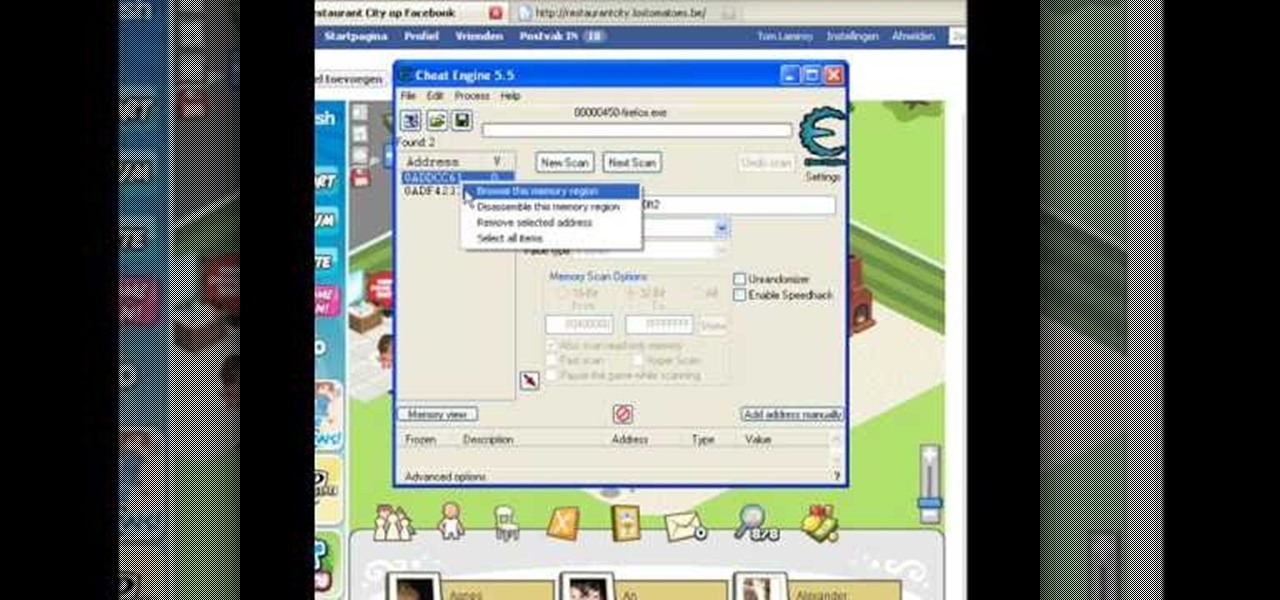
How To: Hack Restaurant City coins & gourmet pts (05/31/09)
Make sure you use FLASH Player 9 First: Deinstall Flash Player 10

Make sure you use FLASH Player 9 First: Deinstall Flash Player 10

Because of the way Google Play works, Android has a "bad app" problem. Google allows any developer to upload an app to the Play Store, regardless of if it works, how it looks, or whether or not it can harm users. Malware scanning happens primarily after apps are uploaded, and though Google has recently taken steps to safeguard users with its Play Protect program, you don't have to depend on them.
Scanners are much too cumbersome to fit in a pocket, but with the use of just one application, you can replace all that bulky hardware with your Android smartphone and take it with you wherever you go. All you need to do is find the scanning app that fulfills your needs. Here are our five favorites that are good for business pros and average joes alike.

Welcome back, my fledgling hackers! One of the first issues any hacker has to address is reconnaissance. Before we even begin to hack, we need to know quite a bit about the target systems. We should know their IP address, what ports are open, what services are running, and what operating system the target is using. Only after gathering this information can we begin to plan our attack. Most hackers spend far more time doing reconnaissance than exploiting.

This video tells us the method to remove Trojan Virus from the computer. This can be done in a couple of steps. The first step involves the downloading of a specific application from the web. We have to search this application in Google. Type 'malwarebytes' in the search engine and press enter. Go to the third result starting with 'Malwarebytes Anti-Malware'. Click on 'Download Now' on the resulting page. Open the application and select 'Perform quick scan'. This will scan the computer for Tr...

