If you haven't heard yet, Google made it possible a couple months ago for every Android user running 2.2 or higher to track his or her smartphone or tablet using their Android Device Manager service. It's a super easy way to track, lock, and secure erase your Android device from the web without ever having to download a third-party application, like Droid Finder, since it occurs in the background via Google Services.

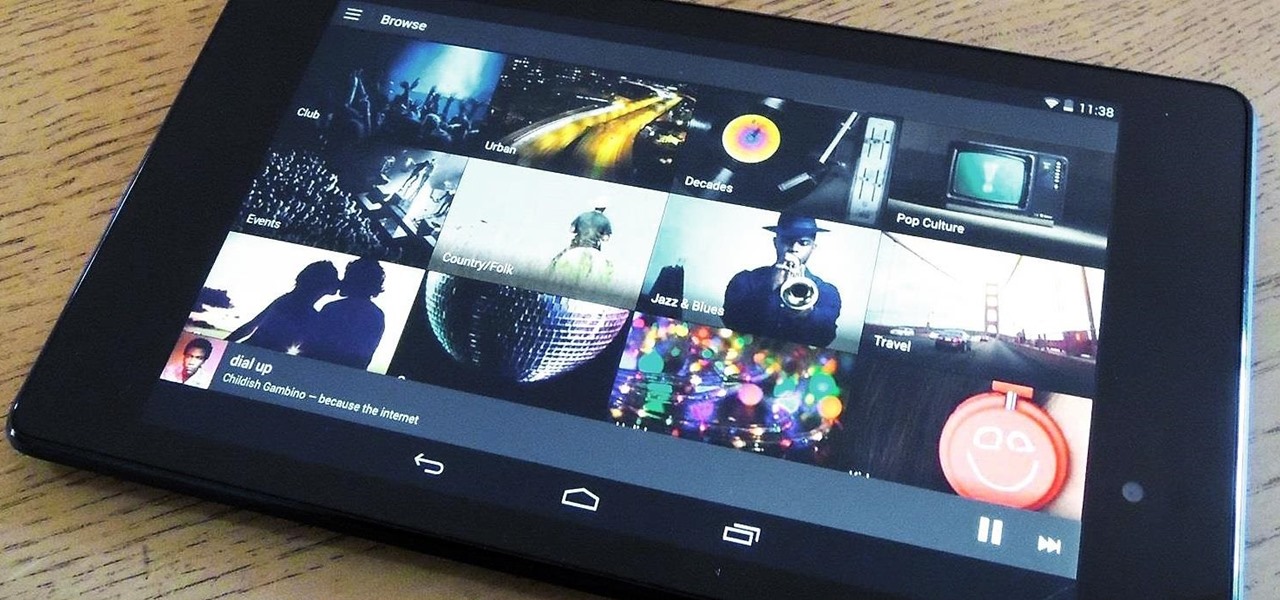
You've probably see this a million times on your Nexus 7 tablet: On some streaming sites it's "You need to upgrade your Adobe Flash Player to watch this video," and on others it may be "You need to install the Adobe Flash plugin." Whatever it is, you have the same problem—Flash does not work on your Nexus 7.

