How To: Use Call of Duty 4 cracked servers
How to Use COD4 Cracked Servers.

How to Use COD4 Cracked Servers.
WPA-secured wireless networks, or WiFI Protected Access, is a form of internet security that secures your wireless LAN from being accessed by unauthorized users. Safer than WEP, or wireless equivalent privacy, WPA still has weaknesses that are prone to cracking - IF, that is, you know what you're doing.
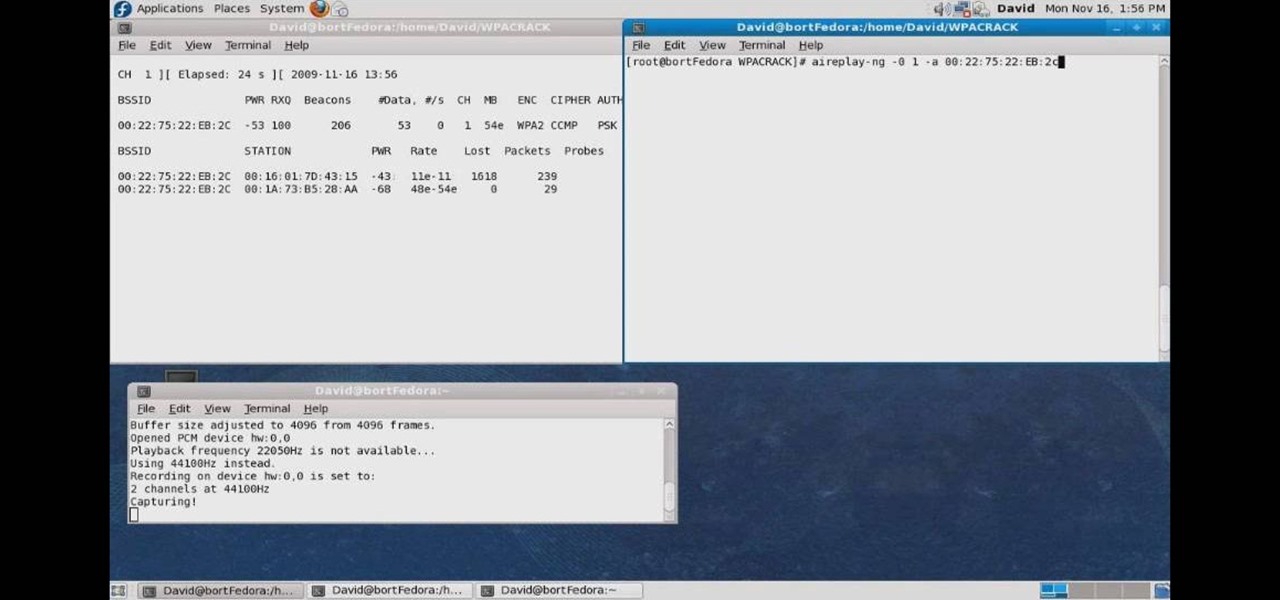
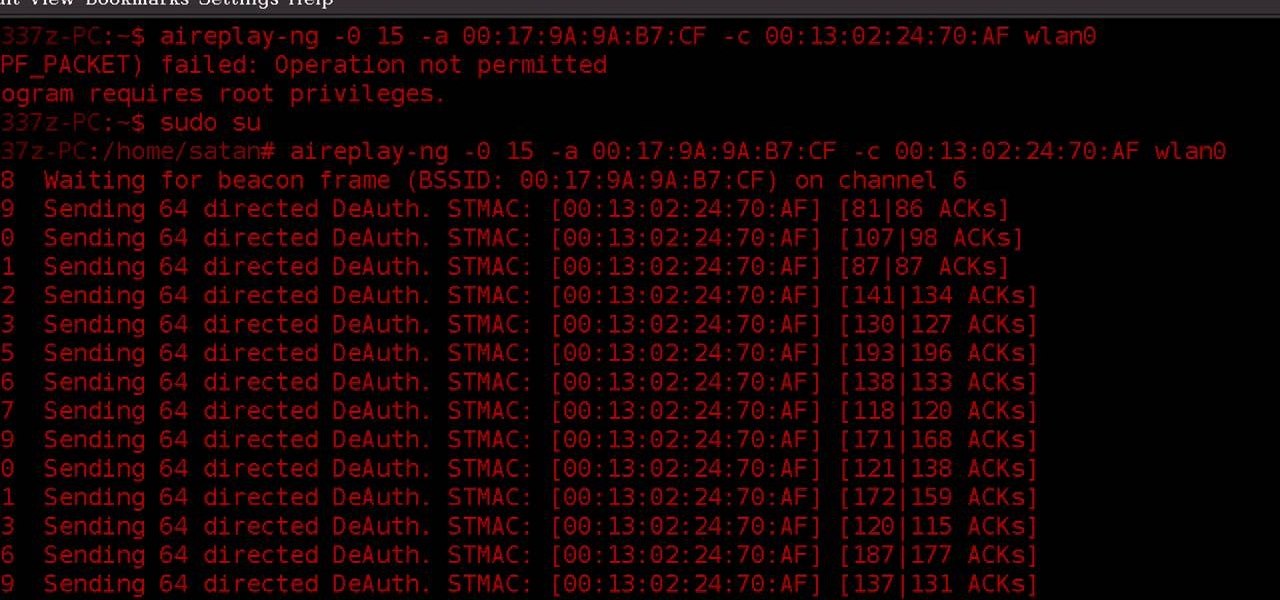
In this how to video, you will learn how to crack a WPA encrypted wireless network. To do this, you will need the Air Crack package for Linux. First, disable the wireless adapter and enable monitor mode. Next, identify the channel in the wireless network and Mac address. Once you have this, you can listen to the traffic coming to and from this point. Wait for the handshake or disconnect something in order to force it to reconnect. From here, you are ready to perform the attack. With any encry...

