This video in the Software category will show you how to create a real cool manipulated globe in Photoshop. You will combine a few images and distort one of them to create a 3D image of a globe. There are 3 components; the background, a hand and an image globe. First open the background image. Then open the hand image, copy and paste it over the background, resize and position it correctly. Now open the third image, choose the elliptical marquee key, draw a circle and copy and paste it over t...
NBC News has fired the producer it deemed most responsible for the airing of a selectively edited 911 call placed by George Zimmerman the night he killed Trayvon Martin.

LiveType ships with many sophisticated design elements so that you can add movement to your static text. You can access them in the media browser. Choosing, editing, applying, and previewing an effect is easy using the media browser and canvas. Live fonts are as easily manipulated as effects. Explore textures as well to make your titles professional and sophisticated.

Brass stampings add that perfect metallic touch to any jewelry project you're working on. While brass stampings are usually made into filigree shapes, they can also be manipulated into pretty floral designs.

The drawing tools in flash aren't always the most intuitive to newcomers. In this tutorial, Ralf will show you how to use the basic drawing tools in flash. You learn the difference between Merge Shapes and Drawn Objects, which are all shapes of the same look and feel with the exception that one can be more easily manipulated and the other. You'll learn how to use this selection and sub selection tools to select various objects on the flash stage. You also see how to use the oval and rectangle...
Quartz Composer is a Mac program that helps you manipulated motion capture video, and you can hack your Xbox Kinect to send motion captured data to your Mac OSX. This tutorial shows you precisely how you can use the Kinect tools to pull this off!

The great thing about paper, is the way it can move and be manipulated to create awesome looking shapes and designs. Origami can take a simple piece of paper and with a few folds here and there, and then you get a beautiful piece of art. This tutorial focuses on how to fold an origami rose from scratch. Enjoy!

Bert shows us how to utilize Photoshop's warp tool to manipulated images. Download the sample files and play along with Bert as he shows you how to use the warp tool in Photoshop.

This video tutorial will show you how to create a very cute envelope holder. This envelope is great for holding cards and candy on special occasions. Your family and friends will surely enjoy this cute and manipulated piece of paper.

Learn how money and number tricks are manipulated by a magician pro - the art of change racing.

This tutorial video will show you what the purpose of compression is and how compression works through its parameters. Your instructor illustrates a drum beat and a plucked guitar line. Beginning with how to compress the drum beat, take (download) a drum sound pack without compression and to add compression using the software right click on the drum machine, choose create, and then choose combo on compressor. The virtual compressor has all the dials and adjusters found on any basic compressor...

Follow these simple instructions from Zeevideo to clean the track ball on the RIM BlackBerry Tour 9630 device. Using two simple items: a clean sheet of paper and a pair of scissors can clear most of your track ball issues. The BlackBerry Tour 9630 dose not have a removable track ball unit so to clean the trackball cut a small piece of paper that can be use to manure under the inset of the trackball, using your thumb move the trackball to the side allowing just enough space to slid the slip of...

A short video dedicated to the DNA Phantom Effect and how it might be related to human emotion. The DNA Phantom Effect is a questionable discovery by Russian scientist and "father of Wave Genetics", Peter P. Gariaev. In 1985 the very first evidential proofs of DNA being able to maintain wave/field type memory were found. That same year, the "DNA Phantom Effect" was given its name after observations made by Gariaev stated that physical DNA somehow attracted and manipulated light in a vacuum ch...

This Lynda tutorial teaches how to use the Logic pro, a songwriting application. Midi sequencing and quantizing is the main focus of this video. Midi is a short name for Musical instrumental digital interface. Midi is not sound. It is a low resolution computer protocol, developed in early 80’s to enable computer to communicate each other. Midi is fast, simple and reliable. It has a intensity stream. In this project, Scot Hirsch explained how a midi file is manipulated in Logic pro. Midi file ...

