Hot Posts

How To: Make Your iPhone Do All Your Talking for You on Calls and in Person
When you don't feel like talking, let your iPhone do all the work. Yes, your iPhone can speak for you, and it works over phone calls and FaceTime calls. It will even work its magic over your iPhone's speaker for in-person conversations. While Apple created this feature to support people who are unable to speak and people who have lost or are losing their speech abilities, anyone can use it.
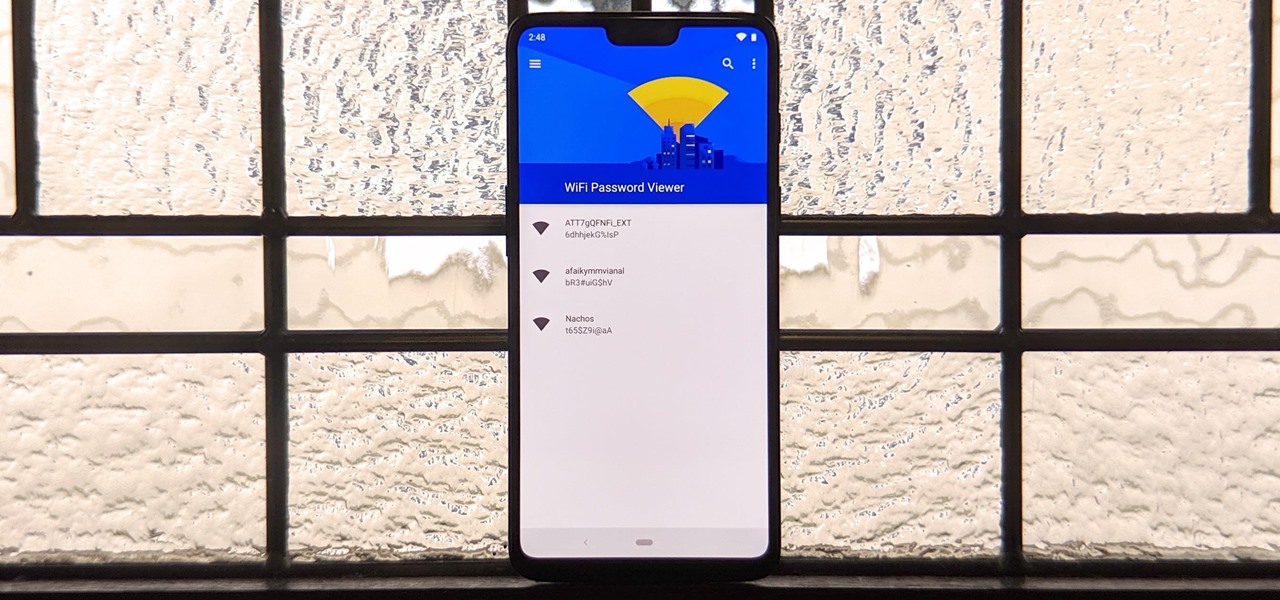
How To: See Passwords for Wi-Fi Networks You've Connected Your Android Device To
You've probably connected your Android device to dozens of Wi-Fi networks since you've had it, and your phone or tablet remembers each of them. Whether it's a hotspot at home, school, work, the gym, a coffee shop, a relative's apartment — or even from a friend's phone — each time you type in a Wi-Fi password, your Android device saves it for safekeeping and easy access later.

How To: Use FaceTime's Secret Hand Gestures and Reaction Buttons to Add Animated On-Screen Effects to Your Video Feed
Apple's Messages app has long had visual effects you could apply manually after long-pressing the send button, and there are even hidden keywords you could use to trigger full-screen effects automatically. FaceTime's latest update also gives you some full-screen effects to play around with during video calls, but the triggers are an entirely different concept — hand gestures.

