Believe it or not, there was a time when smartphones weren't the primary tool for taking photos. People actually walked around with bulky film-based cameras on their necks, and some even used cheap disposables. While photography wasn't introduced to the world when smartphones came out, it's definitely more accessible—and everyone is a photographer now.

You can take macro photos on a huge variety of devices, whether you're using a DSLR with expensive lenses or just your iPhone (or any smartphone, for that matter). One common issue, though, is that it can be hard to get the image as crisp as you want because the depth of field is so small.
Android has released a new application called ezNetScan, which is a free app that scans the wireless network you're connected to and gives you a full log of all of the devices connected to that network. This isn't new for smartphone users, let alone Android users. Fing has been around for a while and does practically the same thing that exNetScan does. It gathers information such as the IP and MAC addresses, device vendors, and ISP location. But while Fing is a great program, it does lack a f...

Samsung will be launching the next edition of its Galaxy Note series in less than a month, and we're starting to get some solid information about the upcoming phablet. As previously rumored, Samsung is skipping a number on this year's model, so the new model will be called the Galaxy Note7.

Having problems with your anti-virus software on Windows? Check out this video tutorial to learn how to remove AntiVirus Pro from your computer. AntiVirus Pro is a rogue and fake scanner program that could destroy your Windows computer... see how to remove personal antivirus!

Look at this video tutorial to see how to remove viruses from your computer if you live in Charlotte, or anywhere else in the world. This will help you remove viruses from your computer yourself, without paying mega bucks to get it fixed. You'll see how to get a free virus scanner, for virus removal. This could take up to an hour or two, depending upon the data information on your PC.

Have you ever lost your house or car keys? Kipkay will show you how to make a backup copy of your keys just using a scanner.

Want to make a Rubik's Cube just like Erno Rubik? Of course you do, but before you start making all of the intrinsic mechanisms of the classic Cube, maybe you should start out a little simpler.

Normally, when standing outside your local regional airport, you'd need a special radio or scanner to pick up the transmissions coming from that Air Traffic Control tower. Well, not anymore.

One of the first steps in attacking a web application is enumerating hidden directories and files. Doing so can often yield valuable information that makes it easier to execute a precise attack, leaving less room for errors and wasted time. There are many tools available to do this, but not all of them are created equally. Gobuster, a directory scanner written in Go, is definitely worth exploring.

Having an efficient workflow is an integral part of any craft, but it's especially important when it comes to probing apps for vulnerabilities. While Metasploit is considered the de facto standard when it comes to exploitation, it also contains modules for other activities, such as scanning. Case in point, WMAP, a web application scanner available for use from within the Metasploit framework.

The public leaks of NSA tools and information have led to the release of previously secret zero-day exploits such as EternalBlue, which was used in the notorious WannaCry ransomware attack. Despite multiple patches being released, many users have failed to update their systems, so many devices are still vulnerable to these now-public attacks.

Watch this automotive video tutorial to see how to scan your automobile for diagnostic trouble codes.

As part of the iOS 11 update, Apple added a document scanner function that creates high-quality digital copies of physical documents, but it was only available inside the Notes app. With iOS 13, Apple has built its scanner right into the Files app, enabling you to quickly create PDFs with your iPhone and do more with them.

One of the first steps in reconnaissance is determining the open ports on a system. Nmap is widely considered the undisputed king of port scanning, but certain situations call for different tools. Metasploit makes it easy to conduct port scanning from directly inside the framework, and we'll show you three types of port scans: TCP, SYN, and XMAS.

Google just rolled out a revolutionary feature to its Pixel devices — Google Lens. Previously, Lens had only been available in the Photos app, but now, whenever you want to learn about something in the real world, you can just bring up Google Assistant, turn on the camera, then let Google's famous AI analyze the scene.

Reports of Samsung's Galaxy Note 8 having an in-display fingerprint scanner have been circulating for the past few days. Fans have been excitedly discussing the potential of the phablet possessing this technology, as it would be the first phone released with these capabilities. Unfortunately, a Samsung official revealed today to Naver — a South-Korean web portal — that Samsung has decided to forgo incorporating the feature into the Galaxy Note 8 due to technical limitations and time constraints.