Watch this instructional magic card trick tutorial to learn how to perform the binary routine. This is an original series of user-created moves. There are 9 phases of the Binary Routine, 6 of which are false, and the other 3 are closers that involve a color card change at the end. This video provides instruction on 2 false cuts and 1 closer, along with some possible variations. Just keep in mind, there is room for adjustment with these phases. If you find a better way to do a certain move, th...

Suzanne Ivester demonstrates how to cover a glass votive candle holder with stenciled polymer clay and embellish it with rubber stamping and metallic effects. Polymer clay is a highly versatile material and can be manipulated to create various effects for myriad crafting projects. Watch this video crafting tutorial and learn how to make a polymer clay candle holder with an Asian-themed dragon.

An attacker with shell access to a Linux server can manipulate, or perhaps even ruin, anything they have access to. While many more subtle attacks could provide significant value to a hacker, most attacks also leave traces. These traces, of course, can also be manipulated and avoided through methods such as shell scripting.

Any internet user will need to download files eventually, and most simply have faith that what they are downloading is trustworthy. This doesn't give much clarity into the contents of the file, but if the file's author published the original checksum, comparing it to the SHA-256 hash of the downloaded file can ensure nothing was tampered with.

How many times have you thrown out the remaining cardboard tube from an empty roll of toilet paper? Most of the time, they don't even make it to the recycling bin, and with the average American using over 20 rolls each per year, that's over 6.4 trillion tubes being wasted each year. Yet these small tubes are particularly valuable helpers around the home, especially when it comes to cleaning, so why toss them out?

In this web design tutorial, you will learn to modify and create various styled quick shapes using info bar and tool modes. As you follow through future tutorials, you will start to realize how important the info bar is for using the Xara Web Designer software.

Rock, Paper, Scissors is a classic childhood pastime, but some people take it a little more seriously than that. There's the ultimate version, which has 25 gestures instead of the traditional three, and there are even tournaments and championships for those who consider themselves real pros.

Bokeh (which translates to "blur" in Japanese) is a photography technique referring to the blurred areas of a photograph. Basic bokeh photographs often have one point of focus, while the background falls away into a dreamy, blurred haze.

At first, it seemed like a clever art installation housed on the web, but now we're not so sure... the Newstweek hack may indeed be legit.

Apple's macOS operating system is just as vulnerable to attacks as any Windows 10 computer or Android smartphone. Hacker's can embed backdoors, evade antivirus with simple commands, and utilize USB flash drives to completely compromise a MacBook. In this always-updated guide, we'll outline dozens of macOS-specific attacks penetration testers should know about.

During our last adventure into the realm of format string exploitation, we learned how we can manipulate format specifiers to rewrite a program's memory with an arbitrary value. While that's all well and good, arbitrary values are boring. We want to gain full control over the values we write, and today we are going to learn how to do just that.

Though the Microsoft HoloLens' release to the consumer market is still a distant thought at the moment, Ubisoft is preparing for the future with the unveiling of AR video game prototypes.

Stop me if you've heard this one before. You plop a marshmallow down in front of a kid and propose the following: You can eat this marshmallow now, or you can wait twenty minutes and eat two marshmallows. What do you think the kid is going to do? Better still, what do you think you would do? Personally, I'd eat the first marshmallow without hesitation. But now we're getting off track ...

360world, a Hungary-based tech company involved in motion control and augmented reality, released information today about their latest products, the CLAIRITY HoloTower and CLAIRITY SmartBinocular. These tools are designed to bring augmented reality into the hands of air traffic controllers, via Windows Mixed Reality, to greatly improve their workflow over tools already in use.

If mainstream media has taught us anything, it's that being beautiful can get you ahead in life. The notion isn't necessarily correct, but it's what the general consensus accepts and it seems to hold quite a bit of weight (no pun intended) in the western world.

As the demand for realistic volumetric video for AR experiences begins to grow (along with the available facilities and services for capturing it), researchers at Google have figured out how to improve upon the format.

