In this video tutorial, we learn how to prevent a laptop computer from being stolen as well has how to install tracking software that will enable you to find the culprit if it is. For more information, including a complete demonstration and detailed, step-by-step instructions, watch this how-to from the folks at Tinkernut.

The first thing that comes to mind when your car is stolen is: ####!! However, once calm, cover these bases when your car is stolen to notify relevant parties and help ensure vehicle recovery or replacement.

How great did Hayden Panettiere look at 2009's Golden Globes? Well, now is your chance to steal Hayden's glamorous look with a little help from makeup artist, TiffanyD.

Do you worry that if your PC is stolen someone can copy all of your data? Then you should encrypt your hard drive and removable USB drives too. In this video tutorial, you'll see how Windows 7 has beefed up Bitlocker, its built-in encryption program, and learn how to use it. It's simple! So simple, in fact, that this home-computing how-to can present a complete, step-by-step overview of the process in just under two minutes of your time. For more information, including complete, step-by-step ...

The Origami Spiked Pentakis Dodecahedron is an excellent Paper Christmas Decoration Star made out of 15 paper squares. In spite of the large paper size I was defeated by the last module after nearly 2 hours (!) of trying to lock the last unit in place each time another one dislodged. Never mind, it is still a remarkable sound structure once (nearly) completed and you can not see which one is not locked anyway.

Check out this video to learn how to prevent your car from getting stolen or broken into. Part 1 of 2 - How to Prevent your car from getting stolen or broken into.

This pair of video walkthroughs will teach you how to complete the sidequest 'Finders Keepers' in Dragon Age 2. In it Isabella will call upon you to help her friend, a former raider named Martin. Look at that face in the thumbnail. How could you not help someone so sad-looking?

This software tutorial will show you how to track a laptop if it gets stolen using free tracking software Adeona. Of course, it's a good idea to figure out how to keep your laptop from getting stolen, but if you lose it, you can use Adeona to find the location of your laptop.

Take it up a notch next Halloween by re-creating a classic princess with a naughty twist! In this two-part tutorial, learn how to steal the look of sweet & innocent Disney princess, Snow White and transform her into one hot retro pin-up model! Makeup & hairstyling is gone over by makeup & hair specialist Iris with a step by step process. Take seven short friends with you as dwarves and your look is complete!

In this prank video tutorial, you will learn how to steal a bed without getting caught. To pull off this cool prank, you will need three group members, a bed to steal, and a place to stash the stolen bed when you are done.

Steal Kim Kardashian's look for your next big outing with this two-part tutorial on how to put together this beautiful celebrity's makeup look. In part one, our host CMichelle, shows us how to prime our face and apply the shadow. The second half speedily goes through how to line the lids.

This guide is a little humerous, but it details the way in which you can hide your chests in Minecraft so that you can stop people from stealing your items in the game. The trick involves a pretty crafty way to build your house.

In this clip, the Achievement Hunters, Geoff and Gus, show you how to navigate the new DLC for Mass Effect 2, Kasumi - Stolen Memory. This cool level is downloadable and if you are lucky enough to get your hands on it, check out this clip for advice on reaching a bunch of important achievements. Have fun!

Nothing can ruin a nice bike ride like getting your bike stolen. Improperly locking your bike or just leaving it unattended is a sure way for it to be stolen.

Hacking into computer systems to steal passwords could be a bit complicated for the average everyday joe, but for all of your tech illiterate folks out there, there's any easy way to get that password, and all it takes is a camera.

Do you play basketball? Take a look at this instructional video and learn how to steal the ball on the court with Kansas senior point guard Russell Robinson. To this you, first you need to apply pressure. As you do this you force your opponent to make mistakes and this will give you a window of opportunity to exploit the situation. Keep in mind that you need to maintain defensive principles.

This may sound like a terrible thing to show you how to do, but the Neistat Brothers are simply victims of bicycle theft who got fed up. They use their own bikes to show you how to steal a bike in NYC (in broad daylight) so hopefully you can learn from them, how to better protect your ride.

There's nothing more maddening than opening the office fridge and discovering your lunch is gone. Put an end to the stealing with some of these strategies. This video will show you how to deter coworkers from stealing your lunch.

