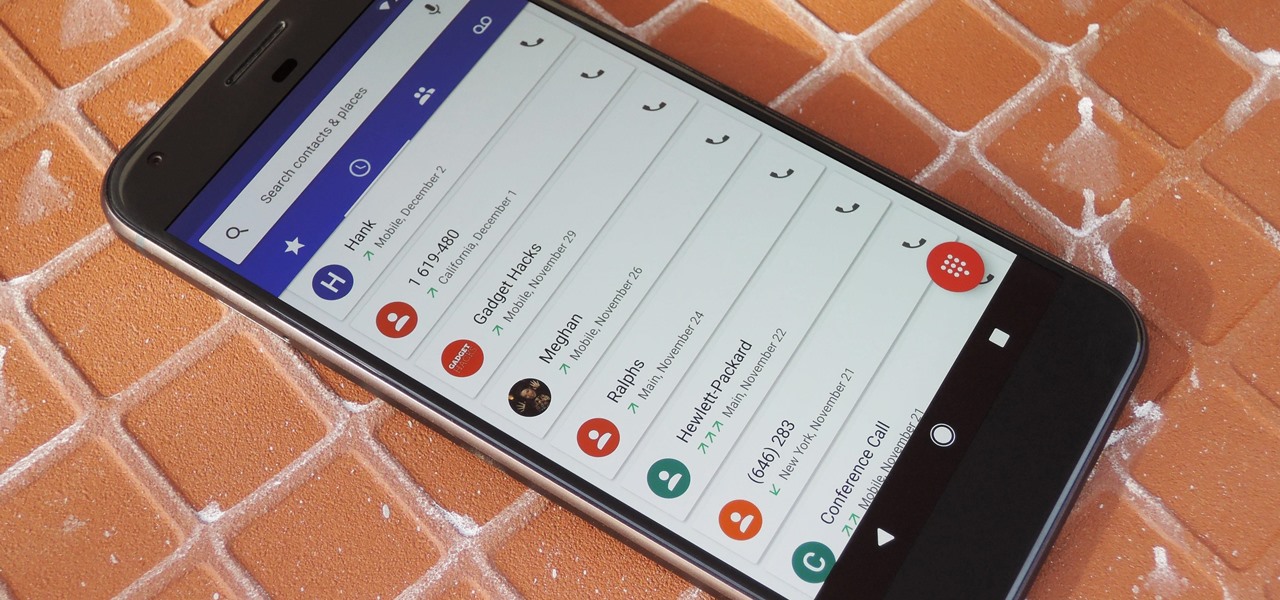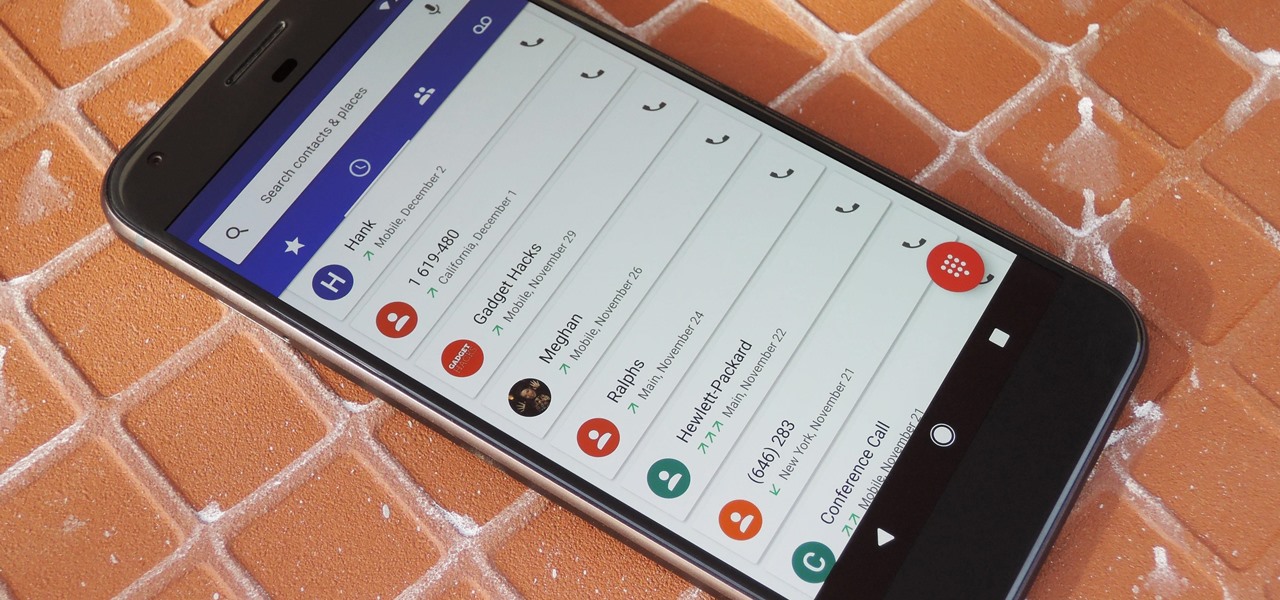
By default, Android limits your call history to the last 500 incoming, outgoing, or missed calls. When you reach this limit, older entries get trimmed off the bottom of the list and deleted forever. This isn't an issue with storage space, because even the biggest call logs only occupy mere kilobytes, so it's really just an artificial limit.