Sometimes you need a password to gain access to an older running Windows system. Maybe it's a machine in your basement you forgot about or a locked machine that belonged to a disgruntled employee. Maybe you just want to try out your pentesting skills.
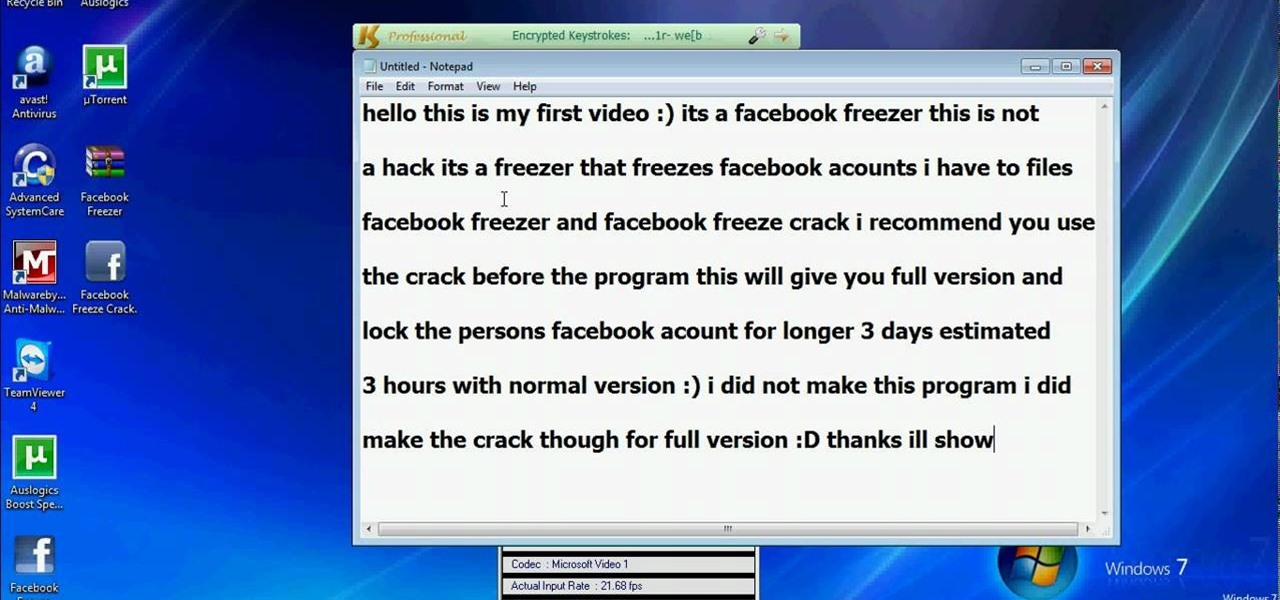
"Facebook is a social utility that connects people with friends and others who work, study and live around them. People use Facebook to keep up with friends, to share links, to share photos and videos of themselves and their friends, and to learn more about the people they meet." -- Facebook

Fixing your Aviso Carbon Fiber surfboard is just as easy as fixing your old poly surfboard. You can remove the drain plug. Dry it out completely. There is no foam to rot or wood to break. If fixed properly Aviso surfboards will keep all of there integrity. This addresses a puncture and a cracked and severely damaged rail.

