Google's push for your safety gained some much-needed attention when it released the Pixel 4 smartphone. It has an app called "Personal Safety," which uses the array of built-in sensors on your phone to detect if you've been in a car crash. The futuristic safety feature was exclusive to the Pixel 4 initially but is now available to all Pixel owners as well.

When the Nexus 5 debuted, one of its coolest features was the fact that you could say "OK Google" any time you were on the home screen to launch a Google Voice Search. This feature was ultimately made available for other devices by way of the Google Now Launcher.

Welcome back, my fledgling hackers! Nearly every commercial enterprise worth hacking has an intrusion detection system (IDS). These network intrusion detection systems are designed to detect any malicious activity on the network. That means you!

It is often said that the best hackers remain unknown, and the greatest attacks are left undiscovered, but it's hard for an up-and-coming penetration tester or white hat to learn anything unless one of those factors is actually known or discovered. But the end goal here in our SQL injection lessons is to make that statement as true as possible for us when performing our hacks.

The iPhone 12, 12 mini, 12 Pro, and 12 Pro Max's new Scene Detection mode automatically adjusts Camera's settings to best suit your subject. That means it won't use the same shooting options for a close-up shot of your friend as it would a wide-angle landscape picture. If you don't want Apple to choose how your scene should look, there's a way to stop it to regain some control.

If you've recently built a Wi-Fi spy camera out of an ESP32-CAM, you can use it for a variety of things. A baby monitor at night, a security camera for catching package thieves, a hidden video streamer to catch someone going somewhere they shouldn't be — you could use it for pretty much anything. Best of all, this inexpensive camera module can perform facial detection and facial recognition!

