For as much money as they've made from North American video game audiences over the years, Japanese game developers don't seem to have very much faith in them. Dozens of great titles from their 40 years in the industry have appeared in Japan and across Europe, oftentimes even in English. But they never make it over to America, like Mother 3, Last Window: Midnight Promise, Dragon Force 2, and Tobal No. 2 (that one didn't even hit Europe).

It's a timeless doggie no-no, and one that has been paradied in numerous dog scenes in movies: A plate of delicious fried, steaming food is left by the owner on the table. The owner then leaves for a brief moment. His dog, smelling the delicious goodness, seizes the moment and quickly jumps up, snatches a piece of chicken, and devours it under the table.
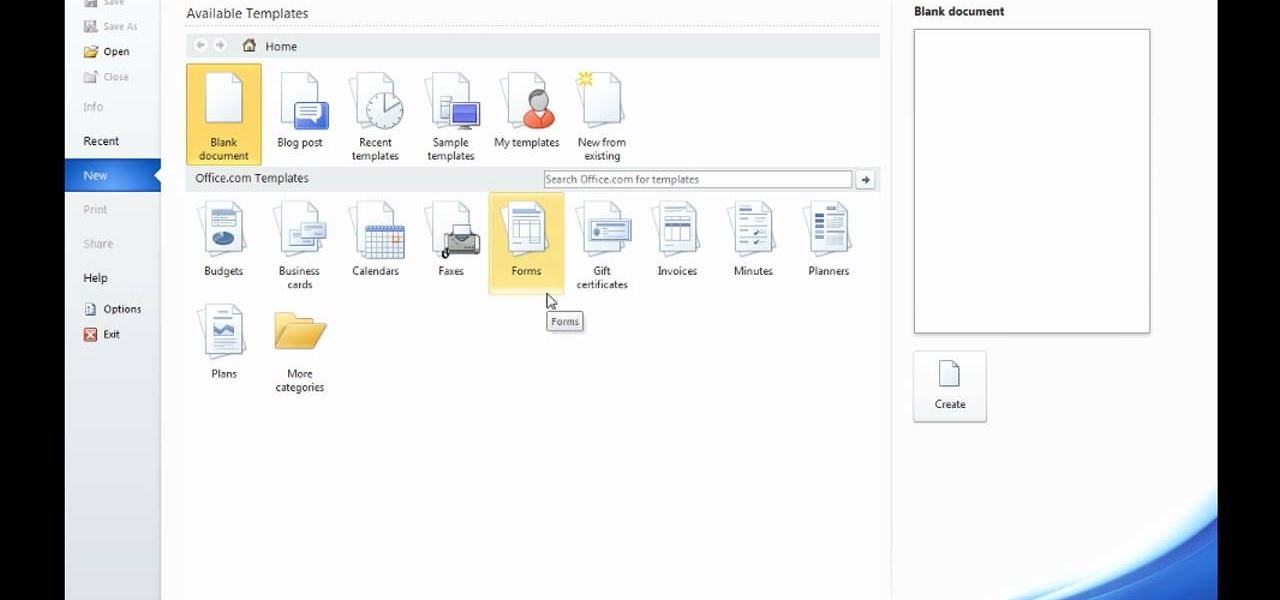
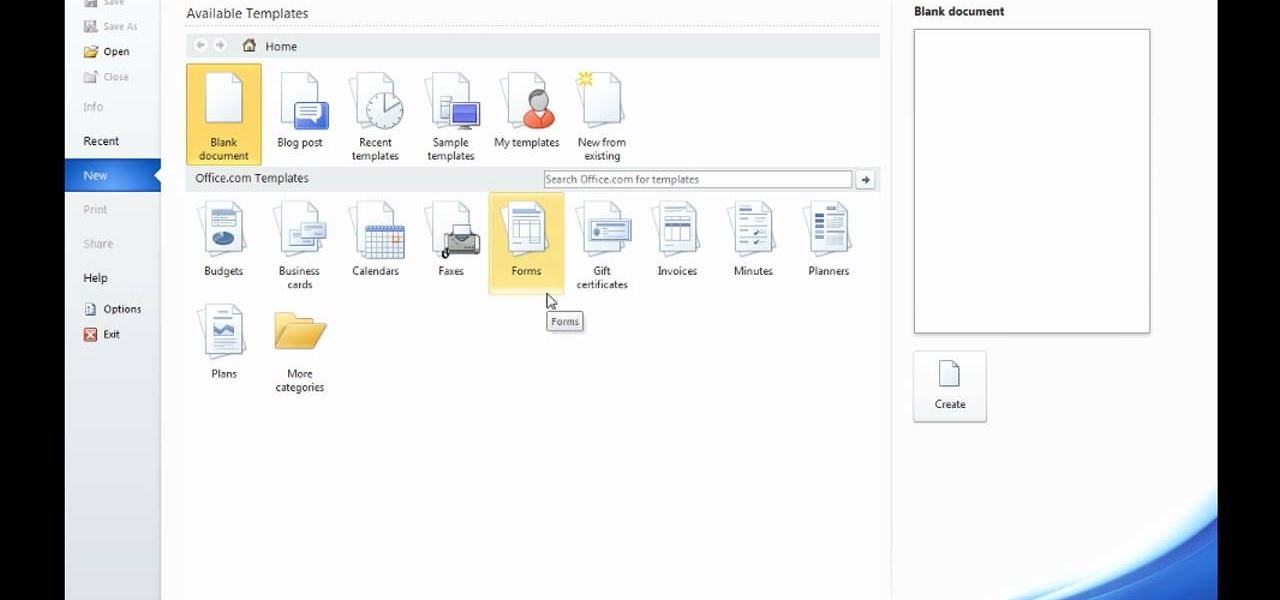