In this video we learn how to crack WPA using Back Track. The first step is the boot into Back Track using a VMware Virtual Machine Image. Next you need to open a shell console. In the console you will type "airmon-ng" and press enter. This does a check to find the wireless guard interface name. Next, type "airodump-ng wlan0" and press enter. This will tell it what wireless card to use and scan for wireless networks. You are looking for the one that comes up WPA. Copy the MAC address then typ...

Leaked databases get passed around the internet and no one seems to notice. We've become desensitized to the data breaches that occur on a daily basis because it happens so frequently. Join me as I illustrate why reusing passwords across multiple websites is a truly awful practice — and compromise hundreds of social media accounts in the process.

Welcome back, my rookie hackers! When Wi-Fi was first developed and popularized in the late '90s, security was not a major concern. Unlike wired connections, anyone could simply connect to a Wi-Fi access point (AP) and steal bandwidth, or worse—sniff the traffic.

An internet connection has become a basic necessity in our modern lives. Wireless hotspots (commonly known as Wi-Fi) can be found everywhere!

Your driveway is not perfect and over time, can succumb to bothersome cracks that make driving very uncomfortable. They can even make walking harder, and are unsightly. But Lowe's has the solution to fill them up in a hurry— QPR's Pavement Crack Filler.

John White and Rosemary Maddox address garden problems concerning heat and sun damage on their plants. Rosemary grows tomatoes that grow healthily, but are dry and cracked at the top. John identifies the problem as an excessive exposure to heat and sunlight, and recommends putting a netting over the plants to filter and moderate the sunlight. Rosemary also has a similar problem with her roses. The leaves on her rose plants become yellow and brown and eventually die off. John calls it "heat sc...
It's good to know the IP address of your computer. With this information, you can track your computers usage online, and will also know how to change it if you want to surf unnoticed. This tutorial will show you exactly how to find the IP address of your PC, so you will never be lost again. There are a number of programs that require your IP address, for example if you are setting up an external device like an XBox live to your Internet connection, you will need to make sure the IP address is...
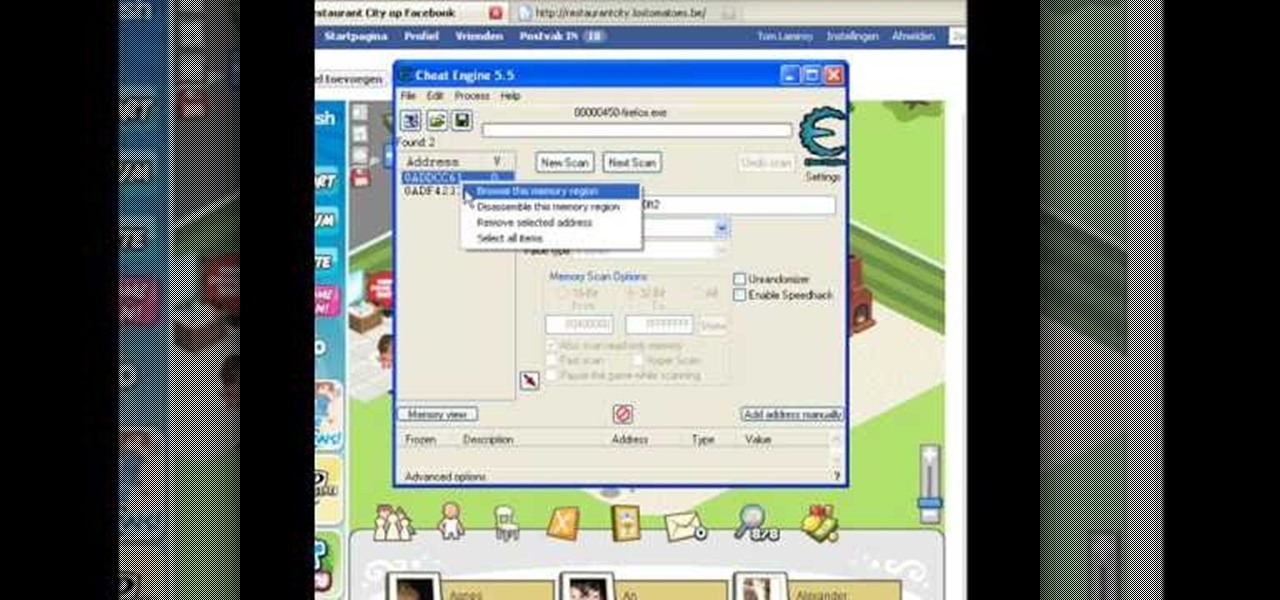
Make sure you use FLASH Player 9 First: Deinstall Flash Player 10

