This video is about combining Microsoft Project 2010 and SharePoint 2010. This combination helps project teams to collaborate and share project information. Information can be displayed on a dashboard. We will also discuss various levels of project management such as starting the project, planning, tracking and reporting on the projects progress.

A pair of organizations recognized companies working in augmented reality for their innovative technologies over the past week. Meanwhile, another company used augmented reality for a sector that is overdue for a technology makeover, while another company has developed new camera modules that could usher in the next evolution of mobile AR.
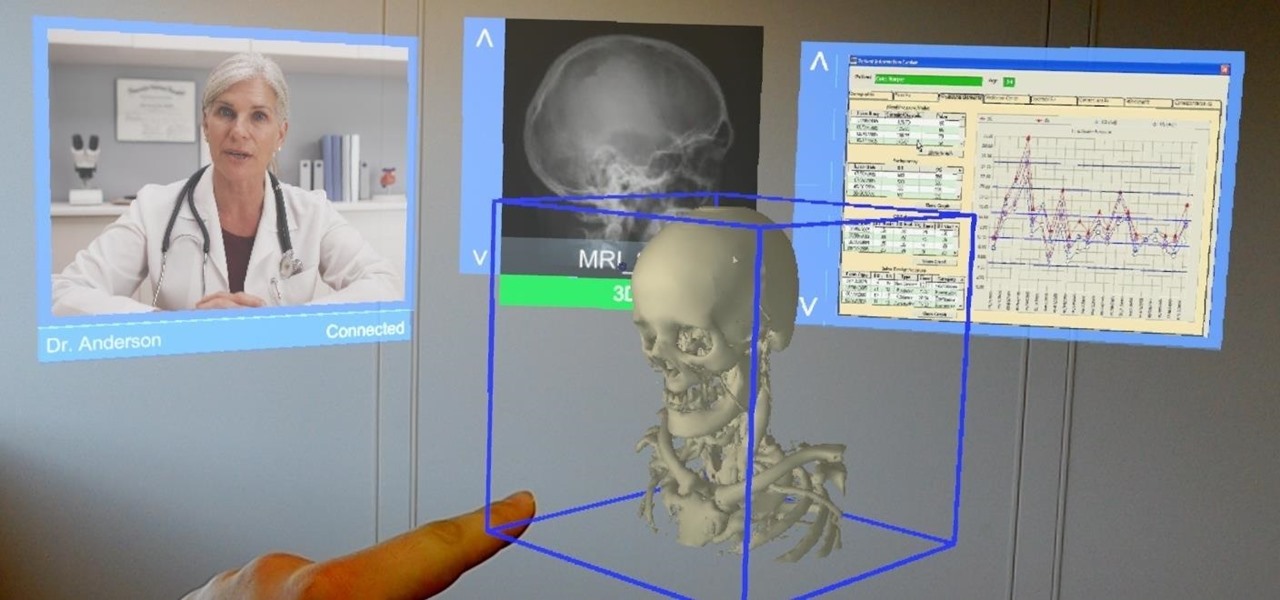
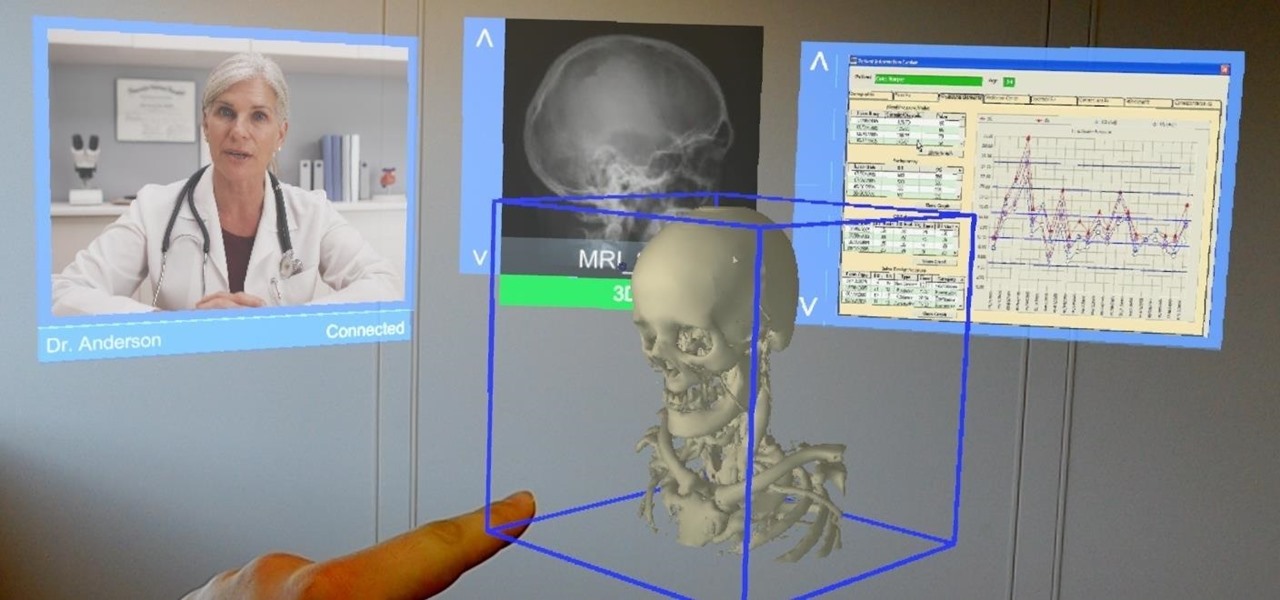
Augmented and mixed reality developer Arvizio is working on a suite of software solutions for enterprises that will extend HoloLens