Welcome back, my aspiring hackers! Those of you who use Windows in a LAN environment understand that Windows machines can share directories, files, printers, etc. using "shares." This protocol dates back to the 1980s when the then dominant computer firm, IBM, developed a way for computers to communicate over the LAN by just using computer names rather than MAC or IP addresses.

With recent security breaches in the news, there is no better time than the present to make sure you know exactly what's happening on your device.

If you call yourself a hobbyist or a kid at heart, you know that remote-controlled vehicles are more than just fun. If you're a serious R/C man, you'll know all about doing everything to your model truck or car, like fixing wheels, vamping the pinion gears, waterproofing, troubleshooting, electronic diagnostics, setting up, programming and finally... racing. As much as you know about these remote-controlled vehicles, it will never be enough, you'll always be looking for more...

Help yourself win that must-have item with these tips. You Will Need: a computer with internet access, money, & patience. Create an account. Browse the categories to familiarize yourself with the site, especially if you don’t have a specific item in mind. If you know what you want, start searching by using broad terms and synonyms to yield the most results. Add quotes around your search terms or qualifiers, such as a specific color or size, to narrow the field. You can also post on the “Want ...

As a root user, you have a lot of responsibilities to make sure your phone stays secure. Expectedly, some things may slip through the cracks. Remembering to check which apps have been granted root access is extremely important. All it takes is one bad app, so it's good to learn how to avoid that at all cost.

If you've ever seen something called ThinkPoint Antivirus on your computer, you have gotten one ofhte most widespread and infectious fake antivirus malware programs out there. To get it off your PC, follow the instructions below, or watch this video for an alternate method if this one doesn't work.