How To: Make Spoofed Calls Using Any Phone Number You Want Right from Your Smartphone
Spoofed phone calls originate from one source that's disguising its phone number as a different one, and you probably get these calls all the time. Maybe they're numbers from your local area code or for prominent businesses, but the callers are just hijacking those digits to fool you into picking up. Turns out, making a spoofed call is something anybody can do — even you.
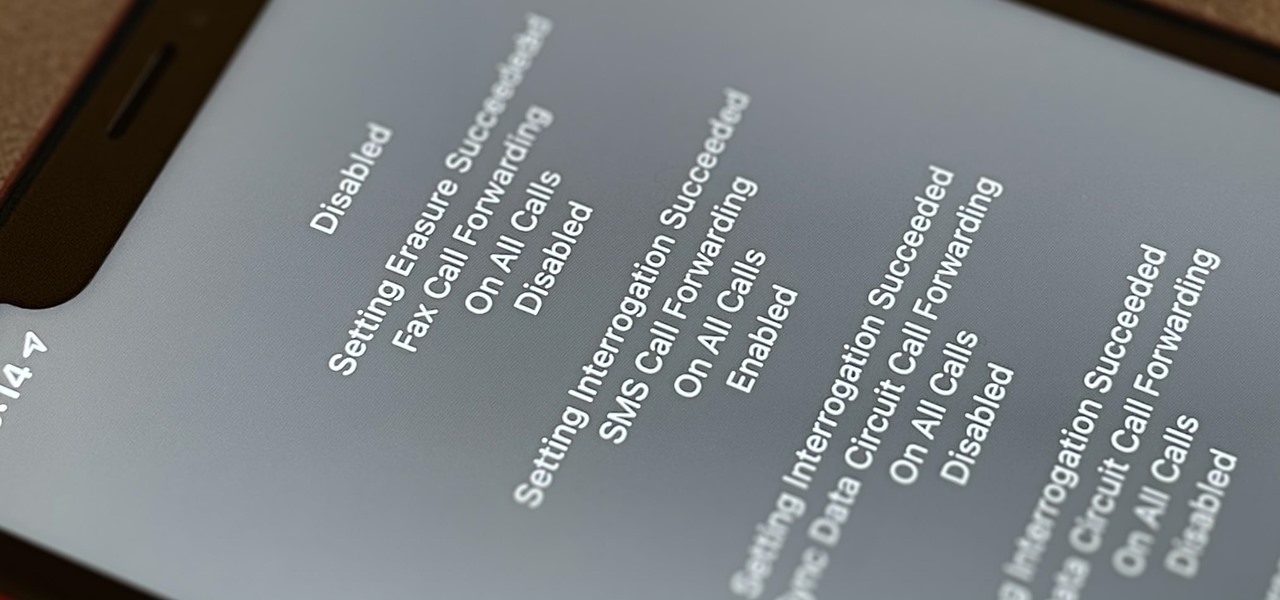
How To: Dial These Secret Codes to See if Someone Is Hijacking Calls & Texts on Your iPhone
Malevolent hackers can divert your incoming calls and texts to any number they want, and they don't need to be a criminal mastermind to do it. Even friends and family members can reroute your incoming calls and messages so that they know exactly who's trying to reach you, and all it takes is seconds of access to your iPhone or wireless account. These secret codes can help uncover them.

How To: The Messaging Trick You Never Knew You Needed
Whether you're wielding an iPhone, iPad, Mac, Android phone or tablet, or even a Windows PC, this little-known secret holds the key to effortless assistance and unwavering obedience. Intrigued? I thought so.
How To: 7 Hidden iPhone Apps You Didn't Know Existed
Your iPhone has hidden apps that work behind the scenes to filter SMS messages, trust computers, deal with payments, test ads, and perform other actions. You won't find any of them in your App Library, but there are tricks you can employ to unlock and use some of these secret apps.

How To: Keep Your Night Vision Sharp with the iPhone's Hidden Red Screen
Night Shift, Dark Mode, Reduce White Point, and Zoom's Low Light Filter all help reduce the harmful effects on your body's clock that bright iPhone and iPad screens have at night. But there's another option on iOS and iPadOS that turns your entire display red, and it's useful for so much more than just late-night browsing in bed.

How To: Find Vulnerable Webcams Across the Globe Using Shodan
Search engines index websites on the web so you can find them more efficiently, and the same is true for internet-connected devices. Shodan indexes devices like webcams, printers, and even industrial controls into one easy-to-search database, giving hackers access to vulnerable devices online across the globe. And you can search its database via its website or command-line library.