Preventing S cracks in ceramic work can be simple when using these expert tips. Learn how to prevent S cracks with this free ceramics video series.
Without Tools, Crack a Combination lock! Meant to break into your own lock in case you forgot the combination. Learn how to reduce possible combinations from 64,000 to 100. This lock cracking trick will help you next time you need to pick a combination lock.

This video won't show you how to crack a safe but it will show you the next best thing: cracking a combination lock or master lock! We do recommend only trying this on a lock you have forgotten the combination to and not other unlawful purposes. Watch this video tutorial and learn how to retrieve the combination from a lock. Hack your own lock or your friends and you have the potential for great practical jokes.
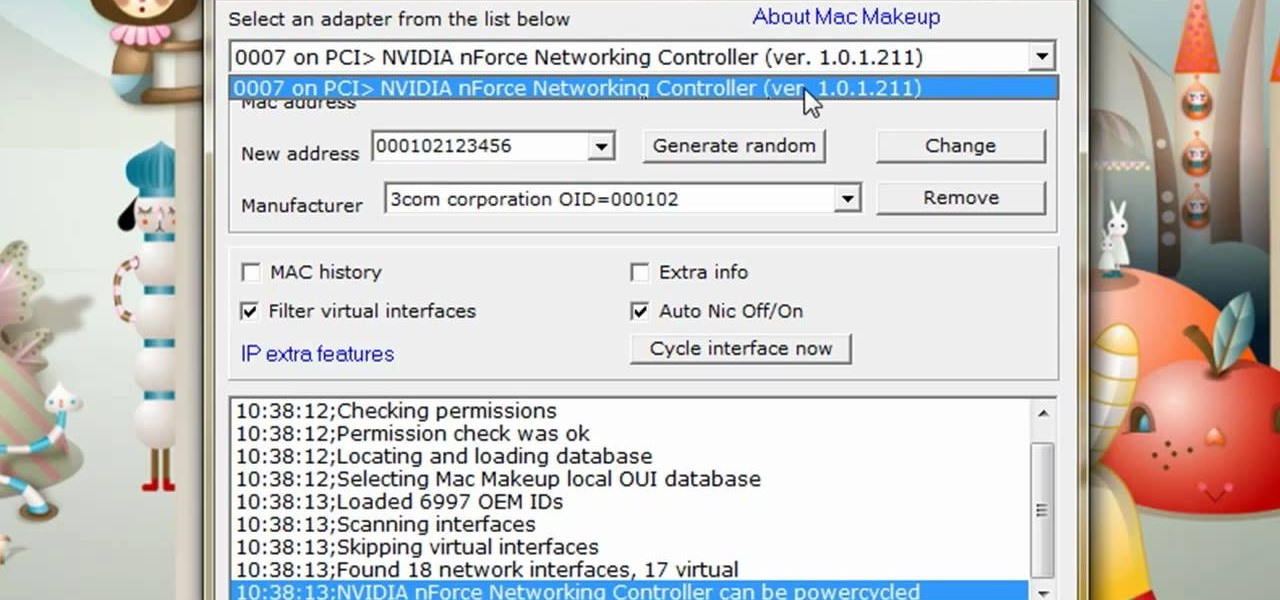
The video is about how to change the IP address. MAC address is the unique identifier a site of the most network adapters. MAC address is used to determine what IP address the computer will have and one way to change the IP address is by changing the MAC address. The method is only applicable for the windows systems and for the MAC systems you need to look at the link provided. In Windows in the start menu, type cmd in the run/search box, which will launch the command window. Type ipconfig/al...