Apple is very tight lipped about their products, and their iPhone is certainly no exception, but when products depend on global manufacturing, it's nearly impossible to keep good secrets contained.

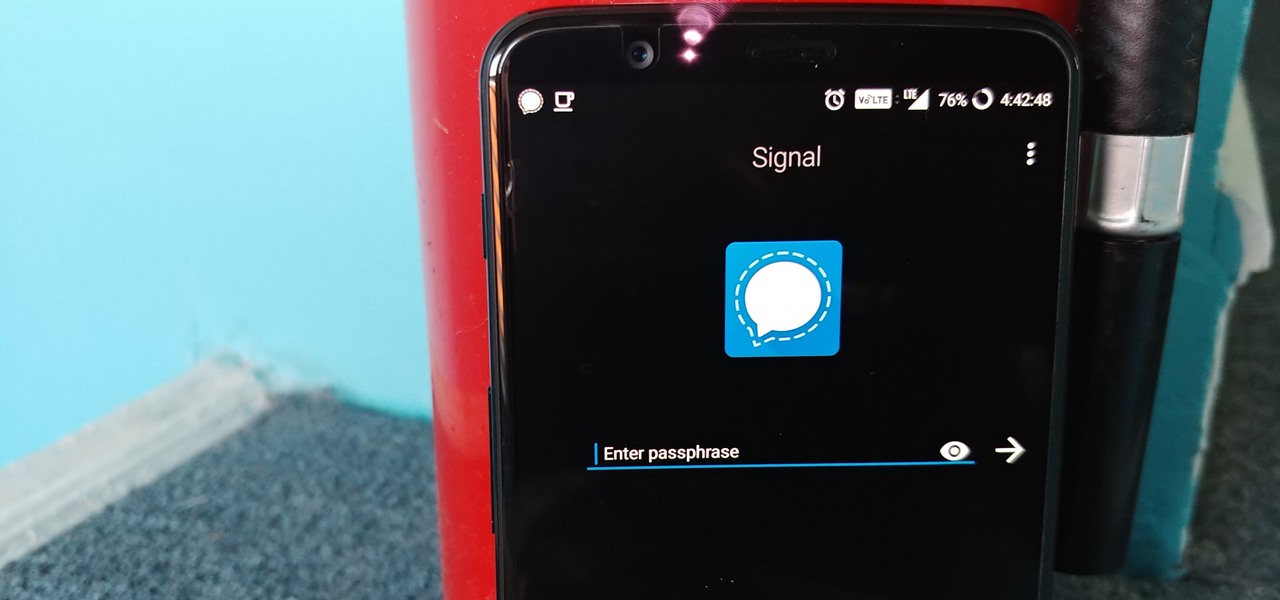
Messaging apps can be a double-edged sword. Not only do they let you interact with other people, but they also let you go back and reminisce on past exchanges. However, that same archive can be used against you in certain situations. Luckily, Signal can be manipulated to remove any record of past messages.

I spent just about my entire weekend trying to break the 800, 900, and 1,000 levels of Instagram — because it's a game, y'all — by playing around with my follower count. I shamelessly manipulated my IG account in such a way that was extremely time consuming and left many of my friends pretty pissed off at me as I spent most of my time glued to my phone. (Sorry, friends. I know I'm obsessed.)