capabilities as a full-fledged collaboration and conferencing tool. The company will demonstrate its Mixed Reality Studio suite to attendees at the Augmented World Expo, which begins later this month in Santa Clara, California.
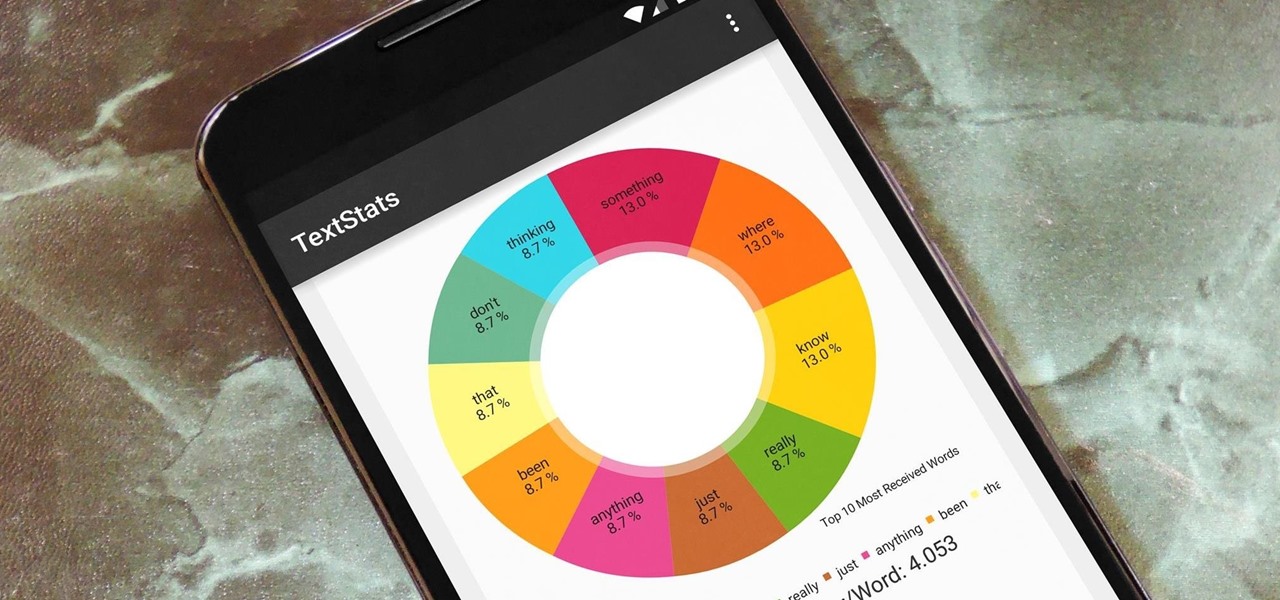
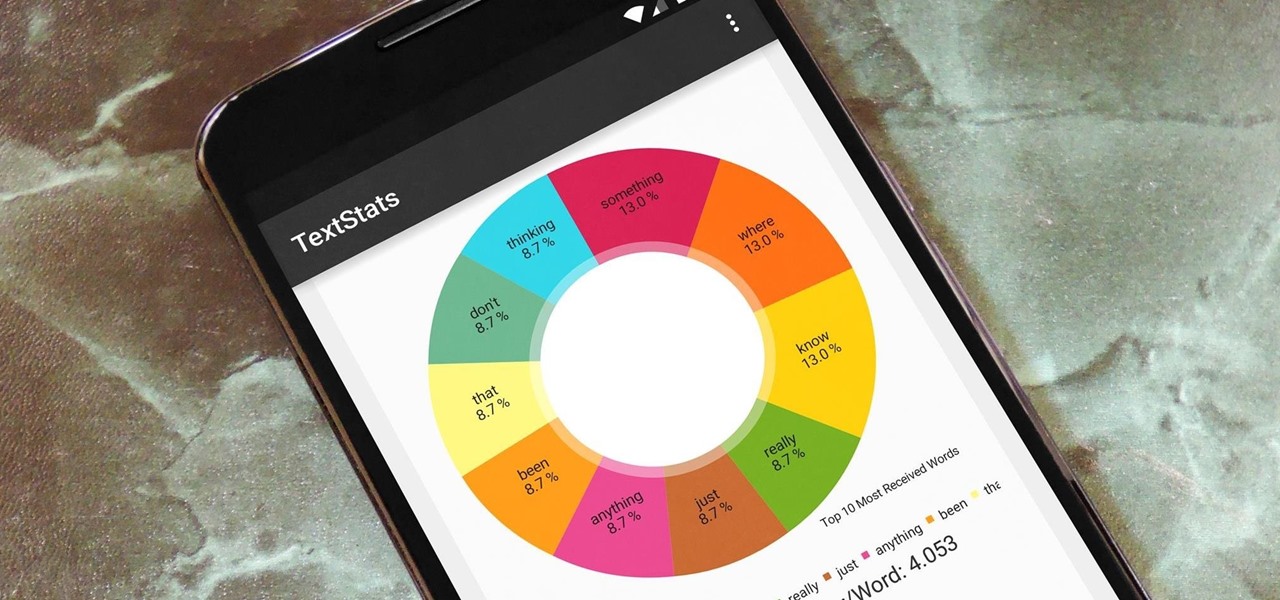
With the advent of text messaging, our communication habits have changed drastically. Social niceties are still there, but we budget our words a