Following through with discipline is the best way to get your kid to behave. Don't threaten to throw child's toys away if they don't clean up. A follow through would be to throw the toys away! Avoid empty threats when disciplining children.

Your Android phone could be listening to ultrasonic ad beacons behind your back. The unwelcome news comes year after app developer SilverPush promised to quit using its (creepy!) eavesdropping software.

Growing a garden isn't a walk in the park. Besides watering the plants and choosing the right kind of soil, one of the biggest threats is also one of the smallest. Bugs can be a major factor when planting certain fruits or veggies in a garden and should be taken care of as soon as possible.

In order to keep your PC safe from annoying or potentially dangerous threats on the Internet, a properly-configured firewall is a crucial item in helping prevent your system from becoming compromised. The Windows Firewall in Windows Vista™ is the first line of defense in helping to keep your computer safe. By preventing your computer from being infected by malware, Windows Firewall is designed to be easy to use and is automatically enabled to protect your computer as soon as Windows starts. T...

There are many threats to be wary of when playing Terraria. If you'd like to be able to feel safe from a couple of them, watch this video and learn how to protect your house during Red Moon events and Goblin Invasions.

Make your way through the Chimera tunnels and find your way to the Stronghold's access point. Once inside eliminate all possible enemy threats. Sounds easy? Just wait!

Watch Ray Mears from the BBC explore the most dangerous threats in the desert--spiders, snakes, and scorpions--with a desert ranger. Learn how to avoid black widows by observing an area before you sit down! Do not "mess with any animals you know nothing about." If stung, stay calm.

Kill in the Defender Shadow Arena Challenge in the Drowned Pass on the Xbox 360 game Darksiders. You need to enter the Shadow Realm and defeat four portals to free Vulgrim.

People like Ralphige and The Jerky Boys have elevated prank phone calls to an art. Here’s how you can get in on the fun.

You may or may not know it, but getting rid of old batteries is a problem nowadays. Buying alkaline batteries from the store can be bad news, since these cannot be reused or even recycled. They end up in land fills and can pose serious toxic threats. Buying recycled batteries from the store is a better way to go, since these guys can be recycled and of course, reused. So check out this tutorial for some more adivce on properly disposing or your batteries. Good luck and enjoy!

This video tutorial from ballader1 shows how to remove viruses, trojans, adware, spyware from your computer.

In this episode, Brandon Jackson shows how to merge two images with the Photoshop gradient tool to create a banner montage. Doug Grammar joins D.Lee Beard again, this time to explain spyware, adware, and keylogging. They explain what these threats to your privacy & computer speed are as well as how to prevent and get rid of them. Speaking of security, Jason Rybicki shows one way to tell if your privacy is being compromised on a Mac using a free widget.

See Licker Beta and the U-8 Boss on this level of RE. See the playthrough for Resident Evil 5: Chapter 5-1, Underground Garden in this three-part video. The ruins appear to be adjacent to a large facility. Perhaps the answers Chris and Sheva seek can be found inside?

If your personal food pyramid replaces “Grains” with “Pizza” and “Fruits and Vegetables” with “Taco Sauce,” it’s time to make some changes.

Learn how to use more English phrasal verbs with this instructional English language lesson. get...over with

The beauty of southern Europe won't protect it from invasions of disease-carrying ticks and mosquitoes—in fact, the Mediterranean climate and landscape may be part of the reason the bloodsuckers are expanding there, bringing unique and terrifying diseases in their wake.

