The right music can spur you to pick up the pace during an intense workout, pep you up before you hit the treadmill or walking path, and even encourage you to lift for just a few extra reps. Although we all have our favorite workout playlists, scientists have discovered what it is, exactly, that makes you workout harder when certain songs begin.

During a contest in 2010 regarding which country Justin Bieber should visit next on his tour, North Korea won by a landslide. Unfortunately, he never went, and that's partly because nobody in the internet-less dictatorship probably voted. Instead, the contest was rigged by 4chan members and a few playful bots that voted for NK hundreds of thousands of times. What this shows is that not only is Justin Bieber an asshole, but that bots can be used as a very powerful tool—not only to cause mischi...
We've all seen the classic tornado-in-a-bottle science experiment, which uses 2 two-liter bottles to create a whirlpool effect. This version requires you to get the tornado started yourself by spinning the bottles, but what if you want to make it fully automated?

When the new iOS 6 came out a few months ago, I was pumped because I finally would get Siri on my iPhone 4. Having the automated voice assistant readily available on my phone would be cool, even if I probably wouldn't use it all that much.
The gold standard in any business is reaching the front page of Google. You need to get your brand in front of audiences. While it can seem daunting, it's not impossible when you master SEO best practices.
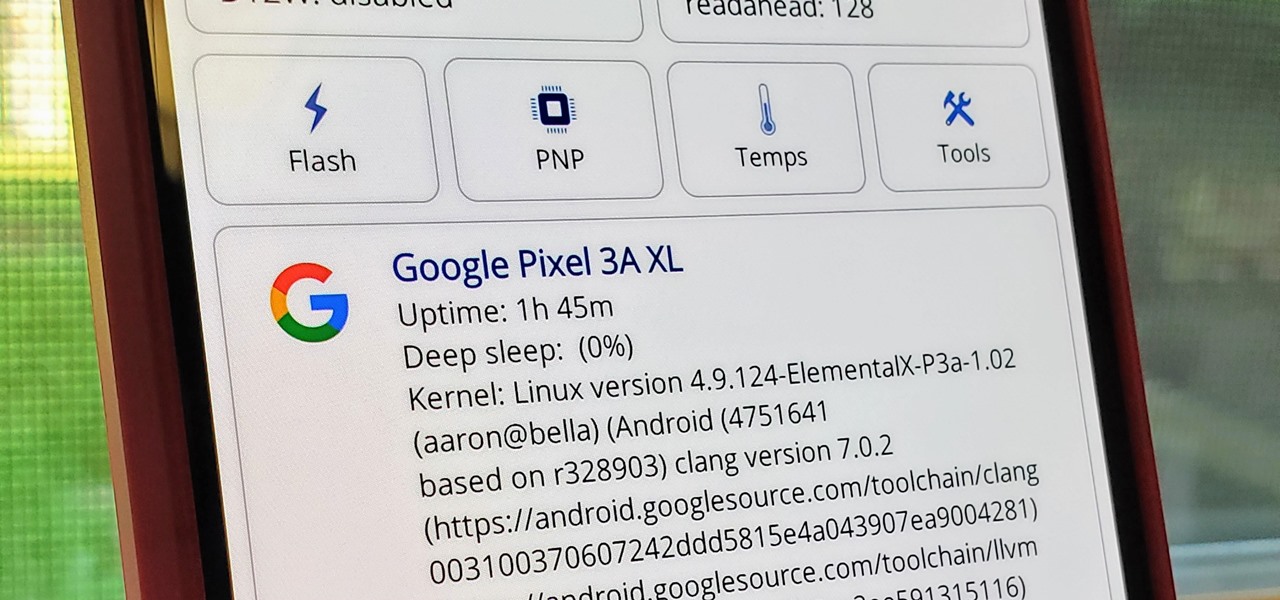
The Pixel 3a runs smoothly out of the box already, but installing a custom kernel can supercharge your experience even more. From fine-tuned CPU tweaks for boosting performance or battery life to adjusting the display colors for your screen how you want, ElementalX kernel can provide you with a ton of new features you didn't know you were missing.

Ask anyone that works on the development of driverless vehicle technology and there is a very good chance that AutonomouStuff will have supplied something to their project.

Keeping the books in order is one of the great challenges every business owner faces. Having a great product or service is one thing, but managing the minutia of invoicing can trip up a lot of small- and medium-sized businesses.

