The hands are one of the more overworked parts of the body. Watch this video to learn massage techniques that can be used to relieve aches, pains and knots in these regions while the client is relaxing on a chair. A word of advice though, use lotion instead of oil because most clients go back to work after a massage and you do not want to leave their hands greasy.

Austin Chau does a short tutorial about how to use the JavaScript Client Library with the Google Calendar Data API.

Compromised uTorrent clients can be abused to download a malicious torrent file. The malicious file is designed to embed a persistent backdoor and execute when Windows 10 reboots, granting the attacker remote access to the operating system at will.

It turns out that the new Galaxy Samsung S8 Active (codenamed Cruiser) will be headed for AT&T in the US later this year, just like previous Active models. SamMobile revealed that the device would be exclusive to the network with a model number SM-G892A.
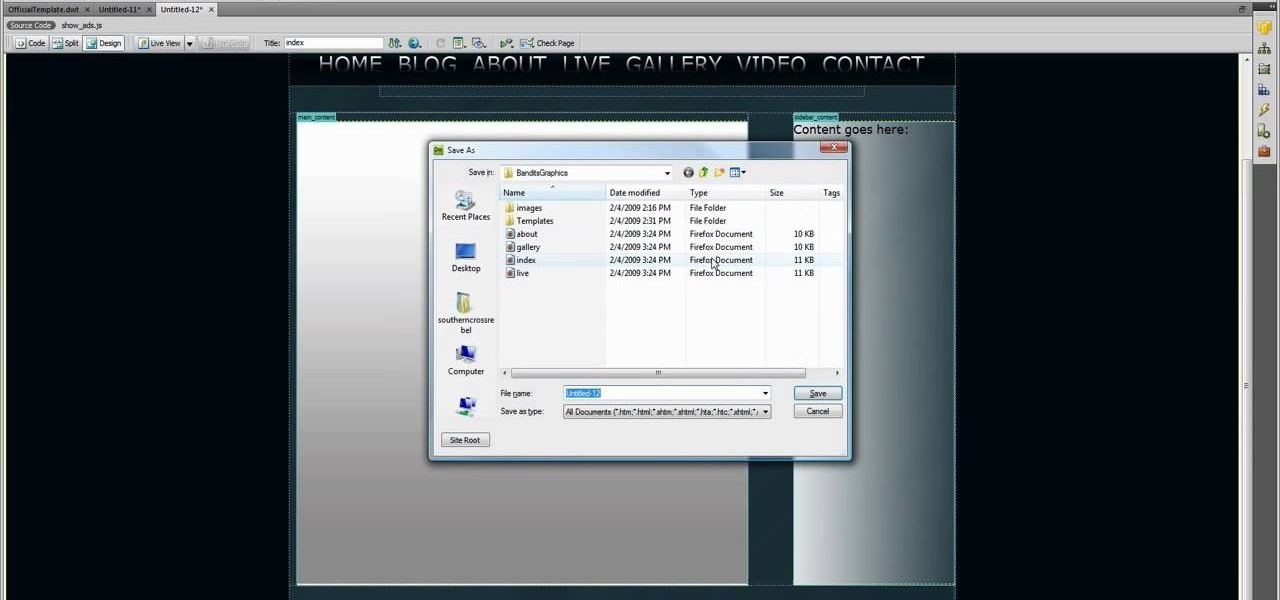
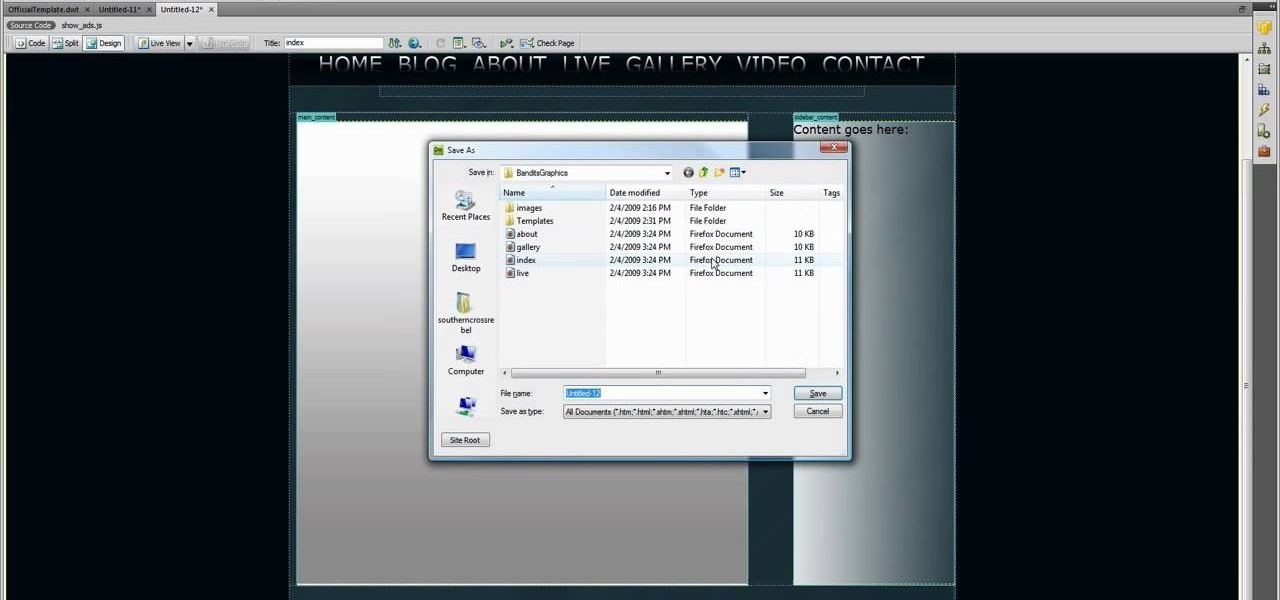
Down, down, down! Yep, what you want is lower on the page and you want to get there faster. SO, why not scroll baby scroll! Ever wanted your website to have a scroll bar? Well, now you can by watch the following video. This how-to will show you how to use Dreamweaver to insert a scroll bar to allow for easy navigation for your or your client's website. It's not too hard, so follow the bouncing ball and learn what to do.