How To: Hack Apache Tomcat via Malicious WAR File Upload
Web applications are a prime target for hackers, but sometimes it's not just the web apps themselves that are vulnerable. Web management interfaces should be scrutinized just as hard as the apps they manage, especially when they contain some sort of upload functionality. By exploiting a vulnerability in Apache Tomcat, a hacker can upload a backdoor and get a shell.

BT Recon: How to Snoop on Bluetooth Devices Using Kali Linux
While many people may use Bluetooth every day, the majority don't know how it works or that it can be hacked. Bluetooth hacking gives a clear window into the world of the target. Nearly every device has Bluetooth capabilities, and people store a great deal of personal info on their phones and tablets. Hack their Bluetooth connection, and you may be able to access all of that data.
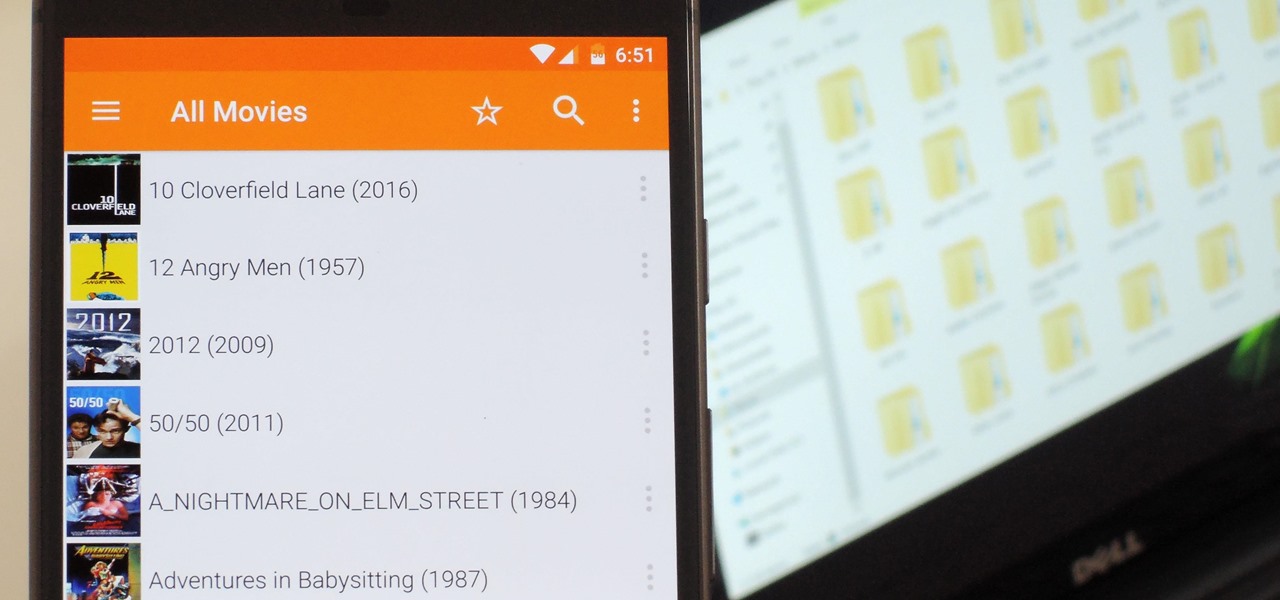
VLC 101: How to Stream Movies from Your Computer to Your Android Phone
Even though your phone has a built-in media player, it's got nothing on VLC. The popular third-party video player supports virtually every codec and file format, and even better, you can use it to stream movies, shows, and other video files from your computer to your phone.

How To: Find Identifying Information from a Phone Number Using OSINT Tools
Phone numbers often contain clues to the owner's identity and can bring up a lot of data during an OSINT investigation. Starting with a phone number, we can search through a large number of online databases with only a few clicks to discover information about a phone number. It can include the carrier, the owner's name and address, and even connected online accounts.
Android Basics: How to See What Kind of Processor You Have (ARM, ARM64, or x86)
Starting with the release of Android Lollipop, the process of installing the Xposed Framework got a bit more complicated. Not only are there separate installers for each Android version, but now, you also need to know exactly what type of processor is in your device to make sure you're downloading the right files. In fact, CPU architecture is becoming a factor in more and more scenarios these days, including certain sideloaded app updates and, of course, custom ROMs.

