In this video, we learn how to build a nest box and ladder for a chicken coop. Start off by creating the box with several pieces of 2x4's. Measure each piece individually, then screw them into place. Make sure it's the size that you want it and that it's secure and lays flat on the ground. Once finished, you will bend some metal and place it on the sides of the coup and then fasten the hinges so they are free swinging. Then, pull in a few more piece and you will have created the nest box insi...

A bird's nest is the symbol of life, new life, family, and unity. So the motif makes for an excellent pendant to wear around on a necklace, earrings, or bracelet. But don't go to the store and waste your money on name brand jewelry with this pretty motif.

"The Cuckoo's Nest" is an old song from the 14th century, according to some sources. There are many variations on "The Cuckoo's Nest". Learn how to play "The Cuckoo's Nest on the guitar with this tutorial. This is a traditional version of "The Cuckoo's Nest" played in folk dance style. This song is normally played in D, but this version is voiced in G and capo'ed on the 2nd to give it a lighter sound, so it is actually played in A. With this how to video you will be able to play the tradition...

In this ASP.Net video tutorial, Chris Pels will show how to use nested master pages to create individual master pages that represent different standard content layouts for a web site. First, see how several major commercial web sites use a standard set of content layouts. Next, see how to nest a master page within another master page, and use the design time support in Visual Studio 2008. Then, learn the considerations for establishing a “page architecture” which represents the major types of...

This is a glitch walkthrough to find the Pelican in the bottom of the crow's nest. Its shows how to get to the bottom of crow's nest and get on that random pelican.

Rick Steinau with Ask the Exterminator demonstrates how to prevent yellow jackets from nesting in your home's walls. In mid to late summer yellow jacket populations increase. Yellow jackets can find spaces in the veneer or in cracks in bricks or siding. You can hear scratching noises in your walls as the wasps move. Observe wasp activity late in the day when they return to their nest for the night. Treat reachable holes with pesticide dust and a bellows. Leave the hole open to let the wasps f...

For Lemon Meringue Nests you will need the following: Some ready made meringue nest,

In this clip, you'll learn how to sort your Google Gmail inbox by creating nested labels—in other words, a label within a label. For all of the details, and to learn how to create nested labels yourself, take a look.

Ant problem? If the ants have come marching two by two—or, God forbid, 10 by 10—it’s time to put an end to the parade. Here’s how. How to get rid of ants, a guide by Howcast:

This is just a short climbing tutorial that demos what happens just after you go into the crevasse. Ditching the pack is easy if you have pre-hooked the pack to harness. The nest step is securing yourself with a prussik and getting it ready to use as a stirrup. But as we see, practice practice practice. Check out this instructional climbing video that offers some self rescue tips from a crevasse while climbing. These are good safety tips and procedures to learn.

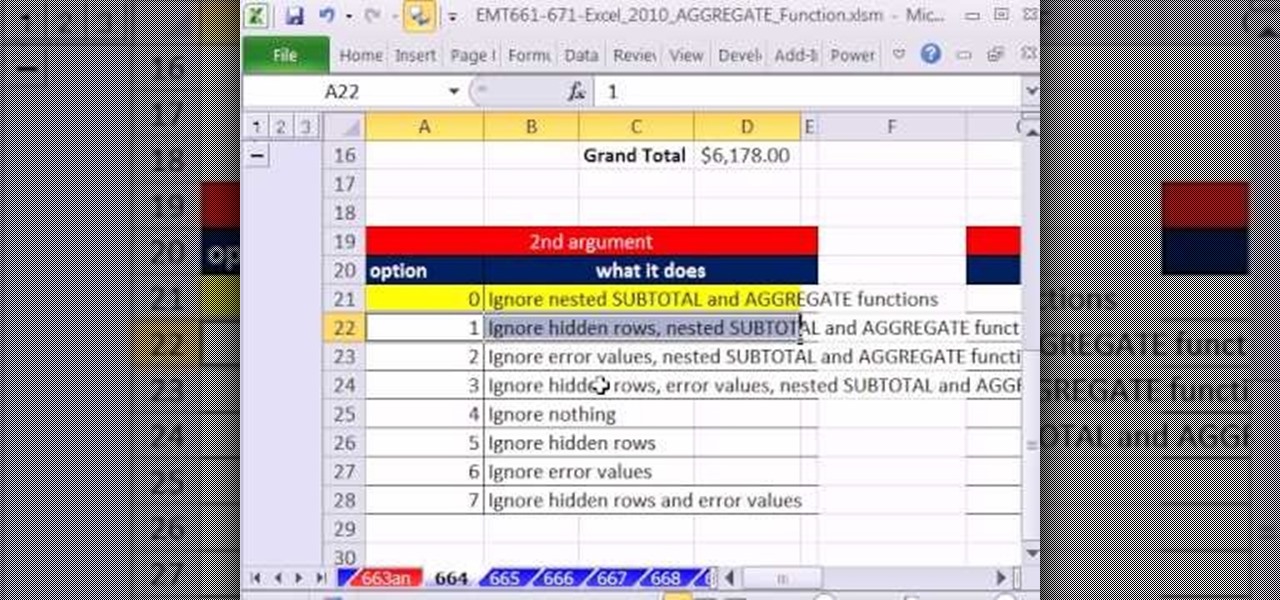
New to Microsoft Excel? Looking for a tip? How about a tip so mind-blowingly useful as to qualify as a magic trick? You're in luck. In this MS Excel tutorial from ExcelIsFun, the 664th installment in their series of digital spreadsheet magic tricks, you'll learn how to make a calculation on a column of values that contain subtotals that you do not want to include in the calculations. The AGGREGATE function will ignore nested SUBTOTAL and AGGREGATE functions when making calculations.

