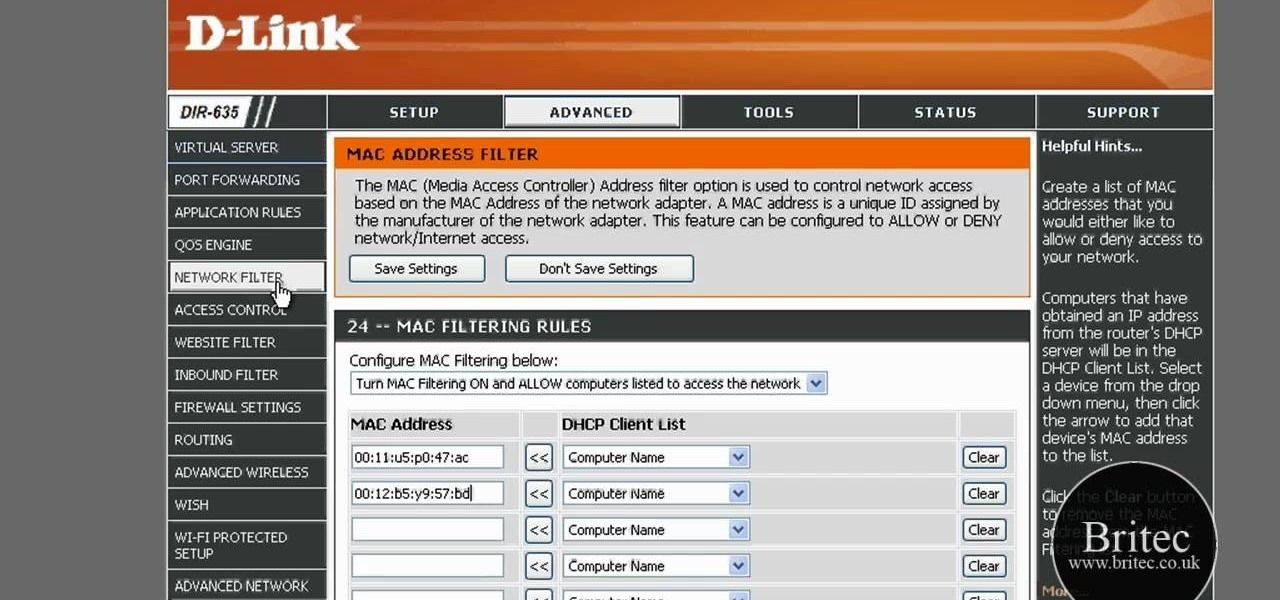
After finding and monitoring nearby wireless access points and devices connected to them, hackers can use this information to bypass some types of security, like the kind used for Wi-Fi hotspots in coffee shops, hotels, and in flights high above the ground. By swapping their MAC address for that of someone already connected, a hacker can bypass the MAC filter and connect freely.

MAC addresses (not to be confused with Macs) are unique identifiers assigned to network devices in order to access the internet. Hotels use these Mac addresses in order to check if a registered patron has agreed to their terms and conditions, how much bandwidth is being consumed, and of course, whether they've paid or not.

