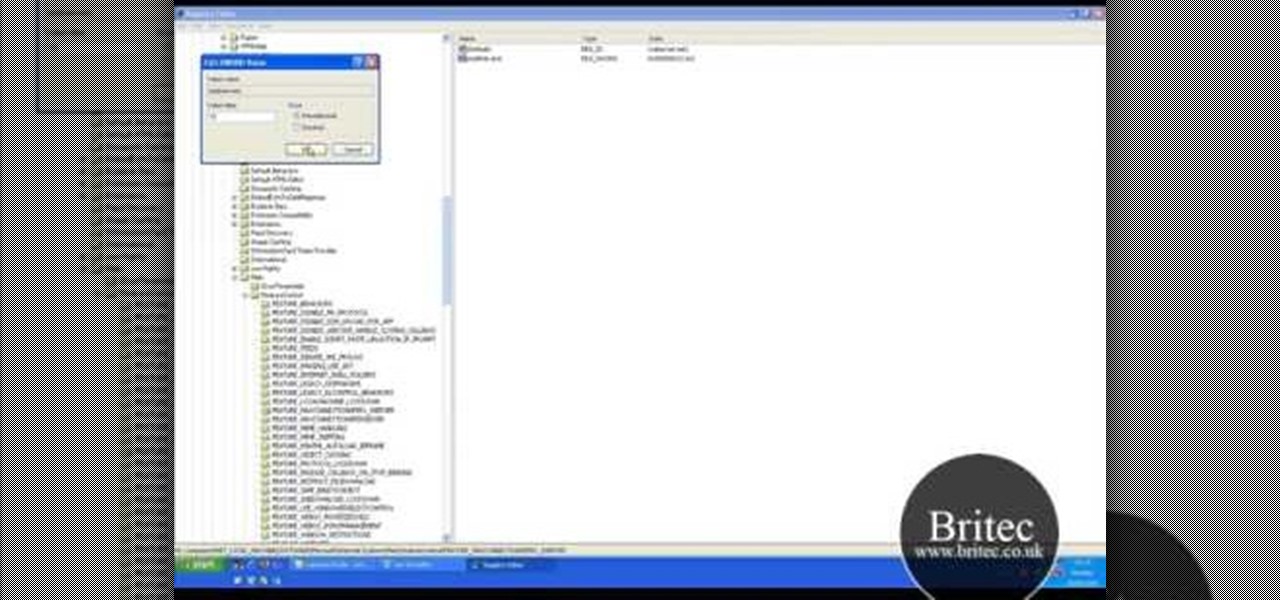
Want to increase the maximum number of possible connections in version 8 of Microsoft's IE web browser? With this little registry hack, it's easy! So easy, in fact, that this home-computing how-to from the folks at Britec can present a complete overview of the process in just over two minutes. For more information, including step-by-step instructions, take a look.

Want to know how to make HijackThis, the popular malware scanning program, display only malicious registry entries? Learn how to use the Ignore List to acheive just that with this free home computing how-to from the folks at CNET TV, which offers complete instructions on how to tweak HijackThis to make removing viruses and spyware a breeze. For more information, and to get started protecting your own Windows PC from malicious software, watch this handy how-to.

Imagine this scenario: You exploited a system using metasploit and you want to install a backdoor. You have a few options;