When Disney teased an augmented reality game called Star Wars: Jedi Challenges running on a headset from Lenovo, fans had more questions than Disney had answers. When? How much? Can I be a real Jedi?
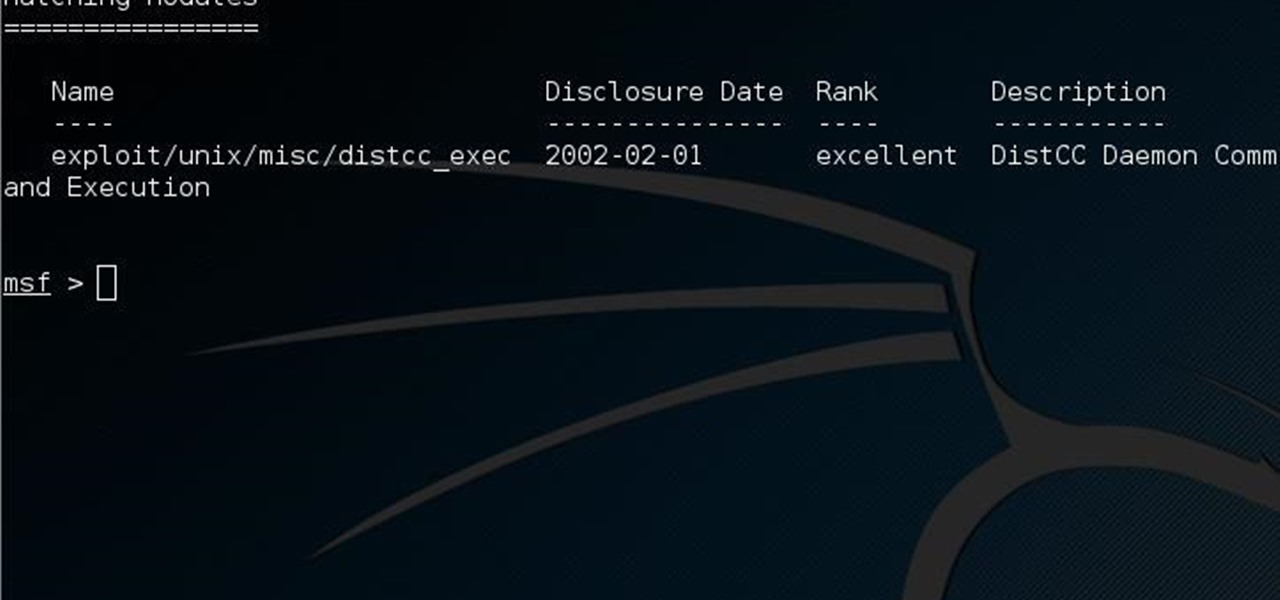
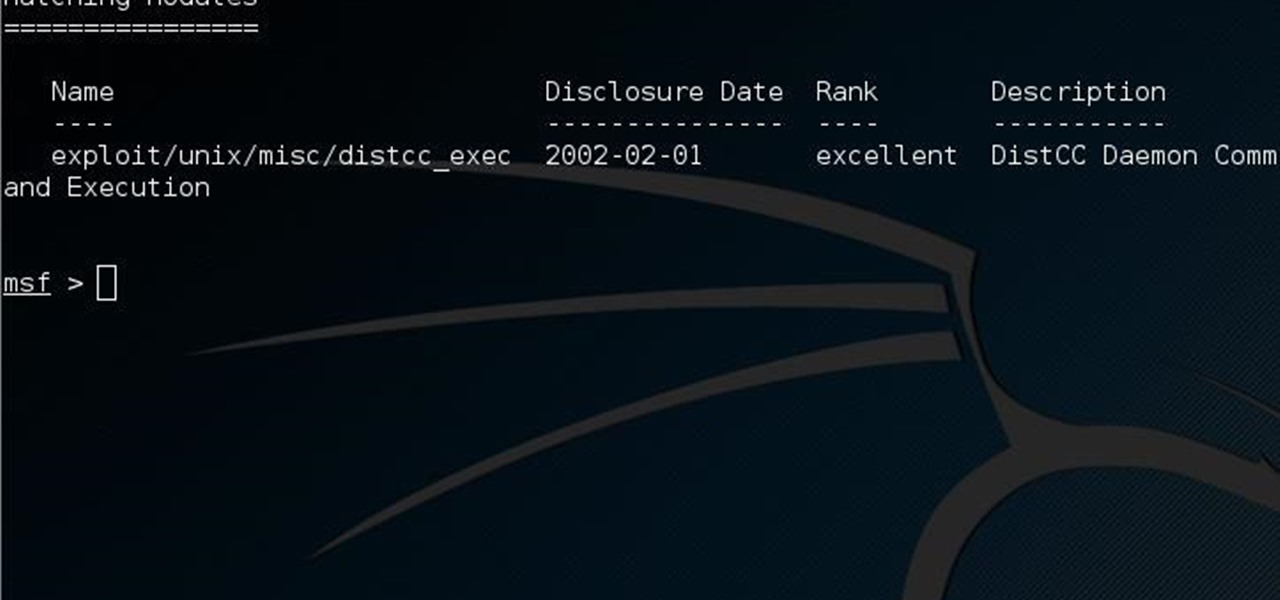
This guide is written for anyone who is practicing his penetration skills using the Metasploitable 2. The problem that we are facing here is that we have to penetrate to Metasploitable 2 and when this happens we understand that we are not logged in as root but as a user with less privileges!

