Hi everyone! Last time we finished analyzing the assembly representation of our vulnerable piece of code (have I ever told you it is vulnerable?). This time we are going to introduce some fundaments about exploitation by demonstrating how to crash a program's execution. If that sounds lame, next time we will see how this crash can in fact be useful to control the program's execution, achieving remote code execution!
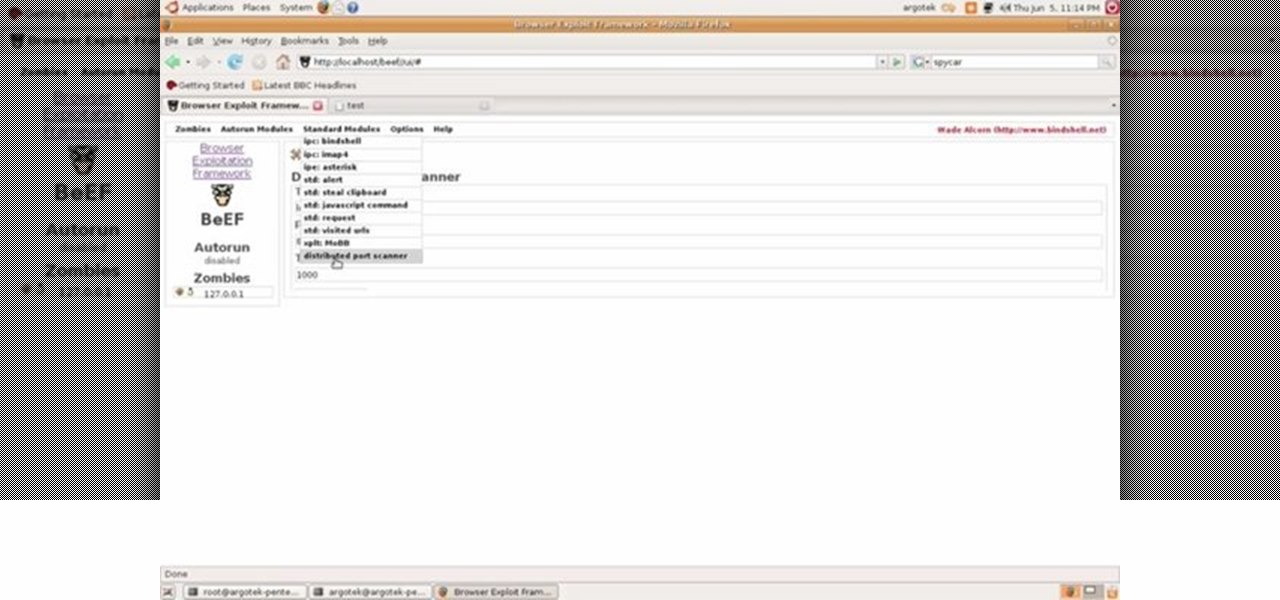
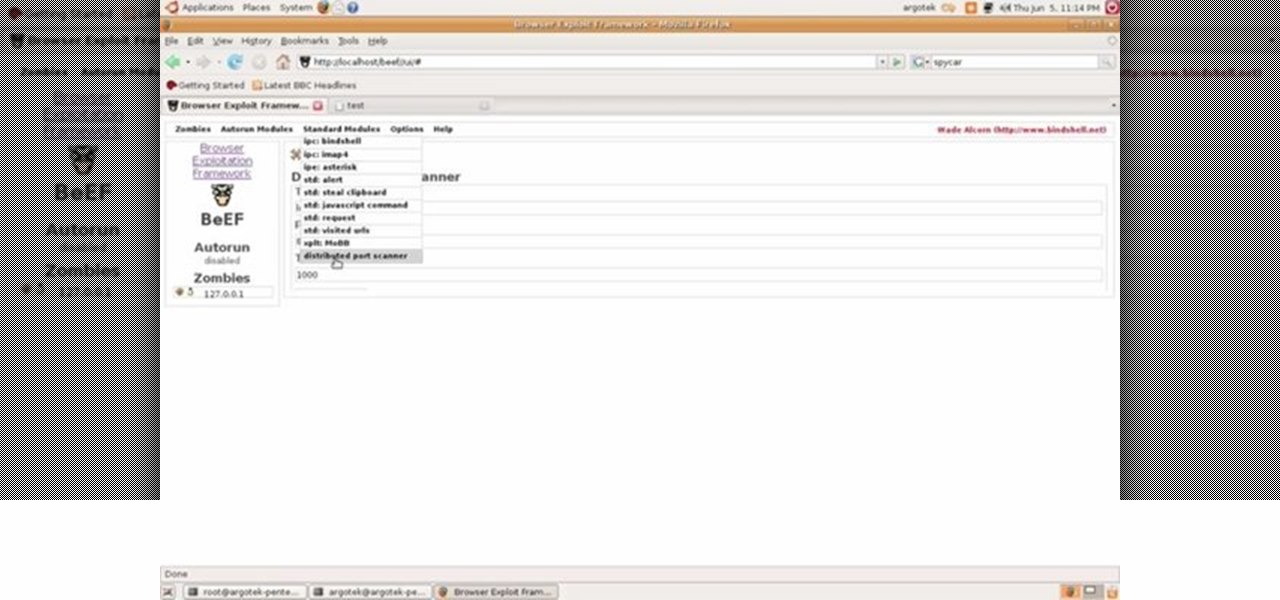
This video tutorial talks about browser exploitation. Particularly, it talks about tools, like BeEF, that can be used to hack known vulnerabilities within browsers and some cool frameworks that you can use to check the security of your own browser. To get started hacking your own browser, watch this how-to.
Hi everyone! In the previous part of this series, I introduced one way to hijack a program's execution flaw, though I only showed you how to crash the program and left you with a little mystery to solve. Today we are giving the solution of that and then introducing shellcode usage and remote command execution.
Hi everyone! Last time we explained what roles Ebp and Esp registers have. We first introduced function's stack frame building, return address and calling conventions, but left some of the concepts floating without a full stop.
Hi everyone! In the previous part of this series we introduced remote code arbitrary execution via buffer overflows using all of our past experiences.