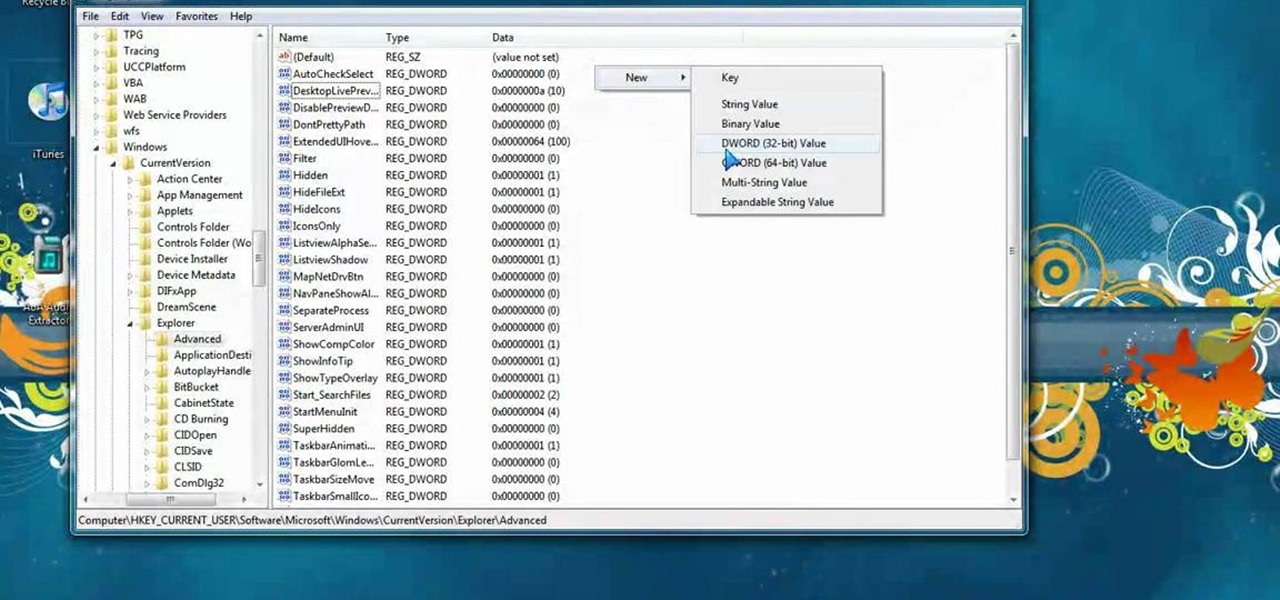
In this video, we learn how to tweak Aero Peek and Desktop Live Preview on Windows 7. First, go to registry editor, then current user, then software, then Microsoft, and go down to Windows. After this, click on current version, explorer, and advanced. Now, right click on the white space and click "new keyword value" and name it "desktoplivepreviewhovertime". After this, double lick and change it to decimal, then change the value data to 10. Next, create another keyword value and name it "Exte...

Tired of being limited with your right-click options in Microsoft Windows? There's a program that could help you out, and it's called Right-Click Extender. Insert many different additional items to the right-click context menu.