A car is stolen every 33 seconds in the United States, and from that, the percentage of vehicles recovered in the first day is a whopping 52 percent. Over the next week, that number rises to around 79 percent, but after those initial seven days are up, it's unlikely the vehicle will be found.

Demon's Souls is famous for being one of the hardest games on the PlayStation 3 today. It takes most anywhere from 30-50 hours just to complete one playthrough. But, this man has gone and completed the entire game in under one hour (54:54 to be exact). Wanna know how? Check out this video walkthrough of how to beat the game in under one hour. If anything else you can watch and be completely amazed at how amazing this guy is at this game!

Want to learn how to play Dashboard Confessional on the guitar? With this tutorial you can learn how to play "Stolen" by Dashboard Confessional on the acoustic guitar. This version is a simplified version of the song and is not exactly how Dashboard Confessional plays it. This lesson is geared towards intermediate guitarists because it assumes prior knowledge of guitar playing. Watch this how to video and you will be able to sing and play the guitar along to "Stolen" by Dashboard Confessional.

Want to learn how to play Chuck Wicks on the guitar? With this tutorial you can learn how to play "Stealing Cinderella" by Chuck Wicks on the acoustic guitar. The capo is on the 1st fret used in standard tuning. This version is a simplified version of the song and is not exactly how Chuck Wicks play it. This lesson is geared towards intermediate guitarists because it assumes prior knowledge of guitar playing. Watch this how to video and you will be able to sing and play along to "Stealing Cin...

In a twist in the tumultuous lawsuit between Uber and Waymo, Uber revealed today that they found a document on an employee device, allegedly stolen from Waymo.

Hello everyone. I'm Calypsus and i've been around for a while learning from various tutorials, expanding my knowledge and this is one of the best platforms for newbies to sharpen the skills. Today i decided to register myself and contribute to this wonderful community. Since this is my first post, any kind of feedback is appreciated.

Computer system authentication is critical to keeping systems safe from unwanted users, intruders, and abusers. Basically, authentication is the process of the potential user proving they are an authorized user.

While the Play Store has a plethora of apps available for finding lost Android phones, Google came out with its own web-based application, Google Device Manager, earlier this year to help you keep track of all your Android devices and remote lock, erase, ring, and track if need be.

If you're scared of using public Wi-Fi networks with Firesheep out and about, then maybe you should fight back. Don't switch to another web browser— keep using Firefox safely with the help of a new Firefox Add-on that combats Firesheep's password stealing capabilities. It's called BlackSheep, and when installed and running, it will alert you whenever Firesheep is active on your network connection.

In this episode of Full Disclosure we are explaining the website attack known as Cross-Site Scripting (XSS). Cross-Site Scripting is a type of security vulnerability that affects web applications that do not sanitize user input properly. This kind of vulnerability allows an "attacker" to inject HTML or client side script like JavaScript into the website. Cross-Site Scripting is most commonly used to steal cookies. Cookies are used for authenticating, tracking, and maintaining specific informa...

Welcome... the the final mission of Dragon Age 2. You initiate it by reading the letter The Last Straw on Hawke's desk. But before you do that, you should complete any sidequest you still want to do because the game is officially over after this. This video series will guide you through the quest, and this guide from the creators of this video should fill in the gaps.

So, you've found yourself in a hotel room, and for some reason you just have to remove that cable from the wall. However, it is protected by a cable lock. In this instructional video, see how to defeat these using a piece of toilet paper, a pen, and the cable lock itself!

Uber and Waymo's lawsuit is starting to pan out. Following a ruling on Monday, May 15, Judge Alsup, who called Waymo's patent infringement claims "meritless," ordered Uber to perform a series of actions and duties for Waymo. Without further ado, here's what Uber must do to begin to put this lawsuit behind them (well, maybe):

Though you can use the Social Engineering Toolkit to clone websites, this way is much more customisable.

The Call of Duty Black Ops Zombies (that's a mouthful) map Ascension introduced perk-stealing monkey to the bestiary of enemies. They are quite annoying, and this video will teach you how to deal with and dispatch them easily, keeping your precious perks intact for better zombie slaying.

You've made it far, Hawke. 'Demands of the Qun' is the final quest in Act 2 of Dragon Age 2. HThis eight-video series will walk you through the entire quest, with knowledgeable commentary on strategy and tactics that should teach you everything you want to know. You should also check out the written version of the walkthrough here for further tips and support.