Autocorrect, a common feature available on most Android keyboards, helps fix fat-finger typos and even predicts the words you want to write. Without this feature, it'd take me about 5 minutes to write a sentence, and even then, it'd probably still be intelligible.

The outstretched arm, the perfectly positioned angle, the shot and the subsequent array of tinkered saturation, contrast and shadows. In almost every car, changing room, or Starbucks, these string of events happen—you might know it as the selfie.

You've got a brand new Nexus 7 tablet for Christmas, and you're extremely eager to start using it. There are many things you can do with it, like shake for new wallpapers, get rounded screen corners, and make it help you fall asleep at night. But, before you get into softModding your Nexus 7, you should know the basics, and if you've come over from a Kindle, turning your new Android tablet into a powerful eReader is a must.

What can be said about Spotify that most of us don't already know? It's the most popular digital music streaming service out there, giving you access to millions of songs on your computer. However, the mobile service was once an exclusive feature for paid subscribers. Not anymore, suckers.

The easiest way around a security policy is to find users who don't follow it. The Have I Been Pwned database identifies accounts with information breached by major third parties like Yahoo and LinkedIn. With Maltego, hackers can locate breached accounts created using company email addresses, potentially giving attackers access to a company account if the employee reuses a compromised password.

Your iPhone's Mail app has a lot of fantastic productivity features, such as unsending emails, follow-up reminders, opening drafts from almost any view, the snooze option, bulk-selecting messages, and the formatting toolbar, but one of the most helpful ones might just be the one you're not using.

Android phones have supported keyboards and mice for a long time, and you've even been able to use physical keyboards with iPhone and iPad models. But iOS 13 and iPadOS 13 finally include official mouse support. That means you can use a wireless or wired mouse and keyboard with your iPhone or iPad, though, a futuristic peripheral that combines the two may be even better.

Apple's latest updates to its operating systems add another security feature to its Find My service, so you have an even better chance at locating your lost iPhone, iPad, or Mac should it ever happen. As long as you have the option enabled, you can leverage other Apple users' devices to find yours on the map.

Who's ready to let future Facebook augmented reality smartglasses read their brain? Well, ready or not, the tech giant is making progress in the area of brain control interfaces (BCI) by funding research.