You should encrypt everything. These are what you need: BackTrack 4,0, modify IP tables, Python and ARPspoofing. Program the PC to flip to forwarding mode. Adjust the programming in the IP tables. You are convincing the host and the client that the man (PC) in the middle is the host and capture passwords, user names and other information from unsuspecting clients. This program strips the "S" from "https" which make your computer vulnerable to hackers. You need to observe the address bar and m...

With rumors of the Active and Prime versions on the immensely popular Galaxy S5 circling the web for the past few weeks, today, we've got some clear proof of the upcoming Active variant.

Welcome back, my hacker novitiates! Many of you have probably heard of a man-in-the-middle attack and wondered how difficult an attack like that would be. For those of you who've never heard of one, it's simply where we, the hacker, place ourselves between the victim and the server and send and receive all the communication between the two.

This video tutorial from iDeviceTutz shows how to change the SSH root password for iPhone or iPod.When iPhone or iPod is jailbroken it sets its password to default - alpine.Thus your device becomes vulnerable from a network attack that could steal your information or identity. So you need to change your password as soon as possible when your device is jailbroken.For this you'll need Mobile Terminal program on your device and SSH client (Cyberduck or WinSCP) on your computer.First download and...
Hello, I'm a new guy around here and since I'm not seeing much tutorials in C i thought of contributing with something relatively simple. This will be a short series.

