Moss can be a beautiful part of natures, but it can also wreak havoc on your roof shingles or garden plants and rocks. If you've got a moss problem, watch this video for some easy ways you can solve them.

Still using the same lightweight, oil-free lotion during the winter as you did last summer? Then it's obvious where your flaky, dry winter skin is coming from. The shift from warmer, more humid days to dry and cold immediately saps your skin of moisture, meaning you have to update your beauty routine to stay moisturized.

Welcome back, my rookie hackers! A short while back, I began a new series on database hacking, and now it's time to continue and extend your education in that field. As you know, the database contains all of the most valuable info for the hacker, including personally identifiable information, credit card numbers, intellectual property, etc. So, it's the ultimate goal of cybercrime and the APT hacker.

The cord on your headphones is usually more enemy than friend. While they obviously need it to function, a tangled or unnecessarily long cord can wreak havoc on your sanity. Personally, I've broken at least two pairs of headphones by tripping over the cord and yanking the jack right off of the wiring. There is a fix for that, but you can prevent the problem altogether by organizing your cords. There are plenty of ways to wrap a cord so it won't get tangled, but you still have to unwrap it if ...

As dedicated bicyclists are well aware, riding can be very dangerous. Now that daylights savings time has ended in the United States, darkness appears quicker, and the night is especially dangerous for cyclists because of the low visibility that drivers have. Not only is darkness a danger, but also fog, blizzards, and heavy rain—all wreaking havoc on the vision. To combat this, bikers attach reflectors: clear front reflectors, red rear reflectors, amber pedal reflectors, and clear side reflec...
Even with so many awesome real life weapons out there that wreak jaw-dropping damage and explosions, boys and men everywhere still grovel at the feet of lightsabers, that mystal (and unfortunately made up) weapon touted by Jedi in the "Star Wars" movies.

Cracks in your shower, if left untreated, can wreak untold water damage. Fortunately, this video tutorial presents an easy-to-follow guide to resealing a shower stall using silicone. For detailed, step-by-step instructions, and to get started repairing your own shower, watch this handy home DIY video tutorial.

This walkthrough guide will cover the complete Overload DLC mission pack for the Mass Effect 2 action role-playing game on the Xbox 360. Overload became available for download in June 2010 on Xbox Live Arcade (XBLA), and features four different missions. Watch this series for all the gameplay action from Mahalo.

Welcome back, my tenderfoot hackers! A number of you have written me telling me how much you enjoy the Mr. Robot series on USA Network. I am also a huge fan! If you haven't seen it yet, you should. It may be the best show on TV right now.

In the winter, the weather can be especially unpredictable. Ice, snow, low temperatures, and high winds can all play havoc on our trees and shrubs and these can be expensive losses. In a two part series, Allen Smith gives some tips on how to protect your garden.

Video: . Connect a piano keyboard or start playing on your computer keyboard right away! Practice one hand at a time, change playback speed, transpose to a different key, create loops to repeat, track your progress and much more. How to Play Guardian by Alanis Morissette - Interactive Piano Tutorial.

While mobile data caps are larger than they used to be, many of us still have limits to contend with. If you find yourself up against that ceiling month after month, your iPhone itself might be to blame. Luckily, there's an easy fix to stop your iOS device from burning through data in the background.

While mobile gaming, in the 10 years since the App Store launched, has matured to console-level quality, premium augmented reality games built with ARKit (or ARCore) have been scarce.

Everyone feels a little safer with Android's security updates, which are welcome and often necessary protective measures. But what happens when the update that's supposed to safeguard your phone actually ends up wreaking havoc with its security system?

If you've ever logged on to the popular music application Pandora, your password is saved onto that computer in the local storage...for good.

This tutorial is one technique to use the full functionality of your Pi. The small size makes it ideal for inside hacks, but still has the capabilities of a average desktop or computer. I should mention that a tutorial that OTW has done, but I'm gonna take it a step further. OTW made a brilliant article, but only touched on the surface of the possibilities. I hope this article will both show you many the possibilities and also allow you to start causing havoc, but I'm planning on making this ...

Street Fighter IV : Blanka, the Brazilian Beast unleashes havoc upon the World Warriors once again. Street Fighter IV is a 2008 fighting game produced by Capcom. Street Fighter IV is currently released for PlayStation 3 and Xbox 360, with a Microsoft Windows version in the works as well.