During the holidays, many recipes call for cracked black peppercorn (it's much fresher and much tastier than regular pepper in a plastic seasoning jar).
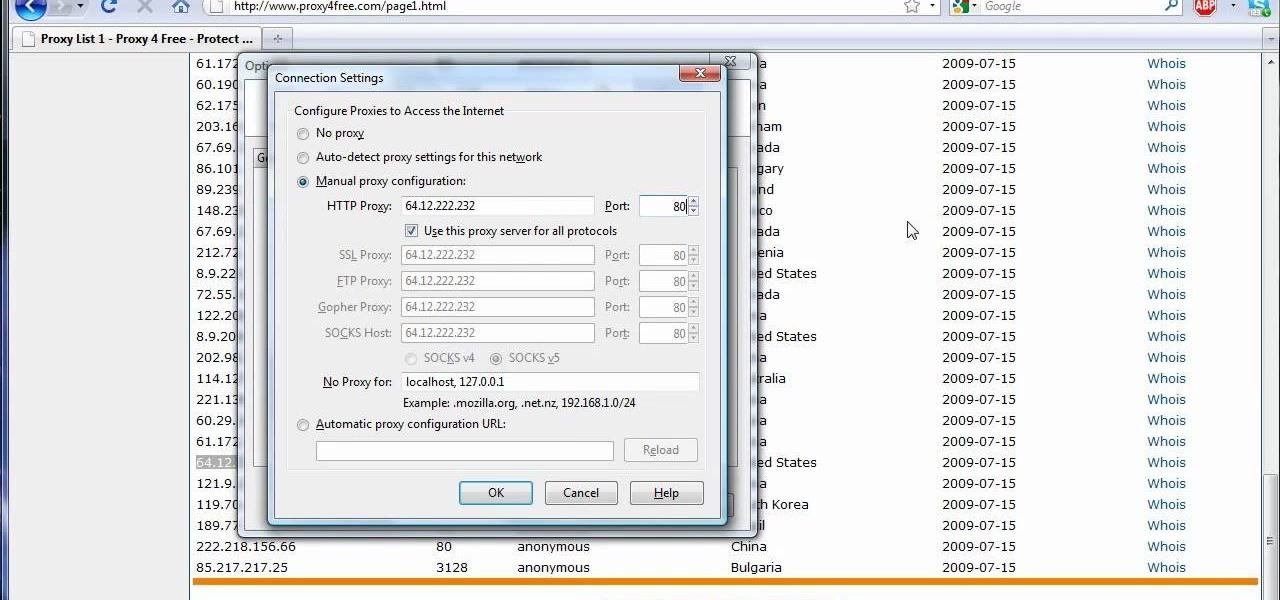
The video shows us how to use a proxy server with Firefox to hide your IP address. you can actually use this to avoid the hacking and various things that are blocking you from websites. Firefox is one of the easiest way to do this and for doing this you need to Google search the free proxylist and then you can select a proxy from the one which is related to the country you are residing in. Then copy that proxy server and then go to tools and click on options and under advanced tab click on ne...
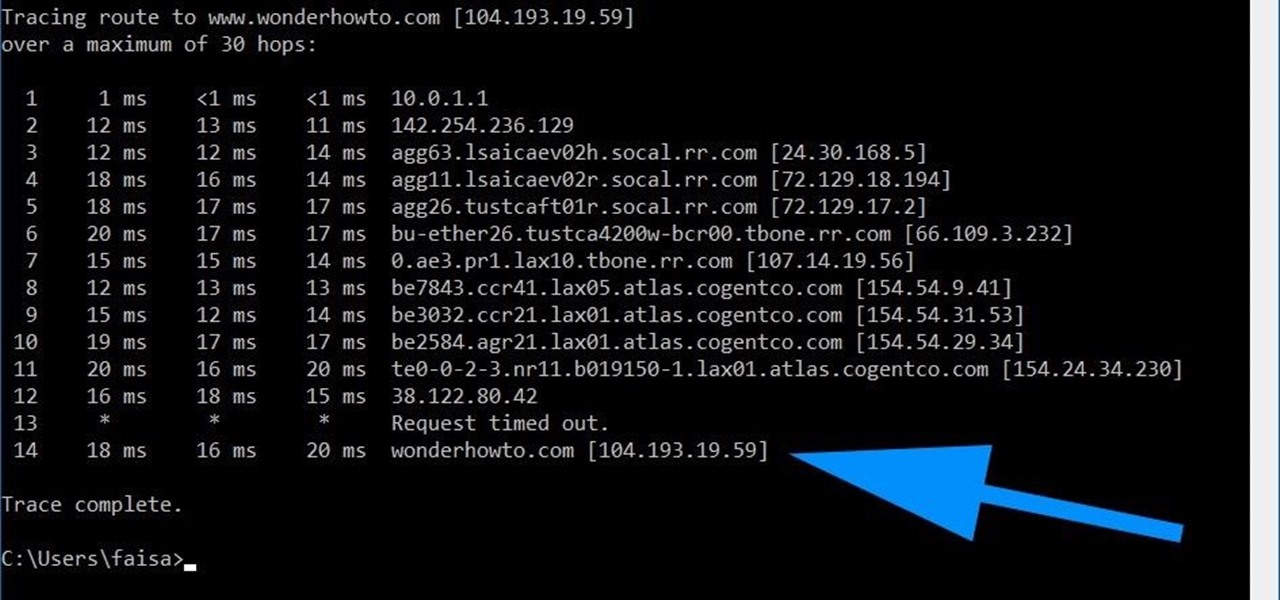
Using a simple trace trick, you can easily look up the IP address and its location for any website. This method uses a command line command to first find the IP address of a given website, and then uses a free online tool to get that IP's location.