Scanning is an awesome, fast way to transport a document into your computer. But, what if you want to edit it once you've scanned it? Most scanner programs will import your document as a read-only PDF or image file. With this tutorial, learn how to use the program ClaroRead on a Mac to scan your document directly into Microsoft Word for editing. This will save you a lot of time and a lot of annoying formatting and copy and pastes!
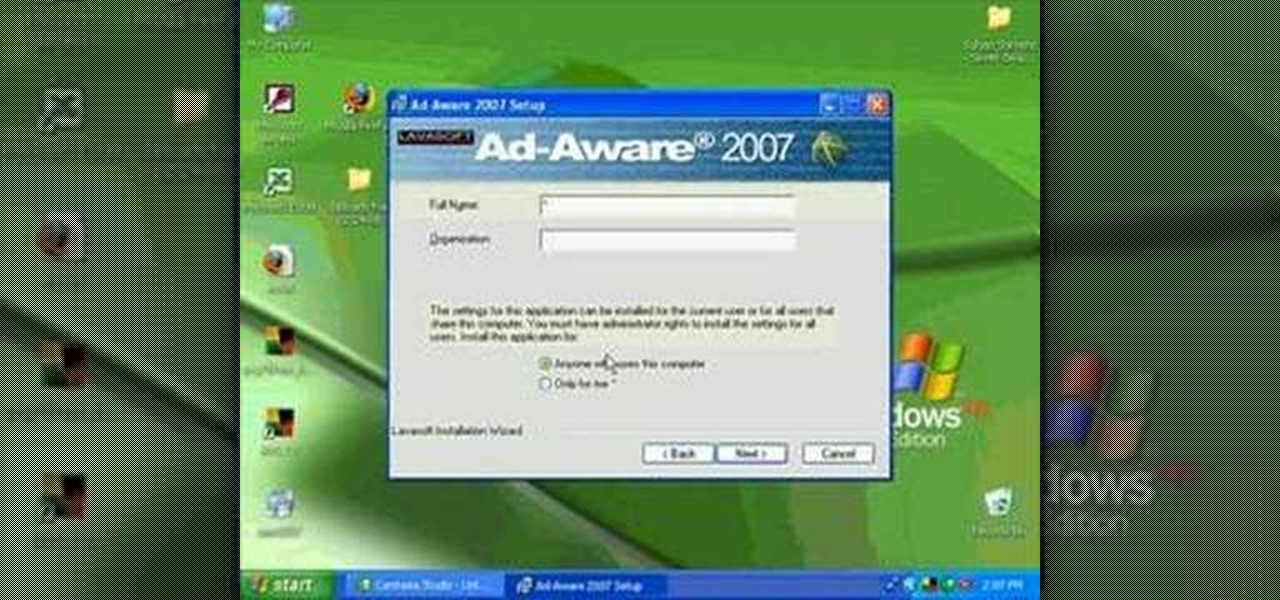
This is a Computers & Programming video tutorial where you will learn how to remove annoying spyware on your PC in Windows XP. Some spyware can be really nasty. This video shows how to remove spyware for free. Go to Download.com, and search for ‘ad aware’, download and install it. This video recommends Ad-Aware. While installing, select safe mode of scanning, otherwise some spyware may not be detected. Then, you need to update the definitions. Keep the definitions updated regularly. After upd...

Don't cancel your virus scans because they're inconvenient. Reschedule them! Watch this software video tutorial to learn how to schedule and reschedule AVG anti-virus scans so you can complete them whenever you want to. This how-to video is geared toward new AVG users.
Today is election day, or maybe not, but you're going to have to learn how to vote sooner or later anyway.