Microsoft Word 2010 prevails with new advancements. New options such as Backstage view allows the user to work efficiently and utilize new abilities when managing documents. It succeeds with new abilities that will allow the user to complete tasks quicker than before. Working with the newly enhanced ribbon allows the user to navigate with an easy, more personal customized environment. Now with more options and commands at your fingertips, it is evidently shown that Microsoft is gifting users ...
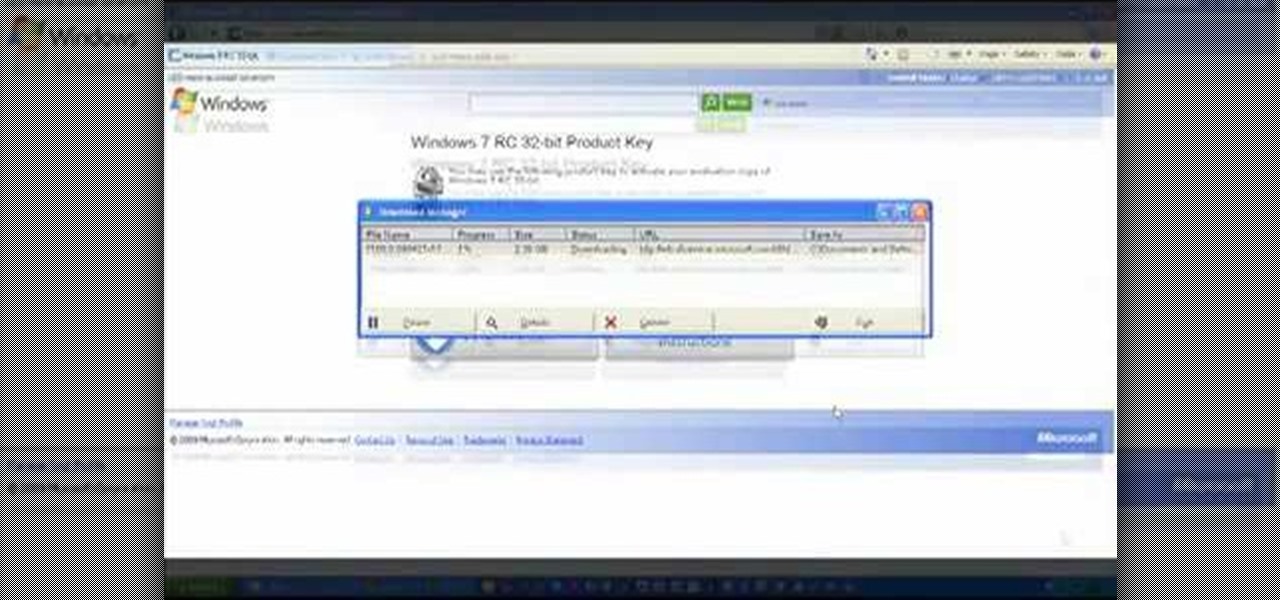
Microsoft has released its latest rendition of the Windows operating system, Windows 7. Windows 7 succeeds Windows Vista and comes with many improvements and useful updates. To install the update one a personal computer running Windows, a backup of the user's personal files and data onto a detachable hard drive is recommended to prevent data loss during the update process. The ISO image of the Windows 7 OS is burned onto a DVD. A partition is optionally created on the user's computer to allow...