The Lab Rats, Andy Walker and Sean Carruthers, explain Media Access Control (MAC) addresses. Filtering MAC addresses allow you to very specifically control access to your wireless network.
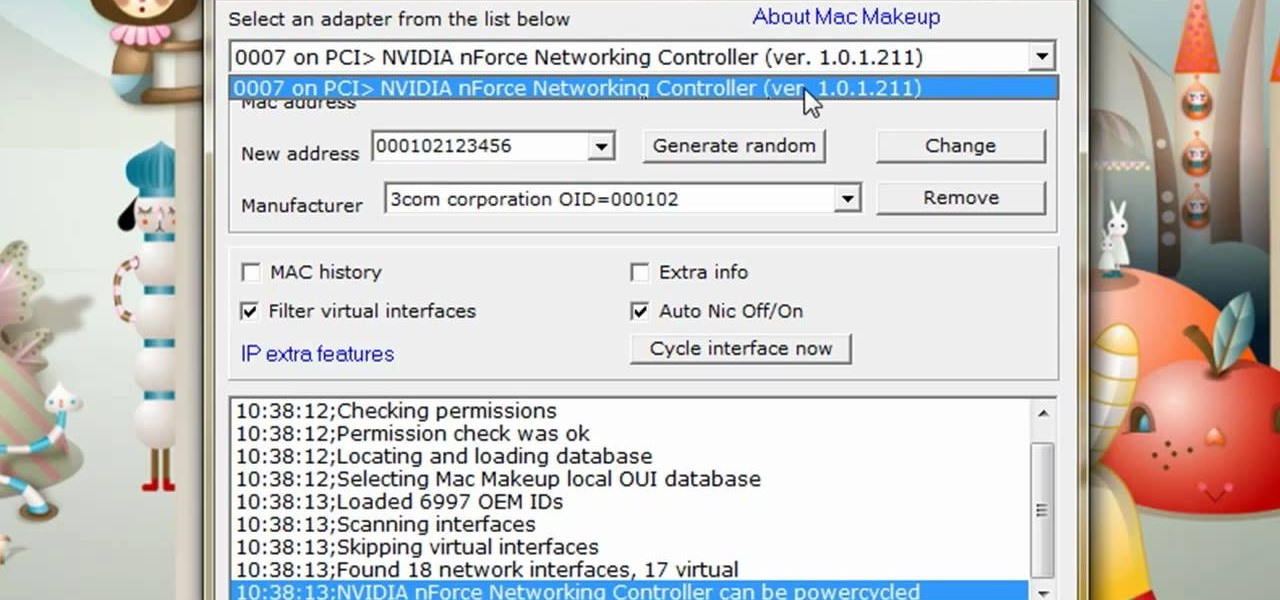
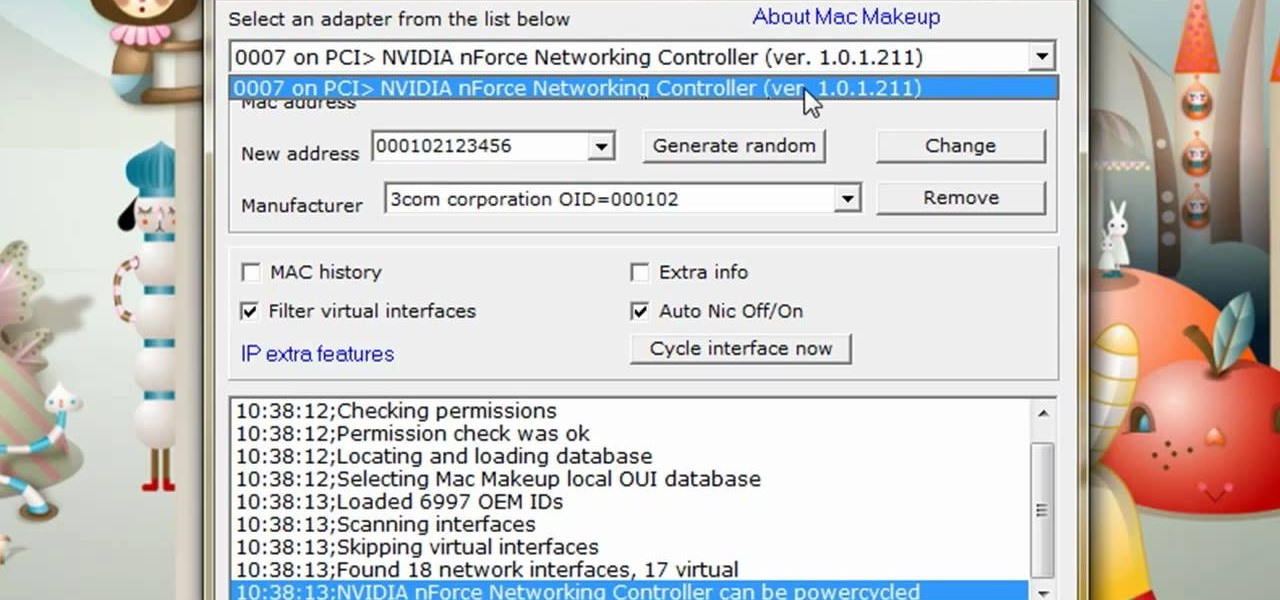
The video is about how to change the IP address. MAC address is the unique identifier a site of the most network adapters. MAC address is used to determine what IP address the computer will have and one way to change the IP address is by changing the MAC address. The method is only applicable for the windows systems and for the MAC systems you need to look at the link provided. In Windows in the start menu, type cmd in the run/search box, which will launch the command window. Type ipconfig/al...
In this tutorial, we learn how to quickly find your MAC address. This is the address that identifies your computer on a network. When you go to a campus, you will need to register your computer with a resnet so you can access the internet. To find the address, you will head to the Apple menu, then click 'about this MAC'. Click on the 'more' button and then click on 'network' and 'built in Ethernet'. This is the MAC address that you will need to register your computer, you may have a few of th...
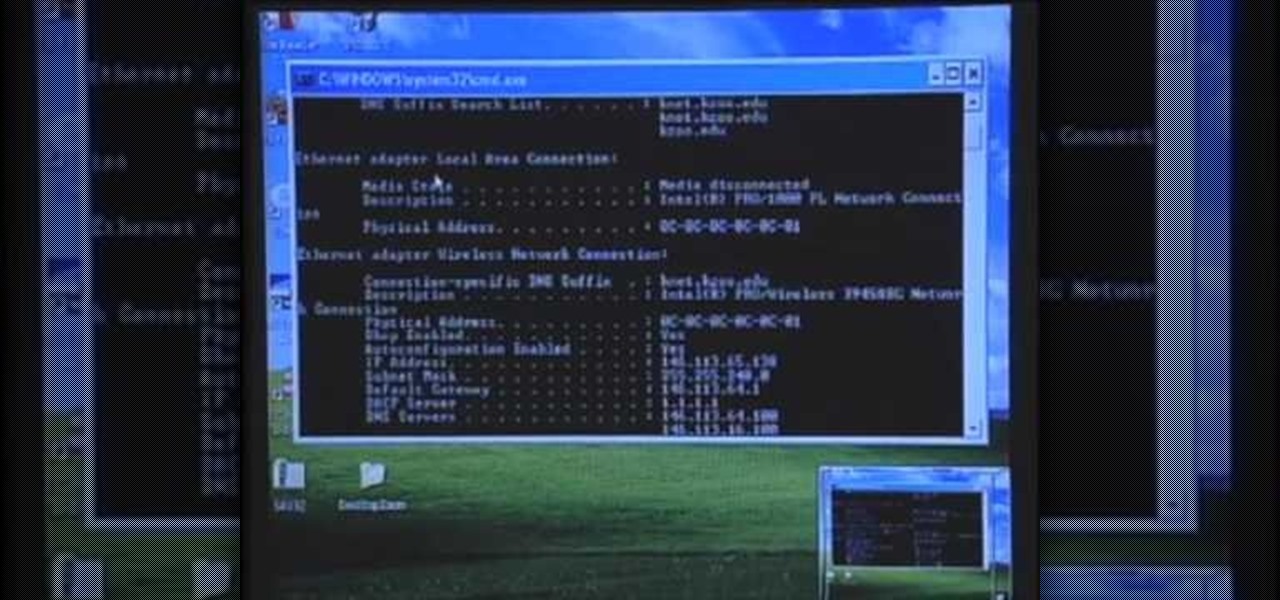
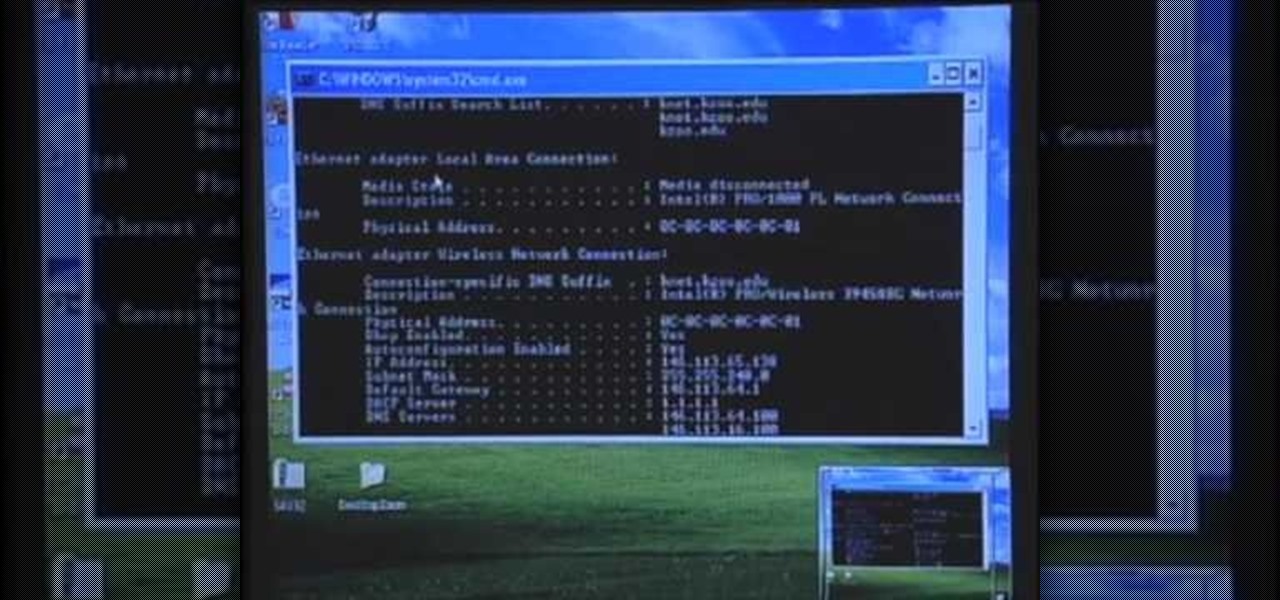
In this video Guides4tech teaches the secrets of finding your local IP and MAC address in simple steps. First click 'Start' and select 'Run' on your computer. Now type 'cmd' to open the command prompt. In the command prompt type 'ipconfig/all' and press 'Enter'. Your IP address will displayed under the 'Ethernet adapter local area connection' menu. Your MAC address will be displayed as 'Physical address' under the same menu.

