
How To: Switch Between Multiple Outputs with a One-Button Redstone Relay in Minecraft
Relays are simple redstone devices that allow you to switch between multiple outputs with only one input. They're incredibly useful in the right situation!


Relays are simple redstone devices that allow you to switch between multiple outputs with only one input. They're incredibly useful in the right situation!

Devolped by the same team of engineers responsible for LightWave 3D, modo, lowercase, delivers the next evolution of 3D modeling, painting and rendering in a single integrated and accelerated package for the Mac and PC. And now, modo is a true end-to-end solution that includes true 3D sculpting tools, animation and network rendering! More than just features, modo is a truly elegant integration of technology, raw horsepower and refined workflow. With such a wealth of inbuilt features, however,...

The Geminid meteor shower 2010 is tonight, climaxing sometime between midnight and dawn Tuesday. Usually, the Geminid meteor showers in December are awesome spectacles, one of the most intense meteor showers of the year, but this year the moon will be out until after midnight, lessening visibility. But just because you can't see the meteor shower this year, doesn't mean a meteorite or two didn't sneak into Earth's atmosphere, hurdling to the ground, waiting for you to find it. So, get your me...

This FL Studio tutorial gives demonstrations of different Waveform outputs from simple FM Synthesis with descriptions of how we achieved it. These are very rough examples but they will help you understand the Sytrus matric and how to use FM Synthesis in FL Studio.

This music production software tutorial demonstrates the use of an Audio Delay to create an effective CV delay, with some tweaking in Reason. CV delays are useful for instrument design and combinator construction. Learn how to delay control voltage outputs in this Reason video.

This test can be used to determine whether the given graph is a function or not.

In this software video series, you will learn how to use Takes in Houdini 9. Part one: Intro to Takes

In this instructional DJ video, take a look at the back of the Gemini CDM-3600 unit to learn how to use the inputs and outputs. This video is ideally for beginners who are just starting off as DJs and need some advice on the various outlets. Learn how to use the back of a Gemini CDM-3600 by watching this DJ tutorial video.

Everybody is going digital these days, so everybody has a reason for software like HandBrake. You can save your entire DVD collection on your computer in digital files, and you can convert videos into different formats. Check out this video tutorial on how to rip DVDs and convert videos on Ubuntu Linux, Windows, and Mac.

In this tutorial, we learn how to graph a parabola. Quadratic functions are parabolas. To graph these, you will first need to look at the function, which is the set of outputs for a set of inputs. Write this out on a t-chart to find what your 'x' and 'y' values are. Once you find these, you will plug in the coordinates to a graph. After you have written down the coordinates, you can graph your parabola. This is easy to do if you are familiar with quadratic functions and good at math. Just pra...

Learn how to master tunes using Reason 4.0 software to get a more effective sound. The first step is to make sure the outputs are not in the red. If they are in the red, that means the sound is not that good, and you don't want to work with a bad mix. The next step is to add a McClass mastering suite to your mixer. As per the guide in this video, everything should be below 100 to 175 Hz mono. However, this is a personal preference and you should do what you feel is best for the sound of the m...

Want to learn how to broadcast live & record from your game console while viewing game-play in HD - using the BlitzBox B1-HD (for under $100). THis is an easy way to record your PS3, PS2, XBOX 360 or Wii games.

In last Saturday's workshop, the tutorial was on the ABBA switch, so named because it fires redstone pulses in A-B-B-A order. While the turnout was low, it was a really productive workshop! We experimented with a lot of things and had a great time. Hopefully you'll consider joining us next time!