Give a bird a home with help from this handyman tutorial! Learn step-by-step how to build a professional looking Bluebird nesting box bird house. To build this nesting box you will need the following tools & materials: rough cedar or pine, a tape measure, pencil, speed square, hand saw, compound miter saw (if possible), exterior wood glue, drill bits, screw gun or drill, paddle bit, coarse thread drywall screws, deck screws, galanized finished nails, and a hammer.

Freelance web developer and Internet marketer David Frosdick offers some tips and tricks in this video tutorial on how to secure your Gmail account.

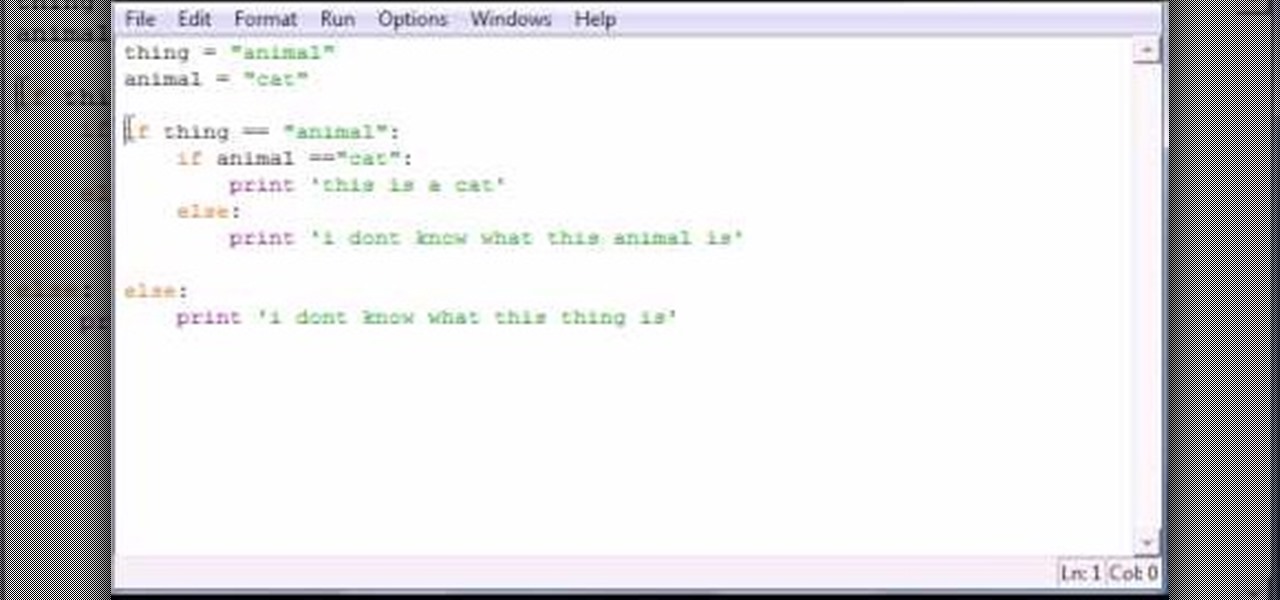
Bucky from The New Boston serves up this Python video tutorial on how to program nesting statements in Python. This is the program you use to write all of your Python code down. Nest a simple "if" statement!