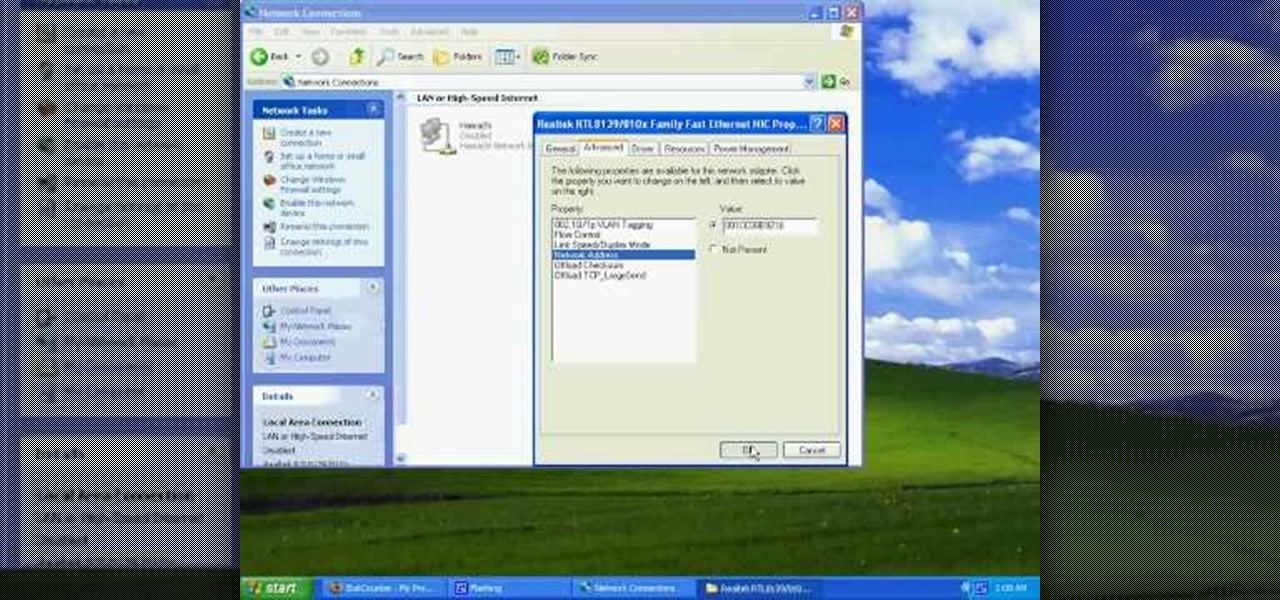
This video tutorial from tarunkumarsinghal shows how to change Mac address on Windows XP. Click Start menu and then Control Panel. Make sure control panel window is in classic view mode. If not, change it to classic from the left pane.

