Null Byte users have often requested video content, but the question has always been what format would best serve our community. This week, we partnered with Null Space Labs, a hackerspace in Los Angeles, to test the waters by hosting a series of talks on ethical hacking for students in Pasadena Computer Science Club. We invited students and Null Byte writers to deliver talks on Wi-Fi hacking, MITM attacks, and rogue devices like the USB Rubber Ducky.

A weak password is one that is short, common, or easy to guess. Equally bad are secure but reused passwords that have been lost by negligent third-party companies like Equifax and Yahoo. Today, we will use Airgeddon, a wireless auditing framework, to show how anyone can crack bad passwords for WPA and WPA2 wireless networks in minutes or seconds with only a computer and network adapter.

After gaining access to a root account, the next order of business is using that power to do something more significant. If the user passwords on the system can be obtained and cracked, an attacker can use them to pivot to other machines if the login is the same across systems. There are two tried-and-true password cracking tools that can accomplish this: John the Ripper and Hashcat.

While the security behind WEP networks was broken in 2005, modern tools have made cracking them incredibly simple. In densely populated areas, WEP networks can be found in surprising and important places to this day, and they can be cracked in a matter of minutes. We'll show you how a hacker would do so and explain why they should be careful to avoid hacking into a honeypot.

Sometimes you need a password to gain access to an older running Windows system. Maybe it's a machine in your basement you forgot about or a locked machine that belonged to a disgruntled employee. Maybe you just want to try out your pentesting skills.

A flaw in WPS, or WiFi Protected Setup, known about for over a year by TNS, was finally exploited with proof of concept code. Both TNS, the discoverers of the exploit and Stefan at .braindump have created their respective "reaver" and "wpscrack" programs to exploit the WPS vulnerability. From this exploit, the WPA password can be recovered almost instantly in plain-text once the attack on the access point WPS is initiated, which normally takes 2-10 hours (depending on which program you use).

Your driveway is not perfect and over time, can succumb to bothersome cracks that make driving very uncomfortable. They can even make walking harder, and are unsightly. But Lowe's has the solution to fill them up in a hurry— QPR's Pavement Crack Filler.

Welcome back, my rookie hackers! So many readers come to Null Byte to learn how to hack Wi-Fi networks (this is the most popular hacking area on Null Byte) that I thought I should write a "how-to" on selecting a good Wi-Fi hacking strategy.

Preventing S cracks in ceramic work can be simple when using these expert tips. Learn how to prevent S cracks with this free ceramics video series.

Since I first announced the new Null Byte recognition for excellence a few weeks ago, several of you have written me asking, "How can I study for this certification exam, and what material will be covered on the exam?" Now I have an answer for you. The White Hat Hacker Associate (CWA) will cover 14 domains or areas. Everything you need to know is here on Null Byte. There will be no questions that are not covered here on this site, guaranteed.