little more since they have to be typed out rather than spoken. After all, SMS stands for "Short Message Service," so this is the nature of the beast.
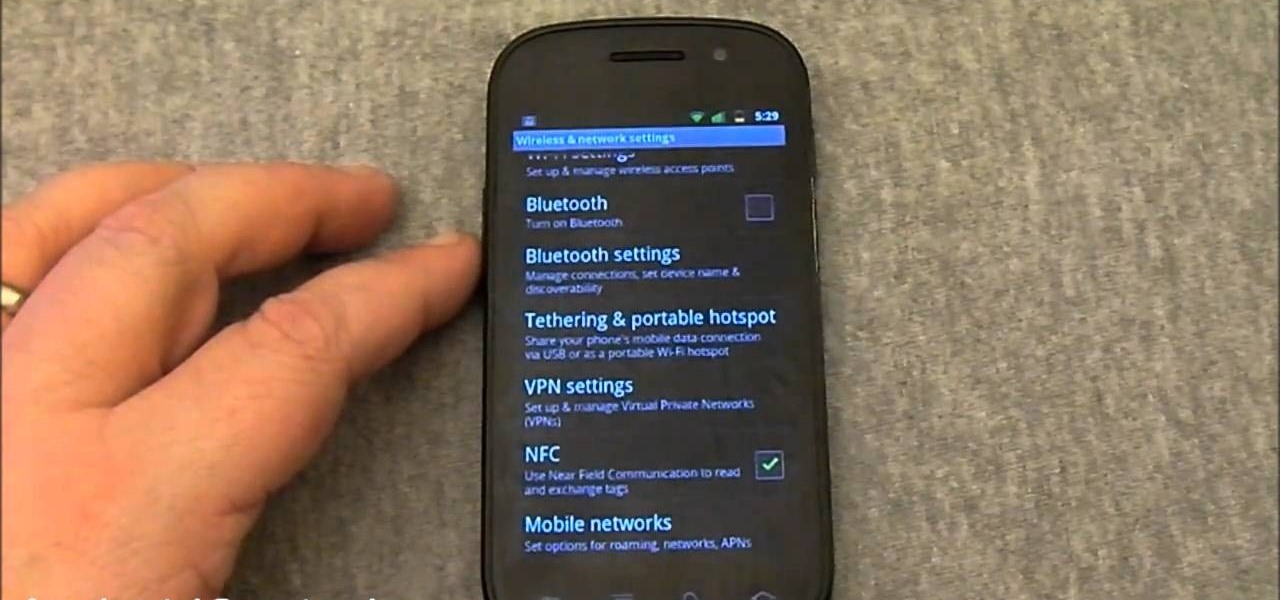
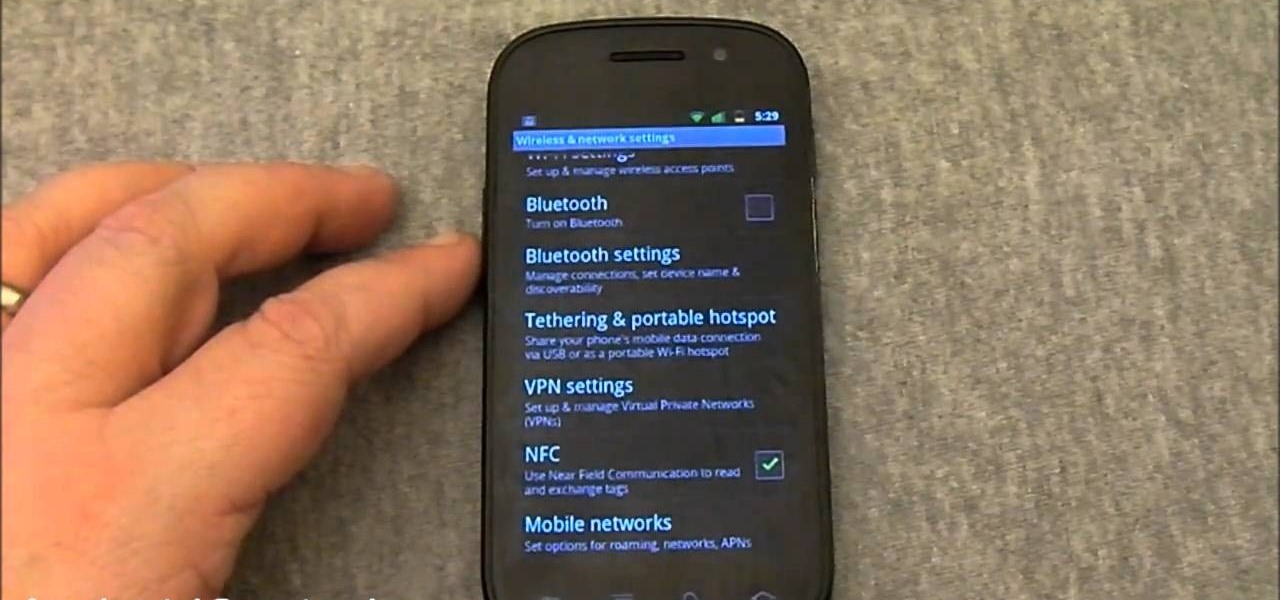
In this clip, we learn how to use the NFC feature on an Android 2.3 (Gingerbread)-equipped Google Nexus S smartphone. For the details, and to get started learning about NFC for yourself, watch this Android owner's guide!