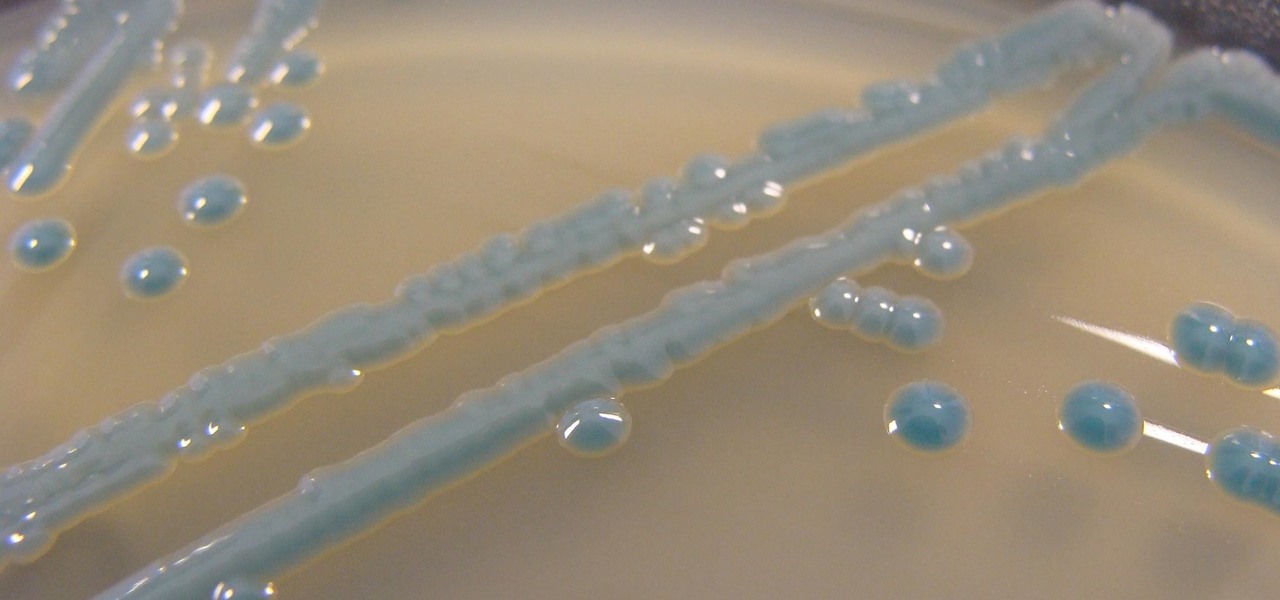
The search is on to find antibiotics that will work against superbugs — bacteria that are rapidly becoming resistant to many drugs in our antibiotic arsenal.

Former Vice President Dick Cheney was so fearful of attacks, he had his heart defibrillator re-calibrated to block incoming wireless signals so that highly skilled hackers couldn't send him into cardiac arrest.

We need to take our privacy and security much more seriously. Whether it's malware-infected apps or the mishandling of our data by companies like Facebook, there are threats all around us in this digital world. Fortunately, some smartphones are simply designed to protect us better.

When it comes to your security, you want the best of the best. Why settle for mediocre service with something as valuable as your protection? Malware continues to make its way onto the Play Store, leaving millions of devices vulnerable. You need an app that will shield your devices from both the latest malware threats and threats nearby. And when it comes to antivirus apps, there is only one choice.

You may have seen news reports over the last two days detailing a major security flaw in virtually all smartphones. The devices that are at risk are not limited to either iPhone or Android — all of us are affected. If you want to make sure your smartphone and its data stay secure, there are a few steps you can take.

Baidu Inc, the "Chinese Google" search engine and technology company, which has been actively pursuing self-driving cars, reported that a gang of hackers recently attempted to steal its driverless car technology.

Hello fellows nullbyters, first of i will start saying that im addicted to this community, i feel the challenge growing up so fast, all the newbies, amateurs,advanced and professionals hackers around trying their best to help the community, badly but we got some script-kids too but anyway, today we are going to learn how to install and use clanAV in kali linux.. INTRODUCTION
Welcome back Hackers\Newbies!

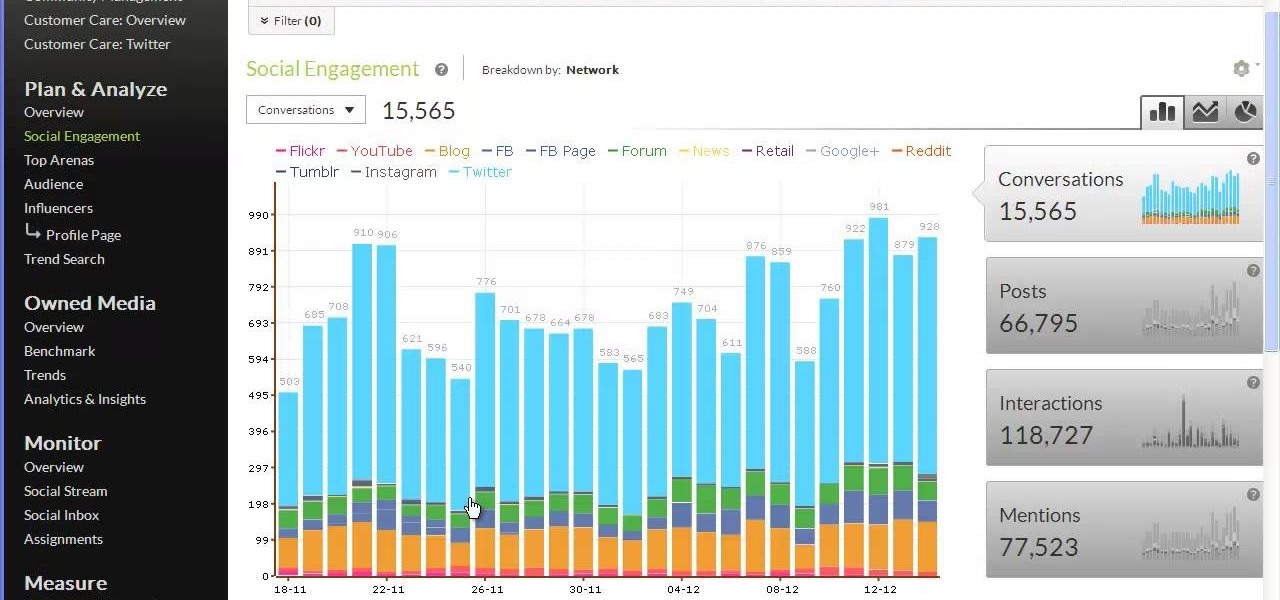
Tracx is a social intelligence software platform that allows enterprises to manage, share and extract actionable insights, threats and opportunities from the social web —in real time.