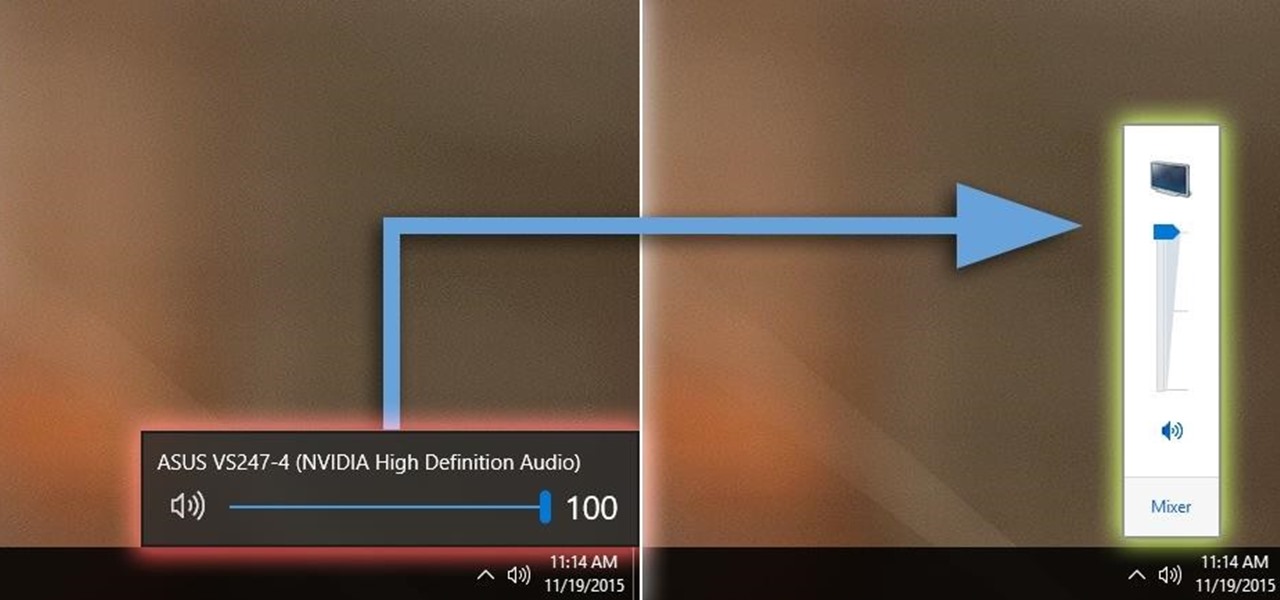
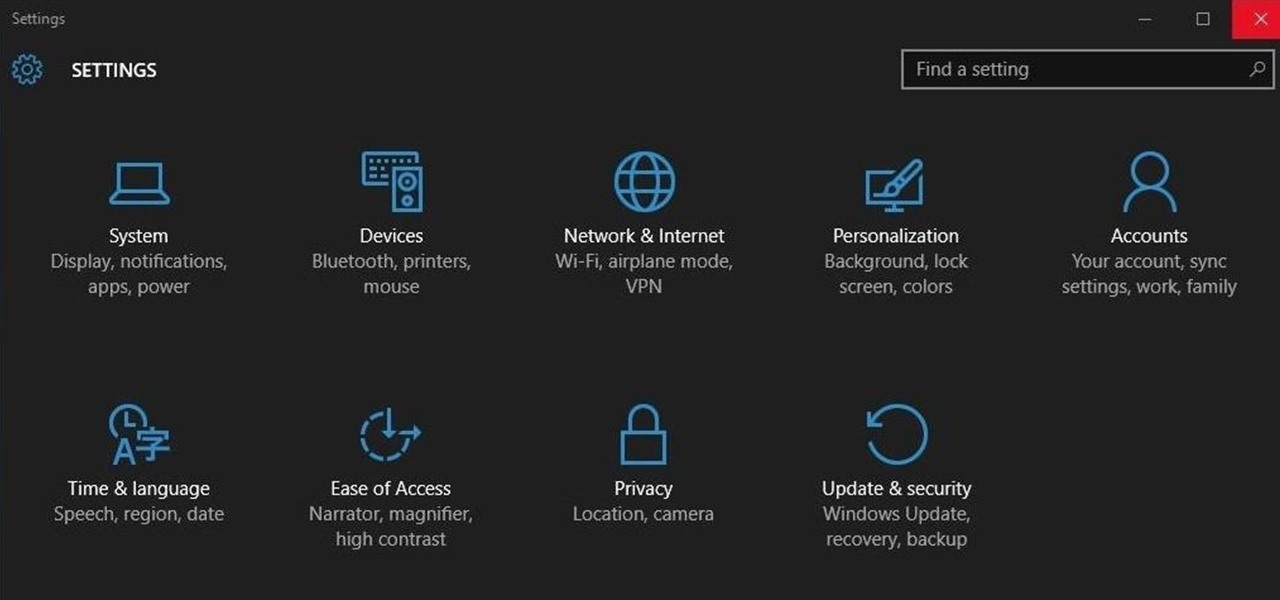
Windows 10 definitely has a sleek and modern look to it, but some of these visual changes have been made at the expense of functionality. For instance, the slider that appears when you click the volume icon in your notification tray now sports a completely minimalist look that lacks the quick link to the full volume mixer from past Windows versions.

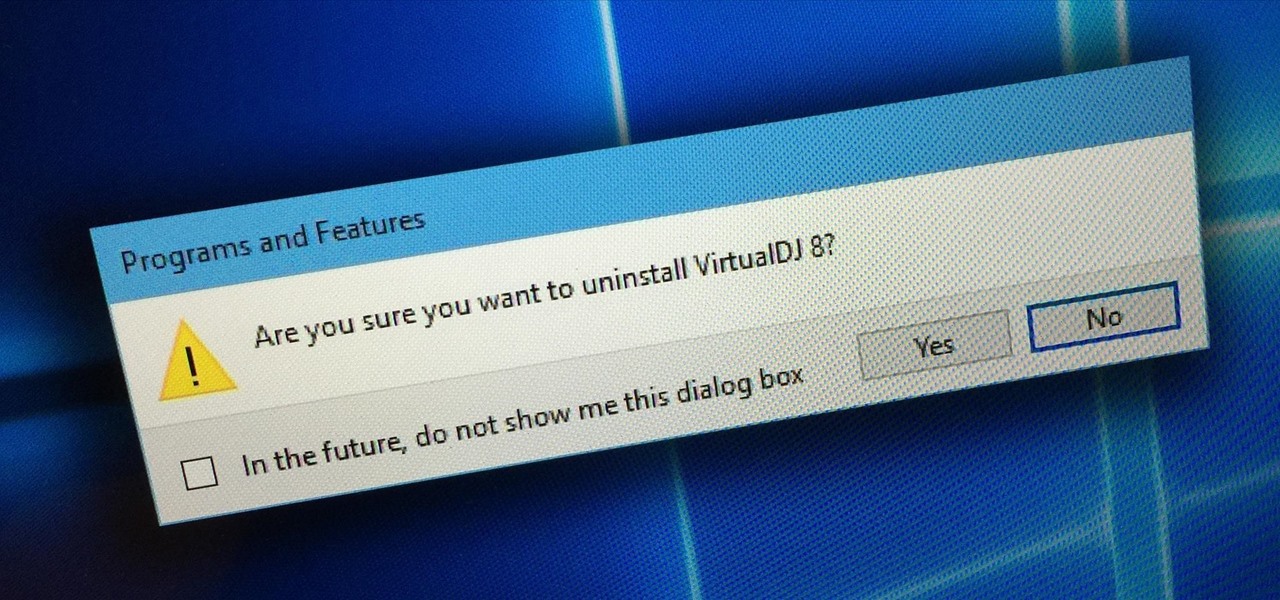
Uninstalling programs in Windows is not the nicest procedure. Some programs bundle a nice uninstaller with them which helps to ease the process. Other programs, mainly those that utilize the Windows Installer technology, begin the uninstall process right away. This can potentially be problematic for users who are trigger-happy with the mouse.