In this clip, you'll learn how to make a call to a web service when working in Silverlight. Whether you're new to Microsoft's popular web application framework or a seasoned web developer merely looking to improve your chops, you're sure to find benefit in this free MS Silverlight programming lesson. For more information, including a complete demonstration and detailed, step-by-step instructions, take a look.

Big Brother is closer to becoming a reality than ever before, especially in the UK. If you're concerned about whether you phone is being tapped, watch this video to learn about steps you can take to find out whether your phone has been bugged or not and make sure your communication remains private.

In this episode of Dogmantics, dog trainer Emily Larlham goes over how to stop a puppy from mouthing and biting and how to interrupt unwanted behavior from your unruly puppy.

Herbert Midgley, the Internet Legend, shows you how to text message to an email address! Need to email someone back, but don't have internet or email on your phone? This is a clever way to send emails to people using sms text messaging. Communication has never been easier.

How to listen effectively by Jeffrey Berman, professor of communications at Salem State College. Professor Berman explores all elements of listening to enhance interpersonal skills for managers. Don't confuse hearing with listening.

To prevent accidents, it's important to indicate to other riders what you're doing. This how-to video covers good cycling communication. These skills are especially important while riding in groups, when visibility is low. Watch this video cycling tutorial and learn how to signal on a bike.

Wally from the East Coast Trans-communication Organization explains a little about collecting EVPs. EVPs, or electronic voice phenomena, are supernatural sounds that can't be heard by the human ear, but can be recorded by a tape recorder and then played back to hear any messages from the beyond. Watch this video paranormal tutorial and learn how to document EVP electronic voice phenomena with the help of a tape recorder.

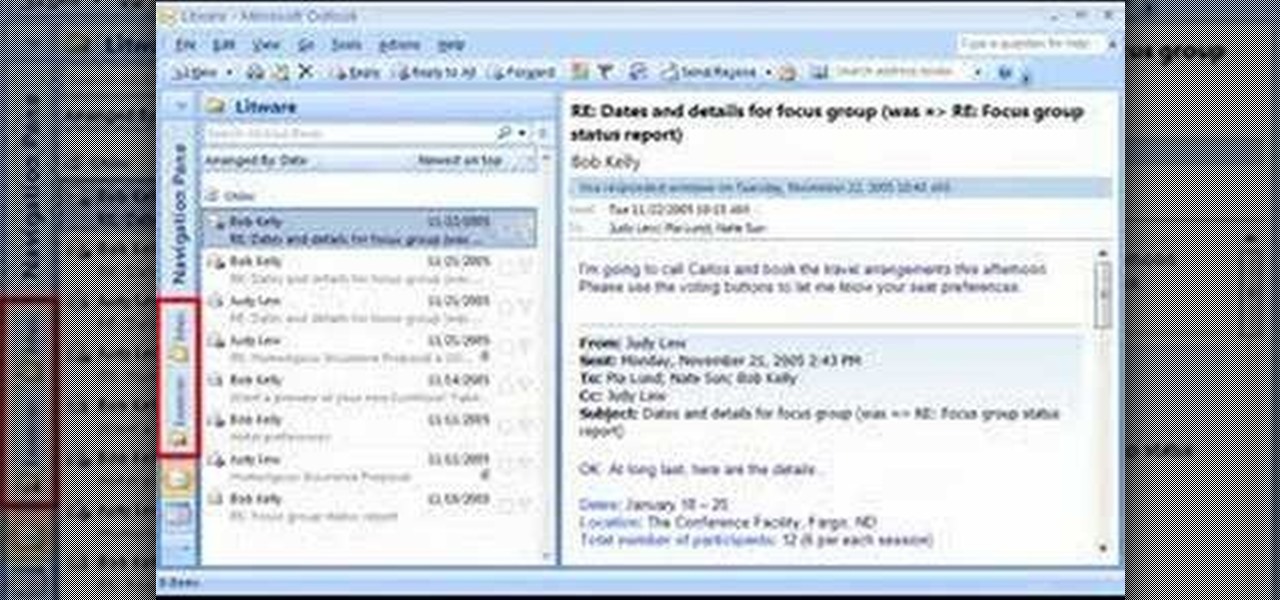
Are you using the Microsoft Office Outlook 2007 Navigation Pane as your communications launching pad — where you can get to your most important folders and views with just a click or two? This tutorial shows you how to change the size of the pane to free up more space, customize the buttons and icons so you see what you want first, and arrange the folders for your convenience. You'll also see how easily you can change the organization whenever you want.

Glue your eyes to the screen, because you will see how to make your very own battery pack for your own two-way handheld radio. If you have an iCom, and need to a battery pack, well then, listen up. With a handy holster for your battery, you'll have never-ending power for your two-way radio communications.

This video teaches a combat medic how to send radio messages using AN/PRC-77.

As many as 6 in every 1,000 children have at least one Autism Spectrum Disorder. People with ASDs tend to have problems with social and communication skills, and have unusual ways of learning and reacting to different sensations. It is important to note that Autism is not just one disorder, but a series of disorders. Learn how to tell if your child is showing symptoms of Autism with this tutorial video.

Augmented reality device maker Vuzix has filed a defamation lawsuit asking for $80 million in punitive damages, money damages, and interest against a short seller who has publicly claimed that the Amazon Alexa functionality of the company's Blade smartglasses is fraudulent.