Wiping our shoes off as we enter the home reduces the amount of contaminated dirt tracked in. Large mats, that cover two or three strides, will ensure that even those that refuse to wipe will leave most of the dirt clinging to their shoes on the mat rather than your carpet.

VPNs add a protective layer between your data and your internet service provider (ISP) or bad actors (hackers), so it makes sense they've become so popular lately. Probably the most common one of these is NordVPN, so we explored its mobile app to find all the options worth checking out.

We're living in uncertain times. The sudden outbreak of the novel coronavirus and subsequent self-isolation of roughly half the world's population has led to a massive reorganization of the economy, countless layoffs, compromised security networks, and a variety of other significant disruptions that will forever alter the landscape of our daily lives.

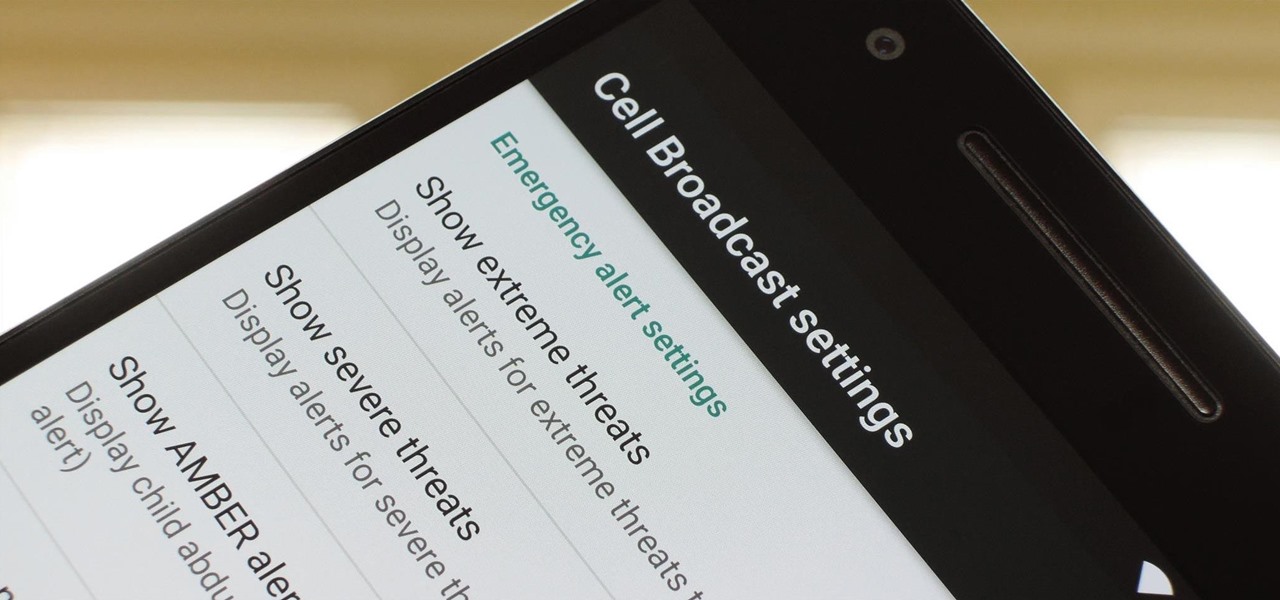
To bring things up to code with a new FCC standard, Android recently added an "Emergency broadcasts" feature that will make your smartphone notify you whenever a potential safety threat or Amber Alert is posted in your area. Even if you have your phone set to silent, these emergency alerts will cause your device to emit a loud, piercing sound when a potential threat is nearby.