A flaw in WPS, or WiFi Protected Setup, known about for over a year by TNS, was finally exploited with proof of concept code. Both TNS, the discoverers of the exploit and Stefan at .braindump have created their respective "reaver" and "wpscrack" programs to exploit the WPS vulnerability. From this exploit, the WPA password can be recovered almost instantly in plain-text once the attack on the access point WPS is initiated, which normally takes 2-10 hours (depending on which program you use).

Cracked ukulele? Why not take a crack at its repair yourself? This tutorial demonstrates how to repair a simple cracked open seam with hot hide glue using the "percussion" technique—a method, which incidentally, will work for any wooden string instrument. For careful, step-by-step instructions, and to get started restoring your own damaged uke, watch this helpful how-to.

This 5 part video tutorial series will show you how subnet an IP address on your personal computer. It's a thorough, detailed walkthrough of each step, with explanations on things as basic as "what's an IP address?" Watch the entire series to learn thoroughly about subnetting IP addresses on your personal computer.

The Lab Rats, Andy Walker and Sean Carruthers, explain Media Access Control (MAC) addresses. Filtering MAC addresses allow you to very specifically control access to your wireless network.

Your IP address is what identifies your personal computer while you are online. You may want to change your IP address for privacy, to bypass website settings, to download, or for various other reasons. This tutorial will take you through the steps you need to start surfing more anonymously.
Wondering how to find the Internet Protocol address of a website?