Welcome back, my fledgling hackers! In one of my recent articles, I showed you how to install BackTrack as a dual boot system on a Windows computer. In this tutorial, I will walk you through BackTrack, giving you a tour of the most salient features for the hacker-to-be.

File permissions can get tricky on Linux and can be a valuable avenue of attack during privilege escalation if things aren't configured correctly. SUID binaries can often be an easy path to root, but sifting through all of the defaults can be a massive waste of time. Luckily, there's a simple script that can sort things out for us.

With the the general computer users understanding of Information security rising (at least to the point of not clicking on unknown links), and operating system security getting better by default. We need to look for new and creative ways to gain a foothold in a system.

Car accidents are the leading cause of death of children in the United States. Follow the guidelines in this how-to video to give your child a safe ride. All you'll need is the kid's new car seat and the owner's manual to your vehicle. Proper installation is key, so check out this instructional video to learn where and how to put that car seat in safely and correctly.

Make reading more fun for your children with a satisfyingly medieval bookcase that your little prince (or princess) will use day in and day out. This woodworking project from Lowe's is a wooden bookcase with a castle top. It's completely functional, with plenty of storage for books and knick-knacks, as well as a storage drawer at the bottom. Best of all, the book castle can be easily modified to remove the castle top when your child's tastes change. Watch all four videos to see the build inst...

Did you know that drowning is the second leading cause of death for children under the age of 14? I worked as a lifeguard and swimming instructor when I was younger and I have seen firsthand too many close calls with kids around water. This program is about basic water safety for children.

How would you like to make some classic toys at home with your kids? Learn how to make three classic children’s toys, a Jacob's Ladder, a dragon clapper and a puppet, in this free crafts video series.

Even if you don't have children, these tips are great for grandkids or visitors with children. This how to video outlines ways you can child proof your home and prevent accidents.

Post-exploitation is often not quite as exciting as popping the initial shell, but it's a crucial phase for gathering data and further privilege escalation. Once a target is compromised, there's a lot of information to find and sift through. Luckily, there are tools available that can make the process easy. One such tool is Postenum.

This is my first contribution in an ongoing series on detailing the best free, open source hacking and penetration tools available. My goal is to show you some of the quality tools that IT security experts are using every day in their jobs as network security and pen-testing professionals. There are hundreds of tools out there, but I will focus and those that meet four key criteria:

Dragonfly's are fascinating in both appearance and movement. Learn how to make a paper dragonfly in this free crafts video series.

Are you looking for a fun way to keep track as your child gets taller? Learn how to make a children’s height measuring board in this free crafts video series.

Are you looking for a fun way to decorate your child’s room? Learn how to make a child’s lamp shade in this free crafts video series.

Looking for free poncho patterns? Learn how to make a fleece poncho without sewing in this free video series about no sew projects.

4 in 5 child car seats are installed incorrectly. Here are some tips on how to do it right.

Being able to use scissors is a good benchmark for measuring fine motor skill development in your child. These simple instructions will help you teach your children how to safely use scissors. NO HAIRCUTTING HINTS INCLUDED!