As part of the iOS 11 update, Apple added a document scanner function that creates high-quality digital copies of physical documents, but it was only available inside the Notes app. With iOS 13, Apple has built its scanner right into the Files app, enabling you to quickly create PDFs with your iPhone and do more with them.

One of the first steps in reconnaissance is determining the open ports on a system. Nmap is widely considered the undisputed king of port scanning, but certain situations call for different tools. Metasploit makes it easy to conduct port scanning from directly inside the framework, and we'll show you three types of port scans: TCP, SYN, and XMAS.

A remote administration tool, or RAT, is a piece of software used for remotely controlling machines. They are commonly used by tech support to gain remote access for troubleshooting purposes, but RATs are also an important part of a hacker's advanced persistent threat (APT) toolkit. Unlike standard administration RATs, these tools are designed to be delivered stealthily and operate undetected.

For many of you, this is common knowledge. But I still regularly see comments posted here and elsewhere asking, "This <AV bypass> doesn't work, because when I upload my payload to VirusTotal...."

Welcome back, my budding hackers! I've written several listener guides on creating a malicious PDF or malicious Word document that would carry in it a payload with the Meterpreter, or reverse shell enabling you to own the system. One of the hurdles to using these techniques is the antivirus (AV) software on the target system. For instance, if you try to email a malicious PDF or Word doc, it's likely that the victim system will alert the victim that it contains a virus or other malware.

In this tutorial, we learn how to scan and edit negatives with SilverFast and Photoshop. First, open up the software and lay your negative in the scanner. Make sure you have selected the correct settings when you go to scan it, and click that it's transparent. Also, you will need to increase the size of it and make sure the lighting is correct. Now, scan the image and load it onto the software. Once it's loaded, you will be able edit it by zooming in and then rotating the image so it's the co...

With technology nowaday, it has become so much easier to scan documents. In the past, people would always take their work to places like Kinkos and pay others to do something that would be simple and easy to do at home. But since the release of multi-functional printers that not only print, they scan, fax, and can even download pictures directly to your computer. This tutorial will show you how to scan a document and send it to your Word program. Enjoy!

Buying a digital camera doesn't mean your old prints, slides, or negatives are obsolete. You can easily convert them with a scanner to bring them into the 21st century. Watch this video to learn how to convert photos to digital.

When it comes to attacking devices on a network, you can't hit what you can't see. Nmap gives you the ability to explore any devices connected to a network, finding information like the operating system a device is running and which applications are listening on open ports. This information lets a hacker design an attack that perfectly suits the target environment.

The Galaxy S9 is full of minor improvements and revisions that come together to make it a worthy upgrade over the Galaxy S8. One such improvement is facial recognition, which Samsung has fortified with machine learning and the inclusion of another sensor. The result of these efforts is called Intelligent Scan.
There are plenty of third-party apps for scanning documents on your iPhone, but they can all be tossed out the door since iOS 11 includes one by default now. Instead of a dedicated app, it's included as part of the Notes app, and it's fairly easy to use. After scanning, you can save it, print it, turn it into a PDF, add markup, and more.

So you want to create a meterpreter virus, but you keep getting caught by AV. How do you create one that will go undetected? In this tutorial, I'll teach you how to code your own simple virus that will download a powershell payload from an apache webserver and execute it - bypassing antivirus.