Beginners learning brute-forcing attacks against WPA handshakes are often let down by the limitations of default wordlists like RockYou based on stolen passwords. The science of brute-forcing goes beyond using these default lists, allowing us to be more efficient by making customized wordlists. Using the Mentalist, we can generate millions of likely passwords based on details about the target.
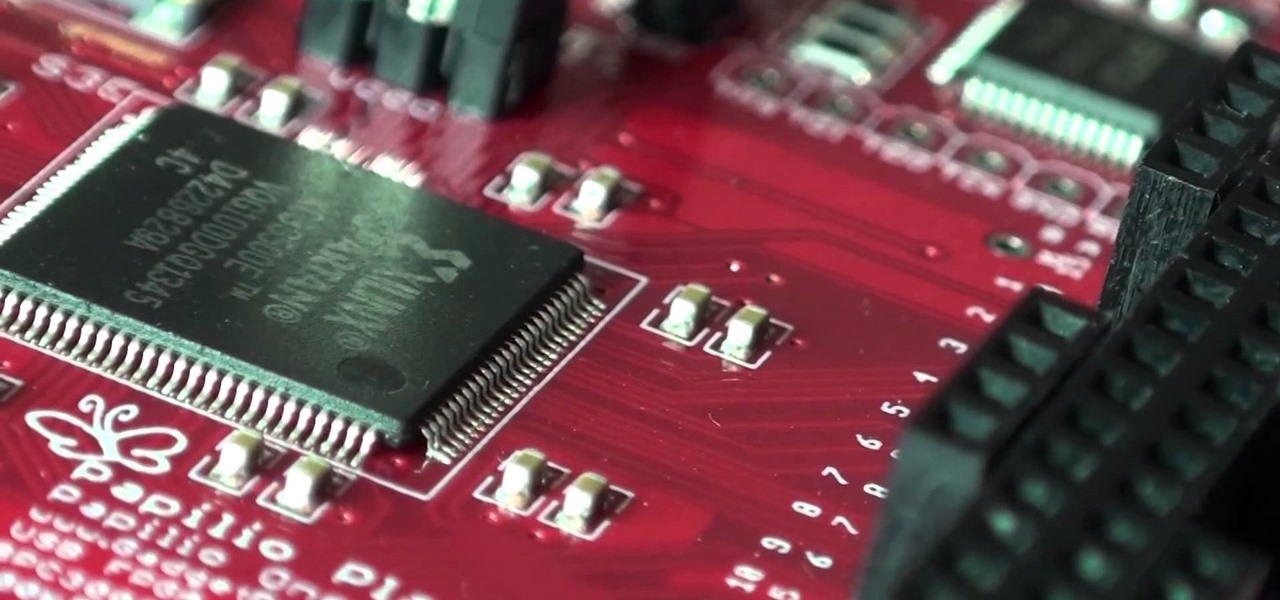
A FGPA is chip that is programmable with the computer to create circuit. It is a totally different type of programmable board compared to an Arduino for example. The Arduino will follow lines of codes to generate the necessary outputs. A FPGA won't however read lines of code, but it is a circuit itself. When the chip is programmed, a series of AND-ports, OR-ports and many others ports are linked together. The FGPA will increase the speed and the possibilities of your designs! I assume that by...
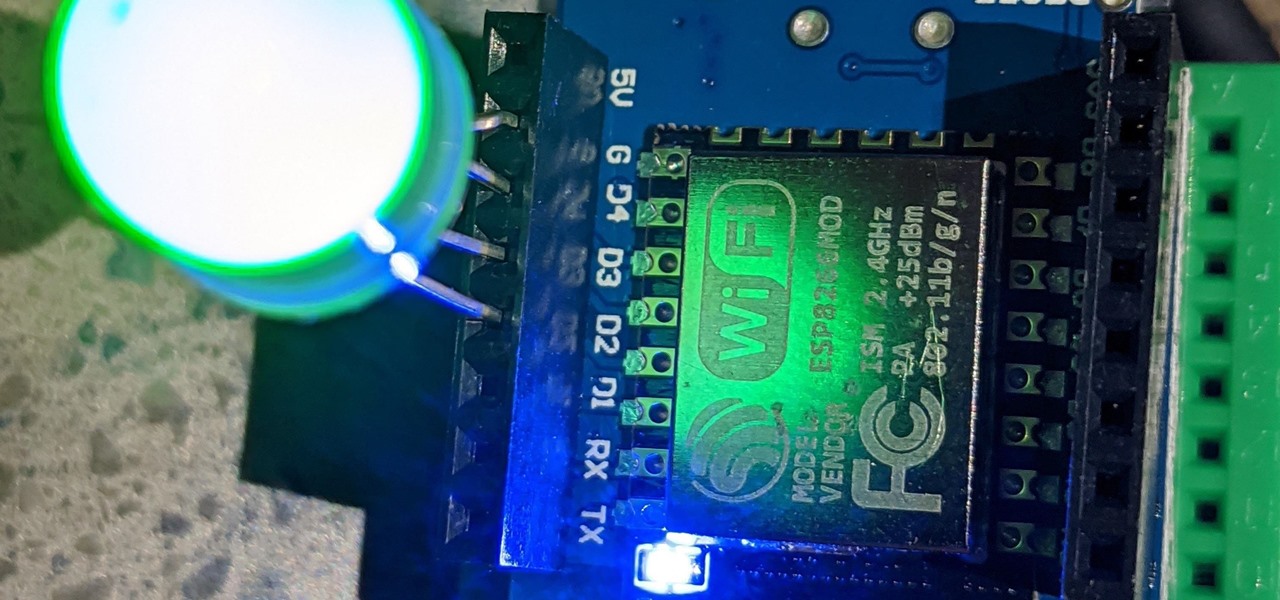
For anyone interested in using cheap, Wi-Fi-connected microcontrollers like the ESP8266, the Arduino programming language can be a barrier to entry. Based on C++, Arduino requires knowledge of more computer science than languages like Python. Fortunately for beginners, setting up MicroPython on an ESP8266 allows anyone to write Python on affordable microcontrollers in a matter of minutes.