In this video tutorial, viewers learn how to find their computer's MAC (or physical) address in a Windows computer. This task is very easy, simple and fast to do. Begin by clicking on the Start menu and open the Run program. Then type "cmd" in the Run box and press OK. When the black command prompt opens, type in "ipconfig /all" and press Enter. The computer's MAC address will be listed as Physical Address under Wireless Network Connection. This video will benefit those viewers who use a Wind...

In this tutorial, we learn how to import Facebook profile pictures into the Address Book on an Apple computer running the Mac OS X operating system. It's an easy process and this video presents a complete guide. For more information, including a full demonstration and detailed, step-by-step instructions, watch this helpful home-computing how-to.

How to Use Your Mac as a Server: Turn your Mac Mini into a server! Yes, that's right, with a little know-how and a little spunk, you can turn an inexpensive Mac Mini computer into a server to provide services over you network. You won't even need the Mac OS X Server, just the Mac OS X Client, so there is no extra software to buy, just the Mac Mini and it's operating system.

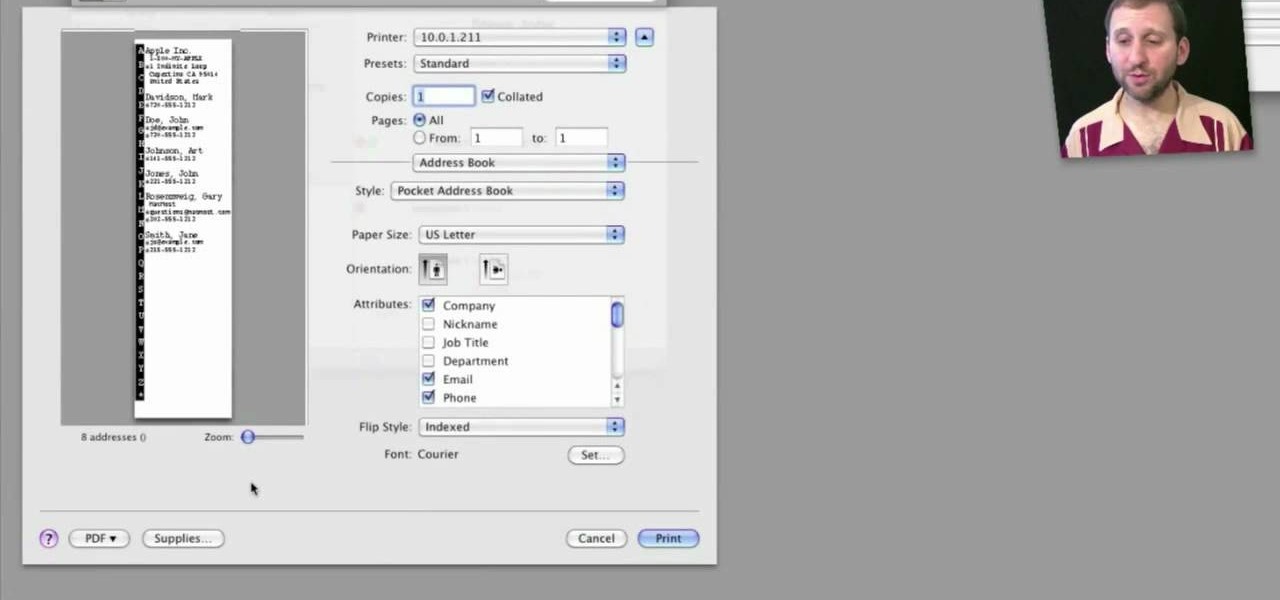
Looking for a quick primer on how to print from Address Book on a Mac OS X computer? It's easy! So easy, in fact, that this home-computing how-to from the folks at MacMost can present a complete overview of the process in just over three. For more information, including step-by-step instructions, take a look.

In this clip, you'll learn how to reinstall an accidentally-deleted system application like TextEdit, Preview, iCal, Address Book or QuickTime without reinstalling OS X. With a little know-how, it's easy. So easy, in fact, that this video guide can offer a complete overview of the process in a matter of a few minutes. For more information, including a complete demonstration and detailed, step-by-step instructions, watch this home-computing how-to from MacMost.

The days of Skype 2.8 for Mac are over! Mac users can now rejoice and make calls with ease using the new beta version: Skype 5.0 for Mac OS X (available here). It was well worth the wait, with a revamped look and feel that simplifies navigation and provides a more Mac-like experience.

If you're like most people running Mac OS X, you've got quite a large number of entries in your Apple Address Book. In this how-to, you'll find instructions for organizing your addresses into groups for easy access in Address Book, other applications, and even sync devices such as other Macs, iPods and iPhones. For more on using groups in Apple Address Book for Mac OS X, watch this video tutorial.