Welcome back, my budding hackers! We've spent a lot of time learning to compromise Windows systems, and we've successfully compromised them with Metasploit, cracked their passwords, and hacked their Wi-Fi. However, very little time was spent developing ways to extract the information from the system once inside.
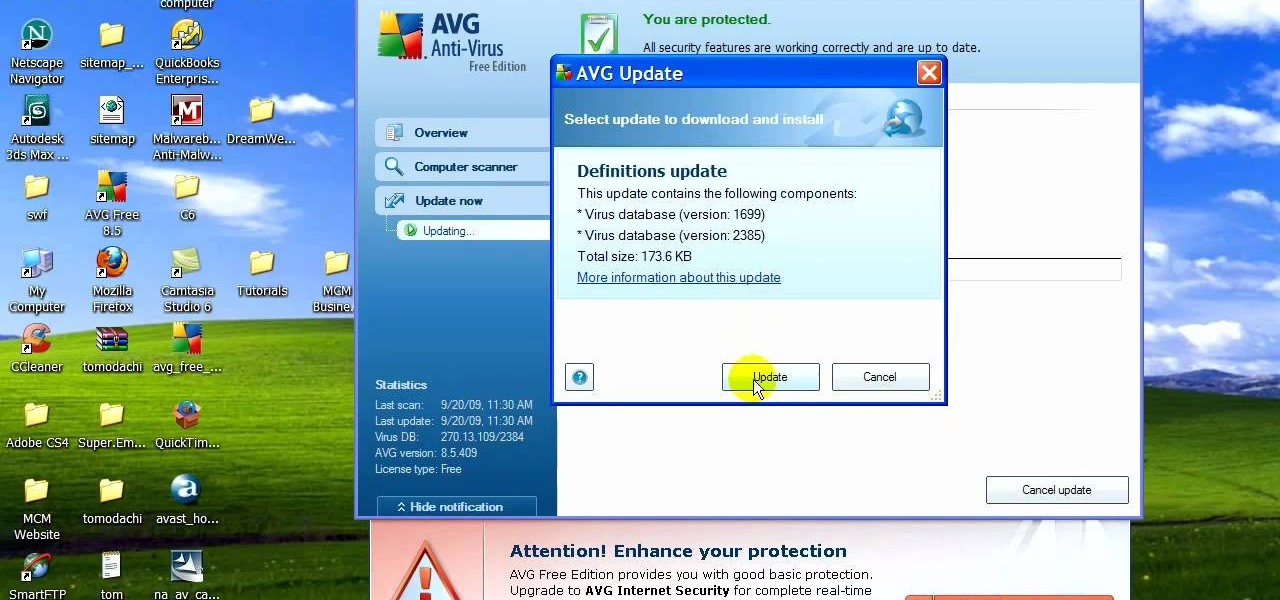
If your computer is working slow--or not at all, there could be some unsavory programs running amok in your system. Trojans, malware, viruses, and hacks are dangerous to the health of your operating system. This video tutorial demonstrates the measures to take in order to rid your PC of malicious programs. Stop being bullied by harmful applications and use such programs as AVG Antivirus and Malwarebytes to protect your computer. Once you've cleaned up your system, be sure to configure your se...

In the season finale of Know How, Tim uses a laser pointer and a wine glass to scan a 3-D image of his mom’s head. You have to see it to believe it.