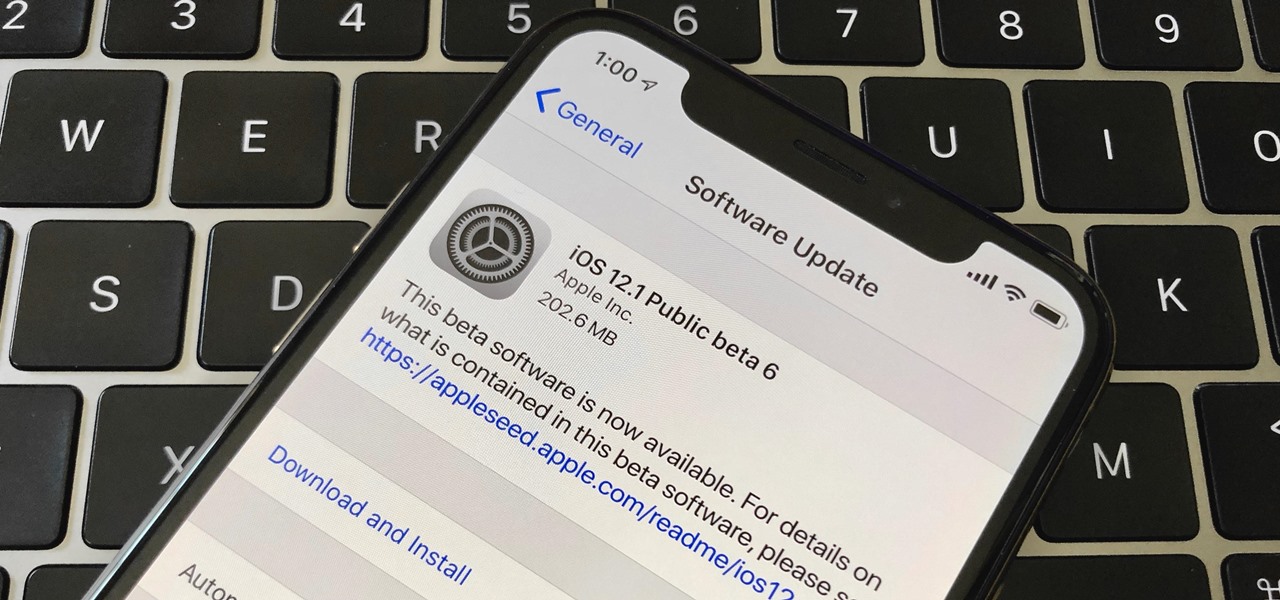
Right after Apple released iOS 12.2 dev beta 6 on Monday, March 18, it seeded the public beta version. So far, from what we can tell, the sixth beta includes a patch for an Apple Pay issue and yet another update to the "About" page in Settings, this time with a new section for warranty and insurance information.

On April 26, 2019, Sinemia posted a note on its website stating it has ceased all operations in the United States. It's not known if it continues to work in other countries or if US users will be getting any refunds, particularly, for annual subscribers.

At this point in our series on creating a customized hacking container, you should be able to use Docker to save and retrieve customized instances of Ubuntu from your own machine. Make sure to revisit part one and part two if you need a refresher.

WhatsApp is one of the most well-known and most utilized cross-platform chat applications available today. It's free for one year, and only $0.99 a year after, which is chump change when you realize there are no hidden costs like international charges. Basically, it creates an easy to use forum for you and your friends to chat, regardless if they're an Android or iPhone user.

The Jetsons may not have gotten everything right about the future, but even though we may not have flying cars or live in the sky (yet), one thing they imagined correctly was our electronics eventually being able to understand us.