If you're at all like me, you constantly get frustrated that repeaters only boost redstone signals in one direction. It's annoying!

Motorola is a shell of its former self. In 2010, it had just released the Motorola Droid, a phone so popular it led to all Android phones being called "Droids" by non-techies. But there have been some rough years between then and now, and Motorola's latest "flagship" doesn't look like it will help get them off this path.

The first augmented reality hardware and software functional requirements guidelines have been released today by UI LABS and the Augmented Reality for Enterprise Alliance (AREA).
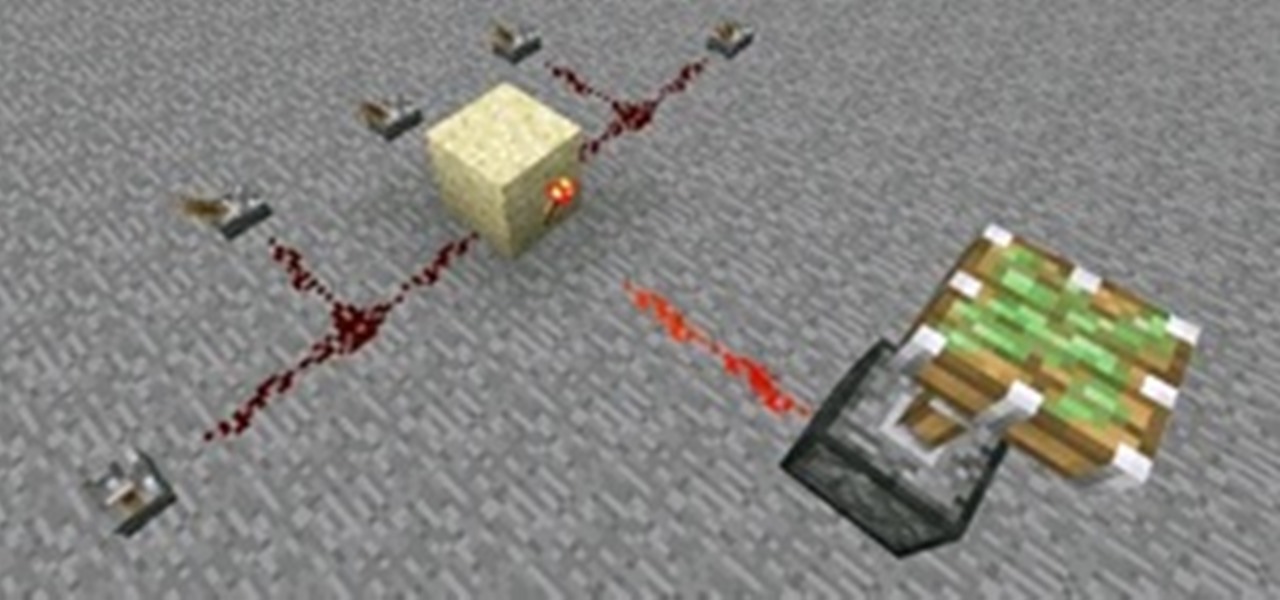
Control is important. Mankind inherently wants to control its environment, which is why we have things like indoor plumbing, electric lights, air conditioning, and more. Likewise, Minecraft has redstone, which is a way for users to control their environment and manipulate it to suit their needs.

GTFOBins and LOLBAS are projects with the goal of documenting native binaries that can be abused and exploited by attackers on Unix and Windows systems, respectfully. These binaries are often used for "living off the land" techniques during post-exploitation. In this tutorial, we will be exploring gtfo, a tool used to search these projects for abusable binaries right from the command line.