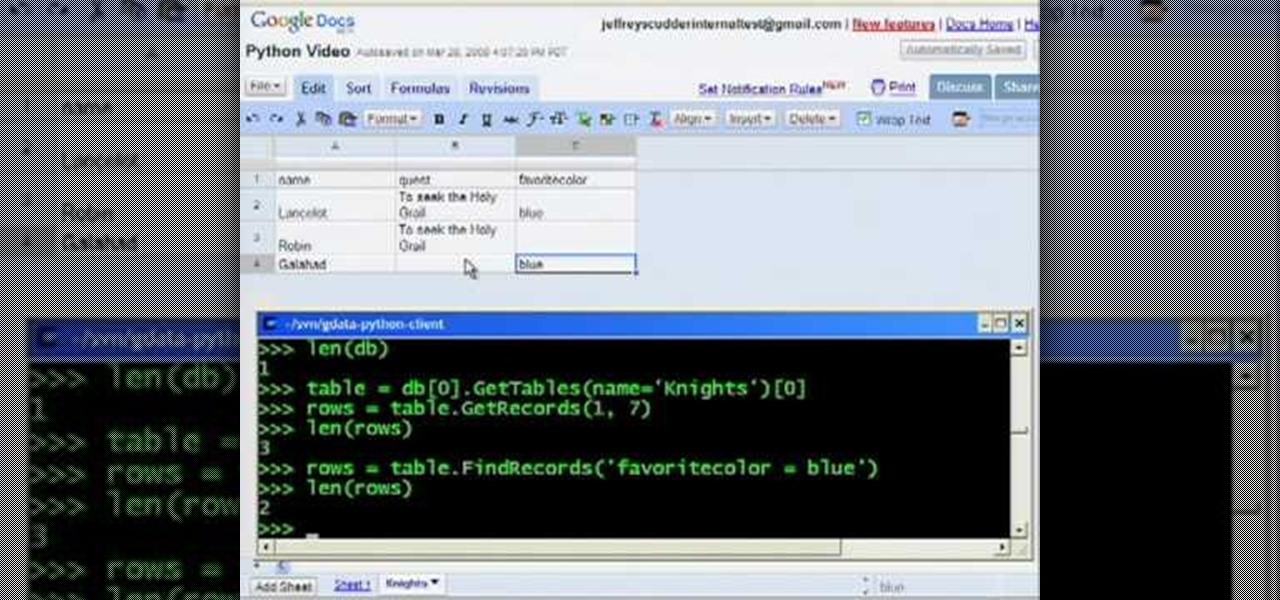
OK, In my last Tutorial we made a Server for sending Instructions to a Client. This time we will build the Client. Fire up your favourite Python environment and get the Code here.

Welcome back, my hacker apprentices! I recently began a new series on digital forensics to show aspiring hackers what the forensic investigator can do and see while investigating a cyber attack. This is the second installment in that series and will focus upon network forensics. In other words, what can a network forensic investigator learn about the attacker during an investigation and how.

This video tutorial from iTouchMaster2 shows how to SSH to iPod or iPod Touch using FileZilla application.

Want to surpass your friends and crush your enemies in the online browser game DarkOrbit? This tutorial shows you how to download and install a variation of the basic DarkOrbit client that also gives you access to cheat codes and other tricks.

In this clip, you'll learn how to get navigate and use the basic features and functions of the Symantec Altiris Client Management Suite. It's easy! So easy, in fact, that this helpful how-to can present a complete overview of the app in just over three minutes. For more information, including detailed, step-by-step instructions, take a look.

This clip outlines a number of simple Reformer-based Pilates exercises to improve a person's gait. Whether you're toying with the idea of opening up your own rehabilitative Pilates studio or merely need some help tackling a certain pedagogical or administrative problem, you're certain to be well served by this free video tutorial from the folks at Balanced Body Pilates. For more (and more comprehensive) information, take a look.

Sending email with the Evolution client in Ubuntu Linux is much the same as with any other email program. In addition to offering step-by-step instructions for the setup and use of Evolution, this Ubuntu tutorial also will teach you how to access your address book when writing an email. For a detailed look at the Evolution email client, take a look!

Each client is different so it is important for a massage therapist to explain the process and adjust the chair before starting a chair massage. Watch this video by Massagenerd to learn how to set-up the chair to give your client a very comfortable and relaxing massage.

How to Use Your Mac as a Server: Turn your Mac Mini into a server! Yes, that's right, with a little know-how and a little spunk, you can turn an inexpensive Mac Mini computer into a server to provide services over you network. You won't even need the Mac OS X Server, just the Mac OS X Client, so there is no extra software to buy, just the Mac Mini and it's operating system.

Not every client or coworker likes to mine through a spreadsheet to find all the important data. So, with Excel 2008 for Mac, you can easily share that data without sending the entire Excel spreadsheet. To do this, all you need to do is to use the "copy as picture" option. The Microsoft Office for Mac team shows you just how to insert a spreadsheet snippet in this how-to video.

With clients like Hilary Duff, Penelope Cruz, and Sarah Michele Geller walking the red carpet, Rachel Goodwin is in demand. We were lucky to hang with Rachel for the day, we begged her to share the secret to her signature smoky eye. Rachel generously gave us a very detailed tutorial to create the look. You won’t be disappointed.

Let's face it, most of us do most of our shopping on Amazon these days. So why should Black Friday shopping be any different? The online retail giant always cooks up some great deals on high-demand items, like headphones. If you're looking to save some dollars on a new pair of Beats, Skullcandy, or Bose, you're going to want to check out Amazon.