There are many ways to attack a Wi-Fi network. The type of encryption, manufacturer settings, and the number of clients connected all dictate how easy a target is to attack and what method would work best. Wifite2 is a powerful tool that automates Wi-Fi hacking, allowing you to select targets in range and let the script choose the best strategy for each network.

Developed by Open Whisper Systems, Signal is a free, open-source encrypted communications app for both mobile and desktop devices that allows users to make voice calls, send instant messages, and even make video calls securely. However, a vulnerability was recently discovered for the desktop version that can be turned into a USB Rubber Ducky payload to steal signal messages with a single click.

Many guides on Null Byte require using the Secure Shell (SSH) to connect to a remote server. Unfortunately for beginners, learning to use SSH can become a confusing mix of third-party programs and native OS support. For Chrome OS users, using SSH is even more difficult. We'll fix this by using the Chrome Secure Shell to establish an SSH connection from any device that can run a Chrome browser.

In my previous article, we learned how to generate a vulnerable virtual machine using SecGen to safely and legally practice hacking. In this tutorial, we will put it all together, and learn how to actually hack our practice VM. This will provide some insight into the methodology behind an actual attack and demonstrate the proper way to practice on a VM.

In a world increasingly regulated by computers, bugs are like real-life cheat codes. They give you the power to break the rules and do good or bad without ever leaving your seat. And government agencies around the world are discovering and stockpiling unreported bugs as cyberweapons to use against anybody they see fit.

Remember portable MP3 players like the classic iPod? Seems like forever ago that they were all the rage, and I don't think I've seen a real one in the wild for a good 5 years now. These devices died out so quickly as a direct result of the onset of smartphones, which allow us to do everything that an MP3 player could do and then some.

Coffee shops are great places to unwind and get some free Wi-Fi, but all the bandwidth in the world can be ruined by someone being a noisy jerk. I usually start blasting music through my headphones whenever that happens, but that isn't always the most ideal situation, especially if I'm trying to study or work.

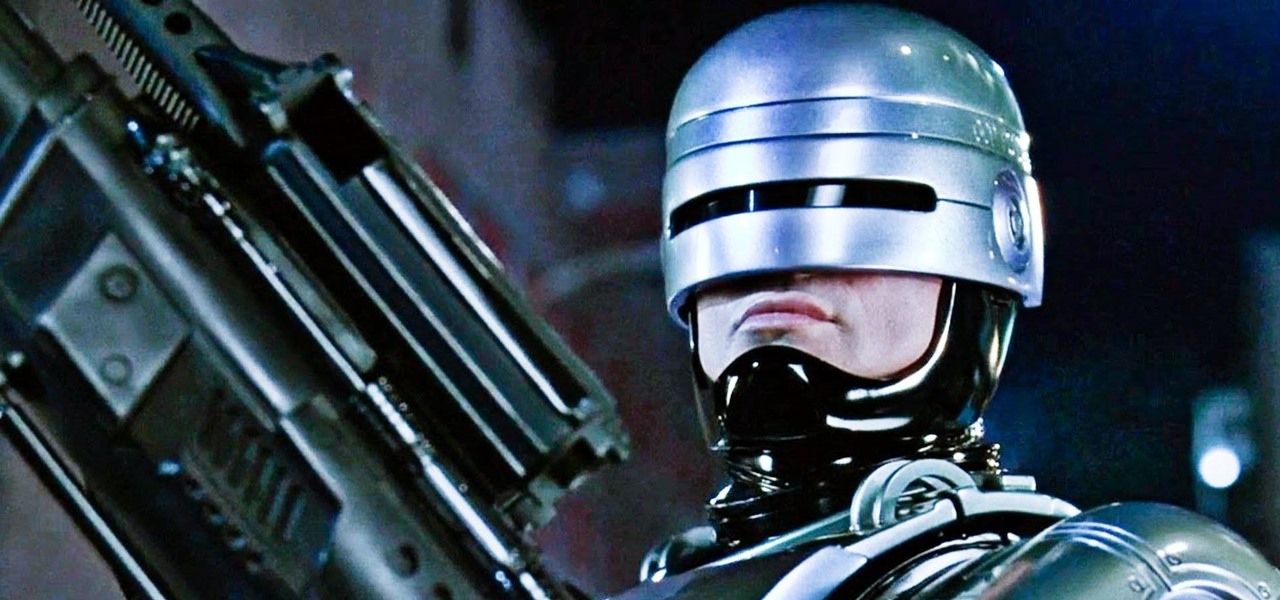
"Dead or alive, you're coming with me!" That iconic quote from the 1987 movie RoboCop was repeated by kids like me for years. The 2014 reboot introduced the baddest robot-cop on the planet to new audiences worldwide. While it didn't live up to the amazingly high expectations set by its predecessors, RoboCop 2014 did show off some newly upgraded gear. The modern look is cool and all, but rolling to a party rocking the 1987 helmet with the retro visor cannot be beat. With Halloween coming up, i...