Nothing ruins a romantic fresh air picnic like the buzzing of angry yellow jackets—especially since, unlike the useful honey bee, they can use their stingers over and over again... Learn how to deal with bees without getting stung. This instructional video from Howcast offers tips on handling yellow jackets.

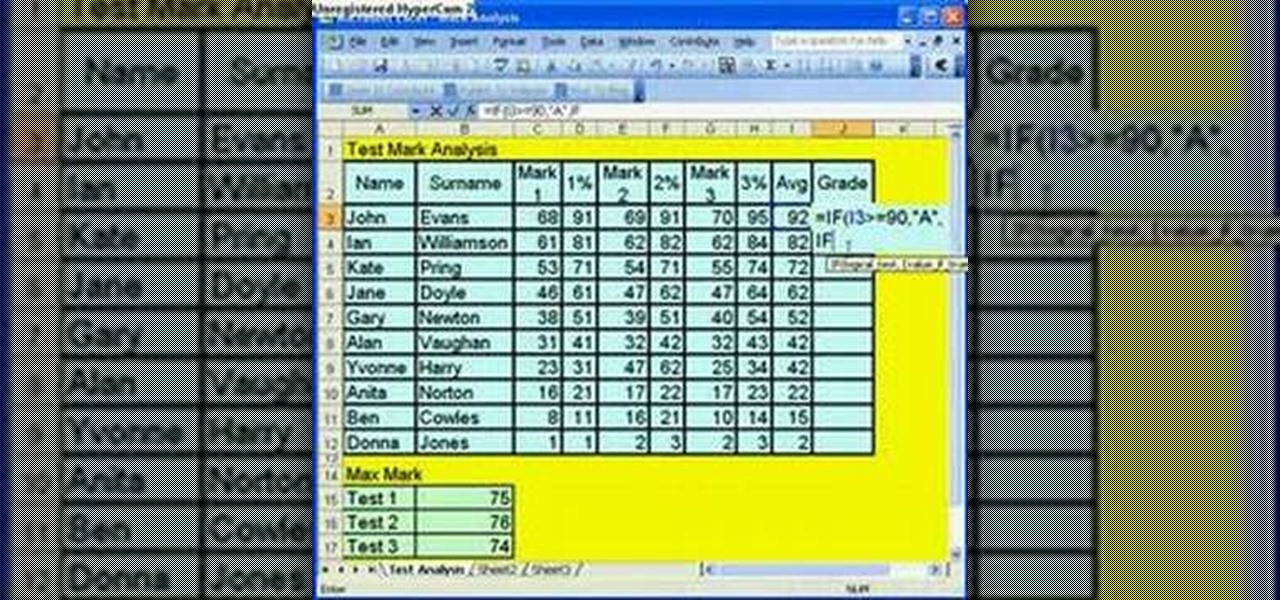
Microsoft Office Excel 2007 spreadsheet manager is a powerful tool that enables information workers to format spreadsheets, as well as analyze and share information to make more informed decisions. In this MS Excel video tutorial, you'll learn about using nested IF functions to calculate a grade from an average mark. For more information on using conditional statements, watch this MS Excel how-to.

Microsoft ASP.NET is a free technology that allows programmers to create dynamic web applications. ASP.NET can be used to create anything from small, personal websites through to large, enterprise-class web applications. All you need to get started with ASP.NET is the free .NET Framework and the free Visual Web Developer. Using Visual Studio 2008's improved Designer, this video will demonstrate how to create a Nested Master Page. Nested Master Pages are useful when you build a hierarchy of te...

In this episode of Halo 3 Tricks we show you how to get out of Crow's Nest using the Phantom.

This demonstrates how to make a pair of birds in a nest with piece of paper and a sharpie. The excellent lighting and high quality video make it easy to follow the folding patterns. At the end, it even shows you how to make the birds a little bit 'naughty'.