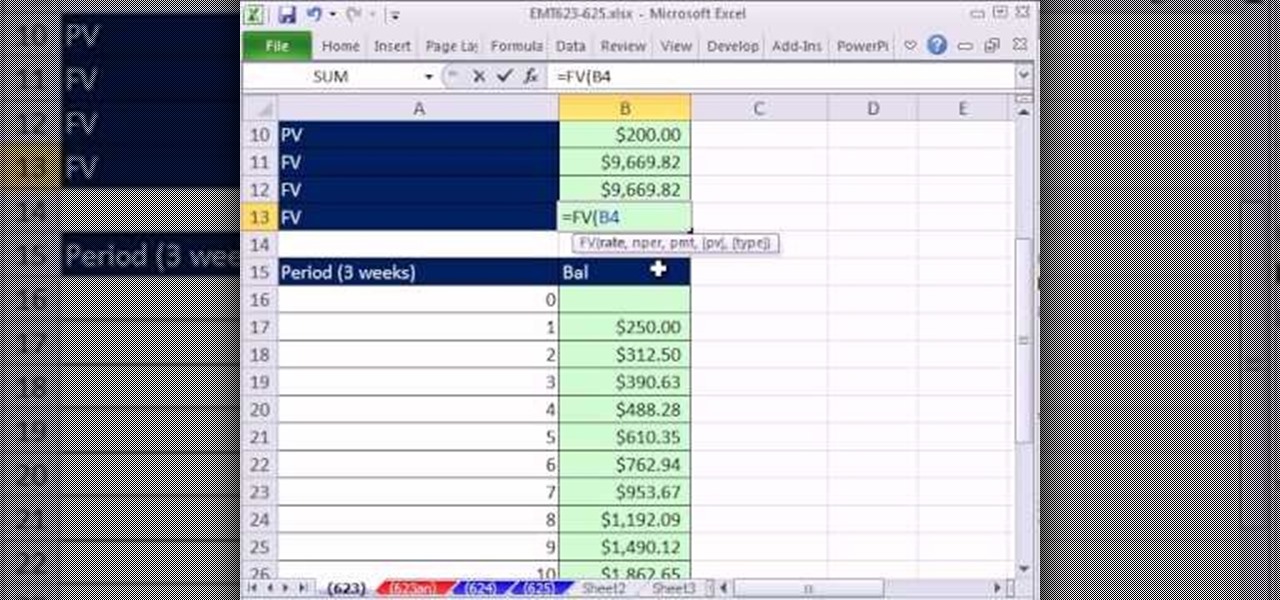
New to Microsoft Excel? Looking for a tip? How about a tip so mind-blowingly useful as to qualify as a magic trick? You're in luck. In this MS Excel tutorial from ExcelIsFun, the 623rd installment in their series of digital spreadsheet magic tricks, you'll learn how to see the pain that pay day loans inflict on people using Excel. Learn how to calculate APR (Annual Percentage Rate), EAR (Effective Annual Rate), an Amortization Table and the EAR for a loan that takes a fee out up front. Learn ...

As the world goes into a frenzy over the latest strain of WannaCry ransomware, it might be a good time to remember to update all your devices. Yes, those little reminders your phone and computer throw at you every now and then to update your junk can be really annoying, but not without merit.

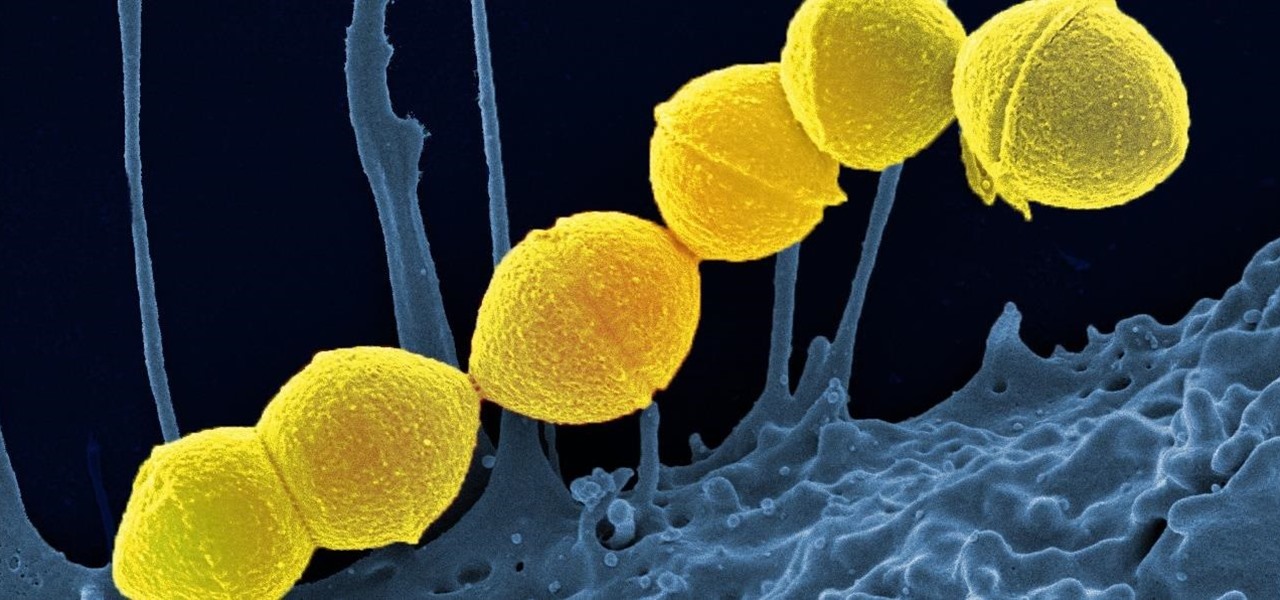
It's not the bacteria itself that takes lives and limbs during invasive flesh-eating bacteria infections. It's the toxins secreted by the group A Streptococcus bacteria invading the body that causes the most damage.