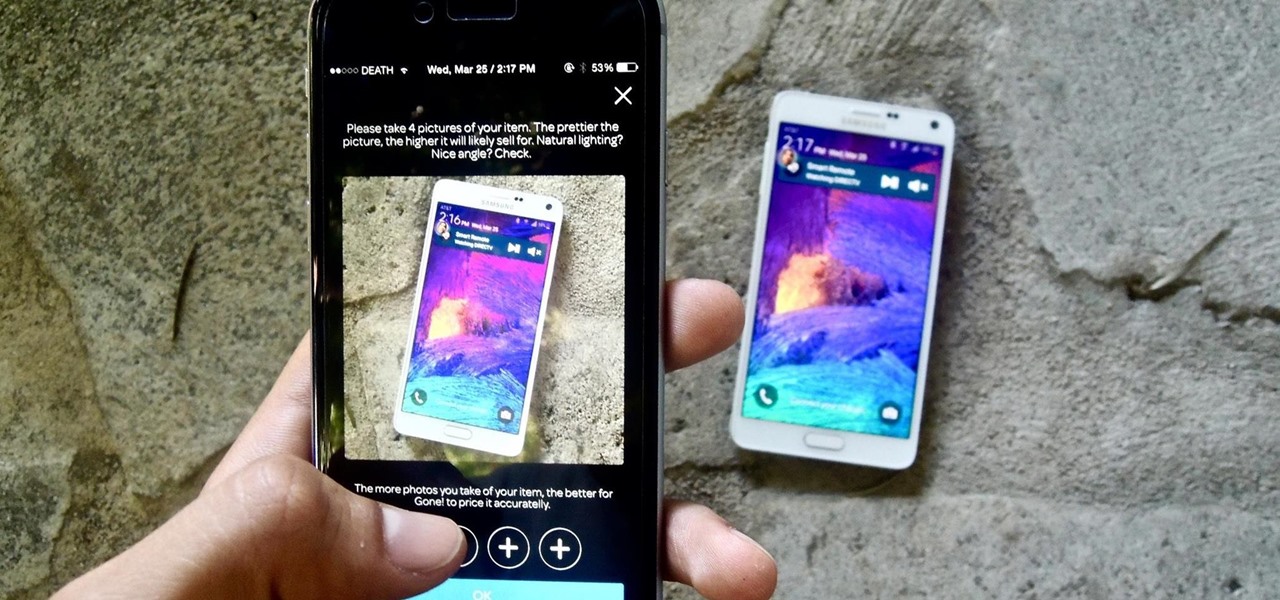
If you want to sell all of the old electronics lying around your home, it takes a lot of work. If you go the eBay route, you have to take tons of pictures, describe it accurately, wait for a week until someone bids on it (or not), then package it, ship it, and wait for feedback. Craigslist is a little bit easier, but usually requires you driving somewhere to meet the buyer in a public place (if you want to play it safe).

Apps that save your passwords have been around for quite a long while. But apps that complete the entire login process automatically? Now that's a different story.

In this video tutorial, viewers learn how to import, manage and export 16:9 footage in Adobe Final Cut Pro. Begin by opening the Log and Capture.Then configure the Logging, Clip Settings and Control Settings. For the Control Settings, set the Device Control as Fire Wire NTSC and the Capture/Input as DV NTSC 48 kHz Anamorphic. Then scroll through the sequence setting of the footage and check Anamorphic. To export, click on File and select Export. Click in Options set the the size to Compressor...

Compound butter is just flavoured butter. LegourmetTV shows you how to make garlic butter, which is a good companion to fresh bread. One clove of roasted garlic is added to half a cup of unsalted butter to make simple garlic compound butter. You can also add cinnamon and sugar to butter for toast. Alternatively, you can even add any of your favourite herbs to melt down a steak. You can also shape the butter into a log, wrap it up in baking paper and keep it in the refrigerator for storage. Th...

On this video from Bushcraft Machete, he explains the purpose of a scandi edge and how to use it. He uses the machete as a planer, stripping the bark from a log by holding the machete almost flat against the log and tapping the back of the blade with a stick. He explains that a scandi edge is sharpened all the way down to a point and has a very low angle. This type of edge makes the machete useful for carving off thin strips of wood. He has sharpened his machete with a scandi edge near the ha...

In this tutorial, we learn how to delete a Facebook account. First, log onto the internet and log into your Facebook account. Once you are logged in, you will be presented with your home page. Now, click on the account settings on the right hand side and find the button that says you want to cancel your account. Once you have confirmed you want to cancel your account, Facebook will send you an e-mail that asks you to confirm it one last time. After you are done with this, your account will be...