If you're on the hunt for a profitable side-gig, or even a completely new way to to make money, you'll want to take a look at Upwork, a leading freelancing platform that connects skilled freelancers with clients from all over the world.

Welcome back, my amateur hackers! As many of you know, Null Byte will soon be re-establishing its IRC channel. In preparation of that event, I want to show how to set up a secure IRC client with OTR, or Off the Record.

Welcome back, my greenhorn hackers! In previous Wi-Fi hacking tutorials, I have shown you ways to create an Evil Twin, to DoS a wireless AP, and to crack WEP and WPA2 passwords, but in this tutorial, I will show you something a little bit different.

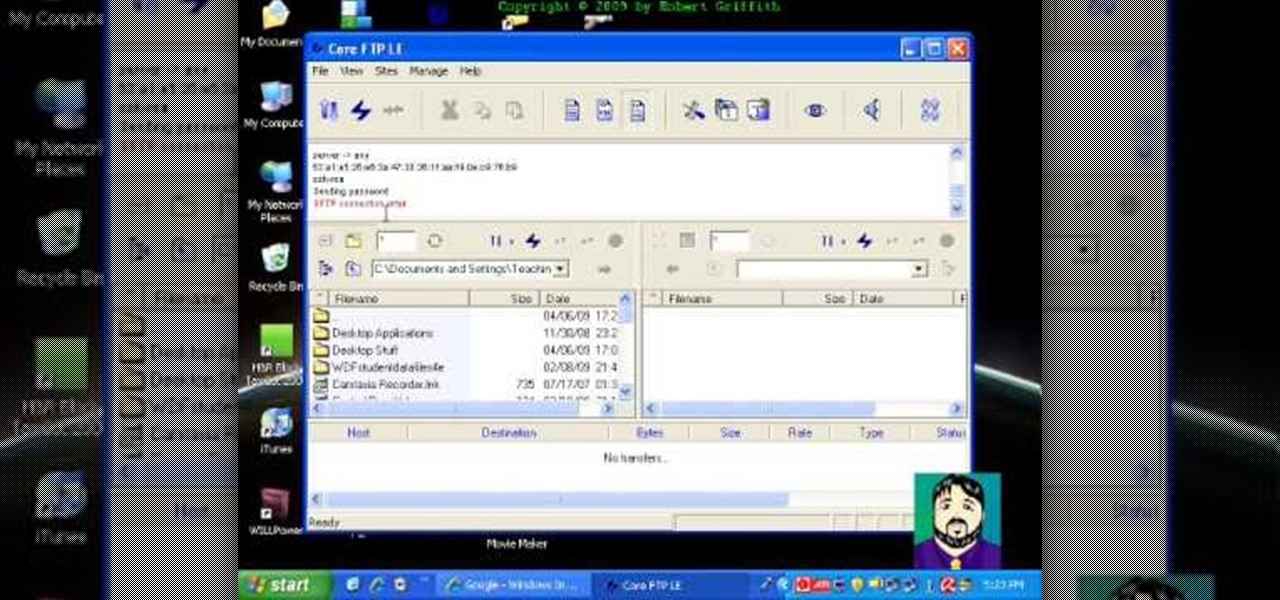
Select an FTP client that allows you to connect to the webserver. Download a free Core FTP Le software. Install the program. Use the site manager to name the internet site. Create a host/url, a user name, password and a connection. Connect to the web server. Create an index file to make files viewable. Open the Core FTP LE software. Drag files from the desktop (left side of the dialog box) to the internet server (right side of the dialog box.)

This video shows you how to use Window Defender on your computer. Go to the start button on the screen and click it. Next, select the control panel. At this point you can type in the word ‘Defender’ or find the icon in the control panel. Once the Windows Defender page comes up you should be able to see whether or not the program is active. If it isn’t active then simply activate it. This program should be run because it helps protect you against spyware and other unwanted activity on your com...

This video shows you how to set up an active speaker system with a built-in amp. Move the gain up and have it halfway up on the mixer. The actual volume control should be set to 0 prior to moving the gain up and down. Mess around with the gain, and slowly bring the gain up until you are slowly tapping into the ampere. You can mess with the gain until it sounds right. This will increase the bass on our mixer.