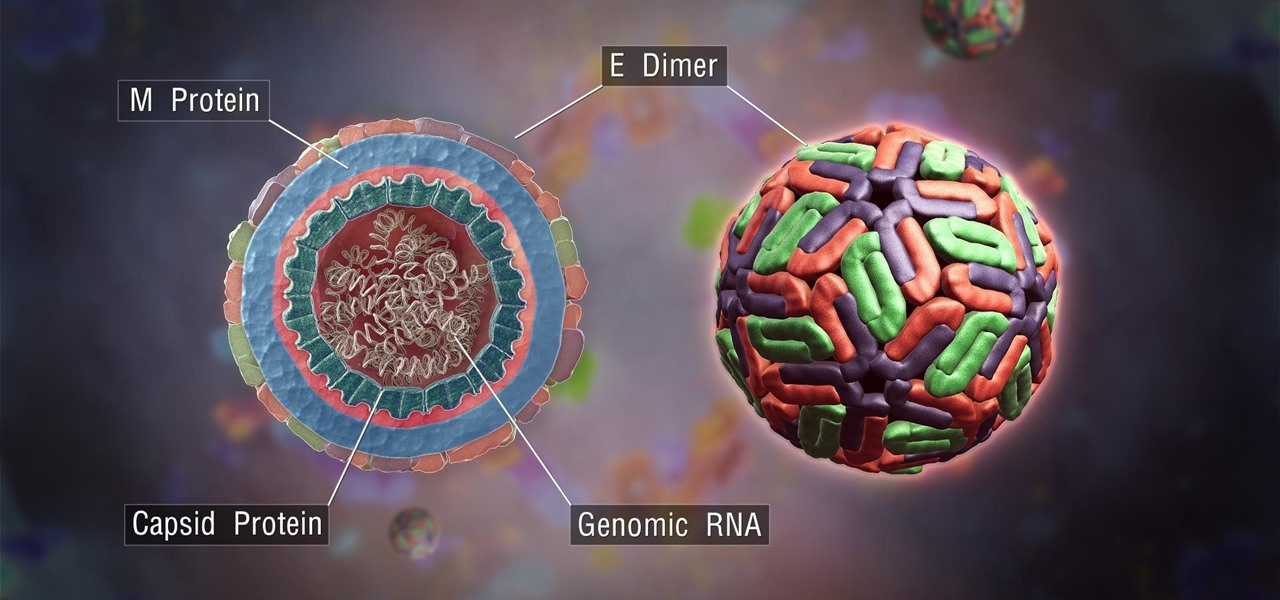
The mention of Zika can strike fear in the hearts of pregnant women. With infections increasing around the world, including in the US, researchers are fighting the clock to figure out how the virus can have such horrific effects in some people.

Those of you who have been a part of the Null Byte community for even a short while know that I sincerely and firmly believe that hacking is the most important skill set of the future.

Welcome back, my hacker wannabees! Most of my recent posts have addressed using Metasploit’s Meterpreter and what we can do once we have embedded it on the victim’s system. This includes remotely installing a keylogger, enabling the webcam, enabling the microphone and recording, disabling the antivirus software, among many other things. The list is almost unlimited.