In this video tutorial, viewers learn how to decorate a modern yule log cake. Begin by glazing the cakes with a chocolate glasage. This glaze is made with sugar, coco powder, chocolate and cold syrup. Pour the glazing all over the cake and shake to make sure that it is spread evenly. Make the glazing thin for maximum coverage. Using a knife, pick up the cake and place it on a decorative piece of cardboard or plate. The cake is then decorated with hardened and macaron. This video will benefit ...

This is a short video on how to make a corned beef flavored sausage log. Learn to make a single corned beef log from 80:20 ground chuck. The process excludes the addition of coarse ground venison to the recipe which works to improve the texture. This clip is concentrated on the mixing and cooking process in a residential environment. Stuffing, slicing and packing are touched on lightly using a 9" commercial slicer and residential vacuum sealer. The recipe is available at the end.

Don Schechter demonstrates how to capture your footage from your camera to your computer and log it for easy access later on for Final Cut Pro. Logging clips allows you to organize your footage without having to waste hard drive space.

SSH, or the secure shell, is a way of controlling a computer remotely from a command-line interface. While the information exchanged in the SSH session is encrypted, it's easy to spy on an SSH session if you have access to the computer that's being logged in to. Using a tool called SSHPry, we can spy on and inject commands into the SSH sessions of any other user logged in to on the same machine.

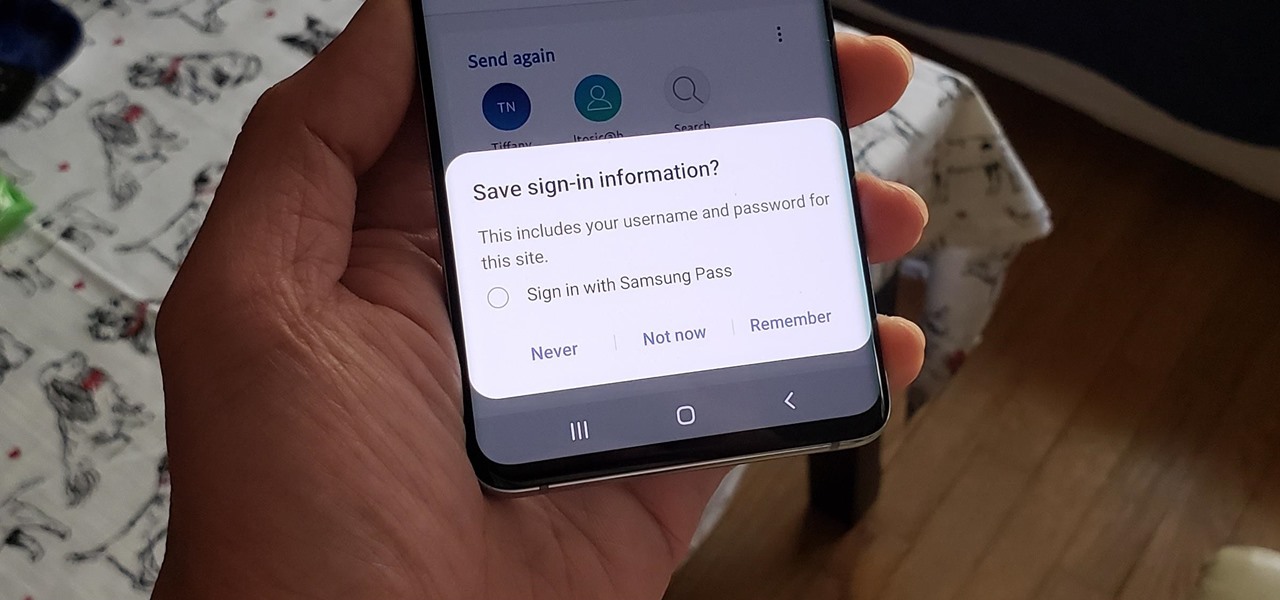
If you use Google Chrome on your computer, you've undoubtedly saved a ton of passwords since the browser always prompts you to. But Samsung uses their own password service on their phones by default, so you'll have to change a setting if you want to use your Chrome passwords to log into apps and sites on your Galaxy.

