In this video, we learn how to write an article. When writing an article, you need to use the proper formatting. This starts with the introduction to grab the reader's attention. Then the middle will elaborate on the introduction with 200 words maximum. The end will give the conclusion and summarize in around 50 words total. Don't give an opinion, just keep it un-biased and let the reader come up with their own opinion. Don't make some common mistakes which include: spending too much time res...
In this tutorial, we learn how to use quotes in an essay. When using a colon, you will set up the quote, then present it as proof of what you have just said. Note that the phrase before the quote could stand on its own as a sentence. For partial quotes, remember when summarizing to embed the author's words in your own sentence. If you take away the quotation marks the sentence should flow like you wrote it. When using commas with quotes, you can introduce the quote with an introductory phrase...

When it comes to building six pack abs, there's no better way to summarize the process than to say no pain, no gain. Sexiness requires work, guys and gals, but we promise the pain will be well worth it!

This is a video tutorial summarizing a one hour tengo dancing class. It tells its audience the different types of tengo and what each dance does. Primarily though this video focuses on ballroom tengo. First you should bring your partner to your left side and then step forward for the T-E-N-G-O then for the man you will go slow, slow, fast, fast, slow, do this with your feet. The woman will follow the man but the man must be the leader of the dance otherwise it will not look correctly. The lad...
In this video from KatiesTeachings we learn how to write an annotated bibliography with 4 easy tips. Katie Mitchell gives this tutorial. Once you find your sources you need to record the bibliographic information like who wrote it, when they wrote it, and when it was published. Next you need to summarize the source. Third, you want to assess the source. In doing this you want to answer questions such as was it good and is it valid. Finally the last step is to reflect on the source. These four...

This video tells us about annotated bibliography, what it is and its elements. Annotated bibliography is basically an evaluation or an assessment of the article you have read. To make an annotated bibliography there are four steps. The first one is to provide the source, the author, where it comes from and the title. The second step is to summarize your reading. The third step is to show that you know what type of article it is, and that means that you have to assess your resource. The fourth...

An two part introduction or overview of English articles: a, an, the, and the zero article. This is for the advanced or intermediate student. Part one presents basic rules or guidelines for using English articles. Part two summarizes the basic rules for using English articles and offers practice.

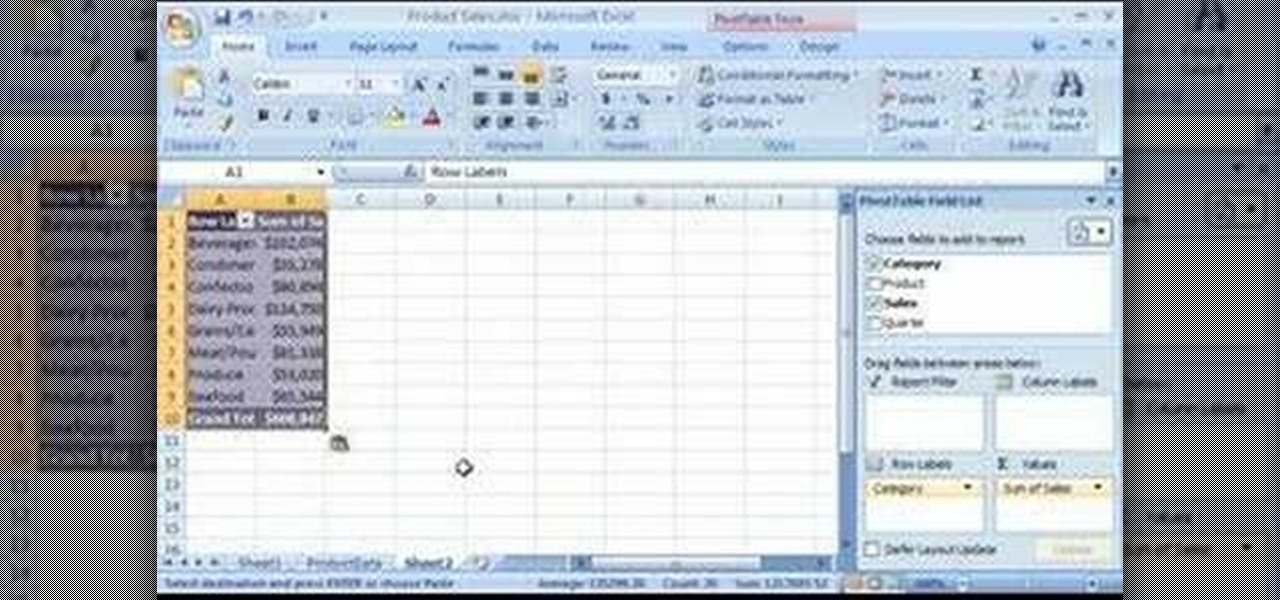
Want to get more from the raw data you're entering into your Excel worksheets? Now you can create two distinct pivot tables in Excel comparing, for example, monthly and quarterly sales data. Not familiar with the pivot table? Pivot tables summarize spreadsheet input by counting, sorting and totaling data within a list and providing at-a-glance computations within the same sheet. Become an expert on the subject within 5 minutes and 24 seconds by following easy to understand instructions narrat...