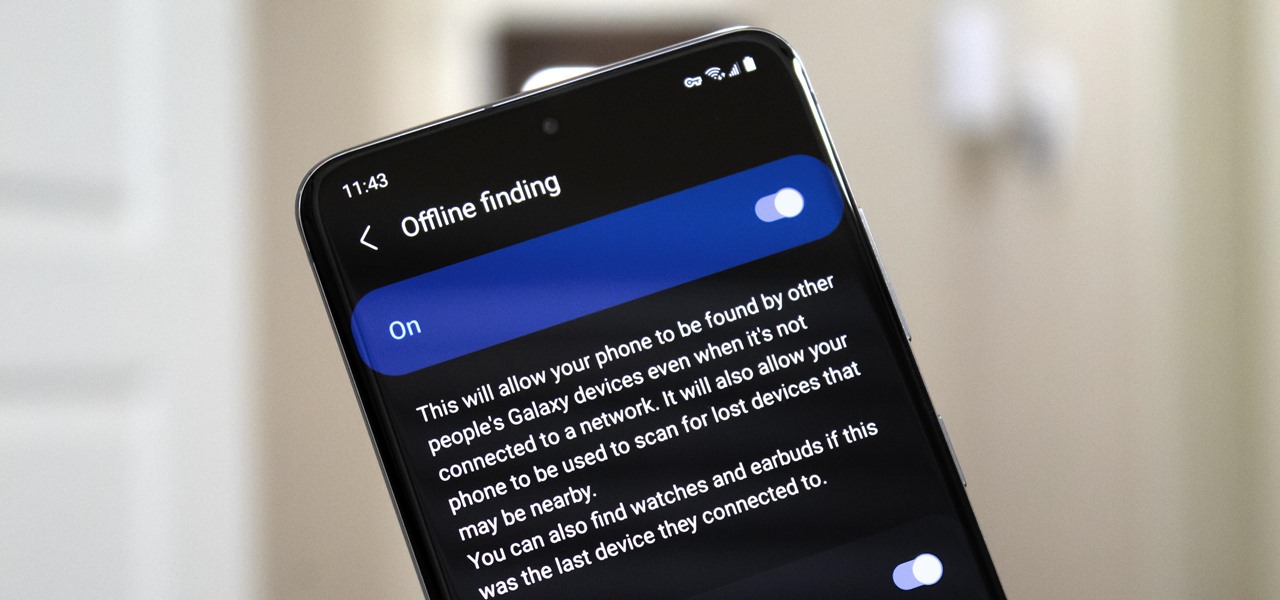
Nowadays, even the dumbest thieves know that the first thing you should do after you steal a phone is turn on airplane mode. Not only does this make it harder for police to track the phone through cell tower triangulation, but it also disables security features the person you stole it from may have implemented — for instance, Samsung's Find My Mobile service.

Apple's upcoming update for the iPhone, iOS 13, is introducing over 200 new features. Many of those were never formally announced, instead silently released in new updates to the beta. After eight developer beta cycles, we were anxiously awaiting the release of developer beta 9. What we got instead, however, was the first iOS 13.1 developer beta.

Like an overbearing mother, Apple will constantly nag you through annoying red bubble alerts about iOS updates that are ready to install. Fortunately, you don't have to take this issue lying down, as there are ways to prevent your iPhone from receiving OTA updates and their corresponding prompts, regardless of whether your device is jailbroken or not.

After a long hiatus, we shall once again emerge from the shadowy depths of the internet to build an exploit. This time, we'll be looking at how to defeat a non-executable stack by using the ret2libc technique — a lean, mean, and brilliant way of exploiting a stack overflow vulnerability.

Super Bowl LII will bring millions of football and non-football fans together to watch the big game on the big screen. But without a cable subscription, this process can be a little daunting. Luckily, the Google Play Store and the iOS App Store offer a few ways to accomplish this — no cable contract required.

For years, PuTTy has reigned supreme as the way to establish a Secure Shell (SSH) connection. However, those days are numbered with the addition of the OpenSSH server and client in the Windows 10 Fall Creators Update, which brings Windows up to par with macOS and Linux's ability to use SSH natively.

Some of us woke up at the KRACK of dawn to begin reading about the latest serious vulnerability that impacts the vast majority of users on Wi-Fi. If you weren't one of those early readers, I'm talking about the Key Reinstallation Attack, which affects nearly all Wi-Fi devices.

Welcome back, my rookie hackers! Most often, the professional hacker is seeking protected information from the target system or network. This might be credit card numbers, personally identifiable information, or intellectual property (formulas, plans, blueprints, designs, etc.). Most of my Null Byte guides have been focused on getting into the system, but this only begs the question—"what do I do when I get there?"

Your Nexus 7 may be a tablet, but it can also be used as a phone, thanks to the continued upswing of VoIP applications, which send voice and media messages over the Internet—not over a cellular network.