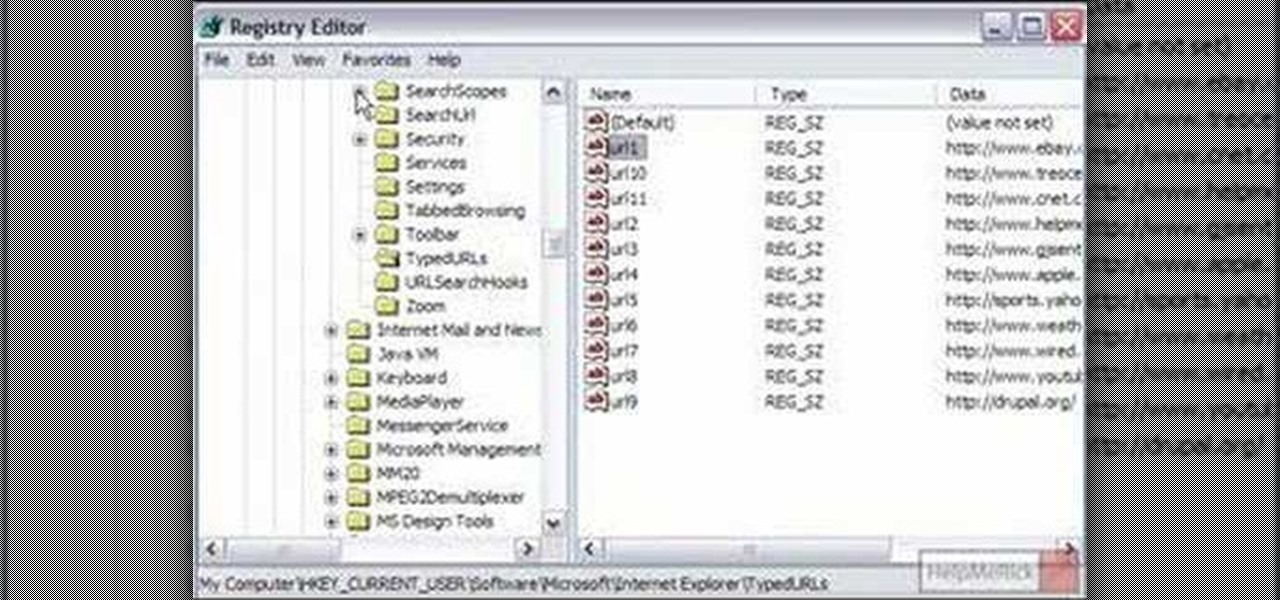
Ever wondered how to go about deleting individual entries from the Internet Explorer address bar? While it's possible, it's not particularly easy. You can do it all at once by purging your entire history through Internet Options or you can hack your Windows registry. For more information, or to try this hack for yourself, take a look!

OneDrive, formerly known as SkyDrive, is a free online storage solution developed by Microsoft. If you're a fan of using cloud-based storage systems, then OneDrive offers you plenty of benefits. It's also heavily integrated into Windows 10, including the new File Explorer, in an effort to make utilizing OneDrive easier for you.