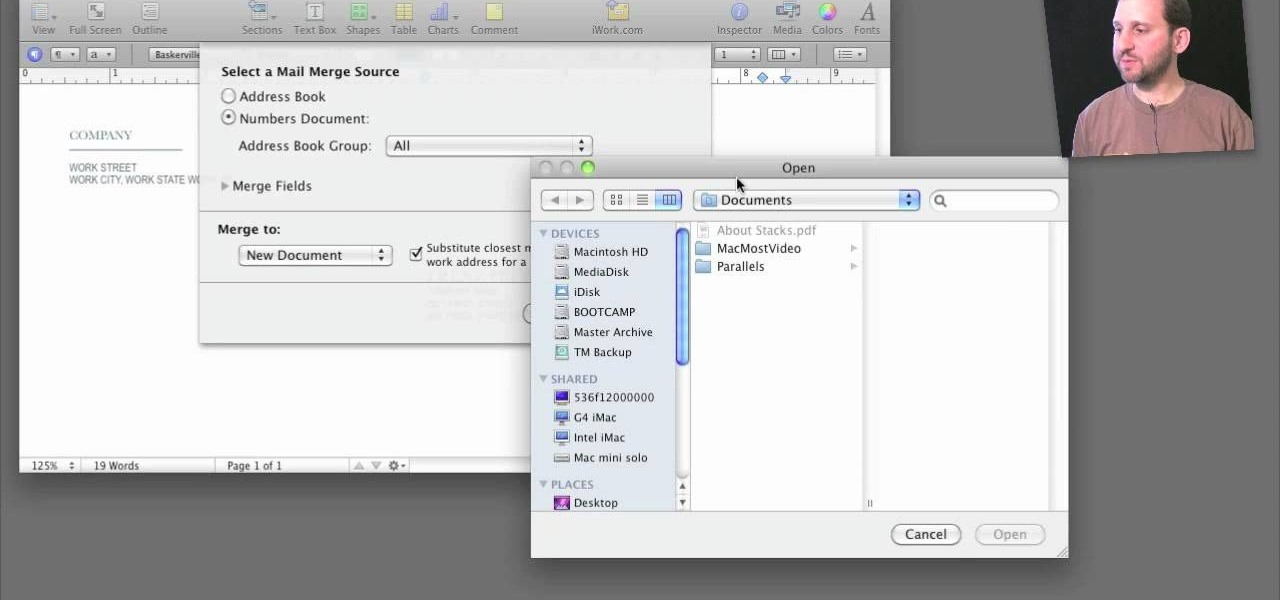
A step-by-step guide that will walk you through Mail Merge on a Mac computer. You will gain how to prep and print envelopes, letters or any document that you need to send to different names and addresses on each item. You can pull the data from your address book or from a Numbers Spreadsheet and will see how to modify and merge the information you will need to successfully set up your documents.

Your IP address is what identifies your personal computer while you are online. You may want to change your IP address for privacy, to bypass website settings, to download, or for various other reasons. This tutorial will take you through the steps you need to start surfing more anonymously.

WPA-secured wireless networks, or WiFI Protected Access, is a form of internet security that secures your wireless LAN from being accessed by unauthorized users. Safer than WEP, or wireless equivalent privacy, WPA still has weaknesses that are prone to cracking - IF, that is, you know what you're doing.

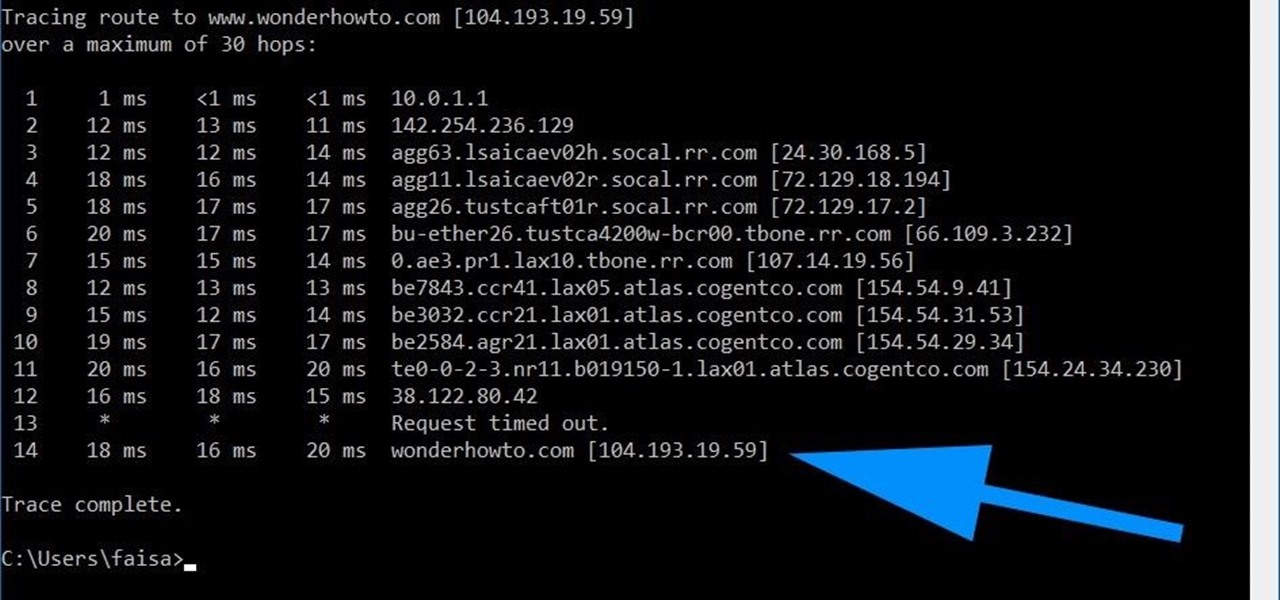
Using a simple trace trick, you can easily look up the IP address and its location for any website. This method uses a command line command to first find the IP address of a given website, and then uses a free online tool to get that IP's location.