By default, as soon as you join a meeting on Zoom, both your microphone and camera turn on, sharing your audio and video to the other chat participants. While that isn't usually a problem, it can be an issue if the meeting hasn't started or you're entering in the middle of a class, and you don't want to disturb the video conference.

With Android 10 "Q" right around the corner, now would be a great time to get accustomed to the new system-wide dark mode it's bringing with it. Dark themes not only allow for more comfortable viewing at night, but can also consume less battery at the same time. With a single button tap, you'll be able to enable this new dark theme for all compatible apps without having to jump through hoops.

A major software tool first promised during the reveal of the HoloLens 2 earlier this year is finally available.

Encrypting payloads and encoding stagers are more effective against macOS than one might think. It's very easy to evade VirusTotal and macOS antivirus software using a few simple tricks.

On Thursday, Osterhout Design Group (ODG) revealed a new, specially-crafted oxygen mask that uses the same augmented reality technology from its smartglasses to assist FedEx Express pilots navigating dangerous conditions.

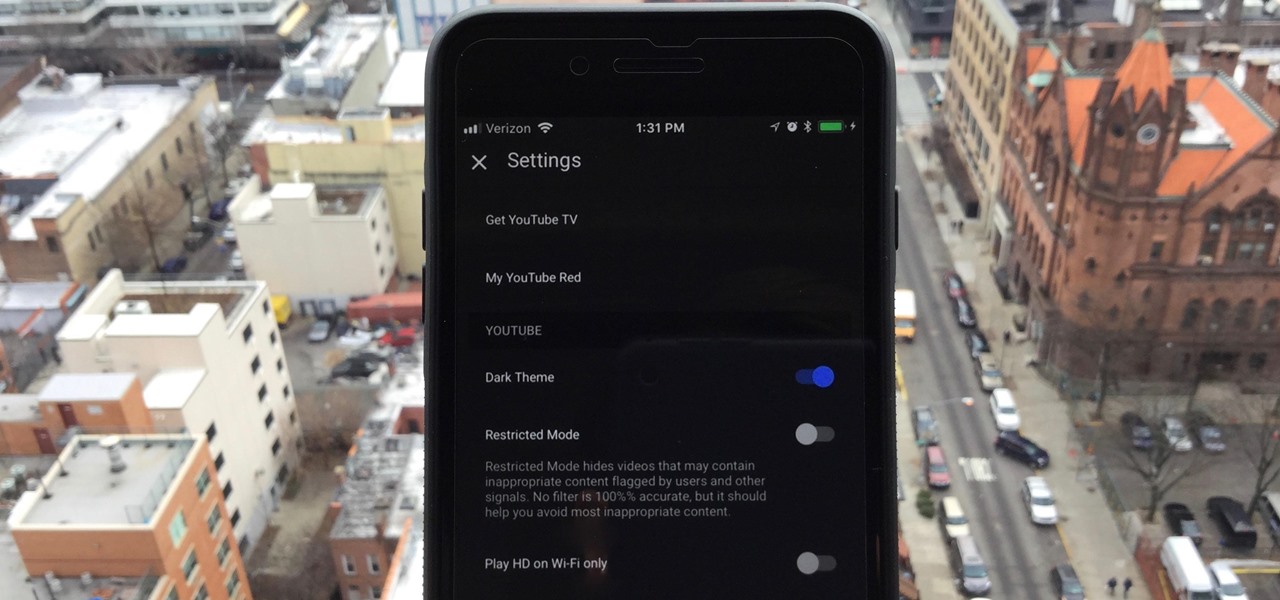
One of the downsides to iOS is the lack of a true dark mode. While Apple has offered a workaround, third-party developers have taken it upon themselves to implement dark themes in their apps. While big names like Twitter and Reddit have led the charge for some time, it appears YouTube is the next app to join the party.