Hello! I would like to share some data about the nests that rabbits and dwarf rabbits build. They represent good shelters for them and their babies.

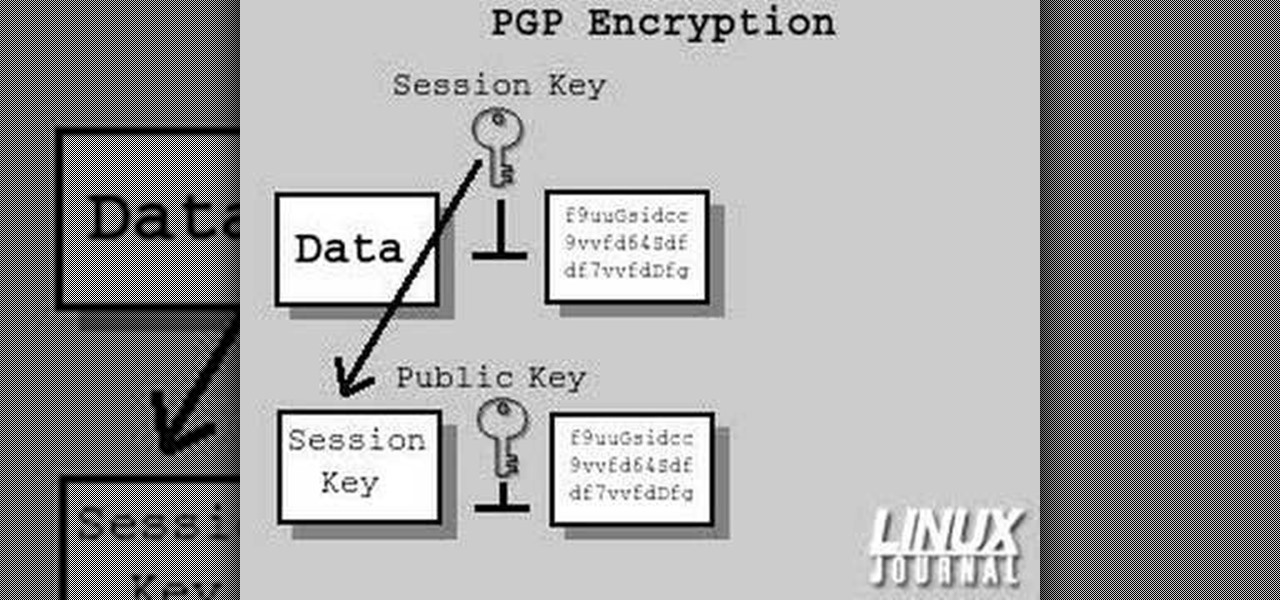
In today's time of rampant IT crimes, including identity theft, security is more important to the average computer user than ever. This tutorial, which was recorded and encoded for the Internet usingly only open source tools, demonstrates how you can use GnuPG to secure and verify data on your GNU/Linux box. Secure your Linux computer with this how-to.

Why should women get all the pretty hats at Easter time? You can make a fun and seasonal Easter hat for a boy quite easily! This video shows you how to take a plain hat and turn it into a birds nest hat. You will need: a hat (a plastic party fedora will work just fine), a wide strip of ribbon for the brim, a pair of scissors, some raffia, artificial leaves, a stuffed or toy bird and some craft glue.

In this tutorial, we learn how to use salty hashes to keep passwords secure. A hash is stored in a database that is hashed with an algorithm, so not everyone can see exactly what your password is. When you type your password into a website, it doesn't actually register as words, it registers as a hash. This keeps your passwords secure so not everyone can see them. Salting is when you use random pits and attaching them to your regular hashes so not every password is the same. The salt is what ...

This hair tutorial is called a wispy bird's nest after its, well, wispy quality and organized jumble of hair strands that forms into a cohesive whole.

Having a secure password is essential in today's interconnected world. Hackers are just around the corner, and if you have an easy to guess or hack password that you use for all of your accounts, someone can login to all of your websites very easily. Look at this guide on how to create a strong password by following the right password rules so that your accounts stay secure.