CyanogenMod continues to be the most popular custom ROM for a good reason. Their team of developers always stay on top of the latest trends, and ensure that their software is packed with nice tweaks and awesome features. One such feature is an audio equalizer that allows you to fine-tune your device's various sound outputs. It's got a great interface, and works with any app that calls on Android's default audio mixer.

Having access to your computer from your cell phone is an extremely useful feature. Whether you need to edit documents or send files that are on your home desktop, or you simply want to watch movies you have saved on your computer, access is key.

There's never been a better time for streaming videos on your phone. With so many options available (including a potential mobile-only Netflix tier) and so many new smartphones having large screens, there's a good chance you know someone who mainly use their phone for videos. And if you looking for a gift for them, there are some great options.

The road to becoming a skilled white hat is paved with many milestones, one of those being learning how to perform a simple Nmap scan. A little further down that road lies more advanced scanning, along with utilizing a powerful feature of Nmap called the Nmap Scripting Engine. Even further down the road is learning how to modify and write scripts for NSE, which is what we'll be doing today.

There was a time when building a website required coding knowledge. Eventually, software came along that made the process easier, and then services like Squarespace made it dead simple for even a technical novice to design a website.

LG announced their latest high-end device on September 6 and its specs are pretty amazing: The new V20 sports three cameras, two displays, three microphones, four DACs for high-end sound, and it's all powered by a removable battery.

Greetings all. I'm back with another informational review of the diversity of utilities for use in the sphere of hacking at your disposal. Today we are going to cover the insides of CUPP (Common User Passwords Profiler) in its entirety. The tool is very basic in nature, as there is little to no configuration needed to get cracking (worst pun ever). So let's get started, shall we?

Hello everybody Joe here. Today I will be demonstrating how you can find XSS vulnerabilities in a website and what you can do with them
I see many people posting the same thing on the internet. "How do I become a hacker? Where do I commence?"

If you've ever wiped your computer without having a proper backup of your operating system, or just wanted to cause some havoc online, chances are you've had to rely on Linux to help you out, specifically the Ubuntu distro.

Welcome back, my budding hackers! In previous tutorials, we've looked at some of the basic commands and concepts for using Linux. Along the way, I realized that I've failed to provide you with some basic background material on the stdin, stdout, and stderror.

Welcome back, my budding hackers! I've written several listener guides on creating a malicious PDF or malicious Word document that would carry in it a payload with the Meterpreter, or reverse shell enabling you to own the system. One of the hurdles to using these techniques is the antivirus (AV) software on the target system. For instance, if you try to email a malicious PDF or Word doc, it's likely that the victim system will alert the victim that it contains a virus or other malware.

A deck of cards may be a magician's best way to demonstrate his or her's sleight of hand, but for the prankster, it's the perfect way to deliver a shocking 300 volts of electricity! And that's exactly what I'm going to show you how to do today. Stuart Edge used it in his "Electric Shock Kissing Prank" to show the ladies how a man can really put the sparks in a kiss.

In this article, I'll be continuing my series on microcontrollers. If you haven't read part one, I'd recommend heading over there and reading it!
I love robots. They have the potential to evolve into Asimovian destroyers of the human species, but have only just mastered the art of cleaning my rug. They have an ever increasing cool factor and a growing number of cheap and simple components that let the hobby roboticist reach for the burning miasmas of plasma. But to get to the stars, we need to start with the basics.

Samsung has just announced the Galaxy Note 10 and 10+. These are the latest and greatest from the largest smartphone OEM in the world. Plenty of numbers and specs have been thrown your way to showcase how good the Galaxy Note 10 is, but we wanted to simplify all this for you and key in on the most important things.

A convincing domain name is critical to the success of any phishing attack. With a single Python script, it's possible to find hundreds of available phishing domains and even identify phishing websites deployed by other hackers for purposes such as stealing user credentials.

Using a keylogger to intercept keys pressed on an infected computer can circumvent encryption used by email and secure chat clients. The collected data can often reveal usernames, passwords, and potentially compromising and private information which hackers abuse for financial gain.

So after setting everything up, creating the system, working with focus and gaze, creating our bounding box and UI elements, unlocking the menu movement, as well as jumping through hoops refactoring a few parts of the system itself, we have finally made it to the point in our series on dynamic user interfaces for HoloLens where we get some real interaction.