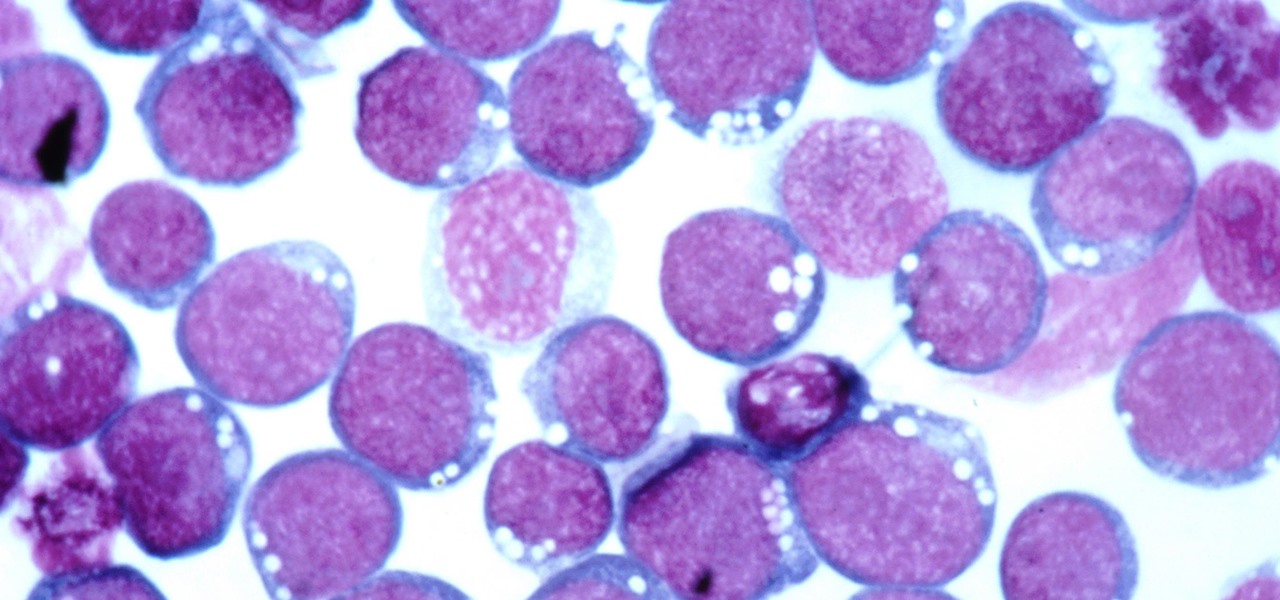
Most of us have already had an encounter with the Epstein-Barr virus, or EBV, for short. As part of the herpes family, it's one of the most common disease-causing viruses in humans. We get the disease with (or without) some nasty symptoms, then we recover. However, EBV stays in our body after the illness has ended, and it's one of the few viruses known to cause cancer.

If you want to appreciate the value of microbes, look no further than a chunk of cheese. Because cheese roughly traces back to the Neolithic Era, we might say the earliest cheesemakers were the first humans to manipulate microbes—without even knowing it. Now, thanks to microbiologists and the long tradition of cheesemaking, we know a lot more about the microbes that make our favorite types of cheese possible.

As many of you know, I have been running a couple of series here on Null Byte about digital forensics called Digital Forensics for the Aspiring Hacker and Digital Forensics Using Kali. Although many readers have seemed to enjoy these series, just as many seem to be pondering, "Why should I study digital forensics?"

Welcome back, my nascent hackers! We have spent a lot of time in previous tutorials focused on hacking the ubiquitous Windows systems, but the vast majority of "heavy iron" around the world are Linux or Unix systems. Linux and Unix dominate the world of Internet web servers with over 60% of the market. In addition, Linux and Unix servers are the operating system of choice for major international corporations (including almost all the major banks) throughout the world.

If you're anything like me, every time you travel you end up in a desperate panic for a decent W-Fi connection. Whether you want to post your photos, research the best beaches, or kill time during an overnight layover, a hotel's Wi-Fi quality is of paramount significance in making a reservation.

Once a hacker has created a PowerShell payload to evade antivirus software and set up msfconsole on their attack system, they can then move onto disguising their executable to make it appear as a regular text file. This is how they will get a Windows 10 users to actually open the payload without knowing they are doing so.

One of the oldest electronic musical instruments is the theremin, a synthesizer that generates sound based on hand gestures, as featured in the classic "Good Vibrations" by the Beach Boys.