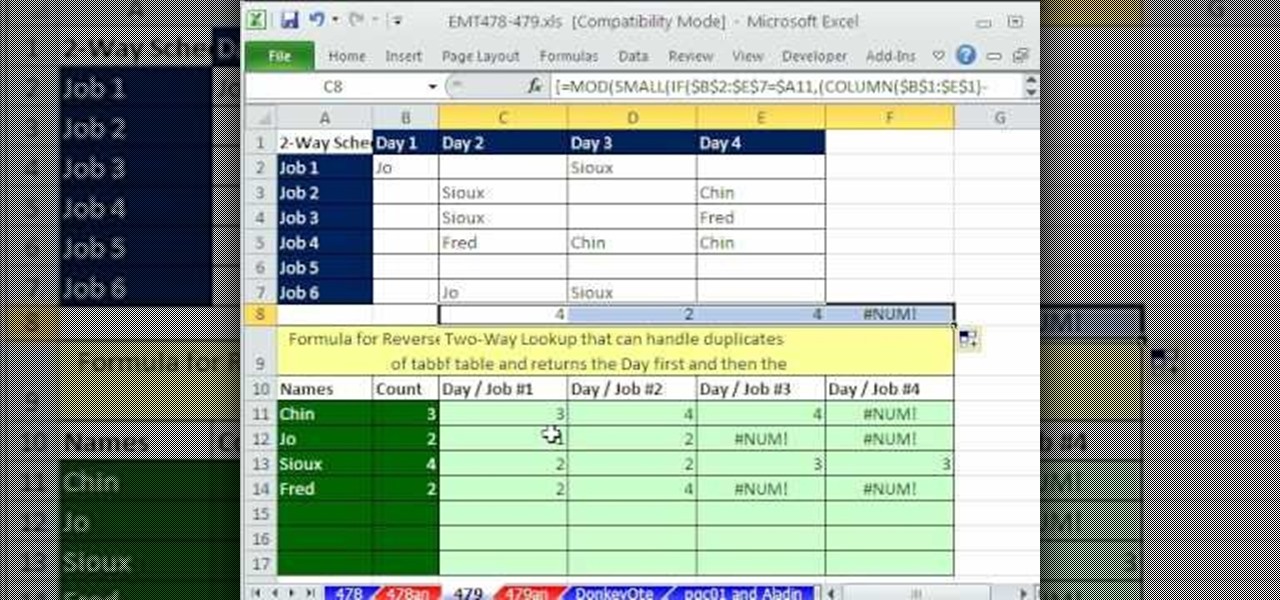
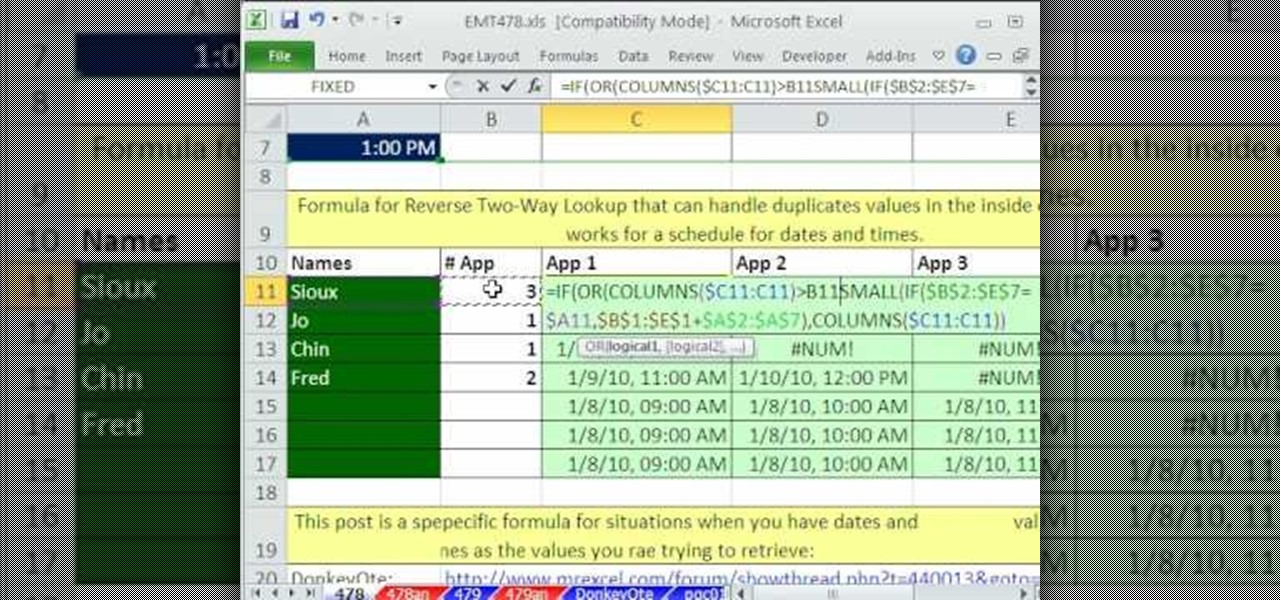
In this Excel magic trick video the tutor shows how to perform reverse two way look up for date and time columns and row headers. In this tutorial he shows a spreadsheet that contains dates in columns and times of a day in rows which makes up a small table schedule. Now he shows how to use those values of the cells in that schedule table and summarize and print out the values based up on a name or some other text value. He also refers to a previous video of his which he says to watch to get g...