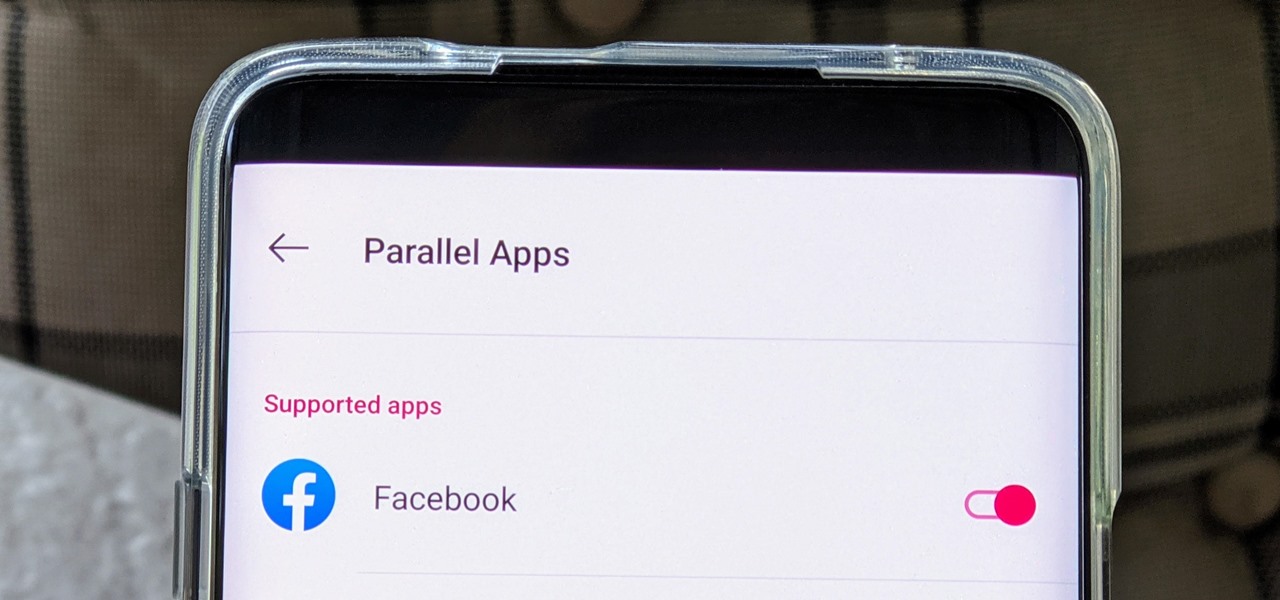
The Facebook app only supports one account being logged in at a time — but what if you need one for work and one for your personal life? That would normally involve logging out and logging in every time you need to switch accounts, but your OnePlus device offers a much better solution.

Increasingly, cutting-edge platforms like blockchain technology and augmented reality are overlapping, forging new digital frontiers that promise to change the way we interact with the virtual and the real world.