Apple unveiled the latest generation of its flagship earbuds, AirPods Pro, on Monday, Oct. 28. Aside from the increased price tag, new in-ear design, and wider charging case, the biggest change by far is in Active Noise Cancellation. Finally, we can listen to AirPods on a plane, walking by a busy road, anywhere with a lot of noise pollution. But how does it work?

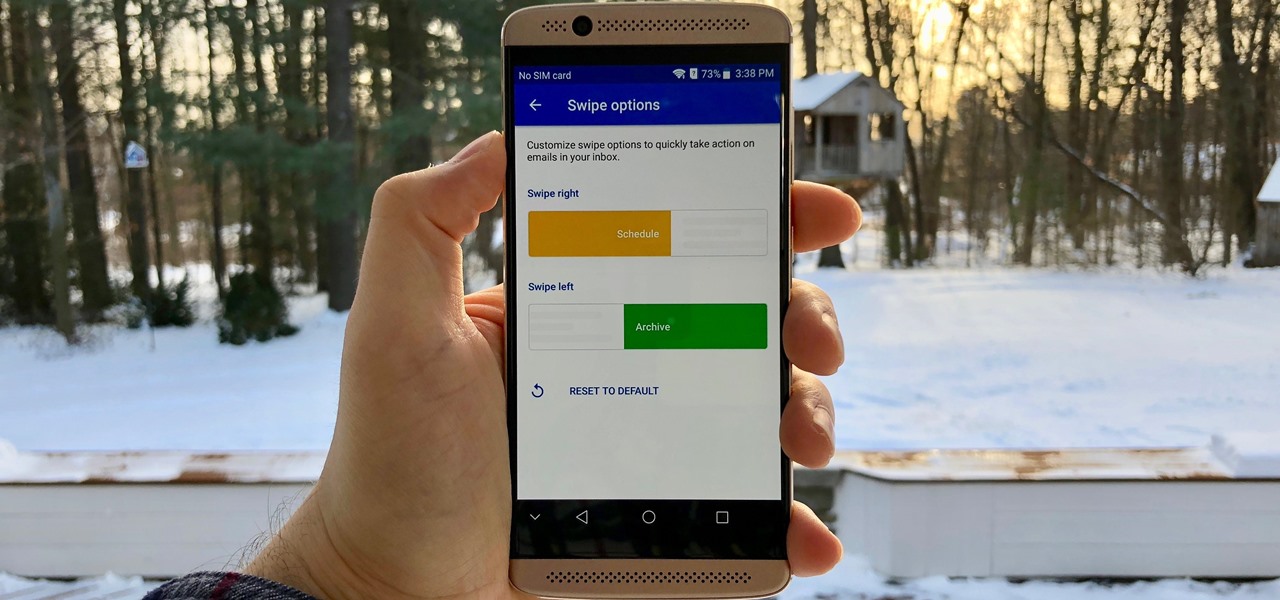
Swipe actions are an integral multitasking feature of any good email client, and Outlook is no exception. The application allows for two swipe actions at a time, but offers seven total options for those actions. We'll show you how to choose which actions go with which swipes to best tailor the app to your needs.