In this Excel magic trick video the tutor shows how to perform reverse two way look up for date and time columns and row headers. In this tutorial he shows a spreadsheet that contains dates in columns and times of a day in rows which makes up a small table schedule. Now he shows how to use those values of the cells in that schedule table and summarize and print out the values based up on a name or some other text value. He also refers to a previous video of his which he says to watch to get g...

Oktay1979 takes a look into writing an annotated bibliography. Learn the steps such as citing a source, summarizing your reading, accessing your source, documenting your authors credentials, and reflecting on your source. Each bibliography is usually 150 words long and done in new times roman. You can also get a form to show you how to format the bibliography correctly. Make your writing process unique and accurate. Make sure you're doing your bibliography right by following the correct steps...

Each paragraph should be roughly 4 sentences long. The first sentence is an introduction, and then you can follow up with detailed sentences. The last sentence is your conclusion. An essay follows this same makeup. The first paragraph is an introduction, and then you have detailed paragraphs, followed by a conclusion paragraph. Each sentence in your introductory paragraph can be the introductory sentence for each of your detailed paragraphs. Likewise, the conclusion sentence in your introduct...

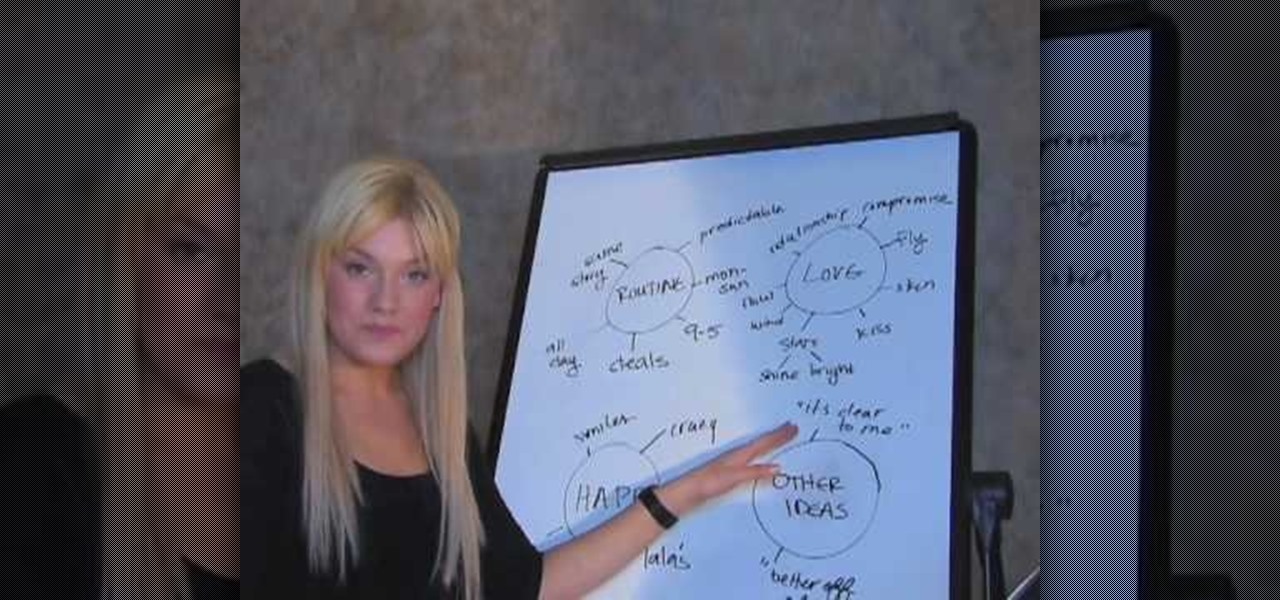
According to hit recording artist Zosia, writing a song is much like telling a small story. The first verse of a song should draw your listeners into the story. Next you'll want to build into a unique and catchy chorus, which will relate your main message. The second verse reveals more of your story and flows into the bridge. In your third verse, you'll want to bring the story to a resolve and summarize the feeling and tone, while leaving a lasting impression on listeners.