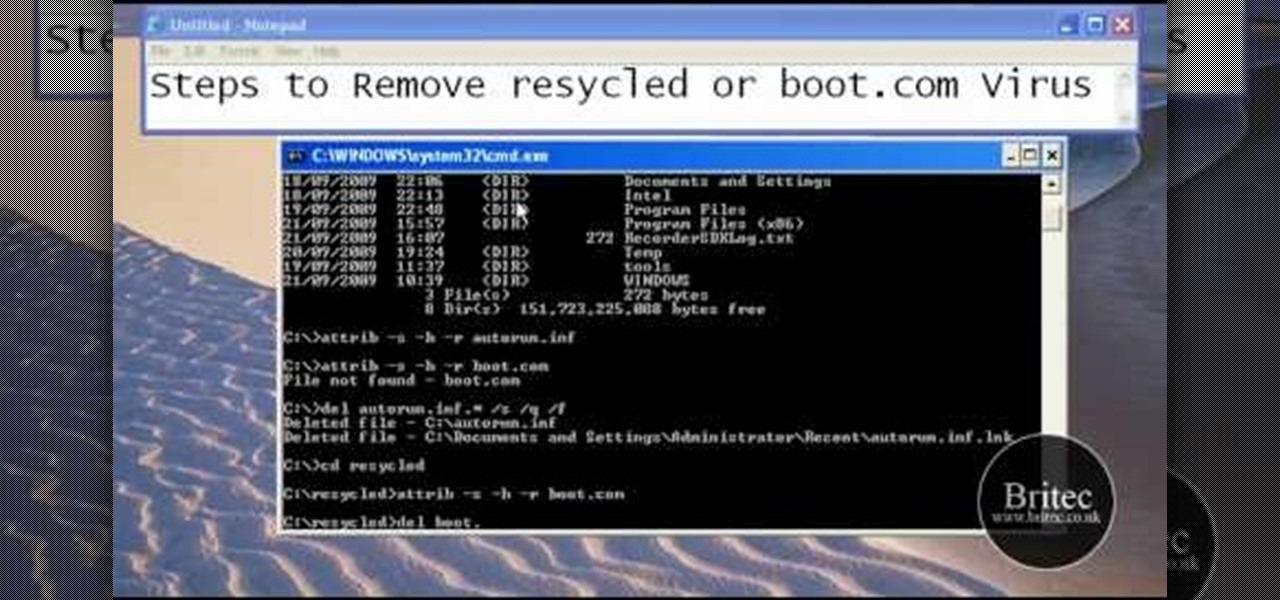
This tutorial describes the procedure to remove autorun.inf and boot.com virus. This virus is commonly called as resycled/boot.com virus, which could damage the system files and may steal important information from the system.This can be removed by any malware / spyware remover like Malewarebytes.

Windows 8, the latest version of Microsoft's flagship software has introduced the new Metro UI screen as a replacement to the classic Start menu. If you want to get rid of the Metro UI, or you want to get the Start menu back, follow the directions detailed in this video

It's easy to restore lost browser bookmarks from a backup copy. Here are step-by-step instructions for Internet Explorer and Firefox.

Start by clicking start and type regedit in the search box. Hit enter and when the screen opens go under hkey current user and click on control panel and then desktop. Under desktop go to menushowdelay. Under menushowdelay right click and then click modify. In the box that pops up set the value to zero and click ok. Then close the registry editor. Next you will want to download ram booster 2. 0. Once you have downloaded and installed the ram booster program you will want to edit your options....

Privacy is important. Whether its a telemarketer or a crazy ex, sometimes you may need to block someone from contacting you. With this tutorial, learn how to get rid of those pesky callers.

Welcome back, my aspiring hackers! In many of my earlier tutorials, I mentioned the complementary nature of hacking and forensics. Both disciplines, hacking and forensics, benefit from a knowledge of the other. In many cases, both disciplines will use the same tool. In this tutorial, we will use another tool that can be used in either discipline—Sysinternals—a suite of tools developed by Mark Russinovich.

Check out this tutorial and make Windows 7 you're own by customizing the log in screen. This is fun to do and will, no doubt, make you feel more connected to your PC.

Level up on Happy Aquarium by hacking it with Registry Helper. Huh? No Cheat Engine? See for yourself. This won't work for all computers, so test it out for yourself.