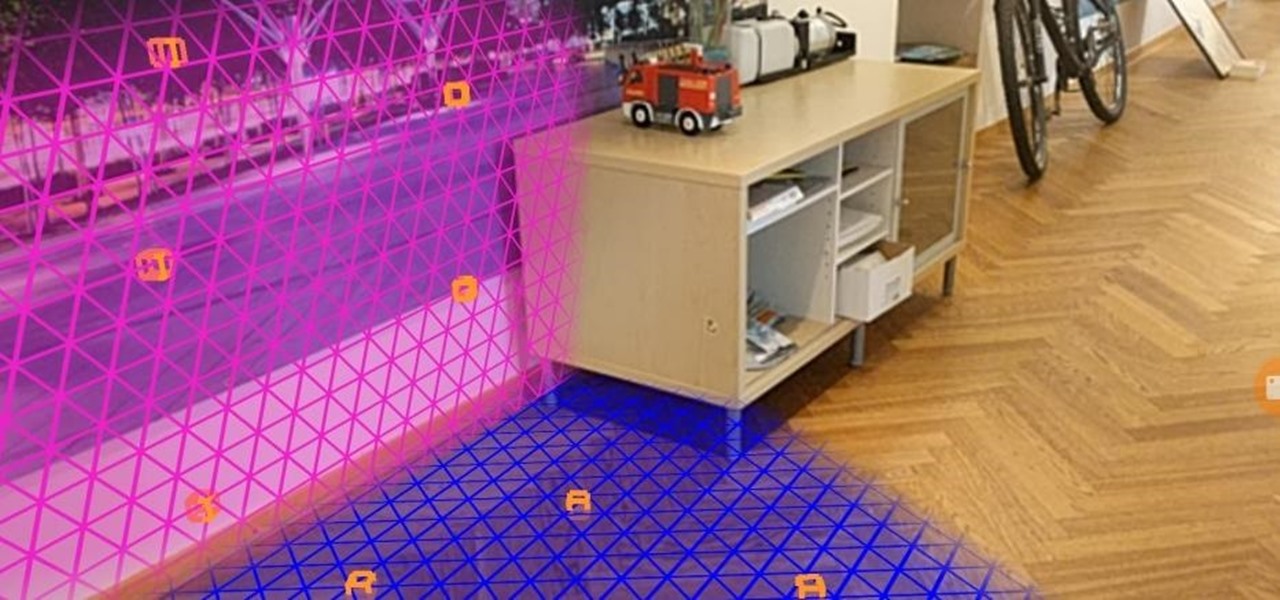
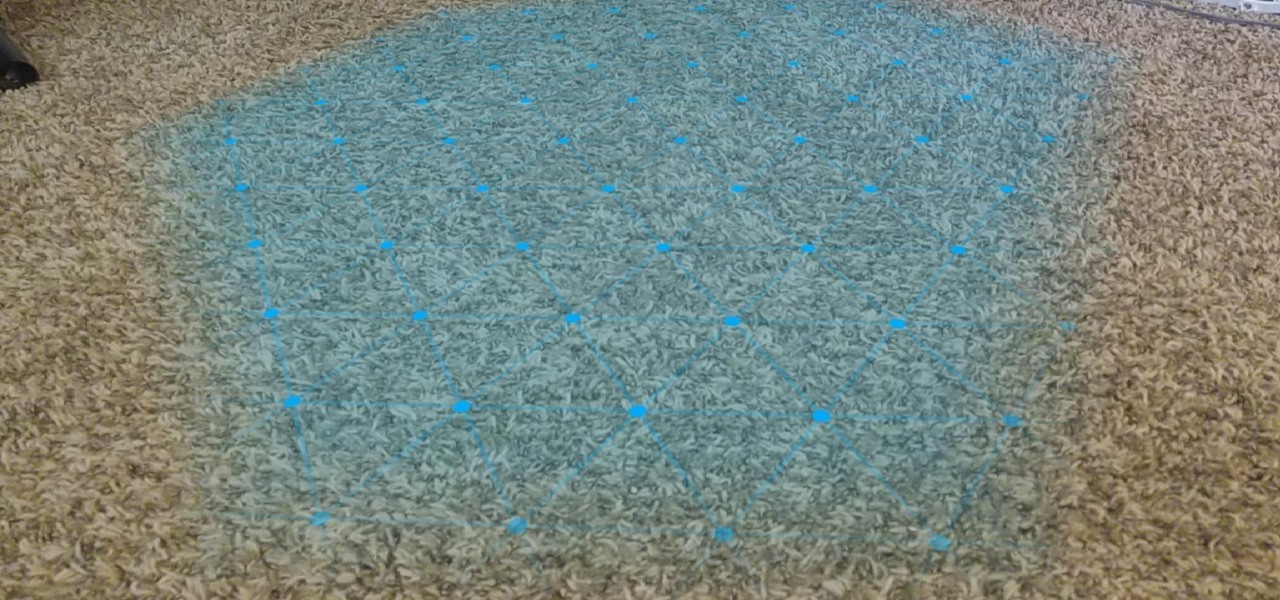
In the latest update to its augmented reality platform, Wikitude has introduced new plane detection capabilities that can anchor virtual content to surfaces at any orientation.

Welcome back, my greenhorn hackers! One of the most important issues any hacker must address is how to get past security devices and remain undetected. These can include antivirus software, intrusion detection systems, firewalls, web application firewalls, and numerous others. As nearly all of these devices employ a signature-based detection scheme where they maintain a database of known exploits and payload signatures, the key is to either:

One of the things that sets a seasoned hacker apart from the script kiddies is the ability to effectively sneak past antivirus defenses when executing an attack. One way to do this is to use custom shellcode in an exploit. Not everyone is an expert at writing shellcode, but luckily there's an easy way to do this that is both quick and effective.

Motorola changed the way users interact with their devices when they introduced their "always listening" feature on the Moto X. When I first saw it demoed, I couldn't wait to get the same functionality on one of my handsets, and now that has finally come to fruition.

Welcome back, my novice hackers! The worst thing that can happen to any hacker is being detected by a security admin, the security technologies (IDS, firewall, etc.), or a forensic investigator.

Welcome back, my hackers novitiates! As you read my various hacking tutorials, you're probably asking yourself, "What are the chances that this hack will be detected and that I'll land behind bars, disappointing my dear mother who already thinks I'm a loser?"

As expected, Apple revealed today at the WWDC keynote that ARKit 2.0 will support multiplayer gaming support and persistent content, which will arrive this fall with iOS 12.