Automated tattoos are now a reality, with 3D printers being hacked into tattoo machines. Multiple people have posted videos of their 3D printer that can "print" tattoos, with one of the more impressive ones shown in the two videos below.

Starting today, you can experience all the unique feature of Samsung's next flagship device, the Samsung Galaxy S5, right on your Galaxy S3 or other Android device.

This HTML web design tutorial will explain what HTML is and how it can benefit you rather you are looking to build a website from the ground up or you are planning on using a combination of automated software and HTML Design and need the flexibility to still make fine tune edits to your website. From a simplistic view the primary purpose of HTML design is to interpret and display text based content in a given web browser. For example when you read articles online from places like wall-street ...

Tons of people listen to music while going to sleep, but some don't like to leave it playing all night. If you hate waking up in the middle of the night and having to turn off your music, why not make your smartphone do it for you?

As a multitasker, I've embraced the hustle and bustle that has filled my life. I'm constantly doing several things at a time, while looking for shortcuts to finish all of these things quicker than before. I brush my teeth with my cell phone in hand and drive to work with breakfast in mouth—I spare no time. Well, now there's an application for the Mac users among us that can help take some of the stress out of doing a thousand things at once.

In the Windows 8 Enterprise edition, you can use the Windows to Go feature to travel with Windows 8 OS, personal files, documents, settings and many more. All you need is an external hard drive or USB drive of 32 GB space or more and USB 3.0 support or more for fast Windows 8 booting. We need the storage media of above specification to create bootable USB to access the data anytime by plugging the media into different PC running latest version of Windows 8 PRO or Windows 7.

Keys are on the way out. They're clunky, take up precious space, and slow you down when you have tons of identical-looking gold ones on your keyring. Everything we can open with keys can now also be opened with wireless technology in just a click—so why use keys anymore? Sure, you can pay hundreds of dollars for an automated lock system on your house—but why do that when you can build it yourself!

When you're a writer with work published across various online platforms, building a portfolio of your work can be pretty time-consuming. That's where Authory comes in.

Fireworks are the best part about the Fourth of July and other celebrations, but they can easily cause accidental injuries. It's both safer and more fun to set them off remotely, so we'll hack some standard fireworks with nichrome wire, a relay, and an Arduino to ignite remotely over Wi-Fi using any smartphone or computer.

There's actually more to the dialer screen on your OnePlus than meets the eye. Besides its obvious purpose of calling people, there's a vast array of secret codes that you can input to troubleshoot your device, in addition to revealing important information, making anonymous phone calls, and so much more.

Hackers rely on good data to be able to pull off an attack, and reconnaissance is the stage of the hack in which they must learn as much as they can to devise a plan of action. Technical details are a critical component of this picture, and with OSINT tools like Maltego, a single domain name is everything you need to fingerprint the tech details of an organization from IP address to AS number.

Analysis of photographs and social connections can be a huge component of social engineering. Understanding who a person is, as well as who they know, can establish links within a company. This information could be used by hackers to execute elaborate social engineering attacks.

Telemarketers can be as terrifying as a villain from a horror film. Your phone rings with an unknown 800 number, and you immediately fill with a sense of dread. There's no way to get them to stop calling; you imagine the number appearing on your phone at all hours of the day and night, haunting you.

Parkinson's disease, a condition that can impair movement and coordination, affects over 10 million people worldwide. And with around 60,000 Americans being diagnosed every year, we're on track to see almost one million Parkinson's afflicted Americans by 2020.

While Unity is already the leading 3D engine for augmented reality content in terms of volume, the announcement of Project MARS, a new augmented reality authoring tool, at Unite Berlin in June promised to expand AR development to a whole new audience of designers and other non-coders this fall.

With the arrival of iOS 12, Do Not Disturb has received long-overdue enhancements to make the feature more user-friendly. Among these changes is a subtle but incredibly convenient feature that helps ensure you remain undisturbed for short periods of time to more focus on your task at hand — without having to worry about turning it off manually or messing with complicated settings.