As the third-largest smartphone manufacturer in the world, Apple devices are a constant target for hackers everywhere. While iOS has seen fewer common vulnerabilities and exploits (CVEs) in recent years, iPhones still aren't hack-proof. Fortunately, you can strengthen your security with the help of a few apps.

Influenced by the growth of augmented and virtual reality technology as well as 3D computer vision, Ericcson Ventures invested in Matterport, whose hardware and software help companies create AR/VR experiences.

Smartphones are still "phones," which means communicating with others is usually a primary use. Ranging from a simple "hi" to a more personal conversation and even sharing passwords, our messages should remain private so that only the intended recipient sees their content. While many apps tout end-to-end encryption, not all apps prioritize security and privacy.

Because it takes two to tango, your dancing Bitmoji World Lens on Snapchat is getting a dance partner.

According to Alex Kipman, HoloLens inventor and futurist at Microsoft, the smartphone is already obsolete. In an interview with Bloomberg, Kipman boldly stated that the HoloLens will eventually replace the smartphone and drive society right into a new augmented normal.

Last week, Apple issued an iOS 7.0.6 update that fixed a serious security vulnerability that could allow hackers to steal passwords, read emails, and get info from other SSL-encrypted communications.

In November 2016, the RCS Universal Profile (Rich Communications Services) was introduced. The technology takes text messaging to the 21st century, emulating many of the features found in IM apps like WhatsApp and iMessage, but working through your phone number like regular SMS or MMS. The only thing is, your carrier needs to support RCS-UP to use the feature. Thankfully, the list is growing.

Applicants looking to attend Magic Leap's first annual L.E.A.P. conference next month in Los Angeles have begun receiving their confirmation invitations, and now we have more detail about some of what will happen at the event.

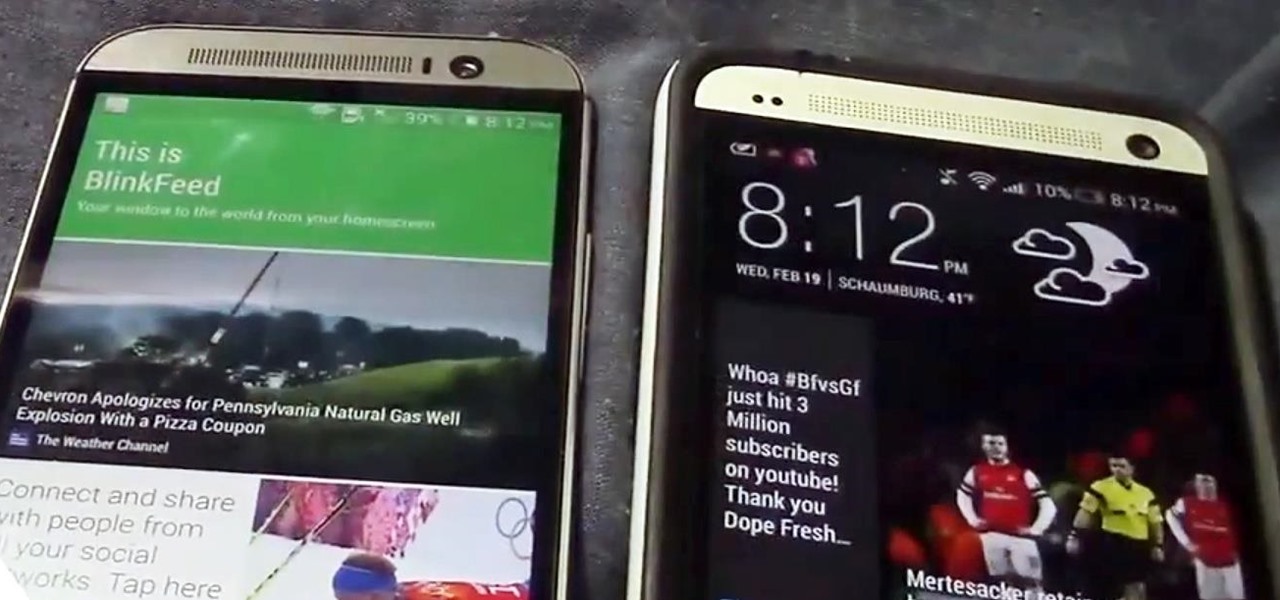
Confirming a lot of what we already knew, now we have a physical walkthrough video on HTC's new flagship, the M8. Or, maybe the "New HTC One", but let's hope that's not the name of the final product. Before we get to the video, here's what we already know:

If you have an iPhone or iPad, but use a Google account for most of your communication, syncing your contacts just got a lot easier. Google recently announced that they added CardDAV support, an open protocol that lets you seamlessly integrate Google Contacts into other services. Google states that "Syncing via CardDAV is only available over SSL for Apple devices on iOS version 5.0 and above." So, if you're running an older iOS version, you'll have to use Google Sync instead.