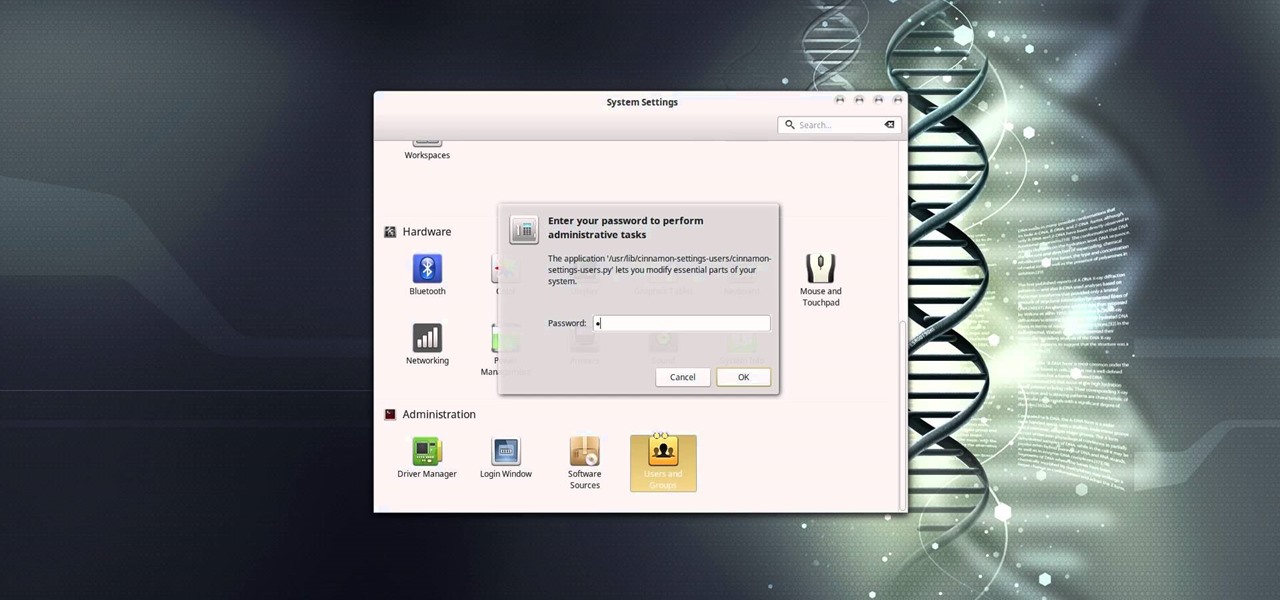
In this video tutorial, I'll show you how to remove the password from the log in screen on Linux Mint 17.2

With all of the different websites we use in our day-to-day lives, keeping track of our numerous login credentials can start to become a hassle. This has created a market for password managers that aim to centralize these account credentials and generally streamline the process of logging into our favorite sites.

It's known that during the Thirty Years' War that took place in Europe between 1618 and 1648, soldiers used Swedish fire torches (also called Canadian candles) for heating, lighting, and cooking meals.

"Dude-man-bro, are you going to Coachella this year?" If I got a dollar for every time I was asked that question, I might just have enough money to actually buy the dang ticket. Concerts have been, for a very long time now, a great way to spend a night or a weekend having fun with friends and listening to some great tunes.

In this video, we learn how to create a free flash website using Wix. First, log online and go to "www.wix.com" and either create a screen name or log into your account. Now, click on "create" and choose a premade template or make one from scratch. Now, change the background to a color you prefer, then add in a frame and different media to your page. You can also add a title to the website by clicking on the "text" section. You can play around with the different effects and additions, making ...

The video shows us how to use a proxy to bypass the Internet Filters. Most of the times in our schools and colleges most of the websites including the social networking ones will be blocked for security reasons and makes us unable to log into those websites. In such cases even the ones from the YouTube, several videos will be blocked. So in this video, we will be shown how to bypass those filters and log into those sites. Firstly go to the website Proxapp and over there you will be asked the ...

Ken Appleby demonstrates how to forward a domain with GoDaddy. First, open your web browser and log onto your GoDaddy account. Click the domain manager option on the left hand side of the home page and log in if necessary. Choose the domain that you would like to forward. Find the forwarding option which is located on the top central portion of the domain manager window. Tick the enable forwarding box. Then, type the address that you would like to forward your domain to in the forward to box....

The video describes a method of doing the twiddle scratch on a DJ turntable. The sound one gets is like a double-click flair, as it’s similar to the double-click flair. In order to do the twiddle scratch, keep your stronger hand (the hand u frequently uses) on the dies while your other hand is on the log. Keep your thumb against the log lightly, and tap back and forth with your two fingers while scratching the disc with your other hand. The whole procedure is given step by step.