Two-factor authentication (2FA) is a great way to add another layer of security to sensitive third-party apps and websites like Venmo. However, before iOS 12, to log into a particular 2FA-secured app or site on your iPhone, you'd have to memorize or copy the SMS code from Messages, then jump back in a timely manner to log in. Apple's latest iOS version streamlines this process.

The AFL-CIO's Transportation Trades Division, which represents 32 unions in the US, has successfully lobbied for the removal of 10,000-lb. and heavier commercial trucks from provisions in bills expected to pass that could allow for millions of driverless vehicles on public roads and streets, Bloomberg News reported.

Faraday Future's all-electric super sports car concept attracted a lot of attention at CES earlier this year, but now it is struggling to replace key driverless engineers and program directors who left the company amid its recent financial troubles.

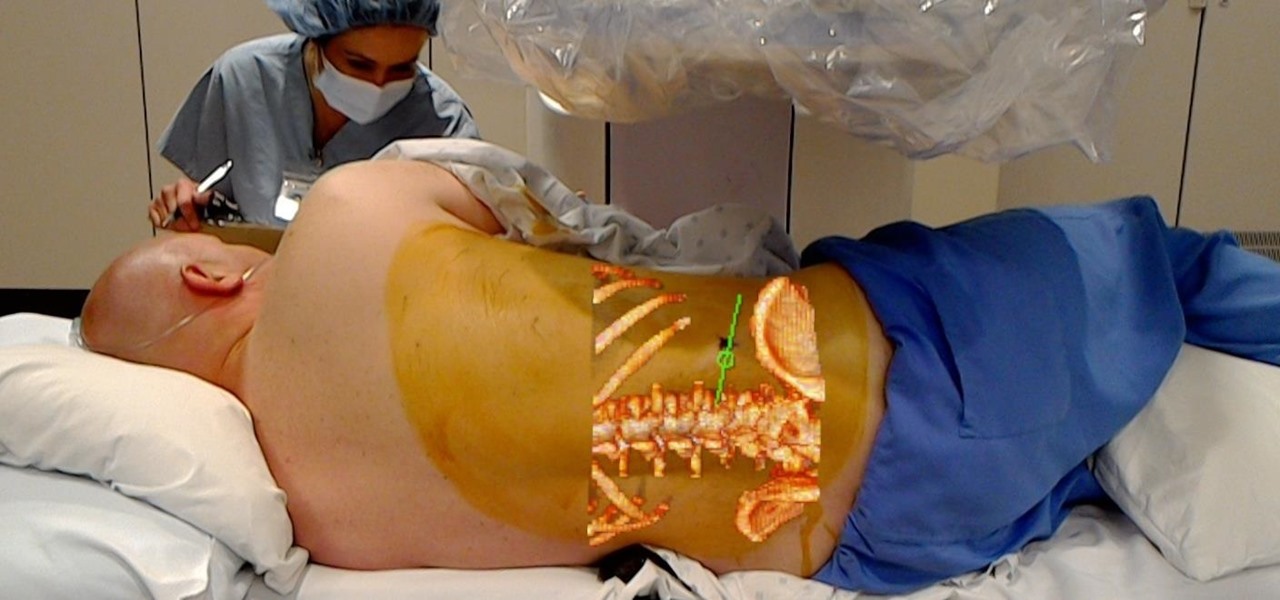
Numerous examples exist of doctors and surgeons using HoloLens to plan surgeries. The device has even been used to view reference images during a procedure and stream it to a remote audience. Until recently, it has not been used to augment the surgeon's view of the patient during a live surgery.

Delphi Automotive PLC has announced it is partnering with Transdev Group to develop on-demand driverless transportation systems, a deal that shows promise for autonomous development on a global scale.

Intel launched their Advanced Vehicle Lab in Silicon Valley this week, and the tech giant is now on the hunt for potential partners.

Despite a round of updates to Pokémon GO that patched and eliminated location spoofing, the game still has a difficult time dealing with the most hardcore cheaters. Like weeds on a grassy lawn, third-party bot makers still remain the biggest thorn in Niantic's side and continue to thrive despite the developer's best efforts to root them out. While the latest updates have blocked users from running modded versions of the game, like Pokemon GO++, that feature built-in joysticks to move your pla...

In a race to make self-driven cars mainstream, Intel announced today that they've bought Israeli microchip technology company Mobileye for $15.3 billion, setting the stage for Intel to dominate a large portion of the driverless market.