A great many S8 and S8+ users have undoubtedly spent quite a bit of time figuring out ways to unlock their new Galaxy in as few steps as possible. One of the most endearing features of previous Galaxy models was the ability to unlock the phone by pressing the home button and momentarily leaving your finger there for the sensor to do its job, almost instantaneously opening the device — all without having to pick up the phone.

The Galaxy S8 has finally touched down, and it's an absolutely gorgeous device. Samsung's brand new flagship comes jam-packed with new features — some refined, and some that aren't. Luckily, we've compiled some major features to help you get started as quickly as possible so you can go about the rest of your day and show off your shiny new S8 to friends and coworkers.

Welcome back, my budding hackers! Recently, I showed you how you could exploit the widely disseminated OpenSSL vulnerability that has to become known as "Heartbleed". Although the world has known about this vulnerability for over a month now, it will likely take many more months—or even years—for everyone to close this vulnerability.

In order to make paper cutting art for your home, you will need: paper, pencils, X-acto knife, card stock, scissors, self-healing cutting mat, poster board, adhesive, and a scanner.

Want to make a Rubik's Cube just like Erno Rubik? Of course you do, but before you start making all of the intrinsic mechanisms of the classic Cube, maybe you should start out a little simpler.

Every now and then, an iOS secret surfaces that makes me wonder, "How am I just learning about this?" I remember the first time I found out how to delete numbers in the Calculator app, and when I discovered you could bulk-move apps around the Home screen. Now, there's another tip to add to the list: a hidden iOS app whose icon you quite literally can't find unless you know where to look.

This year's holiday shopping season is shaping up to be fertile ground for augmented reality to show its worth, as both Walmart and Target have crafted immersive experiences designed to engage shoppers in the coming weeks.

As we enter the second half of 2018, rumors for the second season of flagships have started to emerge. On the Android side, this means the latest iterations of the Google Pixel, Galaxy Note, LG V series, and Huawei Mate. Thanks to FunkyHuawei and XDA, we now have some solid rumors regarding the Huawei Mate 20.

Samsung's Note series is directly responsible for some of the biggest innovations in smartphones. As the first "phablet," it sparked the current craze for bigger screens, and the S Pen stylus has been mimicked numerous times. Even the curved display made famous by the Galaxy S6 edge made its debut on the Note 4, so this is the one smartphone line you want to keep track of if you like to stay on the bleeding edge.

Scanning is an awesome, fast way to transport a document into your computer. But, what if you want to edit it once you've scanned it? Most scanner programs will import your document as a read-only PDF or image file. With this tutorial, learn how to use the program ClaroRead on a Mac to scan your document directly into Microsoft Word for editing. This will save you a lot of time and a lot of annoying formatting and copy and pastes!