Ooooo. Step back, Jack. This one has the taser ignition. Not only that, this dude give you desert decal instructions and ways to camo your potato gun. This potato gun tutorial is pure instruction, in two parts. Kudos. Watch this nifty weapon hack to learn how to build a potato gun launcher with interchangeable barrels. This potato gun "spudzooka" with interchangeable barrels is powered by taser ignition. It also resembles those bazookas and RPGs causing so much havoc on the world today.

It hasn't even been eight years since Candida auris was discovered—cultured and identified from the ear canal of a patient in Japan—and now it's drug-resistant, setting up residence in hospitals, killing patients, and wreaking havoc across the globe.

welcome back my masters , teachers and classmates , in this second part of this 0-day series we will learn the basic of fuzzing, and i bought some gift for nullbyte(a 0 day vuln that will be released today exclusively on null-byte) .

Welcome back, my hacker novitiates! There are many ways to hack databases, and most of these techniques require SQL injection (SQLi), which is a way of sending SQL commands back to the database from a web form or other input. In this tutorial, we will use SQL injection to get access to the underlying server. So instead of getting access to the database and its data, we will use the database as an intermediary to gain access to the underlying server.

Welcome back, my greenhorn hackers! Sometimes, we don't have a specific target in mind, but rather we are simply looking for vulnerable and easy-to-hack targets anywhere on the planet. Wouldn't be great if we had a search engine like Google that could help us find these targets? Well, we do, and it's called Shodan!

April Fools may be over, but any day is a good day to prank someone, and the best time to do it is when everyone's eyes are glued to the television.

Welcome back, my budding hackers! In my continuing series on Linux basics for aspiring hackers, I now want to address Loadable kernel modules (LKMs), which are key to the Linux administrator because they provide us the capability to add functionality to the kernel without having to recompile the kernel. Things like video and other device drivers can now be added to the kernel without shutting down the system, recompiling, and rebooting.

The summer sun can wreck havoc on your automobile. Use this tutorial to keep your paint job shiny and your interior bright in the scorching summer sun.

Hello everyone. I'm Calypsus and i've been around for a while learning from various tutorials, expanding my knowledge and this is one of the best platforms for newbies to sharpen the skills. Today i decided to register myself and contribute to this wonderful community. Since this is my first post, any kind of feedback is appreciated.

The May 2017 security update has begun rolling out to Nexus and Pixel devices, which is usually great news. It means that your device is now being updated to protect you from the latest exploits and vulnerabilities found in Android. At other times, though, security updates patch root methods like Dirty COW, which is extremely frustrating for users and developers alike. Especially since most OEMs don't condone rooting or even unlocking the bootloader on their devices.

Six Flags is teaming up with Samsung to make riding a roller coaster a little more thrilling, and quite possibly a little more nauseating as well.

In my last tutorial I very briefly introduced Zanti , but in this tutorial I will start to show its many features. The first step on hacking is recon . You could use Nmap , but the problem with Nmap on Android is that by itself, in order to gain full functionality your phone must be rooted. Thank goodness for a few geniuses in Zanti's dev team whom managed to implant full fuctionality of Nmap in Zanti without rooting your phone. With that being said, boot up your Android phone and lets start ...

If you keep your iPhone's home screen obsessively tidy, new apps are the bane of your existence. Hyperbole aside, they automatically fill the first available space on your home screen, starting on the second page, which can wreak havoc on your carefully planned layouts. With iOS 14, however, you can auto-hide new apps so that you never see them until you want to.

As long as you're on the internet, you can be hacked. With an estimated 2.65 billion social media users, these apps are prime targets for hackers.

When it comes to shooting games, battle royale titles like PUBG and Fortnite have come to dominate the scene, leaving other sub-genres like top-down and third-person shooters living in the shadows. They're far from irrelevant, though, as evidenced by all the great games released just in 2019 alone.

Particular vulnerabilities and exploits come along and make headlines with their catchy names and impressive potential for damage. EternalBlue is one of those exploits. Originally tied to the NSA, this zero-day exploited a flaw in the SMB protocol, affecting many Windows machines and wreaking havoc everywhere. Here, we will use EternalBlue to exploit SMB via Metasploit.

If you've ever received an email from a sketchy address purporting to be Uber, asking you to sign in with your credentials, you might be a phishing target. Hackers use a fake login page from real-looking domains to trick you into giving up your account information, and while it's been an issue in the past, Uber is making it more difficult on cyber thieves with the addition of two-step verification.