In most cases, when the free trial of software is over, that's it—you're left to either pay for it or find an alternative. But what happens if the trial wasn't long enough to sell you on the product? It'd be nice if there was a way to test it out again without having to whip out your credit card.

How to Use Your Mac as a Server: Turn your Mac Mini into a server! Yes, that's right, with a little know-how and a little spunk, you can turn an inexpensive Mac Mini computer into a server to provide services over you network. You won't even need the Mac OS X Server, just the Mac OS X Client, so there is no extra software to buy, just the Mac Mini and it's operating system.

Smartphones and other Wi-Fi enabled devices send radio signals called probe frames to locate nearby wireless networks, which makes them easy to track by listening for their unique MAC address. To show how this kind of tracking works, we can program a NodeMCU in Arduino to sniff the air for packets from any device we want to track, turning on an LED when it's detected nearby.

In general, hacking and information security is not just one discipline, but a number of them, and today we will look into some of the networking concepts.

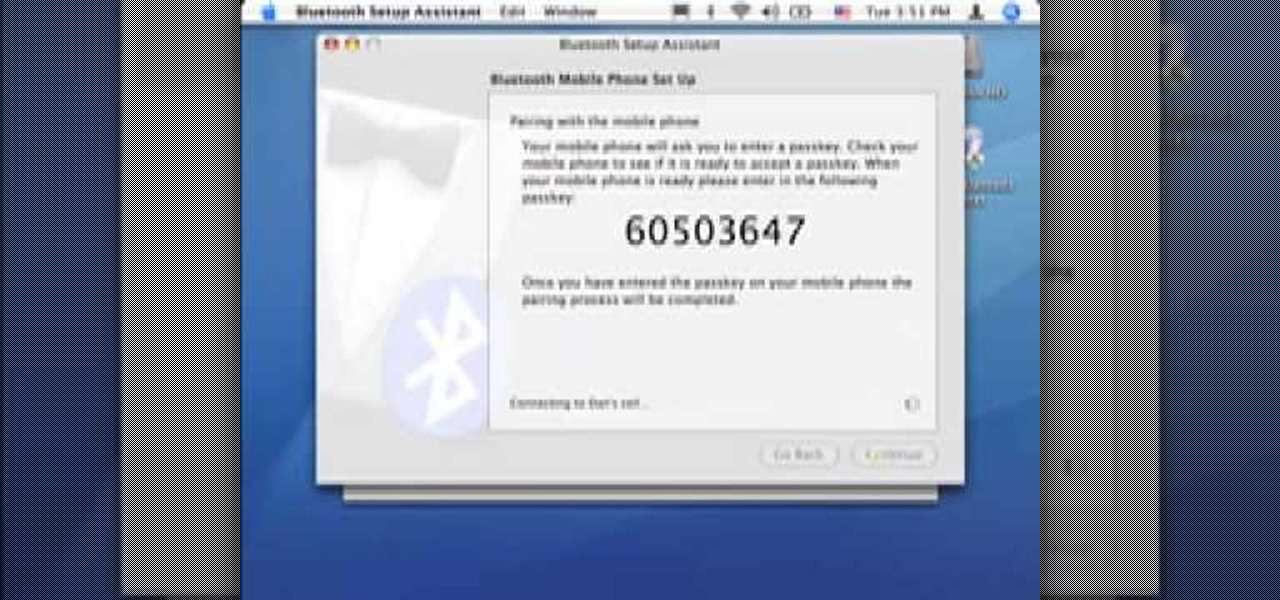
Did you know you can sync up your cell phone (any cell phone with Bluetooth) with your MAC computer? Doing so will enable you to do several things, including importing and syncing your address book, iCal (calender application), and even tethering your phone with your computer so you can get internet.

When joining a new network, computers use the Address Resolution Protocol to discover the MAC address of other devices on the same network. A hacker can take advantage of ARP messages to silently discover the MAC and IP address of network devices or actively scan the network with spoofed ARP requests.