Have you ever bought a cork product? Cork liner? Cork coasters? Wine… with a cork? Well, did you ever wonder where it comes from? Watch this video demonstration and you'll find out how raw cork is extracted from the Cork Oak.

With No Time to Die, the 25th installment in the James Bond saga, arriving in April and Black Widow, the first solo film for the Marvel Cinematic Universe's own secret agent, following a month later, what better way to get in the espionage mood than some augmented reality spy gaming?

There are two types of bricks ("brick" as in "bricking your phone")—soft and hard. Soft bricks are recoverable—something has probably gone wrong with some critical system partition, causing a bootloop or inability to boot in some way. Fine. Re-flashing everything should fix that instantly. Hard bricks are not recoverable—if you manage to hard-brick your Nexus, you are in trouble.

The COVID-19 pandemic has created a frenzy for news and information that is nearly unprecedented in the smartphone era, with a major side effect of misinformation. Now, major tech companies are making it easier to ask for advice about novel coronavirus from their respective digital assistants. Results may vary, but Apple and Google are the most useful at the moment.

When you think about consumer VR headsets, you either imagine a computer-tethered powerhouse like the Oculus Rift and HTC Vive, or something portable yet limited that utilizes your smartphone like Google Cardboard. Somehow, we haven't seen much in-between, but the Idealens aims to fill that gap.

At Next Reality we mostly focus on augmented reality, but that doesn't mean we're not also absolutely obsessed with virtual reality, too. If the thing that's been keeping you from diving into the deep end of VR has been clunky tethered headsets or the expensive but necessary gaming PCs, then it's time for you to try the Oculus Quest, which is currently available to buy here for less than most gaming systems on the market.

When it comes to the business of augmented reality, companies that aren't already introducing new products or apps are focused on producing the AR technology of the future. But in the realm of real products and apps, Magic Leap continues to show off what its headset can do, this time via a new app that transports users to the ocean's depths.

Zenge came to my attention as a free game on the Google Play store — it will remain free until midnight, so anyone catching this review on the 25th, download it ASAP — but I imagine it would be worth the typical $0.99.

If you're someone who loves to read, you've probably read a book that made you want to hop into the story and live in the world that wasn't your own. Reading has a way of letting us escape into other worlds and experience things that we normally wouldn't be able to. Augmented reality is similar in that way. Which is why it makes sense that the two would be combined to create an incredible, immersive new way of reading.

Augmented, mixed, and virtual reality are all a little bit different, but as many expect—including Metavision—the continuum of our next realities will converge and give us one head-mounted display (HMD) platform that can do it all. If Vrvana, a Canadian company building AR and VR headsets, succeeds, that convergence could begin as early as next year.

Welcome back, my tenderfoot hackers! Those of you who have been reading my posts here for awhile know how much I emphasize good reconnaissance. Novice hackers often jump into a hack/exploit without doing proper recon and either fail or get caught. Experienced and expert hackers know that 70-80 percent of a good and successful hack is dependent upon successful and accurate reconnaissance.

Proxies can be quicker to use than a VPN for specific applications, like web browsers or torrent clients. Both services will hide your true IP address, but a VPN is slowed down because it encrypts all data through a VPN network, while a proxy just acts as a middleman for fetching and returning requests from a server on your behalf. When speed is needed, go proxy.

Hi there again, aspiring hackers (and veterans as well)! I'm going to explain how to perform a dictionary attack on a WPA/WPA2 protected network with Wifite. Please note that this doesn't work with WPA Enterprise For that end, you'd have to use an Evil Twin to get the "Enterprise" auth attempt, and then crack it.

If you're worried about the security of your Mac, there are easy measures to prevent the most dangerous attacks. Named after the tactic of accessing an unattended computer in a hotel room, we can thwart "evil maid" attacks with Do Not Disturb and LuLu, free macOS tools by Objective-See that keep an eye on unattended computers and flag suspicious network connections that indicate a malware infection.