While Apple has moved on from Touch ID to Face ID in newer iPhone models, there are still plenty of iPhones with fingerprint sensors — in fact, Apple's second-generation iPhone SE is the first new Touch ID iPhone in three years. With Touch ID, you can register up to five fingerprints, but it doesn't stop there. Using a little-known trick, you can sneak another five fingerprints in there for a total of ten.
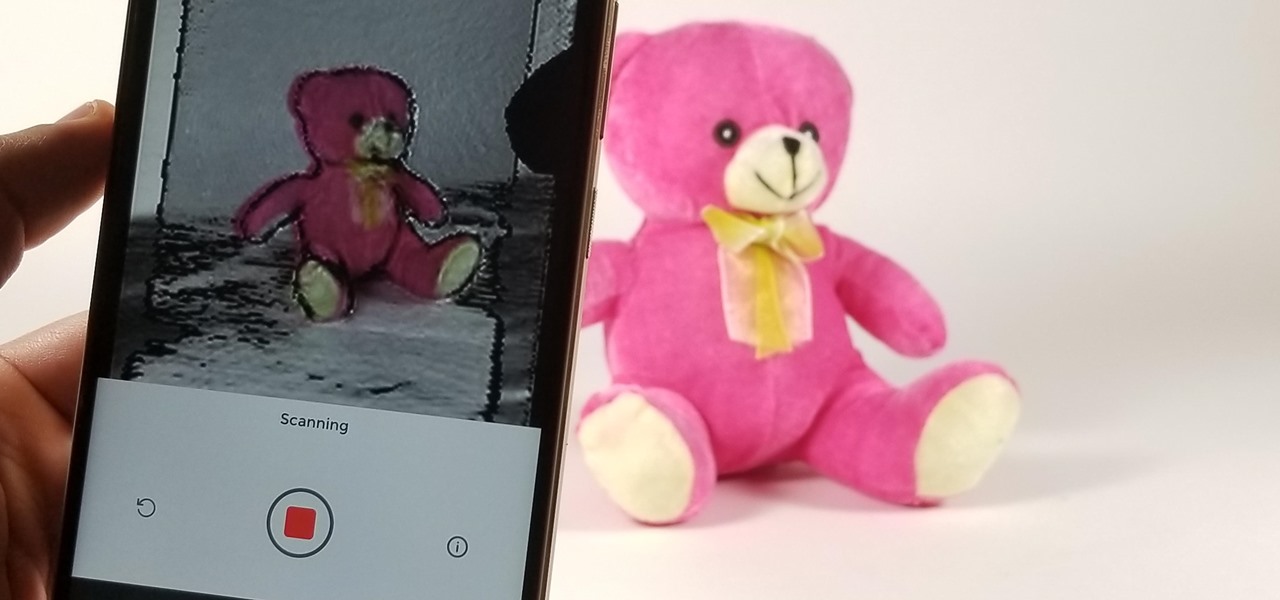
Mobile 3D scanning company Scandy has released a new app for devices on Google's Tango mobile AR platform that gives users the advanced 3D scanning capabilities.

As you might know, there are a multitude of tools used to discover internal IP addresses. Many of these tools use ARP, address resolution protocol, in order to find live internal hosts. If we could write a script using this protocol, we would be able to scan for hosts on a given network. This is where scapy and python come in, scapy has modules we can import into python, enabling us to construct some tools of our own, which is exactly what we'll be doing here.

Believe it or not, there was a time when smartphones weren't the primary tool for taking photos. People actually walked around with bulky film-based cameras on their necks, and some even used cheap disposables. While photography wasn't introduced to the world when smartphones came out, it's definitely more accessible—and everyone is a photographer now.
Spyware are programs that infect your system and / or at the same time collect personal information without your consent.

No more do you have to buy additional equipment just to send a quick fax out. And no more going to the local copy store to pay for faxes. Windows 7 has a great feature built right in called Windows Fax and Scan. See how it works.

James Marey teaches how to test whether your Anti virus is still working perfectly. First right-click anywhere on your desktop, go to 'New' and select 'Text Document' to open a new document. Now find some text containing a virus from the internet or you copy the text from the video. After entering the text, go to file and save the document. Now if your anti virus is working perfectly it will pop out a virus threat indicating the file you just saved. Finally select the appropriate option to re...

See how to scan and read QR codes with your iPhone's camera. Whether you're the proud owner of an Apple iPhone 4G or perhaps just considering picking one up, you're sure to benefit from this free video tutorial. For more information, including a detailed overview, watch this iPhone user's guide.

Want to digitally restore an old family photograph in Adobe Photoshop? Before you can remove noise and dust, you'll need to scan and crop it. Maximize dynamic range with Photoshop's levels and curves tool. Whether you're new to Adobe's popular image editing software or simply looking to pick up a few new tips and tricks, you're sure to benefit from this free video tutorial from the folks at Britec Computer Systems. This video offers a step-by-step guide on how to scan and crop images using Ph...
Need a way to convert your scanned documents back into text files? Check out this video tutorial on how to convert scanned documents (JPG, PDF) to text.