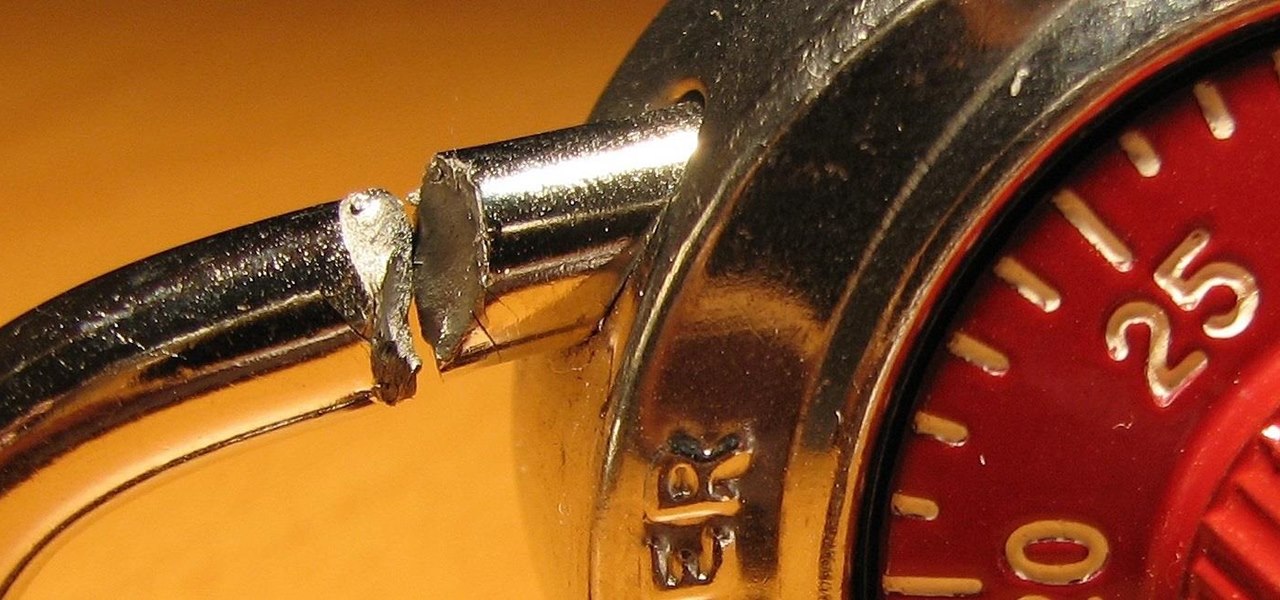
Without Tools, Crack a Combination lock! Meant to break into your own lock in case you forgot the combination. Learn how to reduce possible combinations from 64,000 to 100. This lock cracking trick will help you next time you need to pick a combination lock.

This video won't show you how to crack a safe but it will show you the next best thing: cracking a combination lock or master lock! We do recommend only trying this on a lock you have forgotten the combination to and not other unlawful purposes. Watch this video tutorial and learn how to retrieve the combination from a lock. Hack your own lock or your friends and you have the potential for great practical jokes.

During the holidays, many recipes call for cracked black peppercorn (it's much fresher and much tastier than regular pepper in a plastic seasoning jar).

Hello, Null Byters. I'm Barrow, and I'm excited to introduce myself as the new admin here on Null Byte. Just like previous admins have done before me, I will be writing new guides, updating older guides if they need it, and responding to some of your issues in the forum. Before I get started with any of that, though, I wanted to talk a little bit about myself and the future of Null Byte.

Welcome back, my neophyte hackers! Several of you have written me asking how to crack passwords. The answer, in part, depends upon whether you have physical access to the computer, what operating system you are running, and how strong the passwords are.

Cracked ukulele? Why not take a crack at its repair yourself? This tutorial demonstrates how to repair a simple cracked open seam with hot hide glue using the "percussion" technique—a method, which incidentally, will work for any wooden string instrument. For careful, step-by-step instructions, and to get started restoring your own damaged uke, watch this helpful how-to.