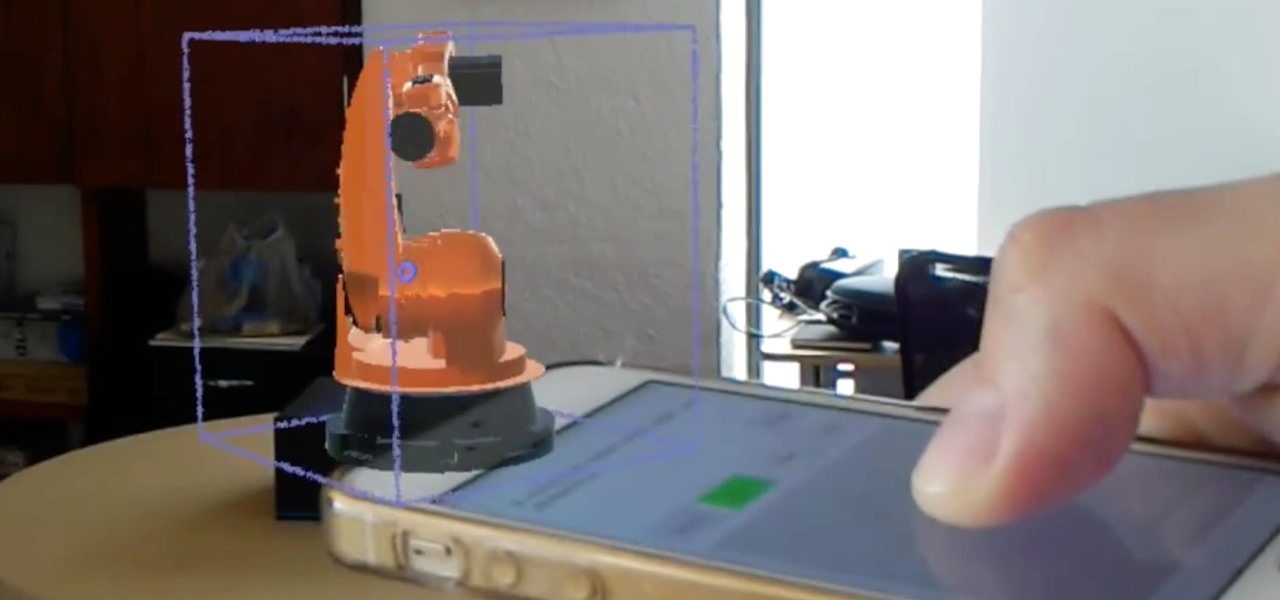
We've highlighted the projects of Wavelength Studios a few times over recent months for their work in the augmented and mixed reality space. Since receiving their HoloLens headsets, they've been hard at work on both development community projects as well as efforts for clients. This brings us to their latest work—a way to control holograms on the HoloLens with our pocket-based modern miracles, also know as smartphones.

Recently, I've been learning Ruby as a second scripting language. But one topic I never covered with the many lessons online were sockets. So I did some research and came up with a very simple client/server connection that sends a string over the socket.

If you've been watching the latest USA TV Series Mr Robot, you will have seen the Raspberry Pi used by Fsoeciety to control the HVAC system. OTW covers this very well here with his take on setup they may of used.

In previous posts here, I have pointed out that hackers are in high demand around the world and in nearly every industry. Every military and espionage unit of every country is trying to hire high-quality, experienced hackers as fast as they can to hack their adversaries' computer systems in order to gain a strategic advantage and to spy.

Welcome back, my budding hackers! In my continuing effort to build your basic Linux skills for hacking, I want to show you how to build a secure "tunnel" to MySQL.

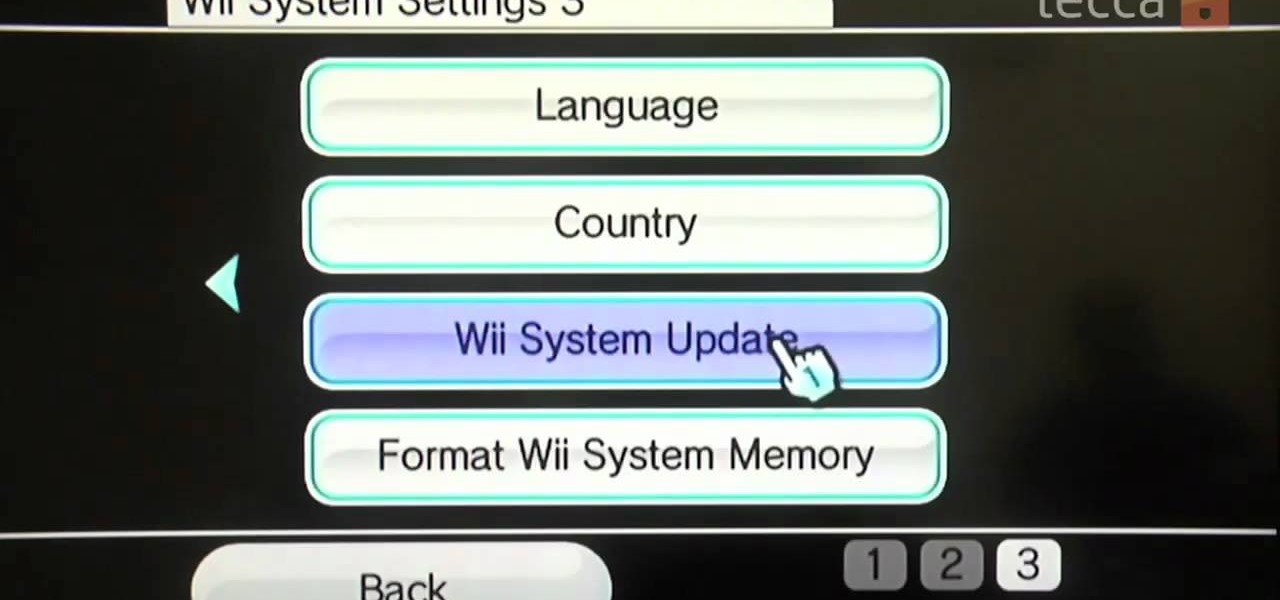
Using the Wii Options menu, it is possible to upgrade your Wii software to the latest version released from Nintendo for the gaming console. You will need to have an active internet connection to download the update first, so make sure that the Wii is connected to your home network. Be sure to check for upgrades every so often so that you have the latest features!