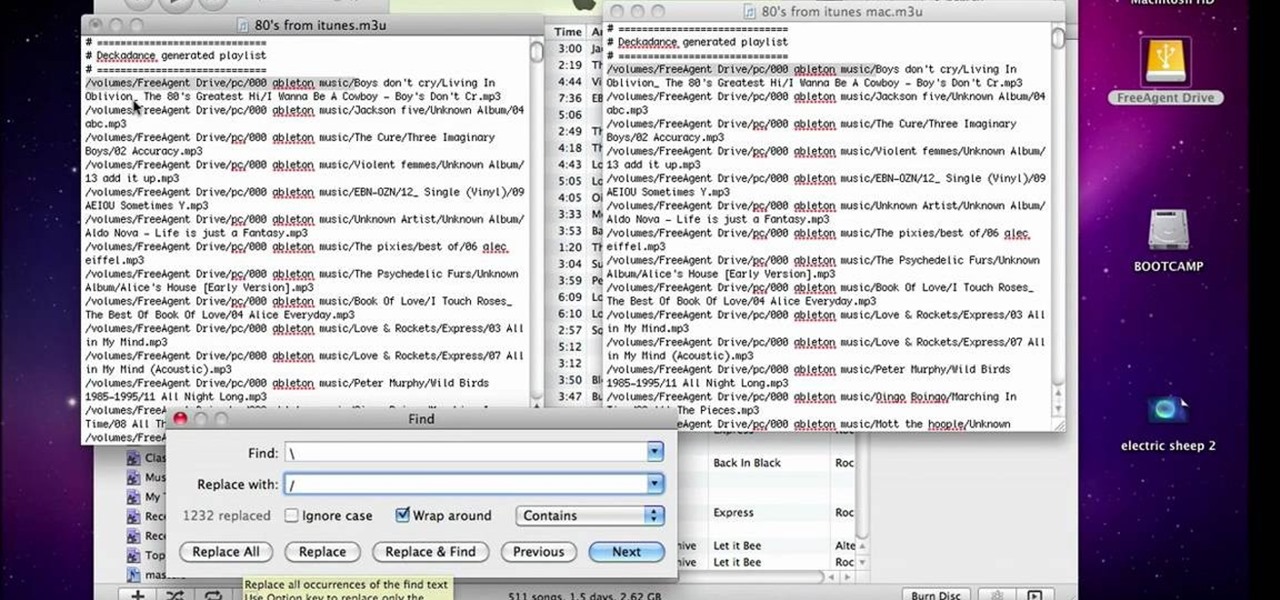
This video will show people who are switching from a PC to a Mac how to move your iTunes playlists to your new computer. From your PC, you should go to the File tab of iTunes and go to your library, choosing "Export Playlist". Next, go to your Mac and select the "Import Playlist" option on the drop down menu. On your Mac, open the file for the PC playlist and use the "Find" option from the Edit menu in order to replace the parts of the address which are different from that of the format which...

Check out this informative video tutorial from Apple on how to organize your Mail in Mac OS X's Mail. See how to sort messages with rules, create smart mailboxes, and comlpletely organize your mail. Mac OS X. It's what makes a Mac a Mac.

Check out this informative video tutorial from Apple on how to use the basics of Mac OS X Mail. See how to set up mail with your email accounts, compose messages, add attachments, view attachments with Quick Look, and search through Mail. Mac OS X. It's what makes a Mac a Mac.

Have you recently switched to an Apple computer? This video how-to demonstrates three helpful techniques to make your transition from PC to Mac as smooth as possible. Specifically, this tutorial addresses workflow management and keyboard shortcuts. For more information, as well as to get started acclimating to your new operating system, take a look at this OS X tutorial.

Check out this informative video tutorial from Apple on how to use Mac OS X Mail to its fullest. See how to filter out junk mail, use data detectors, and view RSS feeds in Mail. Mac OS X. It's what makes a Mac a Mac.

If you use Apple's email services and the "From:" field in your iPhone's Mail app is cluttered with @Mac.com, @Me.com, and @iCloud.com variations of the same address — along with third-party accounts — there's an easy way to declutter things and hide the addresses you don't use anymore.

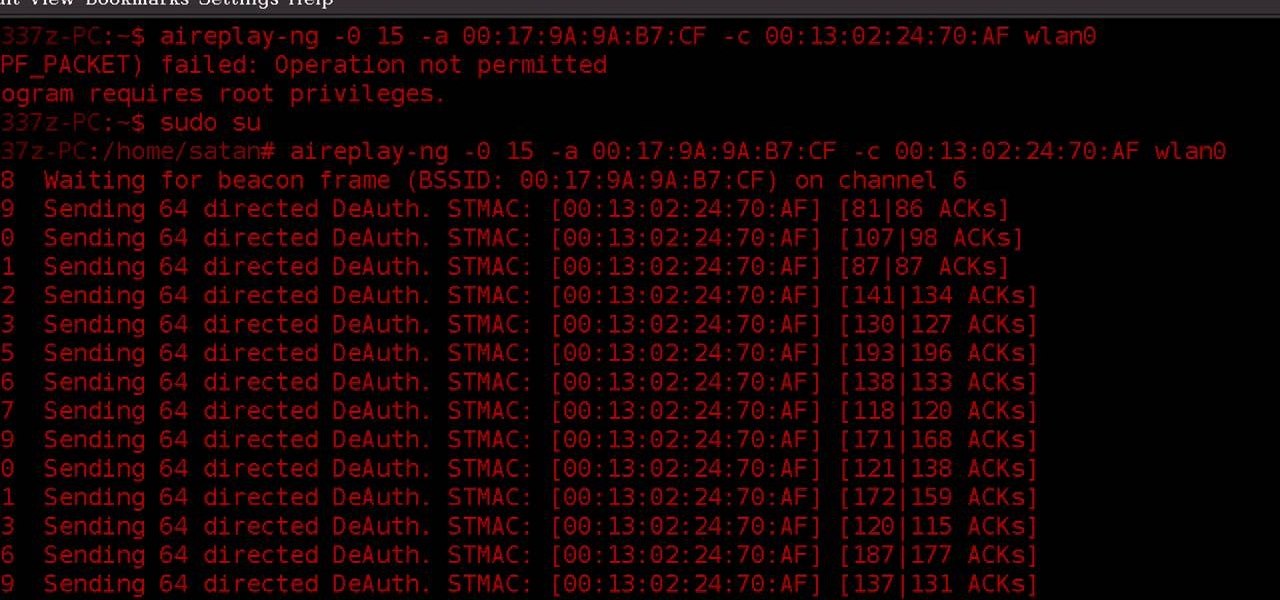
Good day people, today we will examine some basic, for some people well-known attacks, also we will take a look at some advanced attacks.