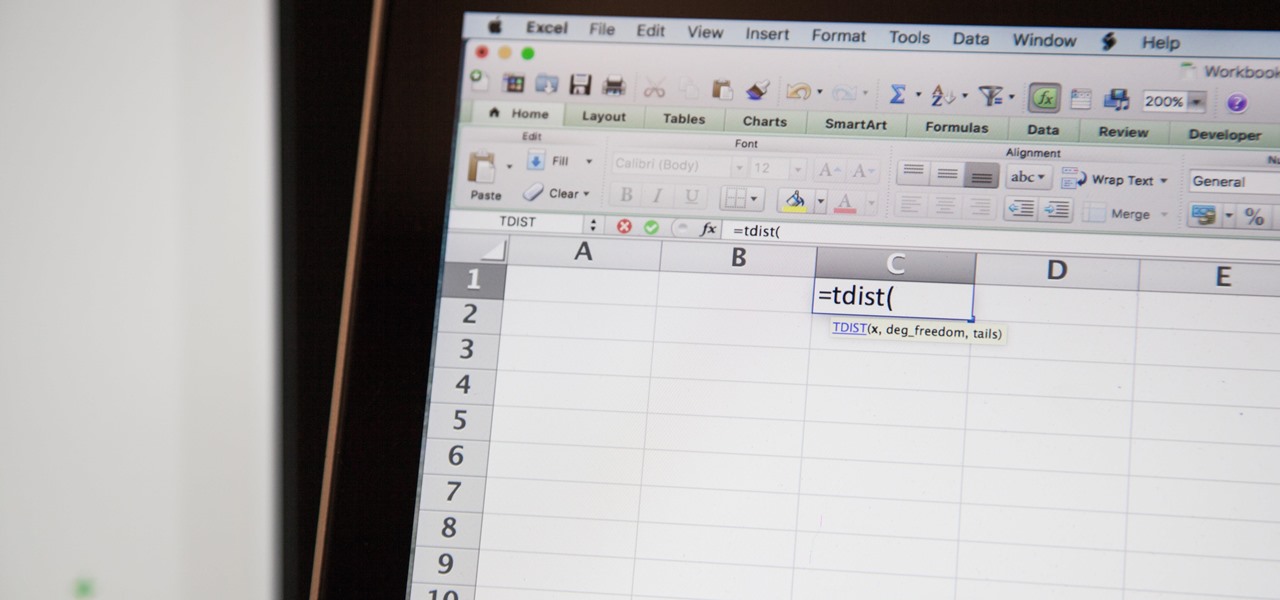
So you need to find the p-value for your hypothesis test. To do so, employ the spreadsheet program Microsoft Excel. Using a simple formula, you can easily determine the p-value for your tests and thereby conclude strong or weak support of the null hypothesis.

Hello, everyone. If you've been following my recent articles, you'll know that I've been rather busy lately working on a project, a rather large one. I've been working with Pheonix750 and Ciuffy to build the Null Byte suite of tools! I got the green light from our admin a while ago, and we've been developing like mad ever since! I'm very excited to launch this project. So, let's start by explaining what it is...

Welcome back, my neophyte hackers! In previous tutorials, we learned how to steal system tokens that we could use to access resources, how to use hashdump to pull password hashes from a local system, and how to grab password hashes from a local system and crack them.

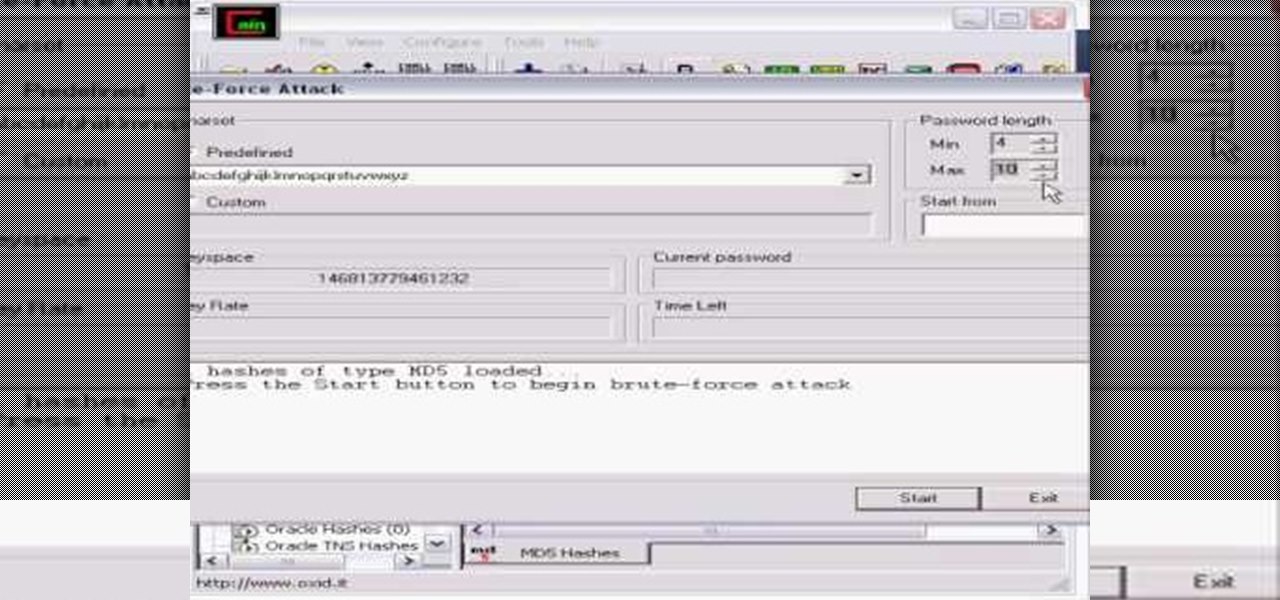
Welcome back, my eager hackers! In recent blogs, I've demonstrated how to grab password hashes remotely using Metasploit's meterpreter and pwdump. Once we have the Windows passwords from the SAM file, we can then crack these hashes using tools such as Cain and Abel.