In 1958, Patrick Flanagan invented the Neurophone, a device patented in 1962 that allows radio signals to be picked up by the human nervous system. The skin is the organ that receives the signal, converting it into a modulated molecular vibration, which the brain interprets into sound. Basically, it gives one the ability to 'hear' through the skin, making it sound like the audio you're hearing is actually in your head. It's kind of like having headphones in your brain. The only problem was th...

Peter John, an accomplished expert in palmistry, demonstrates how to properly understand what it means when your palm reading subject has a long hand and long lines on the palm. He indicates what to look for to indicate intelligence and good communication skills in your subject.

Cellular telephones? So 20th century! With this techy tutorial, you'll learn how to install Skype on your laptop and use it to make phone calls to your friends over the Internet – all without long distance rates! For more information, including step-by-step instructions on how to install the Skype VOIP (Voice Over IP) client on your own computer, watch this free video how-to!

In this video,examine the differences between wolves and the dog as it relates to human-to-canine communication.

Need help with Satellite Uplinks in Battlefield: Bad Company 2 on the Xbox 360? Jack and Geoff from Achievement Hunter give you this two-part video guide on finding all 24 M-Com Stations. In the first video, see the locations of the first 12 M-COM Stations that you must explode for great glory! Part two of this tutorial reveals the last 12 locations, along with the location of the Holy Grail. They also finally break that barrier and hug each other. And they also pick up the Complete Blackout ...

In a LinkedIn post published on Tuesday, Microsoft's leading advocate for the HoloLens made a prediction that the mixing of immersive technologies will define augmented reality in 2018.

Social engineering is a pretty important item in a hacker's toolkit. In Mr robot there was a time, we saw Elliot using social engineering to gain access to his therapist's boyfriend's email and bank accounts by calling him and pretending to be someone from his bank, then Elliot asked him for some info that were really useful to gain access to his account, the target believed to be someone from the bank and gave him the info Elliot was looking for. But How Is It in the Real World?

Radio communication is one of the oldest and most effective means of communication via technology, so it's no wonder it's still a popular way to send and receiver signals, especially on the water. Having a Marine radio can be critical when operating a boat on any type of water. There are many uses for a Marine radio, but the most important is to send a distress signal — here’s how to do it.

If you're feeling unappreciated, underwhelmed, or just plain trapped, taking some time off may help.

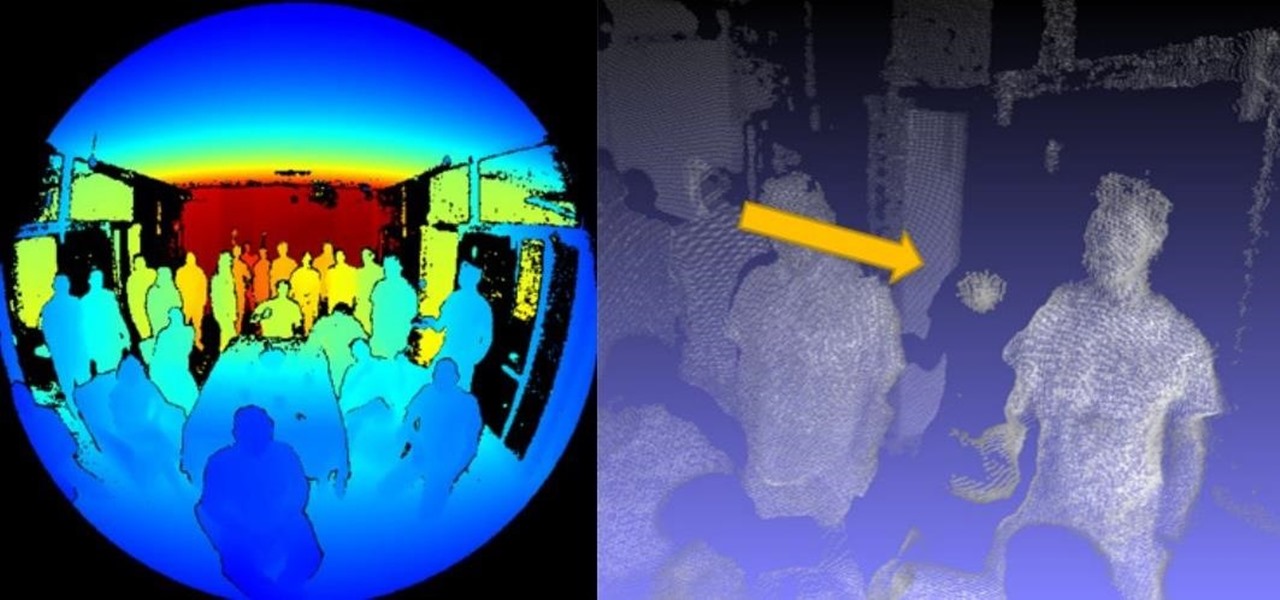
Images captured by Microsoft's next generation Kinect depth-sensing camera that will facilitate augmented reality experiences in the next version of the HoloLens and give computer vision to untold multitudes of connected devices in enterprise facilities, have made their way into the wild.