Sometimes shit goes down on your home computer and you're just not able to be home to fix it. After all, most of us have commitments such as school, work, and volunteer activities that keep us away from our home computers for most of the day.

Earlier this week, Spiderlabs' vulnerability researcher Jonathan Claudius discovered a key in Windows 7 and 8 registries that makes it easy for anyone with physical or remote access to a computer get a hold of the user's password hints. When the "UserPasswordHint" key is read, the hints are displayed as a code that looks encrypted, but Claudius noticed a pattern of zeroes that could be easily translated back to plain text with a decoder he made in Ruby. He added this functionality to the Meta...

See how to build your very own computer! Just watch this video tutorial, in 22 parts, on how to make a homemade computer from scratch! This is a very detailed how-to on creating your own computer tower.

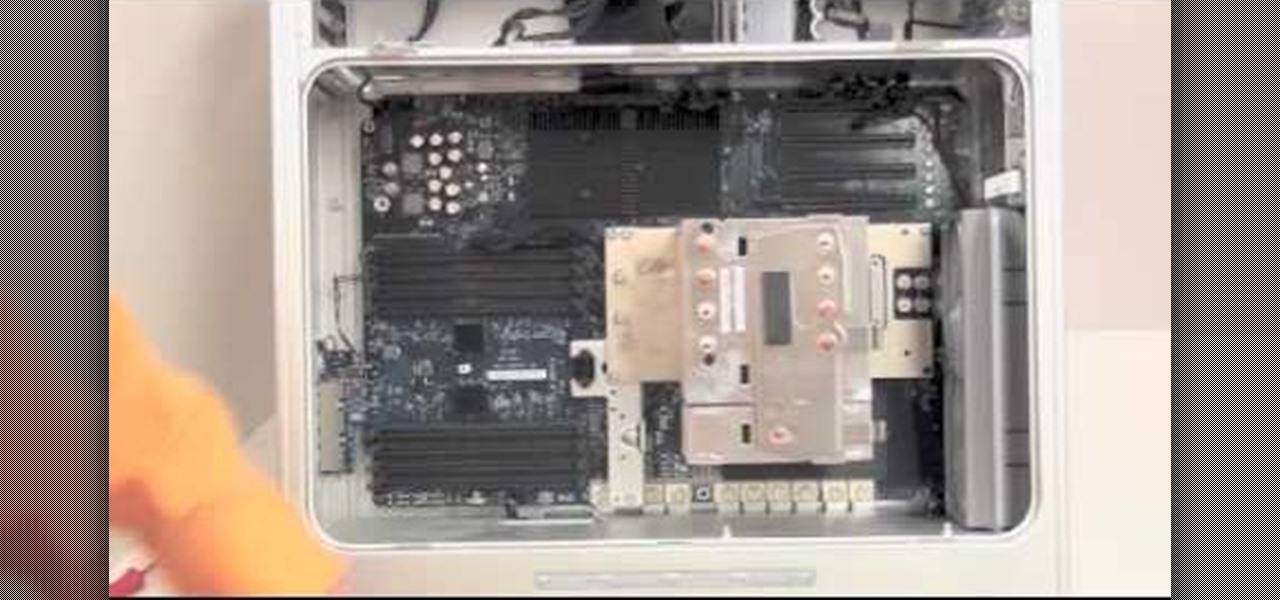
The Apple Lisa. It was first introduced in January of 1983, at a cost of $9,995.00, which today is around $21,693.00. It was the first commercially sold personal computer to have a GUI (graphical user interface). The Lisa's CRT monitor has a resolution of 720 by 364. If you want to know more about Apple's Lisa computer, watch the video and see how to disassemble it, too.

A brief tutorial on how to change the registry of your computer to perform quicker operations when you shut down, log off, or restart.

One of the most annoying of the many annoying types of errors on Windows computers is when you computer won't recognize parts that have always been a part of it, like the drives or keyboard. If your computer has stopped recognizing your CD or DVD disc drive, watch this video. As long as the drive is still connected, the steps in this video should allow you to fix the problem and continue using your drive.

Computers malfunction all the time in the form of freezing, crashing or by just not responding. This can happen due to various software reasons behind the comprehension of an average PC user. But by following some simple steps you can restore your computer some times. Your computer might not responding if there are lot of programs running simultaneously. This causes the available memory to be used up and there by causing your computer to not respond. In such case you can use you computer effe...