Learn how to change your IP address using a Linksys router in simple steps. First search for your IP address in the internet and find it from any of the websites available. Now go to your Linksys setup page by accessing it with your username and password. Go to Mac address code and change the last set of digits by increasing or decreasing a value. Now save the settings and reset your modem and router. Finally check your new address to finish.

In this tutorial, we learn how to detect all computers connected to your Wi-Fi network. To begin, go to the website, http://msdn.microsoft.com/en-gb/netframework/aa569263.aspx. Once you are on this site, download and install the program. Once it's installed, open the program and then look for the MAC address. Once you find this, go back to the website and enter this into the MAC address line. After you do this, you will be able to see what computers are listed on your network. If you see any ...

If you read my article on the OSI model, you got a good overview on communications from that model's perspective, but how does that relate to TCP/IP? We're going to take it a step further, getting into the idea behind the two address concept. How does an IP address and a MAC address work together? If you want to hijack sessions and all sorts of lulz like that, you need to understand these concepts. Let's get into it, mates!

The video provides you two easy ways to get onto MySpace at school. There is no need to install anything at all. If you have a Windows operation system, open a command prompt window and just ping MySpace. Then copy and paste the IP addresses you found directly into your browser's address bar. In case you have a Mac computer, try search 'ip address finder' on Google and tool sites such as ip-address.com can help you find the same information. Now getting onto your favorite MySpace will never b...
Greetings null-bytians. Say you have been able to penetrate your neighbour's AP, and of course you had spoofed your MAC address. Now you go on and test to see with excitement if the password really works and the MAC is still spoofed. You login successfully and you browse the web forgetting to check what your current MAC is. Well, if you may do an ifconfig command, you will see that your permanent MAC is being used. Oh!! and guess what, ... your real MAC has been logged. Even though there is t...

Last weekend, some unlucky Gmail users inadvertently had their email accounts wiped out. Actually, it was 0.02 percent of all Gmail users—or roughly 40,000 of the 200 million who use the email service, due to an "unexpected bug" which affected copies of the data. Gmail does make backup files of everything, so eventually everyone will reclaim their email history. In fact, as of yesterday, Google has successfully restored all information from their backup tapes and has started returning everyon...

An incredible amount of devices use Bluetooth or Bluetooth Low Energy to communicate. These devices rarely have their radios switched off, and in some cases, are deliberately used as trackers for lost items. While Bluetooth devices support MAC address randomization, many manufacturers do not use it, allowing us to use tools like Bettercap to scan for and track Bluetooth devices.

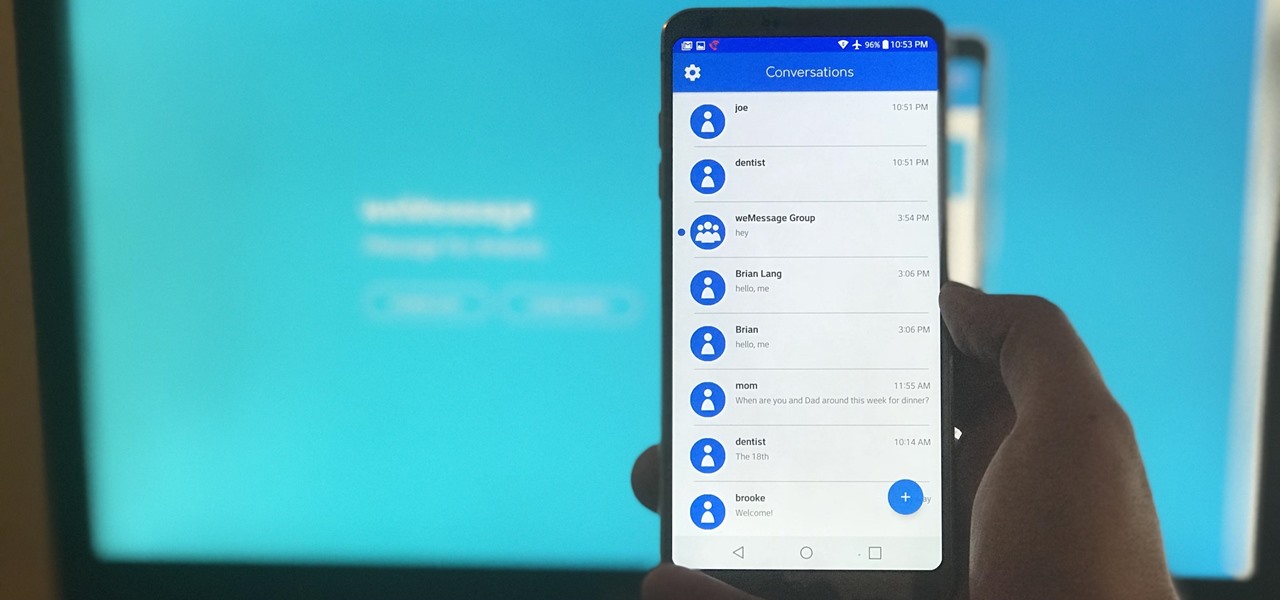
One of Android's most glaring weaknesses is its lack of an iMessage equivalent. That is, of course, until now. There's one app that will allow Android users to experience iMessage on their non-Apple phone, complete with end-to-end encryption, message effects, and group messaging.

Welcome back, my hacker apprentices! My recent posts here in Null Byte have been very technical in nature, so I thought that I'd have a little fun with this one.