While the iPhone XS actually comes with a smaller battery than the iPhone X, Apple claims it, along with the XS Max and XR, offer users longer battery life than last year's first Face ID model. While that may be true, your new iPhone still ships without meeting its full battery-saving potential. There are, however, steps you can take to make sure your X, XS, XS Max, or XR makes it from morning until night.

Web application vulnerabilities are one of the most crucial points of consideration in any penetration test or security evaluation. While some security areas require a home network or computer for testing, creating a test website to learn web app security requires a slightly different approach. For a safe environment to learn about web app hacking, the OWASP Juice Shop can help.

While the security behind WEP networks was broken in 2005, modern tools have made cracking them incredibly simple. In densely populated areas, WEP networks can be found in surprising and important places to this day, and they can be cracked in a matter of minutes. We'll show you how a hacker would do so and explain why they should be careful to avoid hacking into a honeypot.

It's been a while since I wrote up an article for this series but I did say that I'd be covering some WinAPI. So if you're interested in programming for the Windows platform, hop aboard and follow along.

People fundamentally distrust magicians. And they should. The illusions they proffer are just that, illusions meant to astound rather than tangible interactions and results that have weight and meaning in our real world. Our lizard brains know this, and, no matter what the outstanding feat of "magic" presented, we nevertheless hold fast to our survival-based grip on the truth: we just saw simply "can't be real."

Many popular IoT devices have terrible security. For instance, a hacker who's on the same Wi-Fi network as a Sonos speaker can assume direct control over the device's behavior. If an IoT device doesn't secure the messages used to control it over a network, it's easy for somebody to write a few Python scripts to make it do whatever they want.

Design flaws in many routers can allow hackers to steal Wi-Fi credentials, even if WPA or WPA2 encryption is used with a strong password. While this tactic used to take up to 8 hours, the newer WPS Pixie-Dust attack can crack networks in seconds. To do this, a modern wireless attack framework called Airgeddon is used to find vulnerable networks, and then Bully is used to crack them.

The internet is constantly under siege by bots searching for vulnerabilities to attack and exploit. While conventional wisdom is to prevent these attacks, there are ways to deliberately lure hackers into a trap in order to spy on them, study their behavior, and capture samples of malware. In this tutorial, we'll be creating a Cowrie honeypot, an alluring target to attract and trap hackers.

Internet Relay Chat, or IRC, is one of the most popular chat protocols on the internet. The technology can be connected to the Tor network to create an anonymous and secure chatroom — without the use of public IP addresses.

For as long as anyone can remember, older men and younger women relationships have existed. Some may wonder how the older man succeeds at courting a younger women. We found out how they do it! Date younger women.

Most of the stuff on HBO definitely succeeds in supporting their company motto "Not TV". True Blood is no exception. Thus, I will include it here as a pseudo movie poster.

What if everything in life was controlled by augmented reality? Keiichi Matsuda imagines: "The architecture of the contemporary city is no longer simply about the physical space of buildings and landscape, more and more it is about the synthetic spaces created by the digital information that we collect, consume and organise; an immersive interface may become as much part of the world we inhabit as the buildings around us.

Here's another latest in robotics: researchers at the Italian Institute of Technology (IIT) have developed a robot that flips pancakes. The most interesting aspect of the project is the use of kinesthetic teaching, in which the user "trains" the robot by example. The user grasps the robot's limb, and guides it through the motions the user would like it to adopt. This bot takes about 50 trials to get it, but in the end succeeds. Previously, I Want a Robo-Chef in My Kitchen.

Dumb but honest. Like a golden retriever covered in ketchup

PC Gamer represents all that was awesome about games journalism in the '90s, now sadly diminished. Brilliant, funny, full of integrity, and solid print sales were always present, and with the tragic exception of the latter, still are. Video game magazines were hit harder than nearly any other magazine vertical when the internet began its uncoordinated, but inevitable assault on print media. Magazines are now struggling to find their place in a world filled with more competitors than paying cu...

For this week's review round-up, we bring you two games from opposite sides of the indie world. One is a free online hybrid shooter/platformer combining elements of Team Fortress 2 and Minecraft. The other involves driving jeeps around and shooting things as fast as possible. Both are great.

Four years ago Mind Candy was a pretty small game company. They were best known for their revolutionary but short lived ARG Perplex City, and had no other successful franchises to fall back on when that ended. Their plan to save it? Start a free online social game for children ages 7-12 called Moshi Monsters, where kids can create monster pets, raise them, and socialize with one another in a controlled, safe environment.