This is hardcore, serious hacking at its best. So it goes without saying that you probably shouldn't be attempting this computer hack unless you've successfully shut down your friend's computer at school using Command Prompt and sent out a fake virus to loved ones.

Did you know that someone could be watching what you're doing on your computer via another computer? That's right - if they are using VNC or Apple Remote Desktop software they can moniter what you're doing and even control your computer?

Watch this step-by-step tutorial on how to build your own PC computer for under $1000. This is a great, very thorough video!

Ah, the fabled dark mode. In the past, many users were delighted to find the existence of something called Royale Noir, a dark theme option that was available for Windows XP. Yet for reasons unknown, Microsoft had kept knowledge of Royale Noir a secret until some bright minds discovered its existence, and the rest is history.

There are two parts to the StormShield product: The server components (including the relational database and server) and the various agents that run on each endpoint. Among other things, the agent contains a host-based firewall and policy engine that can be customized to control applications and particular endpoint device features such as USB peripherals and registry entries. So watch this tutorial and learn how to protect your PC computer with SkyRecon's StormShield.

How to pick the right RAM for your computer

Can't turn on your computer? The power button might be broke. If so, you're going to have to replace it, and you can do it yourself. See how to remove the power button from the Power Mac desktop computer.

Is your computer overheating? It may be because of a faulty fan. See how to remove the fan in the Power Mac desktop computer.

Want to upgrade your hard drive in your Power Mac? It's a pretty simple task, once you can get inside your computer. See how to remove your hard drive from you Power Mac desktop computer.

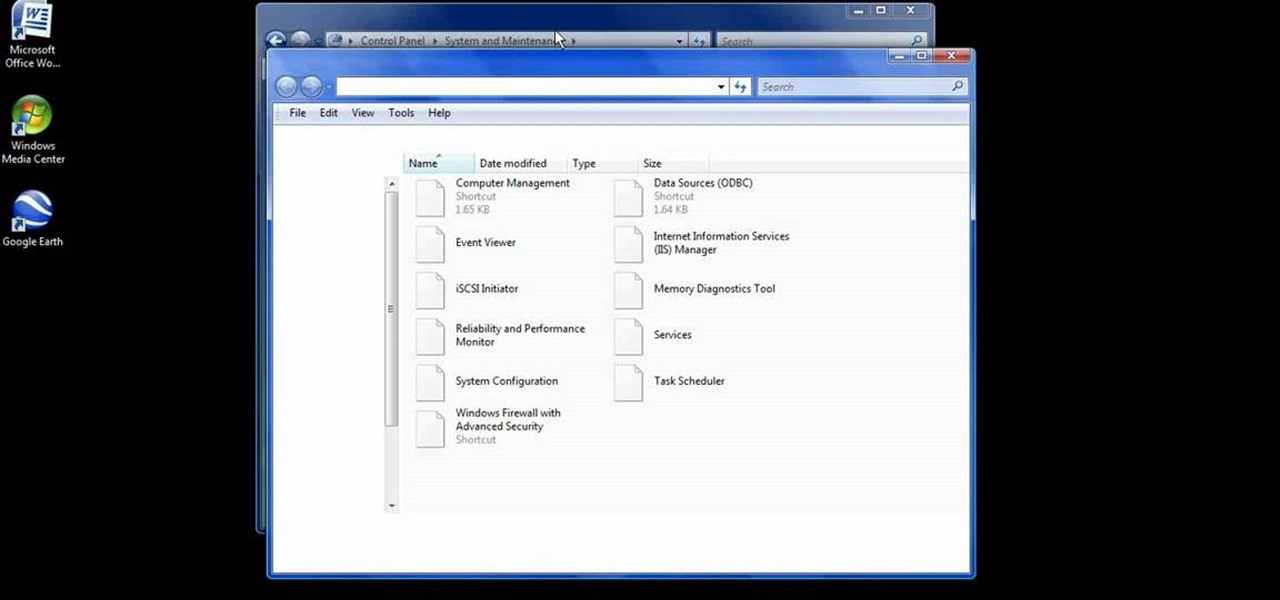
In this video, we learn how to easily defrag your computer's hard drive. First, go to the start menu on your desktop. Then, click on the control panel and then click on "system and maintenance". On the new page, click on administrative tools and then open up computer management. Then, click on disk management and then defragment for your computer. Let this defragmenter run on your computer until it is no longer loading on your screen. When it's finished you can view the results from the test ...