How To: Disarm a Manipulative Sociopath
There are a lot of manipulative people out there, but you don't have to let all of them push you around. It's time for the tables to turn.

How To: Trigger iMessage Effects with Just a Keyword
One of the coolest aesthetic features of iMessage is its animated message effects. If you're like many users, you might even have discovered them by accident, where wishing your friend a "Happy Birthday!" or congratulating them on a promotion unexpectedly flooded your screen with balloons or confetti.

How To: Spy on Traffic from a Smartphone with Wireshark
So you want to know what that person who is always on their phone is up to? If you're on the same Wi-Fi network, it's as simple as opening Wireshark and configuring a few settings. We'll use the tool to decrypt WPA2 network traffic so we can spy on which applications a phone is running in real time.

How To: 19 Harry Potter Spells Your Android Phone Can Cast Using Google Assistant
Apple's Siri is well-versed in the spells of the Wizarding World of Harry Potter, but it's not like Android users are Muggles. Google Assistant, Android's virtual concierge, can cast a few spells out of the box, and it can learn the spells it doesn't know quicker than a year of studying at Hogwarts.

How To: Hack Wi-Fi Networks with Bettercap
There are many tools out there for Wi-Fi hacking, but few are as integrated and well-rounded as Bettercap. Thanks to an impressively simple interface that works even over SSH, it's easy to access many of the most powerful Wi-Fi attacks available from anywhere. To capture handshakes from both attended and unattended Wi-Fi networks, we'll use two of Bettercap's modules to help us search for weak Wi-Fi passwords.
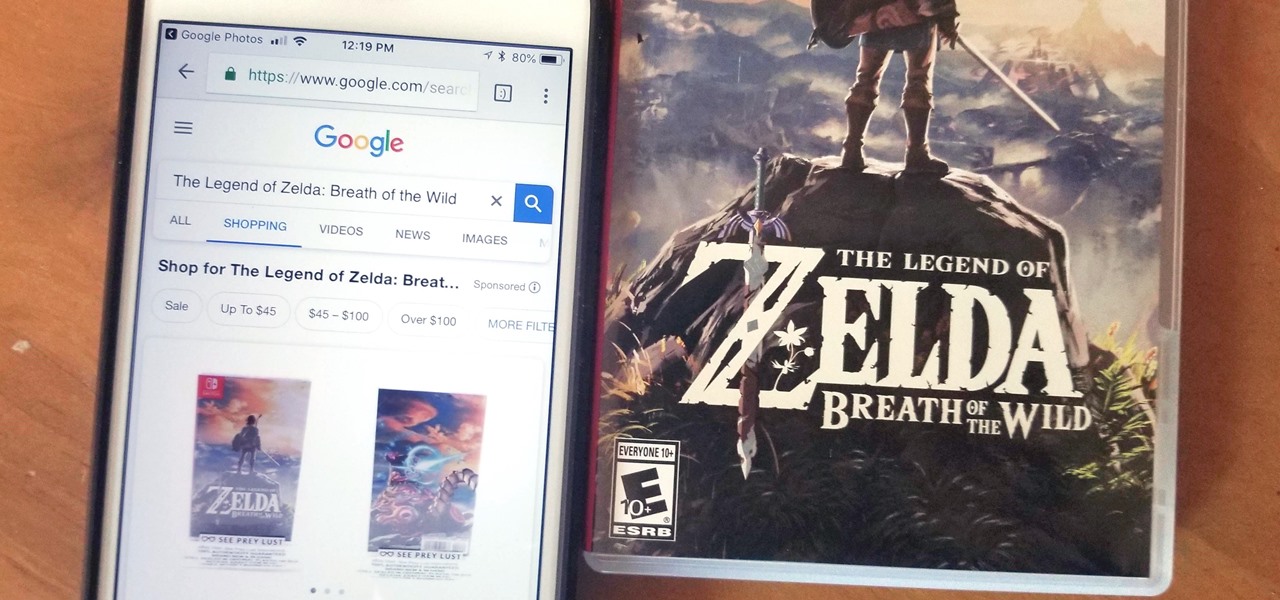
Google Photos 101: How to Track Down & Buy Anything in Your Pictures with Google Lens
Google Lens is a fantastic addition to Google Photos for Android and iOS that allows your smartphone to identify a number of things in your pictures, like landmarks and contact info. Using this power, you can even find out how to buy almost any product you've taken a photo of — you don't even need the barcode.