If you want to instantly resize your active window so that it fills any extra window space on your screen, try the free utility WinMaximumize featured in this Tekzilla segment. Hit the default hotkey (Ctrl+F1) or remap it to whatever keybind you want.

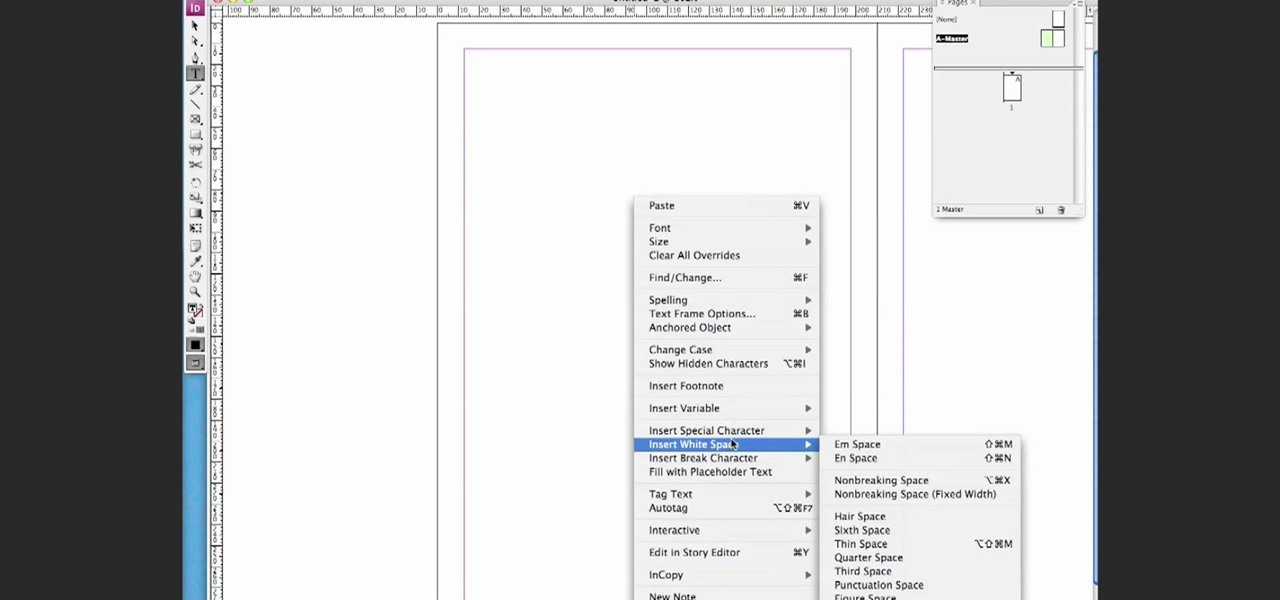
This video is a simple guide about adding automatic page numbering to your document in Adobe's InDesign. It can be a tricky task, but there's no need to fear, this how-to will get you up and numbering in no time. Whether you're making your own document or presentation, or you're working for a huge client and it's got to be right - learn how to set up auto pagination and rest easy, knowing your 1 precedes your 2 and your three then comes next.

Are you an active or aspiring scientist? In this free educational video from National High Magnetic Field Laboratory, learn how to make a model of a comet, and why models are important to scientists. Get started on a scientific road to discovery with help from this excellent video on how to make a model of a space comet.

Watch Jeffrey Scudder demonstrate his GData Python Client Library extension that makes it easy to use Google Spreadsheets as a database in the information cloud.