Hak5 isn't your ordinary tech show. It's hacking in the old-school sense, covering everything from network security, open source and forensics, to DIY modding and the homebrew scene. Damn the warranties, it's time to Trust your Technolust. In this episode, see how to break down IP and TCP header with Wireshark.

With PivotTable reports in Microsoft Office Excel 2007, your sales report will sparkle with power, flair, and functionality. Take a look at this instructional video to learn how to show the big picture, show all the details, or show anything in between. Easily create multiple worksheets to switch back and forth between the various versions of your report. Sort, filter, and summarize your data any way you like. Show the details of any summary value in your report.

RIP Touch ID. Apple's fingerprint sensor on iPhone and iPad models with Home buttons is about to become phased out on Wednesday, Sept. 12. While Touch ID will remain an integral part of models from the iPhone 5S to the iPhone 8 Plus, as well as the iPad Air 2 through the sixth generation iPad, Face ID will completely take over as the default security method for unlocking future iOS devices.

Hello again! In this tutorial, we are going to go over something called "operators" which will help us build upon conditions of control structures and also some variable manipulation. Without further ado, let's dive in!

Starting at 20:00 CET (11:00 PST, 14:00 EST), you can stream the live feed from Samsung's Unpacked 5 event, happening today at Mobile World Congress. While the company may have more than one trick up their sleeve, the star of the show will be the launch of the Galaxy S5.

There has been significant debate over law enforcement's right to access our digital devices in recent years. New tools from Grayshift and Cellebrite are popping up faster than ever to help government agencies, as well as traditional hackers, break into iPhones. If you're concerned, you can take steps right now to beef up your passcode and prevent outsiders from gaining access to your device.

Welcome back, my budding hackers! In previous tutorials, we've looked at some of the basic commands and concepts for using Linux. Along the way, I realized that I've failed to provide you with some basic background material on the stdin, stdout, and stderror.