How To: Steam Food Without a Steamer Basket
I'm not a big fan of single-use tools, especially ones that don't get used particularly often. And I'm especially not a big fan of seldom used single-use tools that take up a large amount of space.
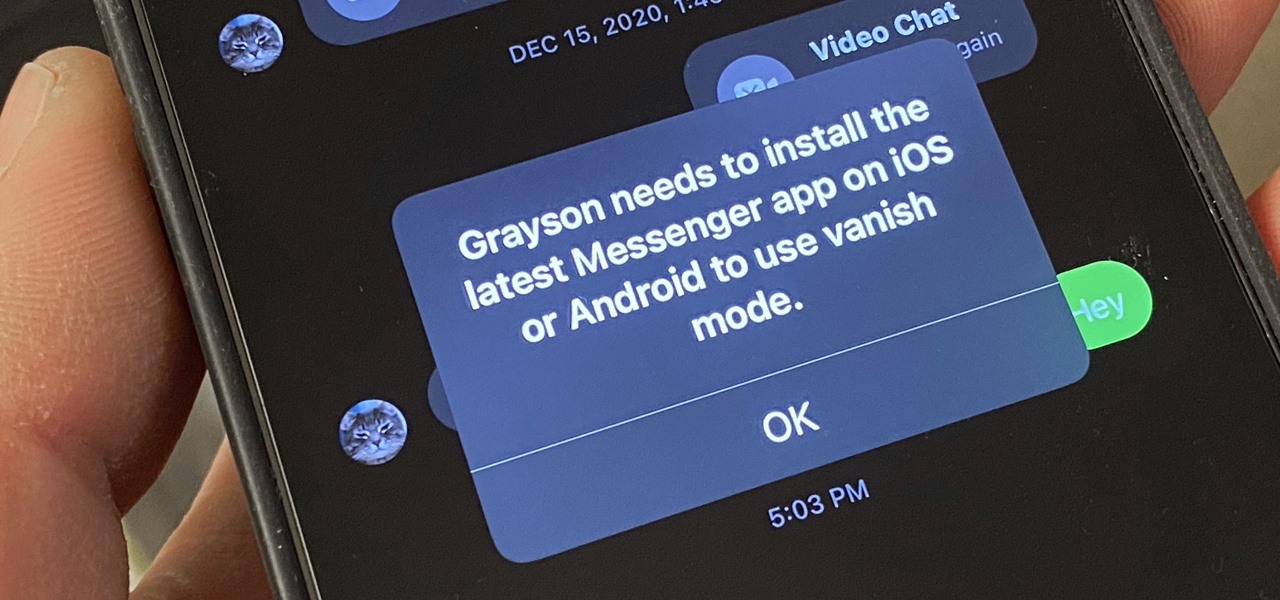
How To: Disable Vanish Mode in Facebook Messenger & Instagram
Facebook recently implemented "Vanish Mode" into Messenger and Instagram, which lets you have an end-to-end encrypted conversation in a chat that will disappear as soon as you leave the thread. As cool as it sounds, it's easy to enable accidentally, and a friend could force you into using it. In some cases, that may not be ideal since everything you or the recipient said will disappear.

How To: Knit with a serenity loom
This video demonstrates how to knit with a serenity loom. A serenity loom can produce a blanket up to 10 feet. To start, thread a double loop of thread through a straw. Then use the loop of thread to pull through a piece of yarn. The straw will help you place the yarn around the pegs of the loom easier. Tie a loop around the anchor of the inside of the loom. Then loop completely around each peg, being sure to place the loops in the middle of the pegs consistantly. Wrap as far as you want your...