Hello, everyone. Stealth is a large part of any successful hack; if we don't get noticed, we're much less likely to be caught. In these next few articles, we'll be building a shell based on keeping us hidden from a firewall. There are many ways to stay hidden from a firewall, but we'll only be incorporating a couple into our shell. This article will outline and explain these evasion concepts and techniques.

Welcome back, my neophyte hackers! Metasploit is such a powerful tool that I can only scratch the surface of its capabilities here. As it has developed over the years, it is now possible to use Metasploit for nearly everything from recon to post exploitation to covering your tracks. Given its versatility, every aspiring hacker should have at least a tentative grasp of Metasploit.

Hello again! In this tutorial, we are going to go over something called "operators" which will help us build upon conditions of control structures and also some variable manipulation. Without further ado, let's dive in!

Learn how to model a fairytale Book in Cinema 4D with this video walkthrough. Whether you're new to MAXON's popular 3D modeling application or are just looking to get better acquainted with Cinema 4D and its various features and functions, you're sure to enjoy this free video software tutorial. For more information, including complete instructions, watch this 3D modeler's guide.

Do you have a budding drummer or drum major in your home? Learn how to make a children’s marching drum in this free crafts video series.

Shelley Lovett has some tips for helping a young child learn how to use scissors. The first thing you need to do is make sure you have paper and child size scissors available for the child to use. A full sheet cut in half is usually more manageable for a young child to work with. Have the child take the paper and just make cuts into the paper however they feel comfortable. Using colored paper can make it more interesting for them. After that very beginning practice stage has been accomplished...

Dr. Bob Sears explains to parents the difference between a child's fever that may be serious and one that isn't. Only when the child's fever is high and any efforts to bring it down have failed, should you seek medical attention. This means the child could have a serious infection. A temperature of 103 or more is considered high, 101-102 is medium, and 99-100 is typical. Dr. Sears recommends using a regular digital underarm thermometer to check the child's temperature. Hold the thermometer un...

Celebrated and award-winning children's illustrator, Jan Brett, shows how to sketch a Siberian Husky dog. Learn how to draw a dog by following Jan's simple instructions that go from making easy shapes to the finished product. This video tutorial gives instructions simple enough for even children to follow along.

Giving your kid a bath is an integral part of child care. What's that saying? Cleanliness is next to Godliness? Okay, maybe not, but a clean baby is a great sight, but there are things to worry about when filling up the bathtub. Could the water temperature be too hot? NFPA's Amy LeBeau on the importance of testing the temperature of bathwater before putting children into the tub. Safety also comes first.

Did you know that a large number of car seats are installed incorrectly? This child safety video offers great tips on how to keep your child from getting harmed in an automobile accident. Learn how to install your car seat properly with these easy to do steps and discover some important car seat safety tips.
Hello! My name is An0nex. I am an ethical hacker who wants to share the art of hacking with all of you guys!

I'm still amazed by all the things some people just don't know. Script-kiddies often refer to Metasploit if someone asks them how to hack a computer because they think there's simply no other way. Well here I am today trying to increase your set of tools and -of course- skills.

In Korea and Japan a special holiday called Children's Day is celebrated. Like Mother's Day or Father's Day in the United States, the occasion honors one particular family member, or members, with gifts and special parades or events.

Jerry Lavender demonstrate how to build confidence in your children. Use secure attachments to provide a stable base for your child. Your child will fee safe to explore the world. Provide structure and predictable environment for your child. This will enable your child to relax. Use a stable routine so that your child knows what to expect during the day. Encourage your child to play with people in their environment. Sports and physical activity raise endorphins and increase happiness. Remembe...

Knitting circular socks on a Passap knitting machine is fun and easy! Follow along in this three part video and knit a children's pair of socks. Complete instructions can be found in Knitwords magazine.

Giving your child a haircut can be a disastrous experience. This how to video gives you some tips on making your child's haircutting much easier. Learn how to give your child a hair cut at home with this video tutorial.

Divorce can be a most difficult process for anyone to go through, let alone a young child. Both parents need to remain large parts of the childs' life, as well as continuously remind the child how much they're loved. This parenting how-to video gives some quick tips on how to help your child cope.

Learn how to teach children to read with these video lessons. Teaching reading to kids has never been easier!

In this how to video, Kathie Hill, children's choir director for over 30 years, gives helpful tips to choir directors in how to get children to open their mouth and sing. This tutorial teaches singing techniques to help one single child or a whole choir of children. Watch this tutorial and you will be able to teach kids to sing in no time.