Google recently rolled out a new Smart Lock option labeled "On-body detection" for Android Lollipop via an update to Google Play Services. As I'm sure you can gather from the name, this new function keeps your phone or tablet unlocked using the built-in accelerometer to determine whether or not your device is being carried on your body, allowing you to set it down and walk away carefree knowing that's it's locked again.

Sitting in the Powell Library at UCLA was a constant thing for me. Directly after class, I would streamline my way there to study all night until my eyes shuttered to sleep. For the most part, my classes and professors managed to keep my studying online via PDFs, emails, long essays and journal entries.

It is said that the best way to avoid detection when hacking is to leave no trace, and often that means not touching the filesystem at all. But realistically, in most cases, it's impossible not to interact with the filesystem in one way or another. The next best thing to do to throw off any investigators is to change the file attributes to hide activity. We can do this with Metasploit's Timestomp.

Welcome back, my budding hackers! I've written several listener guides on creating a malicious PDF or malicious Word document that would carry in it a payload with the Meterpreter, or reverse shell enabling you to own the system. One of the hurdles to using these techniques is the antivirus (AV) software on the target system. For instance, if you try to email a malicious PDF or Word doc, it's likely that the victim system will alert the victim that it contains a virus or other malware.

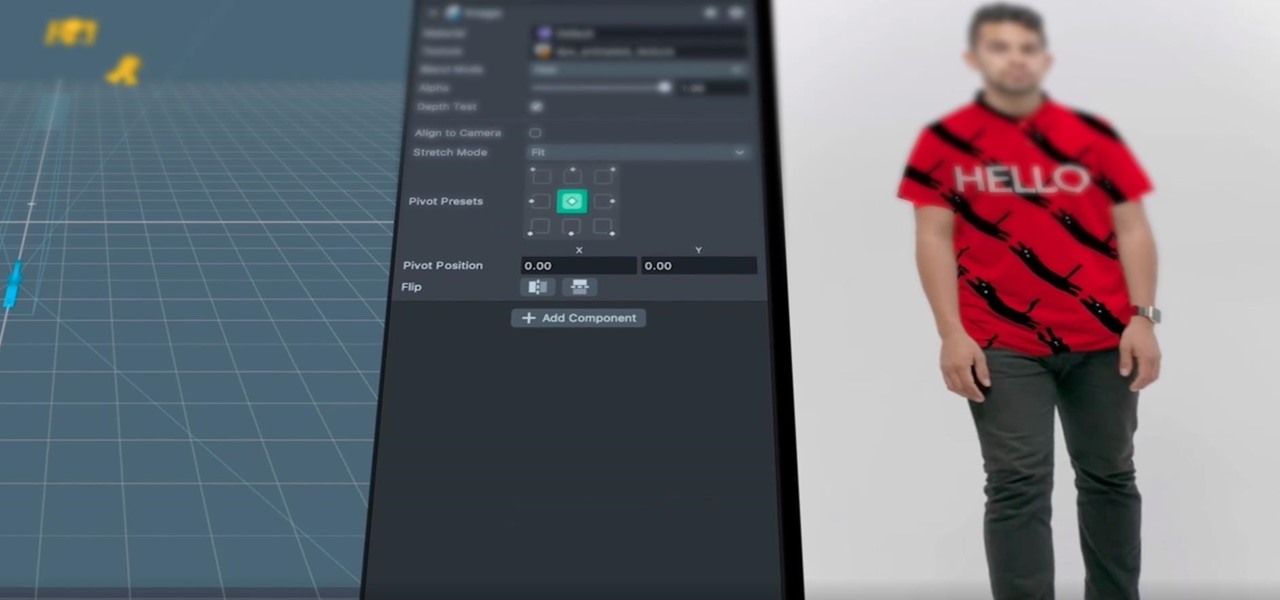
After adding full-body tracking and 3D body mesh in its past two Lens Studio updates, Snap continues to supply creators, particularly apparel retailers, with tools for creating clothing-centric AR experiences.

Hola my fellow hackers! I promised you the tutorials on setting up RAT's and Botnets, but before jumping into those, i want you to know about the precautionary measures and detection of RATs which might be on the system without your prior knowledge. Of course the Anti-virus do most of the job but there are some RATs which slips past the Anti-viruses (This is where Hacker's skill come into play).