'The Deep Roads Expedition' is the exciting conclusion of Act 1 of Dragon Age 2, and this excellent walkthrough of it runs to nine separate videos. Worry not, friends, it in very enjoyable and well-made viewing that will teach you everything you could ever possibly want to know about this quest. It is a strategy guide among strategy guides.

This half-hour episode of Hak5 covers several topics: Using a DSLR camera to create HD footage, building your own Google TV, unlocking & copying locked files with Lock Hunter, using PicPick for screen capture, using WinDirStat for analyzing & cleaning your hard drive, setting up a secure FTP server with Ubuntu Server, and secretly copying data from USB drives with USB Dumper.

Find My iPhone is one of the best Apps of all, allowing you to find your iPhone no matter where it is, lost or stolen. This video will show you how to install and set it up on any iPhone or iOS 4.2 device, even those not technically supported by the newest free release of the software.

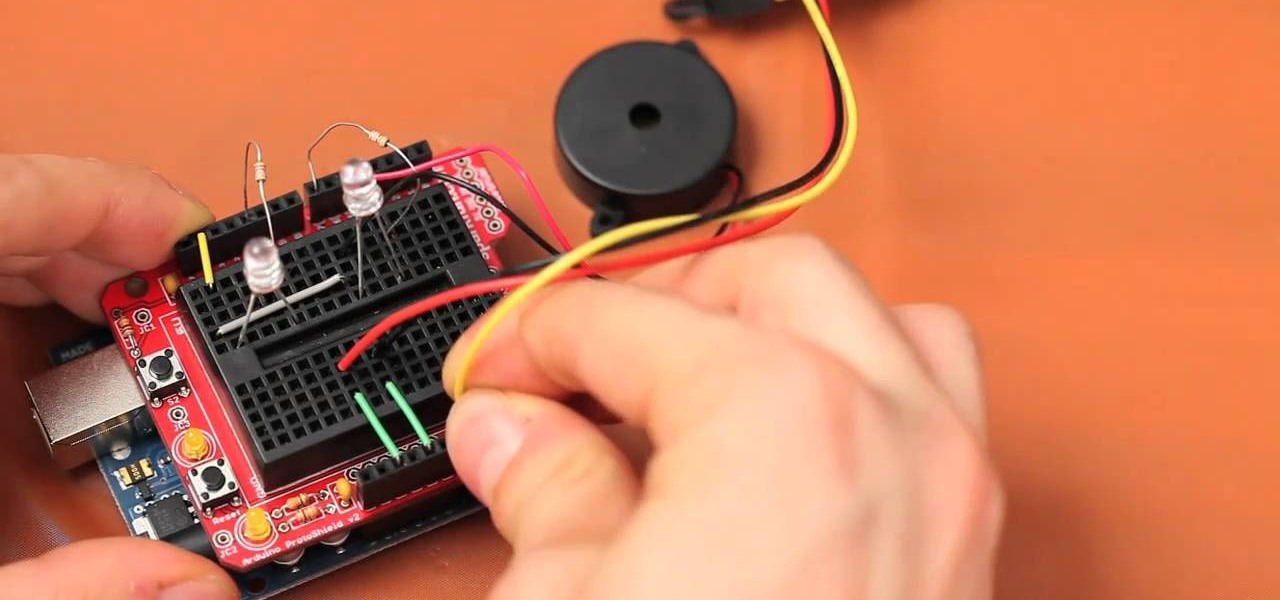
The Arduino Ethernet Shield is a wonderful device for DIY electronics projects, and this project is really creative and awesome. In this video you will learn how to use an Arduino, a promixity sensor, and some LED lights to make a proximity-sensing, LED-lit, evil Jack-o'-Lantern that will terrorize your neighborhood and probably get stolen if you don't watch it like a hawk.

The Microsoft Kinect represents its attempt to steal the Wii's thunder, and it work pretty dang well. Watch this video for a guide to plugging the Kinect into your XBox 360 and setting up your gaming area so that you'll be able to play it.

Want to know how to get a lot of money fast in Mafia II on the Xbox 360? Geoff and Jack from Achievement Hunters tell you the path to riches. If you go to the salvage yard, Mike Bruski will pay you about $400 for each car you steal and crush. What could be better than crushing cars for money?