The ability to stay organized and be resourceful with data gathered from recon is one of the things that separates the true hackers from the script kiddies. Metasploit contains a built-in database that allows for efficient storage of information and the ability to utilize that information to better understand the target, which ultimately leads to more successful exploitation.

Starting in iOS 11, Apple introduced a QR code scanner for iPhone that's baked right into the Camera app, reducing the need for a third-party scanner. However, not everyone knew it existed, so a lot of users were still using third-party QR code scanners. In iOS 12 and later, Apple addressed the issue, making theirs much more visible, as well as improved QR code scanning in general.
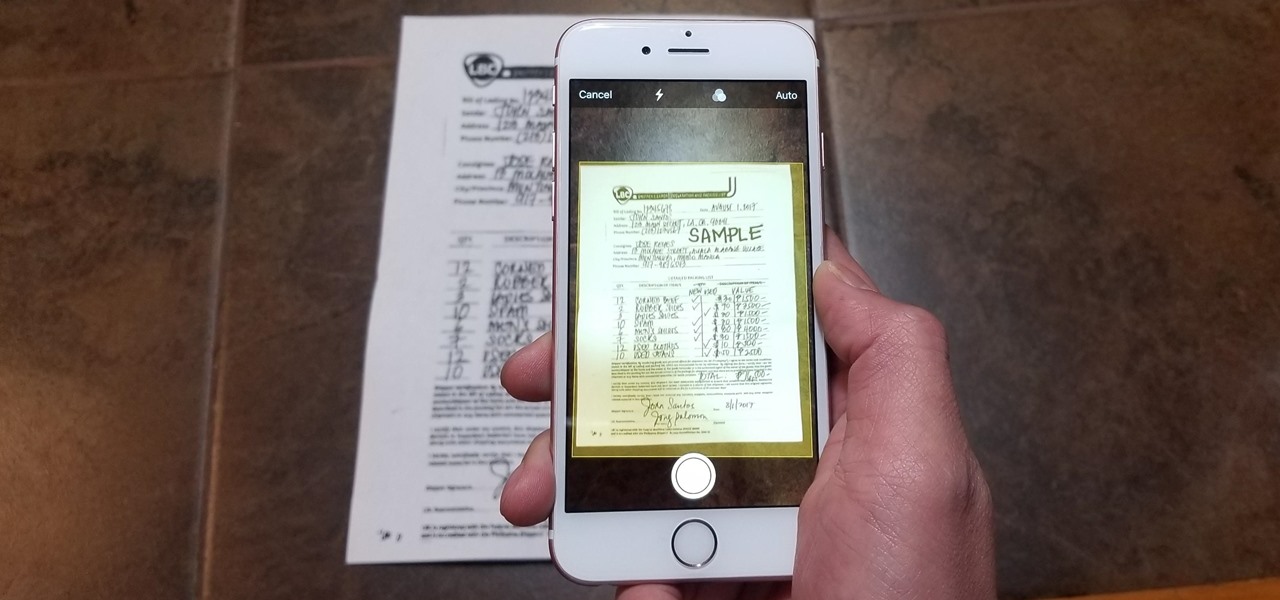
Scanning important paperwork on smartphones is a tedious process, often relying on either external scanners or third-party apps that had to be either purchased or were loaded with annoying ads just to get the job done. Thankfully, iOS 11 now lets you easily scan documents using your iPhone, and finally does away with the need for third-party apps or machines.

At IFA in Berlin today, Sony introduced the latest models of the Xperia line, with new features in tow that should appeal to creators of augmented and virtual reality content.

These days, that pocket-sized computer we call a smartphone is home to your entire digital life. But with the onset of mobile payments and online banking, the line between your virtual world and the physical realm is becoming increasingly blurred.

Welcome back, my novice hackers! Reconnaissance is one of the most important preparatory steps to hacking. As I have emphasized many times before here on Null Byte, you must know the operating system, the ports, the services, the applications, and sometimes even the language of the target to be effective. If you haven't taken the time to gather this info, then you are likely wasting your time.