Dissolve yeast and 1 1/2 teaspoonful of white sugar in lukewarm water. Mix until bubbly then set aside.

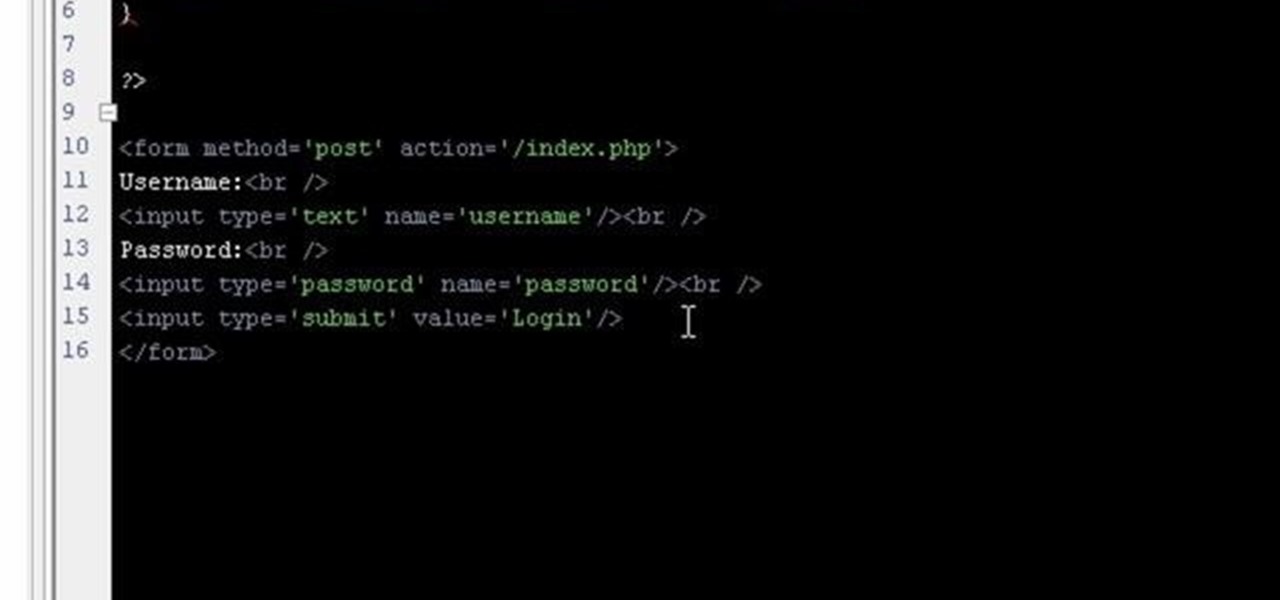
If you're working on a website and want users to use it repeatedly and form a community on it, you should probably give them a way to create an account and log in to your site. This video will show you how to create an AJAX login script using AJAX with jQuery, which will allow your users to do exactly what I described above, making your website much more professional and a much better place for people to stay and click on ads or whatever else you want them to do.

If you've forgotten the password to one or more of the Windows XP accounts on your computer, take heart: This video tutorial will show you how to bypass, and then change, a Windows XP start-up password. For a detailed run through of this simple Windows log-in hack, watch this video how-to.

Much of the excitement around the HoloLens 2 has moved on to many wondering when we'll finally be able to get our hands on what is now the best augmented reality device on the market.

As promised last week, Magic Leap has finally released the long-awaited augmented reality game Dr. Grordbort's Invaders.

French automaker Renault is tapping into the promotional machine for Solo: A Star Wars Movie by deploying an AR experience through Shazam that's triggered via synergistic advertising.