The Pixel 2 and Pixel 2 XL launched in 2017 with three colors: Clearly White, Just Black, and Kinda Blue. For those who wanted to stand out from the crowd a bit, Kinda Blue was the clear choice. Verizon, however, had other plans in mind, and Kinda Blue became exclusive to the carrier. That is, until now.

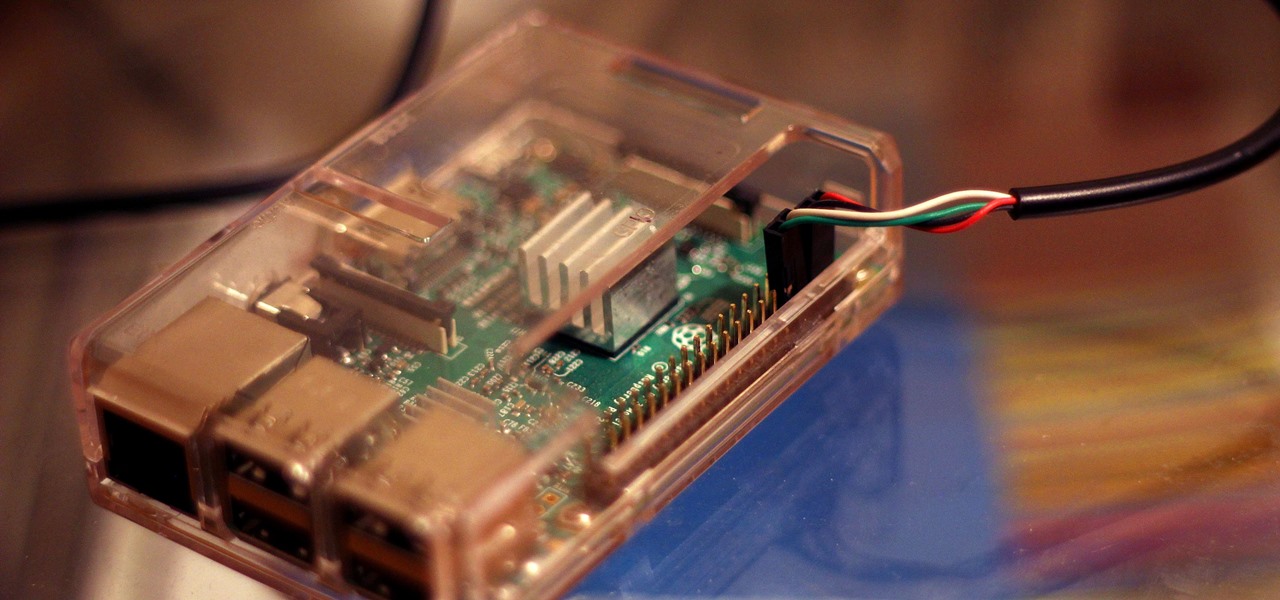
Connecting to your headless Raspberry Pi on the go typically requires a network connection or carrying around bulky peripheral hardware like a screen and keyboard. With the help of an old-school connecting standard, though, you can log into your Pi from any computer using a simple cable. If you don't have a power source, you can also power your Linux distro over the cable at the same time.

It feels like forever, but the wait is almost over. In less than a week, everyone will be able to try out all the cool new features in Apple's new iOS 10. This new update will be available on September 13 to most iPad, iPhone, and iPod touch users via the "Software Update" section in Settings.

It's been a long time coming, but HBO will finally be releasing their cable-free streaming service next month in the U.S., over two years after they had released similar standalone subscriptions in countries such as Norway.

Apple's new iPhone 6 and iPhone 6 Plus go on sale Sept. 19th, but pre-orders begin on Sept. 12th. If you're ready to trade in your iPhone 5 for one of these bigger and more iOS 8-friendly devices, you're probably going to pre-order.

There has been a lot of news over the last couple weeks about the popular Flappy Birds mobile game and its creator, Dong Nguyen.