Microsoft's built-in antimalware solution does its best to prevent common attacks. Unfortunately for Windows 10 users, evading detection requires almost no effort at all. An attacker armed with this knowledge will easily bypass security software using any number of tools.

While the automotive industry is moving towards adopting AR displays in future models, BMW is already shifting into the next gear with its vision of the technology.

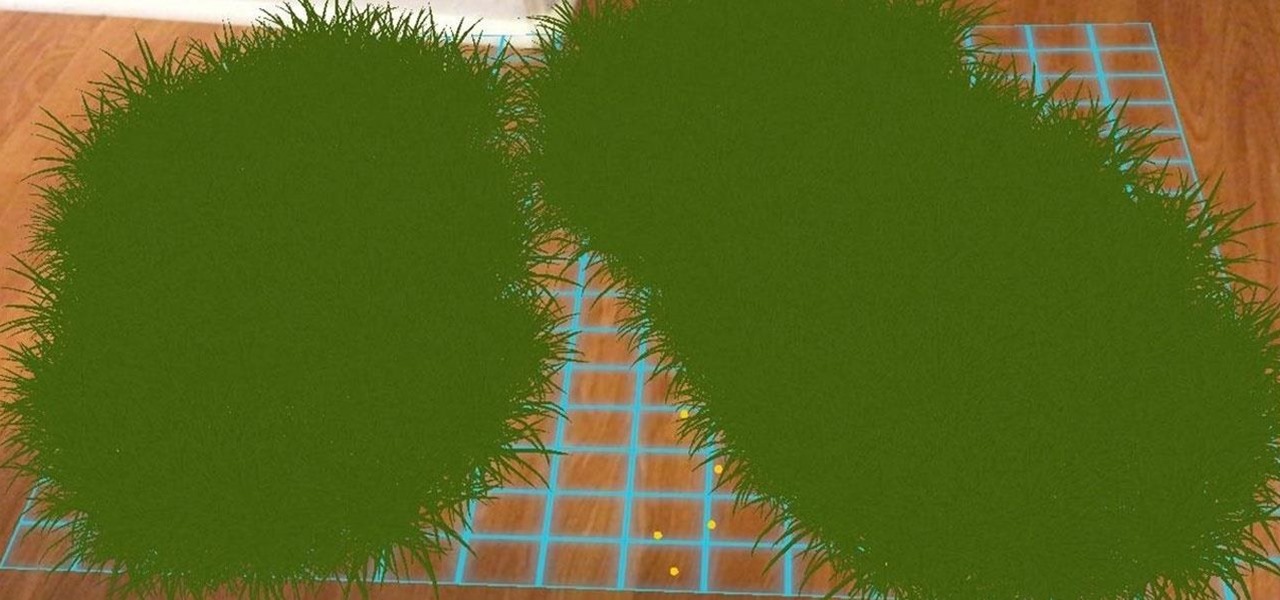
Ever notice how some augmented reality apps can pin specific 3D objects on the ground? Many AR games and apps can accurately plant various 3D characters and objects on the ground in such a way that, when we look down upon them, the objects appear to be entirely pinned to the ground in the real world. If we move our smartphone around and come back to those spots, they're still there.

Welcome back, my novice hackers! My recent tutorials have been focused upon ways to NOT get caught. Some people call this anti-forensics—the ability to not leave evidence that can be tracked to you or your hack by the system administrator or law enforcement.

There are countless tutorials online that show how to use Netstat and Tasklist to find an intruder on your computer. But with a few PowerShell functions, it's possible for a hacker to evade detection from the almighty command line.

The emerging narrative as CES begins is that consumer-grade smartglasses require a heavy compromise in functionality in order to arrive at a form factor and price point that appeal to mainstream customers.