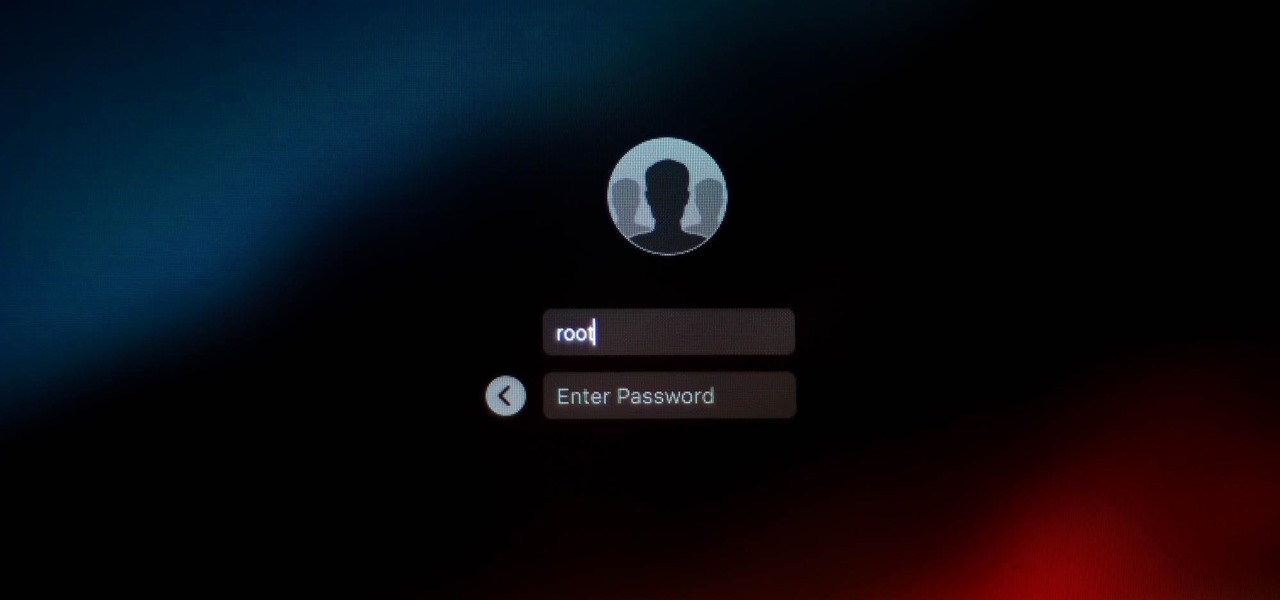
It looks like there is a fatal flaw in the current macOS High Sierra 10.13.1, even straight from the login menu when you first start up the computer. This severe vulnerability lets hackers — or anyone with malicious intentions — do anything they want as root users as long as they have physical access to the computer.

One of the best things I love most about any new gaming console are the apps—I can switch from playing Assassin's Creed III to re-watching the fifth season of Breaking Bad on Netflix without ever getting off the couch. Beat that Atari.

If you've ever logged on to the popular music application Pandora, your password is saved onto that computer in the local storage...for good.

If you're lucky enough to have a large backyard, or perhaps even a plot of land, then you probably have several trees on hand. If for whatever reason one or two of these trees needs to be cut down, don't just dispose of the wood!

In this tutorial, Brian teaches us how to make your wireless network secure. First, go to the start menu, then go to run and type in "cmd", then type in "iconfig /all". Now a new window will pop up and you will look for the default gateway. Find the IP address to log onto the routers you have. Now, type in your IP address into your address bar on your internet browser. You will be asked to log into your account with your password and user name, which you can find at the manufacturers website....

This video tutorial is in the Computers & Programming category which will show you how to set up a Linksys WR54g or WRT54g2 wireless router. First you connect to your Linksys router. Then go to http://192.168.1.1 and type in "admin' as your password in to log in window and click "log in'. then go to the "wireless' tab and enter your wireless network name. In the wireless channel select '11 2.462GHz' and click save. Next go to "wireless security' and type in the wireless network key. This is t...