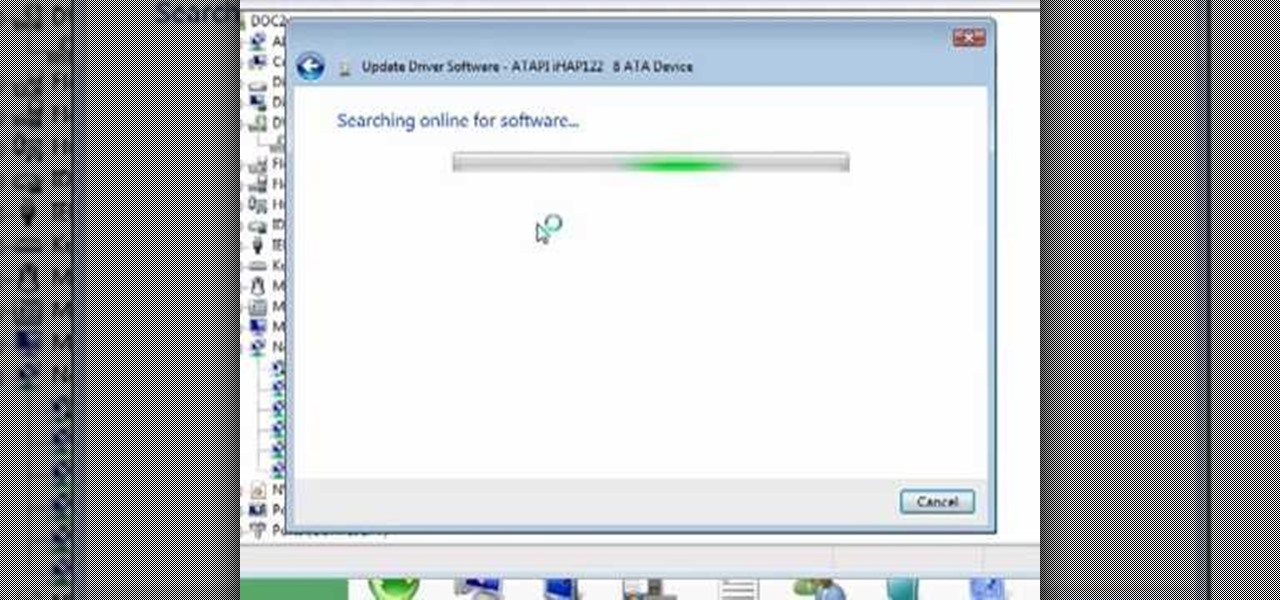
From "Butterscotch" tutorial Michael Callahan walks you through updating your driver for Windows 7 operating system. This will help to improve communication between your printer, scanner, or any other devices digitally connected to your Personal Computer. Simply by going through the "start" menu you can then search and find out if there is new drivers for your devices. After that it will tell you and assist you downloading the new driver. Leaving you with the best driver software for your dev...

Astrum Antivirus Pro is a rogue anti-spyware application and a clone of VirusTrigger and Antivirus Trigger. Astrum Antivirus Pro is often downloaded and installed by a Trojan or through browser security holes. Astrum Antivirus Pro may generate large numbers of popup adverts. Astrum Antivirus Pro will also display notifications of imaginary security risks in its attempts to get the user to purchase the full version. Astrum Antivirus Pro may run a fake system scanner and then display fake syste...

A QR code is a fun and convenient way to link people to a website or app. On iOS, you have a few ways to scan these codes. You can download a QR scanner to get the job done, but Apple has one built into iOS. Or you can add the QR Code Reader tile in Control Center, but that's not even necessary. There's a better way, one that requires basically no effort to pull off.

Websites are often misconfigured in ways that allow an attacker to view directories that are not ordinarily meant to be seen. These directories can contain sensitive information such as private credentials or configuration files that can be used to devise an attack against the server. With a tool called Websploit, hackers can scan targets for these hidden directories without difficulty.

In the world of technology, there's often a trade-off between convenience and security. The Java Remote Method Invocation is a system where that trade-off is all too real. The ability for a program written in Java to communicate with another program remotely can greatly extend the usability of an app, but it can also open up critical vulnerabilities that allow it to be compromised by an attacker.

If your smartphone is ever lost or stolen, it's a terrible experience. If you file a police report, chances are the responding officer will need your device's IMEI or MEID number if you want to stand a chance of getting it back. Same goes for making an insurance claim on a lost or broken phone, so it's definitely important to have this unique identifier handy.

The wait is over. The Samsung Galaxy S6, arguably the best Android phone of this year, has just launched. There was already a lot of hype about this super phone—its looks, its specifications, and its other functions have been under the microscope for quite some time. It will not be a good idea that you take this phone in your hand and use it in the same fashion as you have been using your other phones in the past.

With the gargantuan size of the Samsung Galaxy Note 4, it's no surprise that some of you might have trouble taking advantage of all the features using only one hand. One such feature is the newly-added fingerprint scanner, which allows you to swipe your finger on the Home button to unlock the device, among other things.