How To: Dox Anyone
Doxing is the act of finding one's personal information through research and discovery, with little to no information to start with. You may have seen doxing in the news, for instance when not so long ago, hacker team Anonymous doxed and reported thousands of twitter accounts related to ISIS. Doxing can be useful for finding the address of a coworker, or simply investigating people on the internet. The tutorial I will provide to you now will teach you the basics of doxing and how you can prot...

How To: The Trick That Lets You Link to Specific Start Times in YouTube Videos Right from Your Phone
You can add a timestamp to any YouTube video in just a few clicks from the desktop website on your computer but not from YouTube's iOS or Android app. Until YouTube adds a "start time" when sharing videos from the mobile app, you'll have to use one of these workarounds on your phone or tablet.
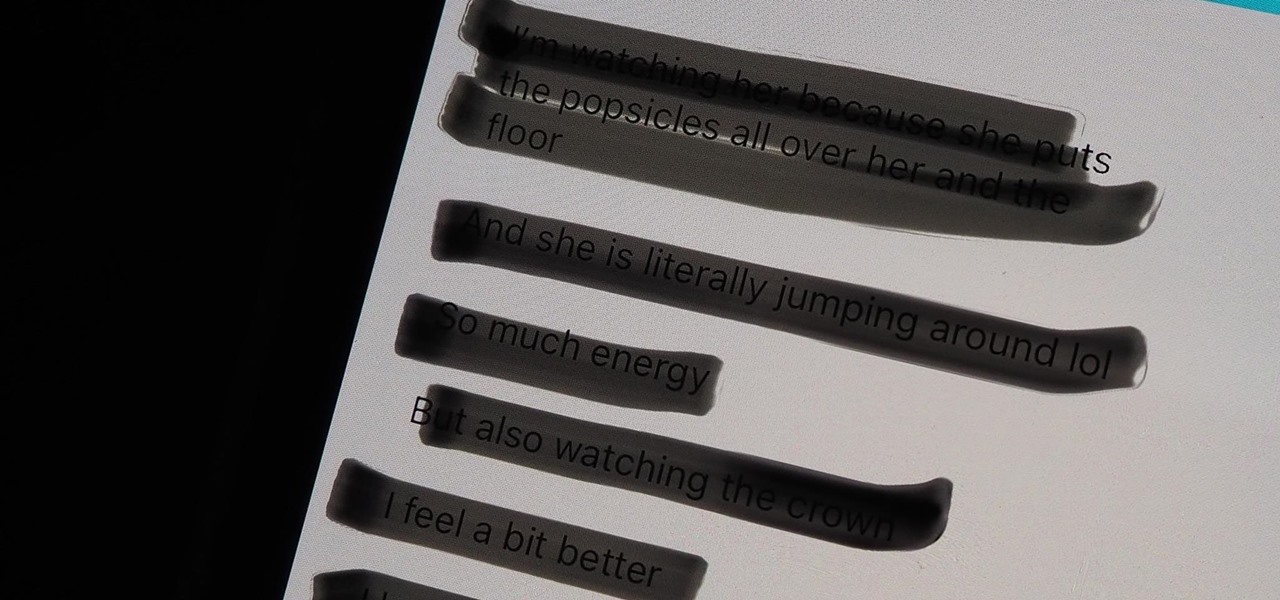
Warning: Sensitive Info You Black Out in Images Can Be Revealed with a Few Quick Edits on Your iPhone
These days, most images we post online or share with others come from our smartphones. Whenever personal data is in them, such as debit card numbers, addresses, phone numbers, passwords, and other sensitive information, it's easy to jump into your iPhone's markup tools to black out the text before sharing. But a digital marker may not hide everything.

How To: Create an Admin User Account Using CMD Prompt (Windows)
This is a quick tutorial on how to create a new administrator account on a Windows computer. Step 1: Open CMD Prompt...

How To: 16 Harry Potter Spells for Siri That Turn Your iPhone into a Magical Elder Wand
Your days as an ordinary Muggle are over — as long as you have an iPhone. With just a word or two, you can use your iPhone and newfound Muggle-born powers to cast spells or utilize charms just like Harry Potter and team. Only your "wand" is from Apple, not Ollivanders in Diagon Alley.