Just like the title says, learn how to crack a master lock. Not pick the lock (picking a master lock will not get you the combo). You don't need any special tools to crack this master lock- all you need is the right technique. Crack master locks for fun only - don't use this for illegal purposes. Great trick if you lose your combination to your master lock. All you need is a little math. Learn how to hack a master lock with this lock cracking tutorial.

Oil is vital to maintaining the health of your engine, but if it's leaving the areas of the car where it's needed it can cause major damage. Watch this video to learn how to diagnose whether a misfire is being caused by a cracked cylinder head or leaking head gasket allowing oil to enter your coolant and spark plugs.

Great news if you're looking to upgrade to either the S10e, S10, or S10+. Samsung has a trade-in program that's offering potentially massive discounts of up to $550 if you preorder one of their flagships right now — but only for certain phones.

Cracking the password for WPA2 networks has been roughly the same for many years, but a newer attack requires less interaction and info than previous techniques and has the added advantage of being able to target access points with no one connected. The latest attack against the PMKID uses Hashcat to crack WPA passwords and allows hackers to find networks with weak passwords more easily.

Leaked databases get passed around the internet and no one seems to notice. We've become desensitized to the data breaches that occur on a daily basis because it happens so frequently. Join me as I illustrate why reusing passwords across multiple websites is a truly awful practice — and compromise hundreds of social media accounts in the process.

It seemed appropriate that we announce the winner of the first White Hat Award for Technical Excellence on the Academy Awards weekend. This is, in essence, our "Oscar" here at Null Byte. Remember, this contest began on January 4th, 2016 and just recently closed on February 15th. In this contest, I was looking for:

Welcome back, my greenhorn hackers, and happy New Year! Now that your heads have recovered from your New Year's Eve regaling, I'd like to grab your attention for just a moment to preview 2015 here at Null Byte. I hope you will add your comments as to what you would like to see, and I'll try to honor as many requests as I can.

In this video, we learn how to repair small cracks in wood projects with Bob Schmidt. Even though the cracks are small, they may catch your eye when you walk into the room. You can minimize this with just a little bit of work with a screwdriver. First, grab your screwdriver and rub the middle of it on the corner of two pieces of wood. This will rub out the two pieces without changing the stain on the wood. If you have a missing crack on baseboard, you can do the same thing, which will lessen ...

How to spackle a crack or a hole

Whatever your reasons for doing it, if you are trying to hack passwords, it helps to have the right software for getting the job done. With the Cain and Abel program, you will be well on your way to hacking even the toughest personal passwords.