The fingerprint sensor on the Samsung Galaxy S5 gets a little flack for its functionality, and that's mainly because the setup instructions ask you to swipe your index finger over the sensor to unlock your device or make mobile payments (and of course, because it was already hacked).

In this tutorial, we learn how to make an iron on transfer for a t-shirt. The materials you will need are: a printer, an iron, hard surface, transfer paper, and t-shirt! To start, find the art that you want to put on your picture and then you will need to transfer it onto the paper for your shirt. Once this is fully transferred with the scanner, load it to your computer. Then, print it out on transfer paper. After this, you will place the paper down on the shirt and iron it for a few minutes....

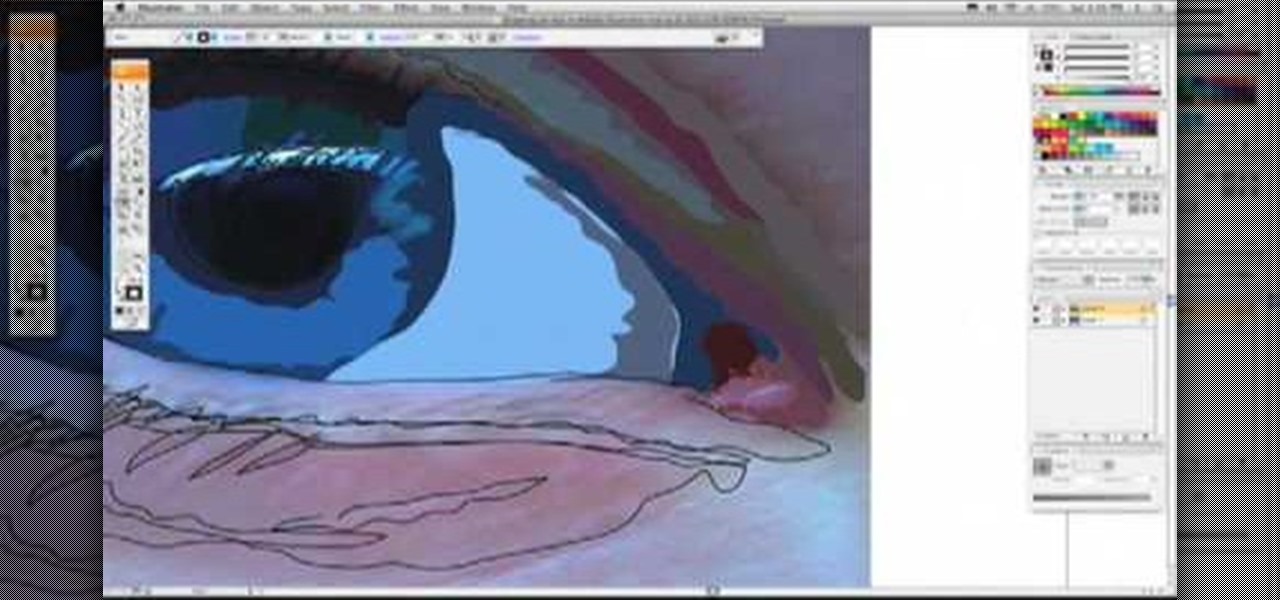
If you love Adobe Illustrator and are looking for an interesting and creative way really to bring the life out of your pictures, this video has an interesting twist. If you remember the movie, "A Scanner Darkly" and the art style that they used, it was quite impressive and unique and called rotoscoping. In this video Karl Gude goes into great lengths showing you his method of tracing the picture and then adding the right colors all the way to the finished product.

In this tutorial, we learn how to scan and edit negatives with SilverFast and Photoshop. First, open up the software and lay your negative in the scanner. Make sure you have selected the correct settings when you go to scan it, and click that it's transparent. Also, you will need to increase the size of it and make sure the lighting is correct. Now, scan the image and load it onto the software. Once it's loaded, you will be able edit it by zooming in and then rotating the image so it's the co...