Just like the title says, learn how to crack a master lock. Not pick the lock (picking a master lock will not get you the combo). You don't need any special tools to crack this master lock- all you need is the right technique. Crack master locks for fun only - don't use this for illegal purposes. Great trick if you lose your combination to your master lock. All you need is a little math. Learn how to hack a master lock with this lock cracking tutorial.
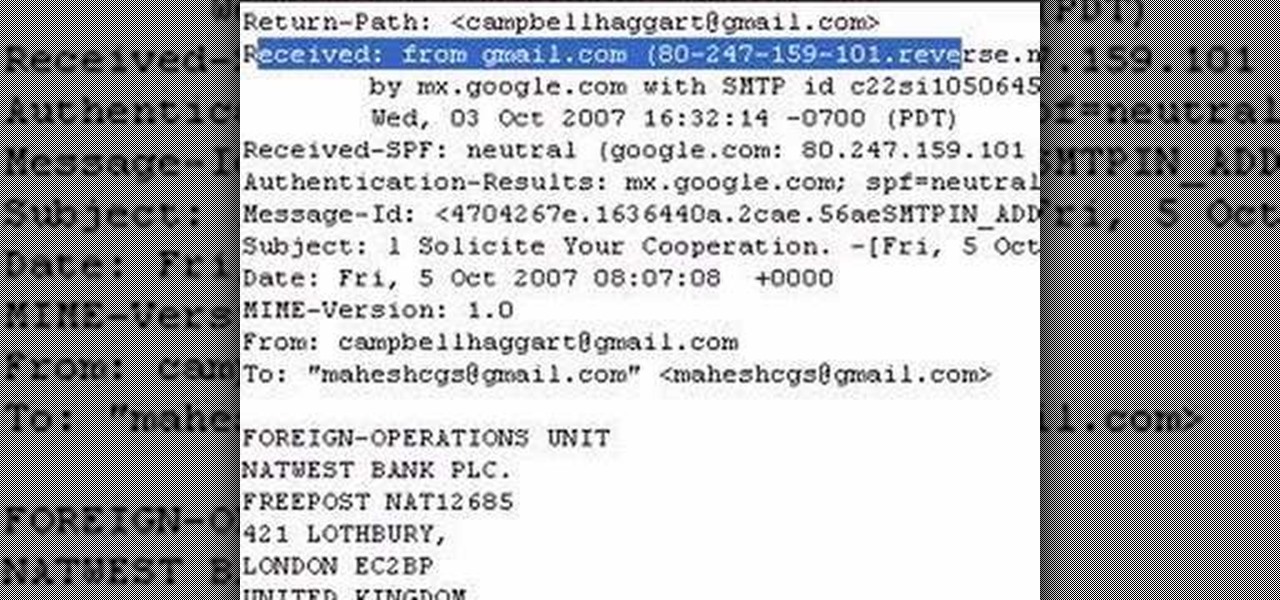
The author shows how to identify the IP address of a email. He shows how to check the 'Show Original' options in Gmail and in that content how to identify where the email came from and exactly its IP address. Now we can take that IP address and go to any of the many IP lookup websites and trace the original geographical location of that IP address. By following the steps in this tutorial you can easily trace out the origination IP address of an email from which you can extract a lot of useful...
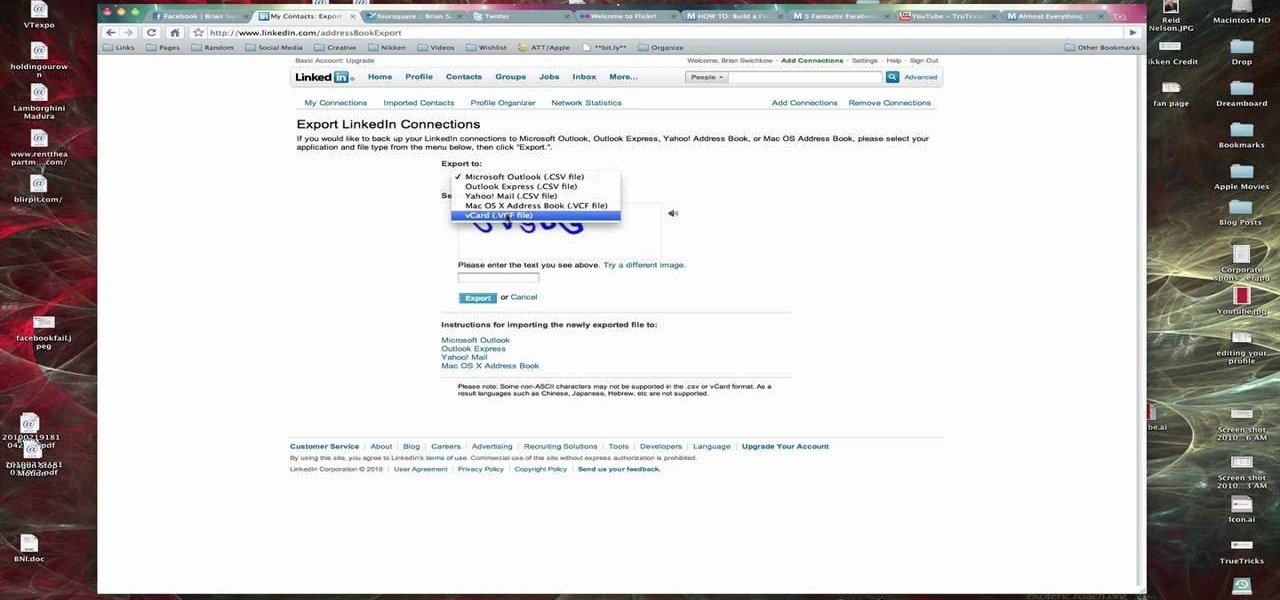
In this Computers & Programming video tutorial you are going to learn how to export LinkedIn contacts to an address book. LinkedIn is great for keeping your contacts in your professional network. To export your contacts go to home page and click on ‘contacts’. Now your full network of contacts will be displayed. On the right hand bottom, click on ‘export contacts’. On the next page select where you want to export the contacts, type in the security code and hit ‘export’ and all the contacts wi...

Great news if you're looking to upgrade to either the S10e, S10, or S10+. Samsung has a trade-in program that's offering potentially massive discounts of up to $550 if you preorder one of their flagships right now — but only for certain phones.