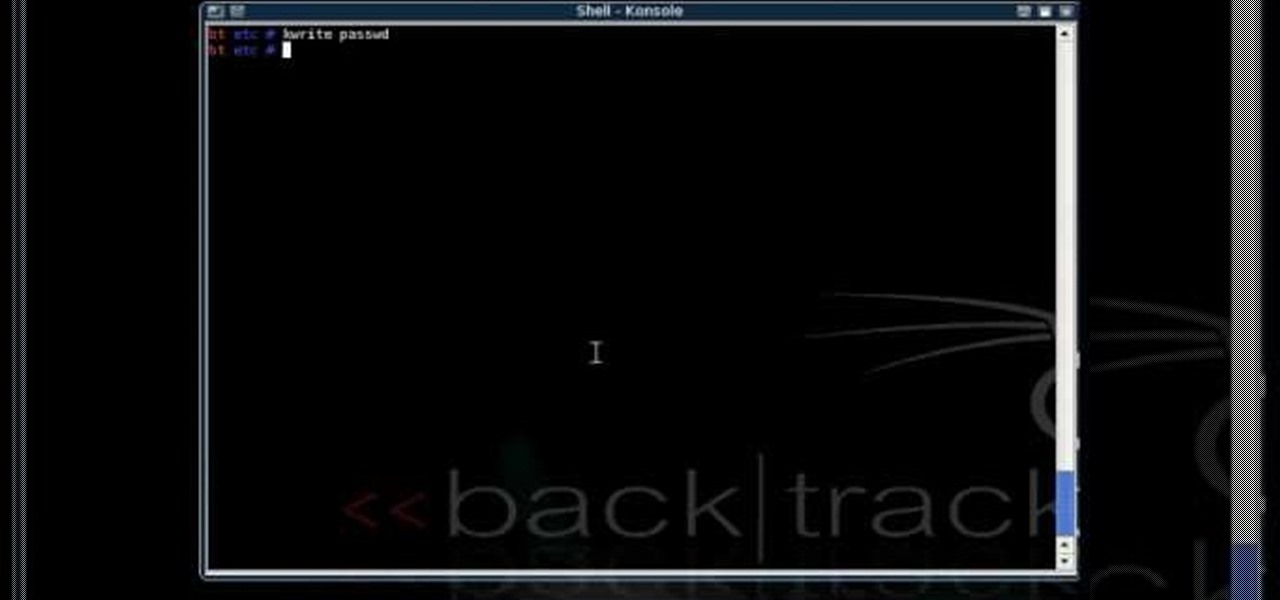
This is a great tutorial on how to use Backtrack 2 to crack a local computer for access. You can either completely change the password or you can wipe it and restore the password so nobody knows you were there

Learn how to crack and separate an egg.

This video from the website What to Cook When shows us how to crack open the crab legs and get the meat out of them. Firstly starting with the cluster of legs, simply grab one of the legs and break it off of the cluster. Now simply grab the leg and starting with the joint, break it into half and pull it apart. Then take the middle section which you just broke and put your fingers right in the middle of that section, crack that one leg and then flip it over and crack it the other way. And once...

Doug Jenkins tells you what signs to look for if you think you might have a cracked head. Does the antifreeze level go down too fast? Notice anything unusual about the oil color or hose pressure? Check all of the warning signs first, because actually getting to the cylinder head is a very complicated process, which involves removing everything from the v-belt and ac compressor to the intake manifold and headers.

Password cracking is a specialty of some hackers, and it's often thought that raw computing power trumps everything else. That is true in some cases, but sometimes it's more about the wordlist. Making a custom, targeted wordlist can cut down cracking time considerably, and Wordlister can help with that.

There are many password-cracking tools out there, but one of the mainstays has always been John the Ripper. It's a powerful piece of software that can be configured and used in many different ways. Metasploit actually contains a little-known module version of JTR that can be used to quickly crack weak passwords, so let's explore it in an attempt to save precious time and effort.

Hashes are commonly used to store sensitive information like credentials to avoid storing them in plaintext. With tools like Hashcat, it's possible to crack these hashes, but only if we know the algorithm used to generate the hash. Using a tool called hash-identifier, we can easily fingerprint any hashes to discover the right Hashcat mode to use to retrieve a password.

Hello readers, and welcome to Null Byte. Before we start, for those of you who may not know me, my name is ghost_; I'm a relatively active member of our community and have been around for a while.

In this clip, learn how to create a camera controller using nulls and user data. This makes animating a camera in a scene much easier. Whether you're new to MAXON's popular 3D modeling application or are just looking to get better acquainted with Cinema 4D and its various features and functions, you're sure to enjoy this free video software tutorial. For more information, and to get started using this trick in your own Cinema 4D projects, watch this 3D modeler's guide.

Learn how to install cracked apps straight from your Apple iPhone. Enjoy cracked apps without even touching your computer. You must add this source to your Cydia if you do not hav it: