Are you inspired by spy movies? Is James Bond your role model? Have you always wanted an exciting military or government career? These tips will show you the best way to land your dream job as a CIA agent.

Learn to cook like a professional Culinary institute of America chef. Watch this how to video as CIA Chef Instructor Iliana de la Vega shows us how to prepare rajas Poblanas. This Mexican recipe is sure to impress everyone at your table. Serve with tortillas.

Not quite sure what to make with all the left over Thanksgiving turkey? CIA Chef Lynne Gigliotti gives some simple tips on how to use up those turkey leftovers. Try making this delicious turkey pot pie recipe. Top your pie with mashed potatoes!
Wanna be a spy? How bout in the CIA! The Arabic alphabet is important. It makes getting around the Arab world, middle east and Indonesia nearly impossible. Check out this simple tutorial on how to learn the Tajweed or Arabic for alphabet.

Discover the secrets to perfect whipped cream from this how to video. The chefs at The Culinary Institute of America show you tips and techniques for whipping cream like a professional.

Learn to cook fish tacos like a professional Culinary institute of America chef. Watch this how to video as CIA chef Joe DiPerri shows us how to make Baja-style fish tacos with southwestern slaw, chipotle pico de gallo and Mexican crema.

This video shows how to draw the comics character Spawn, a former CIA operative killed by his own men and afterwards recruited to be a general in Hell's army. Running at a 6x speed, you will find it easy to replicate. To accomplish this task, you'll need a sheet of paper, a pencil and red, grey and black markers. In less than 10 minutes, without any special drawing skills and simply by following the tracing and coloring shown in this video, you will finish a fully colored entire body drawing ...

These days, news papers, online editorials and magazines are filled with news on Iran and Syria. Of course, that is expected, as such sources need to stay current to stay in the game. My concern is that most of these articles talk about what to do about these situations.

Repetition, repetition, repetition. Brainwashing, is it real? Watch these absolutely stunning segments of hidden camera containing both Bill Clinton, and Barbara Bush. Probably one of the most debatable segments is the one featuring Clinton talking to Larry King behind the scenes. If you turn your volume up it is hard to disregard, that they both in fact knew, Clinton would be elected, and the corruption in media is also clearly demonstrated. There is a segment with Barbara, staring eerily fo...

A router is the core of anyone's internet experience, but most people don't spend much time setting up this critical piece of hardware. Old firmware, default passwords, and other configuration issues continue to haunt many organizations. Exploiting the poor, neglected computer inside these routers has become so popular and easy that automated tools have been created to make the process a breeze.

Learn to cook breakfast like a professional Culinary institute of America chef. Watch this how to video as CIA Chef David Barry shows us how to prepare some hearty breakfasts like steak and eggs with hash browns and Toad in a Hole. You know dad likes his steak and eggs.

In a world increasingly regulated by computers, bugs are like real-life cheat codes. They give you the power to break the rules and do good or bad without ever leaving your seat. And government agencies around the world are discovering and stockpiling unreported bugs as cyberweapons to use against anybody they see fit.

Welcome back, my rookie hackers! Now that nearly everyone and everyplace has a computer, you can use those remote computers for some good old "cloak and dagger" spying. No longer is spying something that only the CIA, NSA, KGB, and other intelligence agencies can do—you can learn to spy, too.

All those early prototype images Magic Leap is so fond of showing off are great, but they rank a far second when compared to a new set of images just revealed by Microsoft in relation to the HoloLens.

In January, ZTE announced they would be conducting an Oreo beta program for Axon 7 users to test Android 8.0 before the masses. Since then, no additional information was released — until today, when ZTE finally opened up the Oreo beta to US customers.

As the world goes into a frenzy over the latest strain of WannaCry ransomware, it might be a good time to remember to update all your devices. Yes, those little reminders your phone and computer throw at you every now and then to update your junk can be really annoying, but not without merit.

Last week, the U.S. Justice Department issued criminal indictments against seven Iranian hackers. These hackers, working for private companies in Iran, are accused of orchestrating DDoS attacks against U.S. financial institutions from 2011-2013 as well as intruding into the control panel of a small dam in Rye, New York. It is thought that these attacks were a response to the U.S. tightening financial restrictions on Iran during those years and the NSA-based Stuxnet attack on their uranium enr...

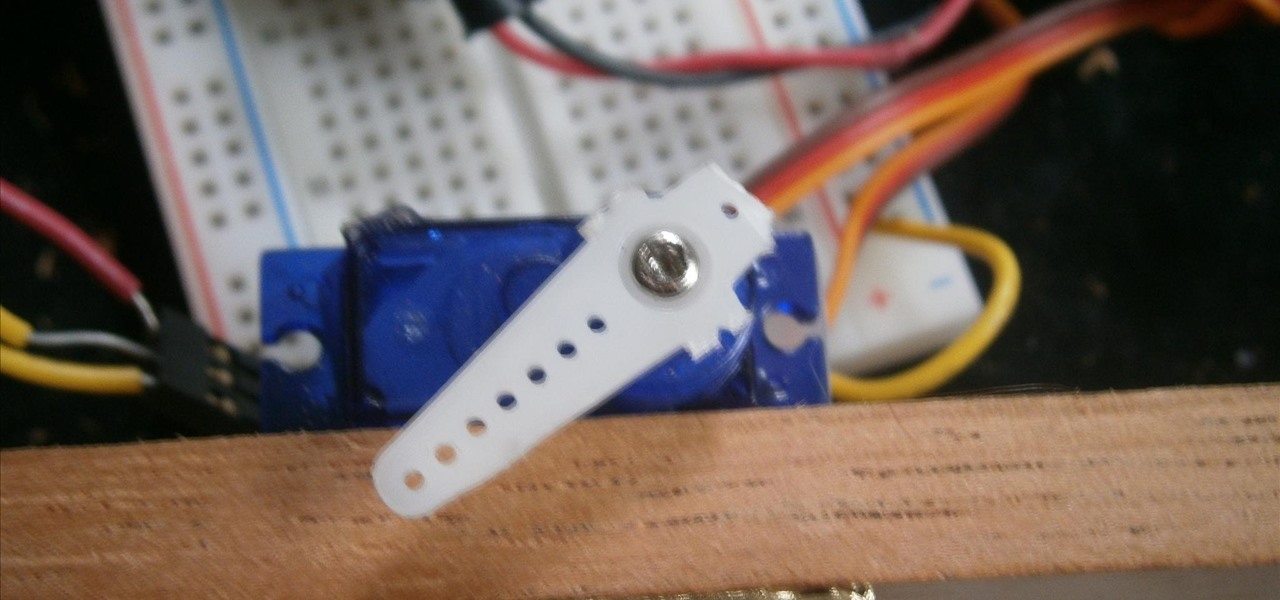
There is something special about a secret knock. It gets you into secret super villain meetings and is a surefire way to test for rotating bookcase passages. Secret knocks usually work with an intimidating drug lord and for policeman listening at the door for the correct pattern of raps.

It seems like a new, dangerous Android exploit is uncovered every month or two. The latest headliners are NightMonkey and Chronos from the list of CIA hacks reported by Wikileaks, which have been billed as gaping security holes in the world's biggest mobile operating system.

You want to become anonymous, and dont want your IP to be logged on websites? Well read along here. Continuing This Series:

I recently had my iPhone stolen at public park and did everything I could to locate it, but with Find My iPhone disabled (I know, what an idiot) and no exact address to give to the police, I had about a .00000001 percent chance of getting it back.

| Update: ZTE's issues with the US government have finally been resolved. Check out the details below.

In the recent hit movie Furious 7, the storyline revolves around the acquisition of a hacking system known as "God's Eye" that is capable of finding and tracking anyone in real time. Both the U.S. spy agencies and an adversarial spy agency (it's not clear who the adversary is, but the location is "beyond the Caucasus mountains," which could imply Russia?) desperately want their hands on this system.

By now, nearly everyone with any type of media access is aware that Sony Pictures Entertainment was hacked on November 24th. Although there can be many interpretations and lessons drawn from this audacious act, there is one indisputable conclusion: it and its ripples across the globe underlines how important hacking has become in our all-digital 21st century. As I have emphasized so many times in this column, hacking is the discipline of the future. From cybercrime to cyber intelligence to cy...

Welcome back, my budding hackers! People often ask me, "Why are you training hackers? Isn't that illegal?" Although I usually give them a short version of this post, there are MANY reasons why YOU should be studying hacking.

Find out how you can kick butt in Obsidian Entertainment and SEGA's video game Alpha Protocol. The RPG and action hybrid came out on June 1st, 2010, and is available on the PlayStation 3 (PS3), Microsoft Windows (PC), and the Xbox 360. This video game walkthrough series from Mahalo focuses on Alpha Protocol for the Xbox 360.

RouterSploit is a powerful exploit framework similar to Metasploit, working to quickly identify and exploit common vulnerabilities in routers. And guess what. It can be run on most Android devices.

Social engineering makes headlines because human behavior is often the weakest link of even well-defended targets. Automated social engineering tools can help reclusive hackers touch these techniques, but the study of how to hack human interactions in person is often ignored. Today, we will examine how to use subtle, hard to detect persuasion techniques to compromise a human target.

Many of our members here at Null Byte are aspiring hackers looking to gain skills and credentials to enter the most-valued profession of the 21st century. Hackers are being hired by IT security firms, antivirus developers, national military and espionage organizations, private detectives, and many other organizations.

Welcome back, my fledgling hackers! Hacking has a long and storied history in the U.S. and around the world. It did not begin yesterday, or even at the advent of the 21st century, but rather dates back at least 40 years. Of course, once the internet migrated to commercial use in the 1990s, hacking went into hyperdrive.

Three years ago, Double Fine productions held an in-house event called the Amnesia Fortnight. The company was split into four teams, each of which set out to spend two weeks developing an idea for a small game and present it to the other groups at the end of the duration. All of the ideas turned out to be winners, and founder/owner Tim Schafer secured publishing deals for all four games to be released on a combination of XBLA and PSN. In honor of the excellent Trenched becoming the third game...

WATCH THIS INSTEAD - Killers: Ashton Kutcher sure is handsome, but I mean come on... A CIA assassin? Please... you're better off watching Jonah Hill play a music executive in GET HIM TO THE GREEK

Dumb but honest. Like a golden retriever covered in ketchup
Some interesting news this week, from Obama's new political ad, to the $20,000 payments by Cardinal Dolan. Take a look:

Though under a lot of the average consumer's radar, the CISPA is now making rounds again with a coalition of advocacy rights groups. The act, known as the Cyber Intelligence Sharing and Protection Act, forces companies to ignore existing privacy laws and share information with the Federal Government. This short article will bring you up to date on this bill. The CISPA is another bill 'designed' to help prevent thefts and prevent them in cyberspace. But again, like all the previous bill before...

It seems like nowadays, whenever Facebook rolls out a new feature, it's immediately controversial. Social Ads put your name and face in the spotlight, Instant Personalization shared your information with partner sites, third-party apps were allowed to access your home address and phone number, and now Tag Suggestions implement facial recognition software to automatically identify your friends in uploaded photos. Most are calling it problematic or creepy, some insinuate CIA involvement, and it...

Like any good video game these days, controversy is a must, and that's exactly what Homefront provides. It's a good old-fashioned, controversial hot potato—isn't that the way war always is?