In this video, we learn how to repair small cracks in wood projects with Bob Schmidt. Even though the cracks are small, they may catch your eye when you walk into the room. You can minimize this with just a little bit of work with a screwdriver. First, grab your screwdriver and rub the middle of it on the corner of two pieces of wood. This will rub out the two pieces without changing the stain on the wood. If you have a missing crack on baseboard, you can do the same thing, which will lessen ...

In this video from flytenewmedia we learn how to send from separate email addresses using Gmail. This is great for small businesses. To make it look like you are sending it from your other email address, and not Gmail, follow these steps. Click on Settings then click accounts. You need to add another email address that you own. Click on next step. Now Gmail will send a verification. click on the inbox and click the link within the gmail that you just received. Now it will say confirmation suc...

This is a how-to –video on using hydra 5.4 to crack FTP passwords. This video is intended for educational purpose only. It reveals the basics of hacking a FTP server using dictionary search technique. Here are the steps involved.

How to spackle a crack or a hole
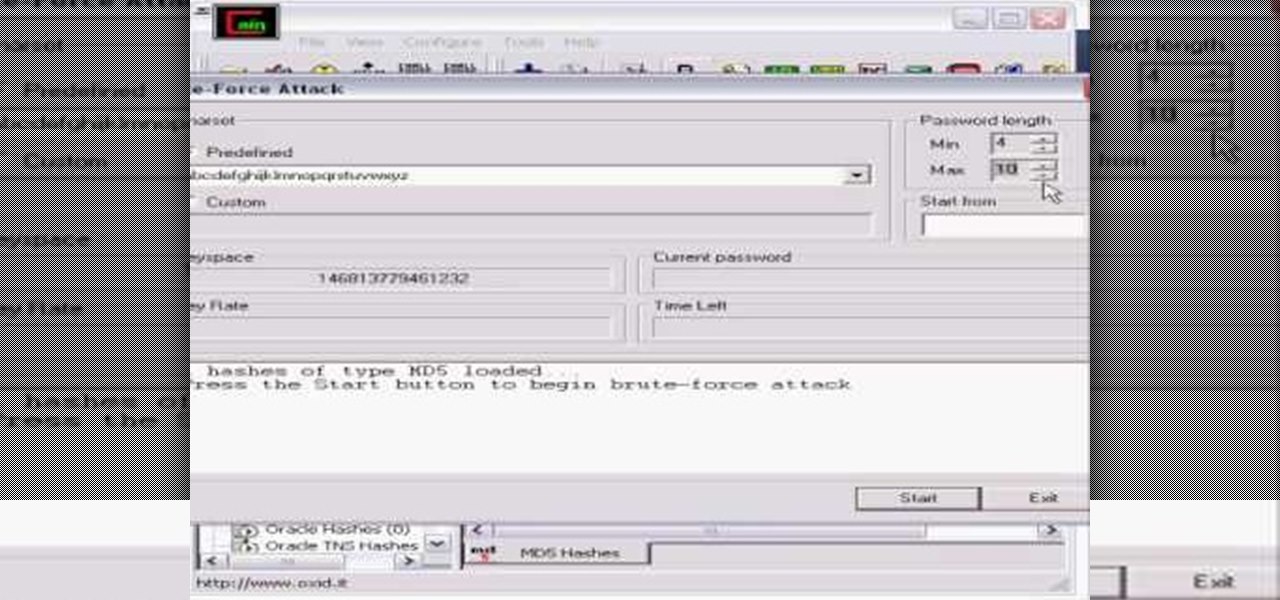
Whatever your reasons for doing it, if you are trying to hack passwords, it helps to have the right software for getting the job done. With the Cain and Abel program, you will be well on your way to hacking even the toughest personal passwords.

If you're like most people running Mac OS X, you've got quite a large number of entries in your Apple Address Book. In this how-to, you'll find instructions for organizing your addresses into groups for easy access in Address Book, other applications, and even sync devices such as other Macs, iPods and iPhones. For more on using groups in Apple Address Book for Mac OS X, watch this video tutorial.
This is a great tutorial on how to use Backtrack 2 to crack a local computer for access. You can either completely change the password or you can wipe it and restore the password so nobody knows you were there
Learn how to crack and separate an egg.

This video from the website What to Cook When shows us how to crack open the crab legs and get the meat out of them. Firstly starting with the cluster of legs, simply grab one of the legs and break it off of the cluster. Now simply grab the leg and starting with the joint, break it into half and pull it apart. Then take the middle section which you just broke and put your fingers right in the middle of that section, crack that one leg and then flip it over and crack it the other way. And once...