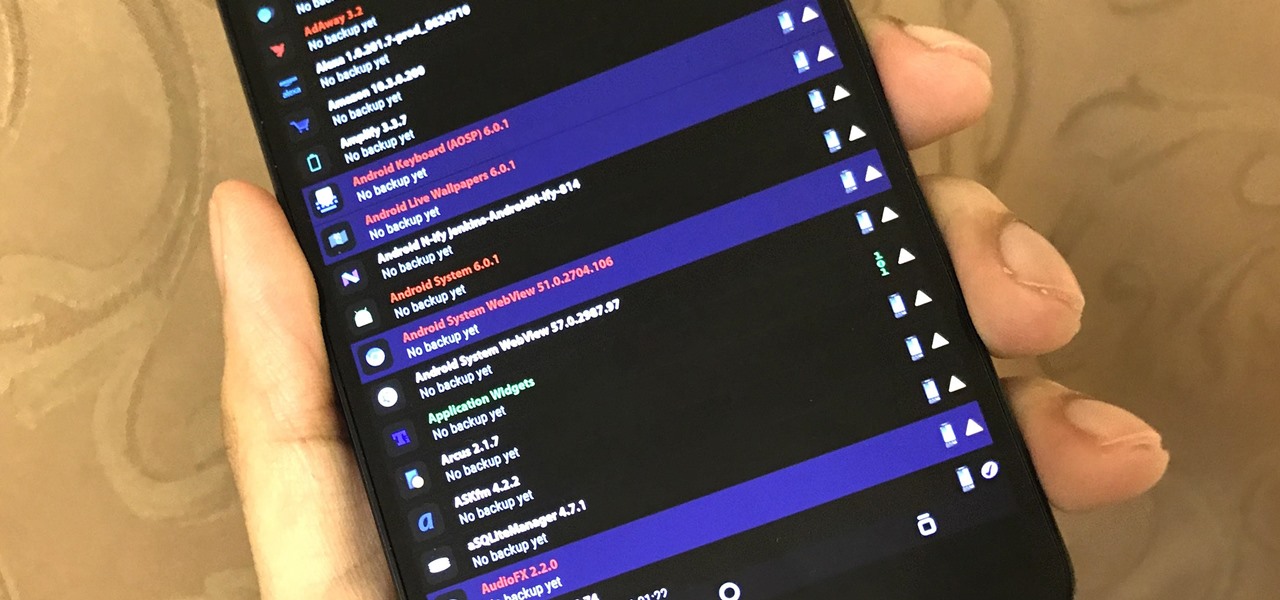
The latest Google Play Services update has somehow broken major functionality in both Titanium Backup and Substratum. Titanium Backup has suddenly become stuck at zero percent while restoring, and Substratum simply fails to apply themes anymore. Both of these apps do require root, but they've slowly become essential to rooted users, especially since apps like these come into play when you're deciding what your next phone should be.

With the recent news that New York County's District Attorney's office is trying to get into over 400 locked iPhones for use in criminal investigations, you can see why it's important to keep other people away from your personal data. The fact that it can and will be used against you in a court of law is just one reason to protect your phone, because even if you make sure to stay above the fray, identity theft and bank fraud are still very real threats.

Amber, emergency, and public safety alerts on an iPhone are loud — startle-you-to-death loud even. They can happen at any time, day or night, and sometimes back to back when you're in a big city. Those blaring sirens can wake you from sleep, interrupt an important meeting, or disrupt an entire movie theater mid-movie, but you can turn most of them off if you're tired of hearing them.

The growing list of dangerous antibiotic resistant organisms has just acquired three new members. Researchers have discovered three new species of Klebsiella bacteria, all of which can cause life-threatening infections and have genes that make them resistant to commonly used antibiotics.

Technology has progressed by leaps and bounds and has blessed people in a number of ways, but at the same time, it has troubled them also. Computers are now used in every aspect of life. No matter if you are a businessman, an employee, a student, or even a housewife, a computer can assist you in your routine work. You save your personal information, documents, and other similar sensitive stuff on your computer that can hurt you if they get compromised.

You encounter this problem many times, when you plug your flash drive, and suddenly you find that all your data has become shortcuts everywhere!!!

There are a lot of things on your computer that can reveal information about you when you are surfing the Internet. If you are like me, then you will do anything to maintain your privacy and prevent those little leaks of information from happening. Here's a list of a few of the "threats" that can reveal information about you:

Despite all the tragic stories you hear on the news, you'll probably never be involved in a shooting. But you never know. Nobody thinks it’s going to happen to them – until it does. Be prepared to survive a shooting rampage, just in case.

As long as you're on the internet, you can be hacked. With an estimated 2.65 billion social media users, these apps are prime targets for hackers.

Most people are familiar with the decline of honeybee colonies around the world. Among other threats, Colony Collapse Disorder (CCD) is eroding the capability of honeybees to maintain their hives and provide their services to human farmers.

The increasingly important world of white hat or "ethical" hacking is getting competitive. Thanks to growing salaries and opportunities for talented and trained coding pros who can infiltrate servers and safeguard networks against digital threats, demand for intrepid cyber warriors is through the roof, and it shows no signs of slowing down any time soon.