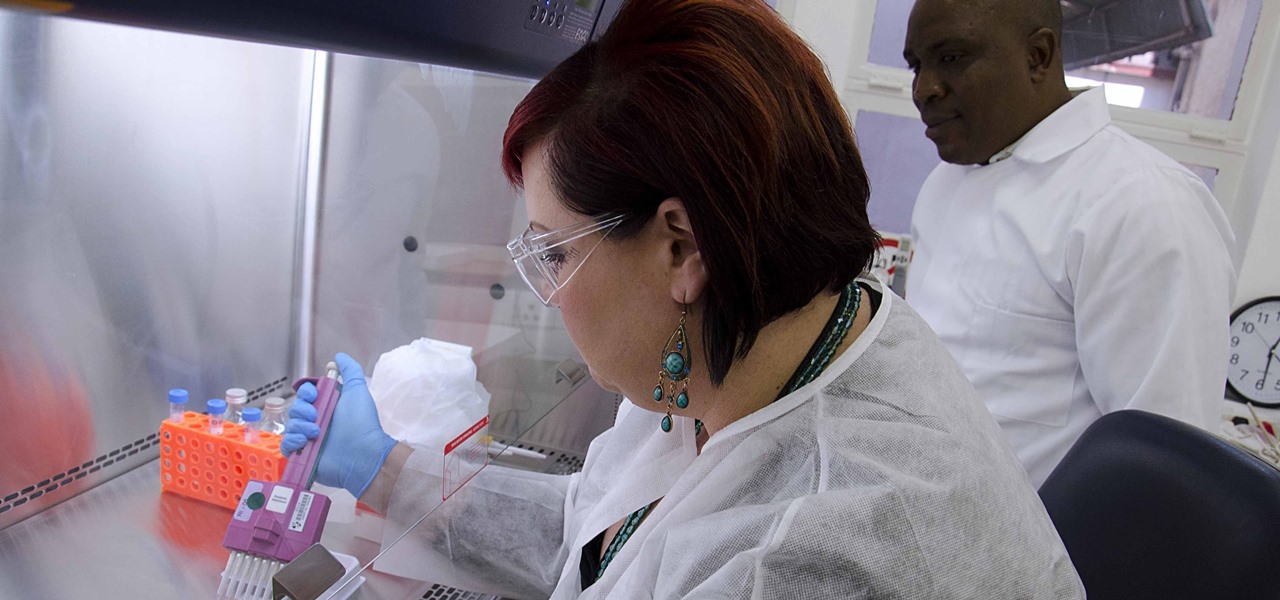
HIV infections persist despite treatment that successfully decreases viral blood levels to the point where doctors can't detect the virus. But that doesn't mean the person is cured. The virus hides in the body, not replicating, just waiting for a chance to jump out of the shadows and reemerge.

Welcome back! In the last iteration of how to train your python, we covered loops, today we'll be covering something that I wish I had learned about much earlier in my scripting career, errors. We all run into them, and they can be frustrating, but there is also a silver lining to them. Today, we'll be discussing why some errors are unavoidable, and what we can do when we run into them. Also, this article will be more of a concept and less of writing actual code, but the information is equall...

One of the primary factors that separates an augmented reality device from a standard heads-up display such as Google Glass is dimensional depth perception. This can be created by either RGB cameras, infrared depth cameras, or both, depending on the level of accuracy you're aiming for.

The release of the Nexus 5 marked the debut of the Google Now Launcher. Even with an integrated Google Now page on your home screen, the most talked-about feature was actually the always-listening functionality.