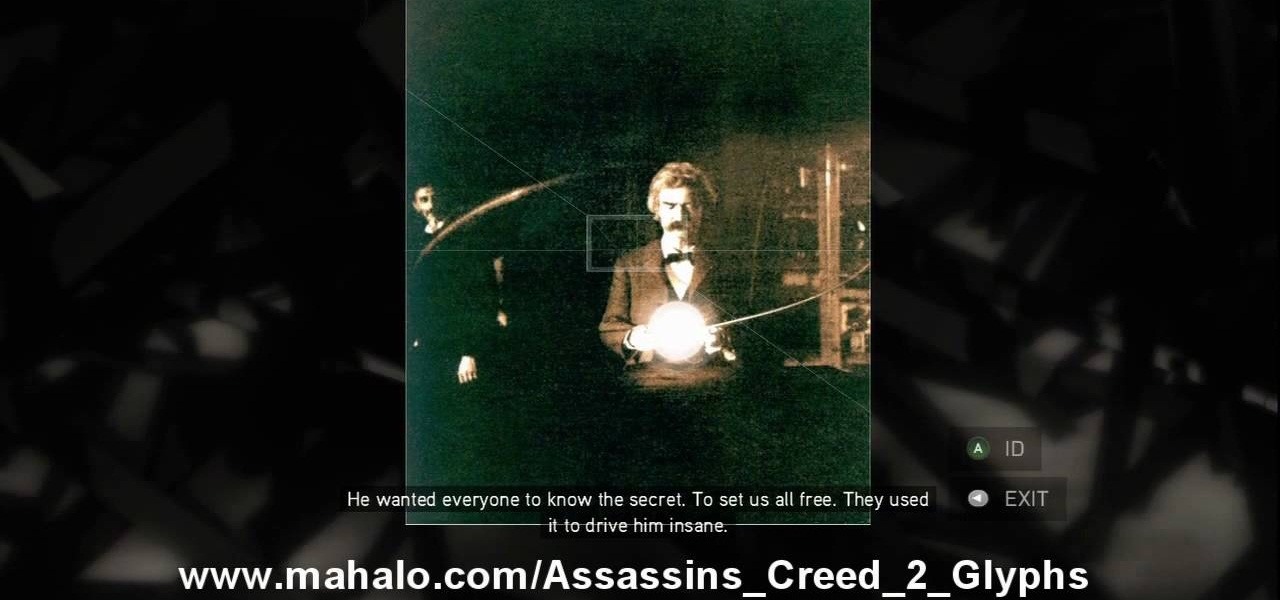
This is the 12th puzzle, entitled "Titans of Industry", in Assassin's Creed 2. Code wheel puzzle 1: The key here is in the “4=1” on the blueprint at the left of the screen. Line up the red 4 over the gray 1 and input the following code: 917240. Image 1: This one’s the opposite of the light-bulb “puzzle” from before – just move the dollar sign over the bulbs to extinguish them. Image 2: Highlight the glowing ball at the center of the image. Code wheel puzzle 2: Your hints here are the “2” on t...

When you first set up an iPhone, you'll be prompted to create a six-digit passcode to unlock your screen and access certain system settings. If you skip this step, you can always go back and create one, which we highly recommend. Without a passcode, everything on your iPhone is accessible by anyone who gets their hands on it — nosey friends, hackers, thieves, local law enforcement, the FBI — and you don't want that, do you?

Feeling lost inside a library? The Dewey Decimal System is a logical and popular book classification system for libraries and schools helping you to easily locate any book or periodical you need. Fool these steps to better understand the Dewey Decimal System.

In this economy being competitive for a job means your application must stand out above the rest. Here's how to write a cover letter to successfully introduce your resume. Make sure your cover letter follows business letter format. Your name and address must be written at the top left corner. The employer's name and address are written just below. The letter should be addressed to a specific person within the company. Paragraphs in a business letter are not indented, but instead are left just...

This how-to video is about how to use command prompt to view the blocked websites at school. This step by step instruction will help one to open the blocked websites at school.

The iPhone 11, 11 Pro, and 11 Pro Max are the most advanced flagships Apple has to offer, but that doesn't mean they're immune to occasional bugs. Anything from an app plagued with issues to a faulty software update still can cause your device to freeze up, so having the ability to force a restart can come in very handy.

It's often the smallest details that determine your overall experience with a smartphone. Unlocking your device with a PIN is an example — and iPhones have had a leg up over Android thanks to their automatic unlocking. Thankfully, this era has finally come to an end with the arrival of the Galaxy S9.

In a recent series of tweets, investor and entrepreneur (and NR50 member) Amitt Mahajan summarized the challenges and opportunities for iOS developers looking to leverage Apple's ARKit for augmented reality experiences.

Google's Gboard is by far the most popular keyboard available right now. Gboard lets you search almost anything—from regular Google searches, to emojis, and even GIFs—just by using your keyboard. The app even lets you share search results, saving you a great deal of time, which would've otherwise been spent juggling between apps and programs.

If you took your favorite search engine, gave it a witty personality, and bundled it together with a messenger-style interface, you'd have the new Google Assistant. It's great for getting fast answers—even on your follow-up questions—but its flair for fun might just be the standout feature.