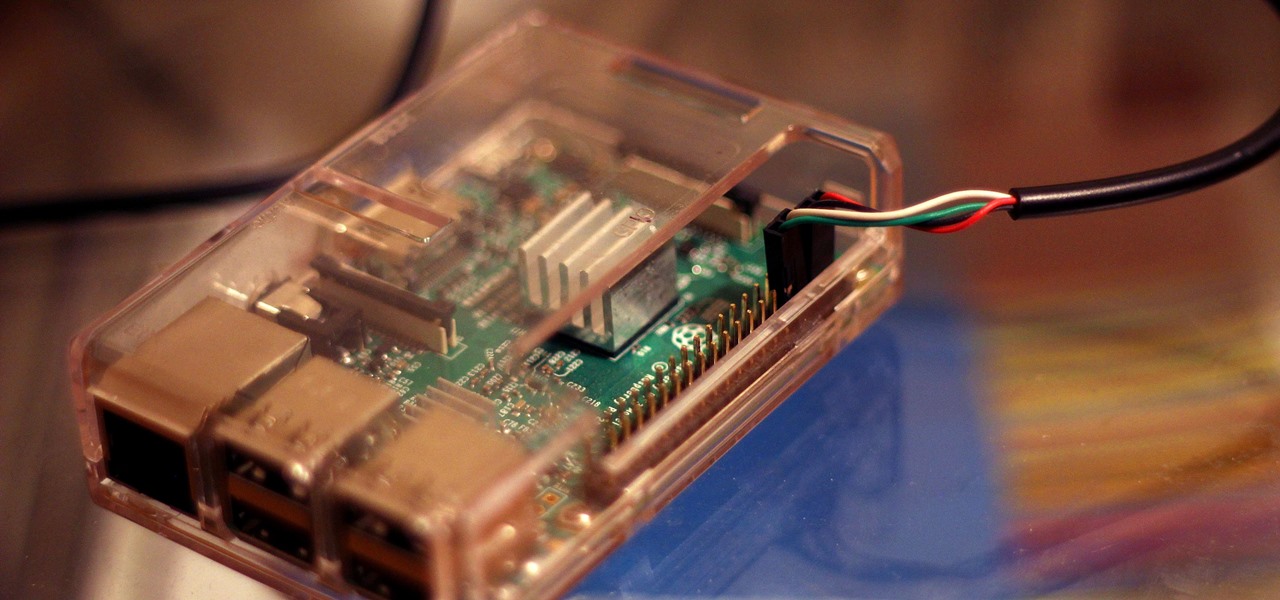
Connecting to your headless Raspberry Pi on the go typically requires a network connection or carrying around bulky peripheral hardware like a screen and keyboard. With the help of an old-school connecting standard, though, you can log into your Pi from any computer using a simple cable. If you don't have a power source, you can also power your Linux distro over the cable at the same time.

Malware attacks on mobile phones are reaching an all-time high and it looks like companies like Samsung are doing all that they can to prevent any unwanted hackers from accessing its sensitive user data.

Welcome back, my nascent hackers! In previous tutorials for my Wi-Fi Hacking series, I have shown you how to crack WEP and WPA2 passwords, break a WPS PIN, and create Evil Twin and Rogue access points. In this continuation of the series, let's look at slightly different approach to attacking wireless.