This new episode of Full Disclosure shows you how to use a SSH Tunnel to secure your data when you are on an untrusted LAN (ex. Coffee Shop, School's network, or Defcon). Furthermore, you can use the SSH Tunnel to bypass the LAN's internet filters. The SSH tunnel protocol works by encapsulates your data into an encrypted payload and transmitting it to the SSH Server which is setup on a trusted LAN.

In this clip, you'll learn how to get started using Secure Computing's Secure Web Protection proxy service. It's easy! So easy, in fact, that this helpful how-to can present a complete overview of the app in just over five minutes. For more information, including detailed, step-by-step instructions, take a look.

In this tutorial, we learn how to get big teased hair. To start, you will need to section off the top of your hair from the crown area. Then, you simply hold the section of hair you want to tease in the air. From here, you will take your comb and brush the root of the hair up against the way it grows. This will create a nest of hair on the root of the hair. When you have enough volume in the nest, continue to do this all the way around your head until you have the volume you need all over. Co...

In this video tutorial, viewers learn how to secure a home wireless network. There are 3 types of security protocols for connecting devices. The 3 types of security protocols are: OPEN, WEP and WPA. Users should use passwords that are secure but no so obscure that they are unusable. The password should not be dictionary words. They should be mixed with casing and contain the user's phone number. Go to your router's website and log into the website. Find the setting for wireless security and e...

Have important files that you want to put on a USB drive but do not want anyone else to be able to access them? Put a password on it using USBSecure.net free resource.

Use three tools to create a simple ponytail. Use a hairbrush, a bobby pin, and a bungee band holder for this look. Using a bungee band instead of a standard ponytail holder eliminates some of the issues typically caused by pulling hair through ponytail holders. Start by using a bristled brush to brush the hair to one location on the head. Secure one hook of the bungee band in the ponytail and wrap the tail around the rest of the hair. Wrap it around again, and secure the other bungee band hoo...

Using ASP.NET Secure Services and Applications Services

Need to know how to tie a Bowline with a few ways of securing it? This way shows you how to secure it with a seizing so that it won't accidentally come undone. Included is a little variation of the bowline with a built-in seizing. If you don't have electrical tape to secure the bowline feed the bitter end back through the hole. It also makes it so you don't have a tail line dangling if you're towing something.

In today's time of rampant information crimes, including identity theft, security is more important to the average computer user than ever. This tutorial from Linux Journal Online shows how you can use GnuPG to secure and verify data on your Linux box. (This video was created using only free and open source software tools: TightVNC, pyvnc2swf, ardour2, audacity, jackd, LAME, kolourpaint, cinelerra-cv, mjpegtools, and ffmpeg.)

Here at the nesting labs, we take on all kinds of esthetic experiments. This week we morph a old lamp into a brand new lace lamp shade. Using vintage and recycled materials we create a lovely, new accessory for the home. Then we take a trip on over to the New York nest of the tidiest bachelor. Learn how to revamp a lamp shade with lace by watching this video interior design tutorial.

Buns and updos are gorgeous hairstyles, with one caveat: If they're not pinned perfectly and securely in place, all your hard work braiding and curling will go to waste as your hair slowly unravels.

Are you secure when downloading security software? Sounds like quite the conundrum, but CNET has answers. See if you're really secure when getting that software, and telling the difference between a rogue antivirus website versus a legit site. See how not to get scammed and destroyed!

In this tutorial, we learn how to lash a bamboo tripod. First, you will tie a clove hitch by taking one piece of bamboo and wrapping the rope around it, then crossing the two sides of the string together to make a hitch. Next, you will secure the clove hitch around the third piece of bamboo. Now, you will rap all the pieces of bamboo together with the rope. Continue to do this until all the pieces feel secure together. Wrap the rope several times around each of the pieces, then wrap it in the...

Picking a secure password is not only important for protecting your privacy, it's also very easy. Provided, that is, that you know how to go about it. This free video lesson from CNET TV will walk you through the process. For more information, and to get started creating and using high-security passwords yourself, watch this video tutorial.

Kandee, a makeup, artist demonstrates a Gwen Stefani up do that was from an Elle magazine cover. Rub hair paste into your hands and smooth it through your hair. Then section crown to forehead and twist it counterclockwise until it starts curling up. Keep twisting and wrap it around into a tight knot. Use a bobby pin to secure it at the base. Then take another section of hair and repeat. Split the bottom section of hair that is left asymmetrically and twist each of those sections halfway and t...