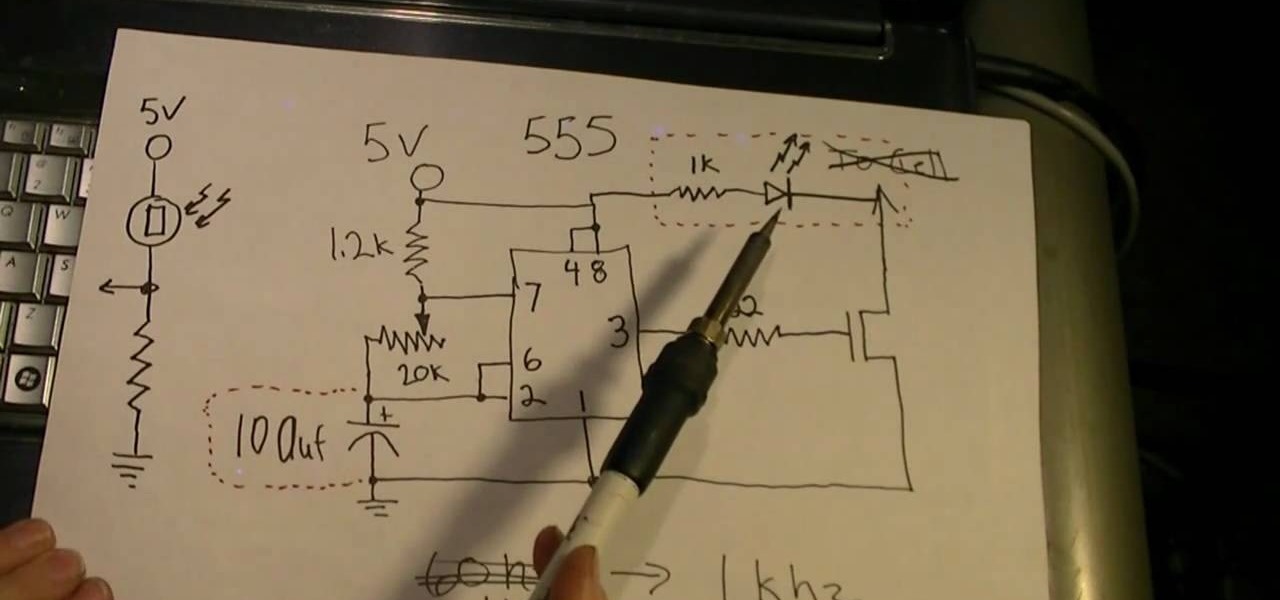
Phosphors are great for lighting up areas where fire will not burn, and also for keeping humans alive in very small quantities. Quenching phosphors allows you to use them for all sorts of cool projects, and this video will show you how to make an IR detection device with quenched phosphors and also how to measure temperature with thermally quenched phosphors.

Flash Actionscript 3 is a wonderfully powerful, but somewhat obtuse, tool for creating websites. This video will teach you how to use one particular function in the language, creating a class that has multiple key detection enabled. This will allow you to create a website where users can key in multiple inputs and the website will respond appropriately.

Tired of getting speeding tickets? Not prepared to start driving by the letter of the law? Well, this instructional video shows a way to con the speeding radar. Regular LED lights can be modified with infrared LED bulbs and will avoid speed detection by the police. Learn how to stop getting speeding tickets and avoid police radar detection by adding LED lights by watching this how-to con video.

You can connect your Nintendo Wii Wiimote to your PC using GlovePie input emulation software and a bluetooth connection. Learn how to program your PC to detect motion from the Wiimote using GlovePie.

Focus in on what matters with the Desire 7's Face Detection feature! Learn how with this quick, official guide from HTC.

Focus in on what matters with the Desire HD's Face Detection feature! Learn how with this quick, official guide from HTC.

In this tutorial, we learn how to use radiation detection equipment. To use the dosimeter, you will remove the cap, then place the pipe on and push down on it. A light will come on, and you can use the knob to zero it. When you look in, you will be able to see it's measured in Roentgens per hour. When you are done using this, zero it again. Next, you will have a CD Geiger counter which has three positions for the knob. Whatever it is set on, you multiply the reading by that number. If you tur...

You can connect your Nintendo Wii Wiimote to your PC using GlovePie input emulation software and a bluetooth connection. Learn how to program your PC to detect motion from dual input the Wiimote using GlovePie. You'll be able to connect two Wiimotes to your PC.

If you have an ARKit-compatible iPhone or iPad, check for a software update, as iOS 11.3, with ARKit version 1.5 in tow, has just dropped. As we previously reported, ARKit 1.5 brings several new augmented reality features for app developers to use.

In this clip, you'll learn how to utilize octrees to resolve certain detection problems when working in MS Visual C++. Whether you're new to Microsoft's popular general-purpose programming language and IDE or are a seasoned developer merely looking to improve your chops, you're sure to find benefit in this free, official video tutorial. For more information, including detailed, step-by-step instructions, take a look. Use an octree to solve collision detection problems in Visual C++.

Lego meets interactive 3D detection and camera mapping.