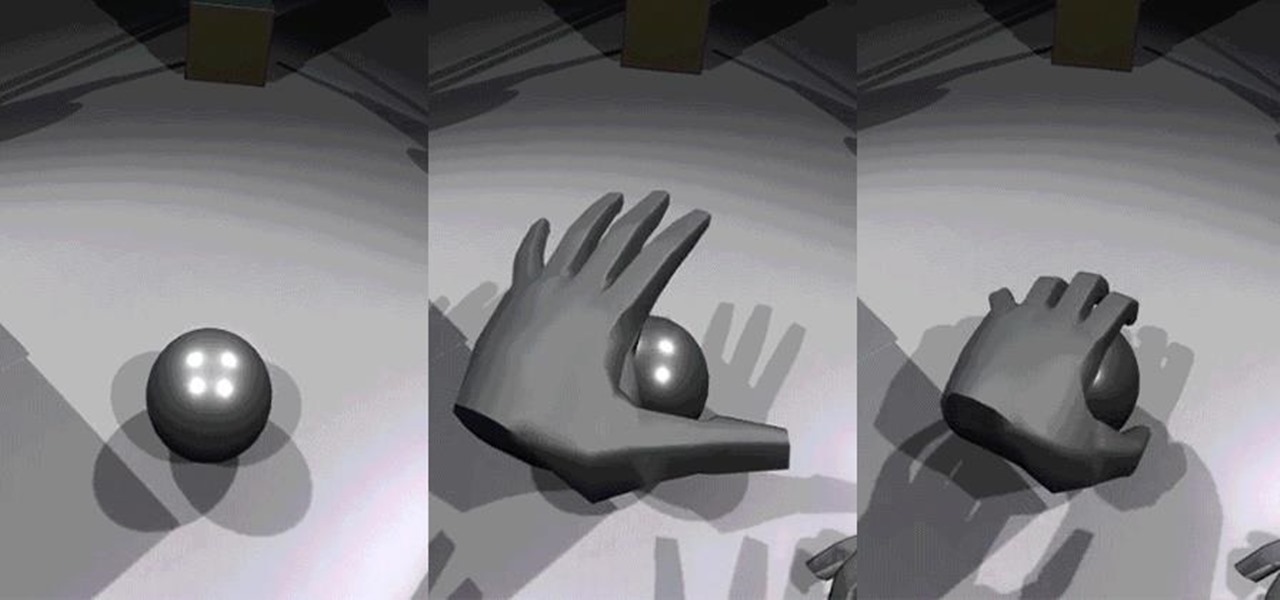
Leap Motion created gesture control for all sorts of things, including virtual reality, long ago, but developers must build in support for their tracking peripheral to use its full potential. As a result, they've created an "Interaction Engine" for Unity, the primary platform for developing virtual and mixed reality experiences, to try and take gesture interaction to the next level.

If you're like me, you don't have time to sit down and leisurely read an entire article from start to finish — but you still want to be informed throughout the day. Instead of just browsing the daily headlines, there's a free service that will summarize any article you throw at it, giving you a better idea of what's going on without committing to reading an entire article.

If you're ever faced with a situation of handing over your iPhone to law enforcement (or getting it taken forcibly), whether by the police, feds, or court system, there are things you can do to prevent them from getting access to all that potentially self-incriminating data. And it takes less than a second.

Working from home is going to be a reality for more people than ever. With Twitter CEO Jack Dorsey announcing that his employees will be working remotely for an extended period of time (and even permanently, in some cases), the workforce is rapidly changing. More companies are certain to follow suit.

If you've received a spam message in Signal Private Messenger, you know that anyone can contact you as long as they have your linked phone number. But when it comes to the people you're actually trying to have a private conversation with, how do you know it's really them?

With over 10,000 possible combinations, a four-digit passcode may seem secure, but it's fairly easy for someone to crack your code—no matter how clever you think it is. Luckily, there are many other options for securing your iPhone's lock screen—especially if your running iOS 9.

Welcome back, rookie hackers! We recently began an exploration of ways to hack using the Bluetooth protocol. As you know, Bluetooth is a protocol that connects near field devices such as headsets, speakers, and keyboards. Its minimum range is a 10-meter radius (~33 feet) and maximum is at 100 meters (~328 feet).

It may seem impossible to win an argument against an irrational person, but it turns out the tried-and-true techniques that hostage negotiators use against hostage-takers work surprisingly well in everyday situations. You may not ever deal with a real hostage situation personally, but life is full of negotiations with unreasonable people, and those conversations don't always have to end in rage or disappointment. The mental techniques that professional hostage negotiators use can help both pa...

Disengagement report numbers for self-driving car testing in 2016 on public roads in California were just released, and the biggest point we can make about them is that Waymo is very far ahead of their competitors in almost every metric.

If you're interested in nabbing superhero memory strength, the secret behind training your brain is not necessarily what you might expect. Your standard G-rated brain strengthening exercises range from crossword puzzles to Sudoku to calculating fairly simple math problems to improve short term memory, but the real clincher used by some of the pros is essentially... porn. Yep, you read right.