How To: Crack Password-Protected Microsoft Office Files, Including Word Docs & Excel Spreadsheets
Microsoft Office files can be password-protected in order to prevent tampering and ensure data integrity. But password-protected documents from earlier versions of Office are susceptible to having their hashes extracted with a simple program called office2john. Those extracted hashes can then be cracked using John the Ripper and Hashcat.

How To: Check if Your Wireless Network Adapter Supports Monitor Mode & Packet Injection
To hack a Wi-Fi network, you need your wireless card to support monitor mode and packet injection. Not all wireless cards can do this, but you can quickly test one you already own for compatibility, and you can verify that the chipset inside an adapter you're thinking of purchasing will work for Wi-Fi hacking.

How To: Make Siri Say Whatever You Want Every Time You Connect Your iPhone to a Charger
Whenever your iPhone's ringer is on, you'll hear Apple's iconic "Connect Power" chime every time you connect it to a wired or wireless power source, which lets you know that charging has started. There's no way to disable the sound without turning on Silent mode, but there is a way to make Siri automatically say whatever you want after a successful connection.

Redstone Logic Gates: Mastering the Fundamental Building Blocks for Creating In-Game Machines
Many people get so discouraged by their failures with redstone that they give up using it entirely, or never progress beyond using simple switches. However, by incorporating logic gates into your redstone designs, the applications are nearly limitless. The ability to add multiple switches to your machines is just a small part of what logic gates can do. Most importantly, they give you control.

How To: Crack a Combination Bike Lock in Under 30 Seconds
Have an old bike combination lock that you can't remember the code for? If it's a simply four-digit cable lock, you can easily figure out the combination with a quick peck-and-go method. Best of all, this technique doesn't require any tools or special know-how, and let's you reuse the cable lock again versus just damaging it with bolt cutters. All you need is a bit of patience and you'll have your figure out your combo in no time.
How To: 27 New Features and Changes Coming to Your iPhone with iOS 17.5
Apple released iOS 17.4 on March 5 with over 30 new features, but now it's iOS 17.5's turn for the spotlight. The update, currently in beta, gives us a few interesting updates and changes for iPhone, including a new word game, and there's even a sneak peek at what could be coming in the stable build.

How To: Roll Sushi—The Ultimate Guide
Sushi rolls, known as makizushi in Japanese, are only limited by your imagination—and your ability to roll them neatly, of course. While it may seem like a lot of effort, rolling sushi is a snap if you have the right tools.

How To: Scrape Target Email Addresses with TheHarvester
Open-source data scraping is an essential reconnaissance tool for government agencies and hackers alike, with big data turning our digital fingerprints into giant neon signs. The problem is no longer whether the right data exists, it's filtering it down to the exact answer you want. TheHarvester is a Python email scraper which does just that by searching open-source data for target email addresses.

Gaslighting 101: How to Turn People's Own Thoughts Against Them
This is evil and it destroys people. Let's just get that out of the way. Nonetheless, suppose you need to make someone distrust their own memory and perception of reality. Suppose you want someone to believe in you more than they believe in themselves.

How To: 20 Surprisingly Practical Uses for Apple AirTags
Apple AirTags are super helpful for keeping track of your keys, backpack, and other frequently misplaced items, but there are some pretty clever things you can do with them beyond finding your stuff.

How To: Hack Coin-Operated Laudromat Machines for Free Wash & Dry Cycles
Most people have had the unfortunate experience of not having a washer and dryer at some point. Apartments in my area tend to charge at least one hundred dollars extra for the units with washer and dryer hookups, and even more if you want a unit with an actual washer and dryer installed already. If you are young and just starting out, this may be hard for you to manage with your current salary. If you have no washer and dryer, the only alternative is the laundromat.

How To: Apple Has a Killer New Word Game Puzzle Called Quartiles Hiding on iOS 17.5
Apple's next software update, iOS 17.5, is relatively minor. Still, it includes one killer new feature for people who like word games: another lexical challenge to complement the crossword puzzles that Apple News already has.