If you're like me, getting as much sleep as possible is priority number one. With more and more time spent on or around our cell phones, it's becoming harder and harder to block out all the noise.
There are thousands of articles published every day about smartphones, tablets, eReaders, and any other kind of gadgets you can think of. The problem is that most people only really care about news related to the devices they actually own. So how do you filter out all of the stuff you don't care about? That's what Drippler does. It pulls news, tips, and app reviews and recommendations from all over the web and puts them all in one place, but only for the devices you want to read about. You te...

You can easily share and transport your photo and videos on the Canon EOS 7D by using the wireless file transmission option. See exactly how sharing and downloading your files to computers and other devices works in this video. When the digital SLR camera is combined with the WFT-E5A Wireless File Transmitter, transmitting is easy.

Rain and snow will ruin your touchscreen device in no time. Want to protect it without spending a fortune on a bulky waterproof case? This video demonstrates a quick-and-easy expedient—a waterproof plastic bag!. For specifics, and to get started making your own plastic bag phone case, watch this handy rainy-day how-to.

It's happened to all iOS users: You're talking to a friend or watching TV, and all of a sudden, you hear "I'm not quite sure what you've said." Apparently, your phone heard something that resembled "Hey, Siri," and activated the assistant. But now, thanks to a new patent from Apple, the days of unexpected Siri may be numbered.

With the new iOS 4.2 (and 4.2.1) firmware for all mobile Apple devices, printing from your iPhone, iPad or iPod Touch has become easy… well, maybe not. Despite the new AirPrint software in iOS 4.2, it can still be difficult to print papers and photos from your mobile device since Apple removed AirPrint from the Mac OS X 10.6.5 software update, due to some kind of legal dispute.

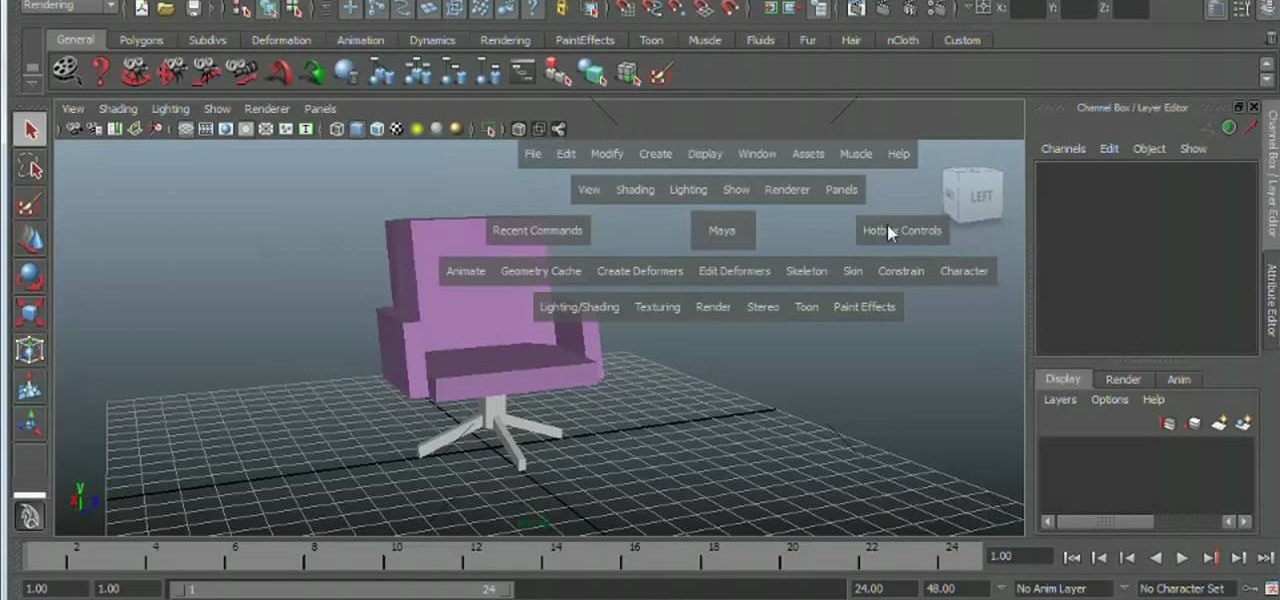
Meet the Maya 2011 Hotbox tool, a highly useful on-screen device for navigating your projects. Whether you're new to Autodesk's popular modeling software or a seasoned 3D artist just looking to better acquaint yourself with the Maya 2011 workflow, you're sure to be well served by this video tutorial. For specifics, and to get started using the Hotbox to navigate your own Maya projects, watch this free video guide.

In this how-to video, you will learn how to update your iPhone or iPod touch to 3.1.2 firmware for free. First, make sure you have iTunes installed on your computer. Download the correct firmware for your specific model on the internet. Once this is download, open iTunes and select your device. Hold the shift key and click restore. Select the firmware file and open it. Hit the restore button in the new window. This will then update the device. This may take a while. Once it is done, the updat...

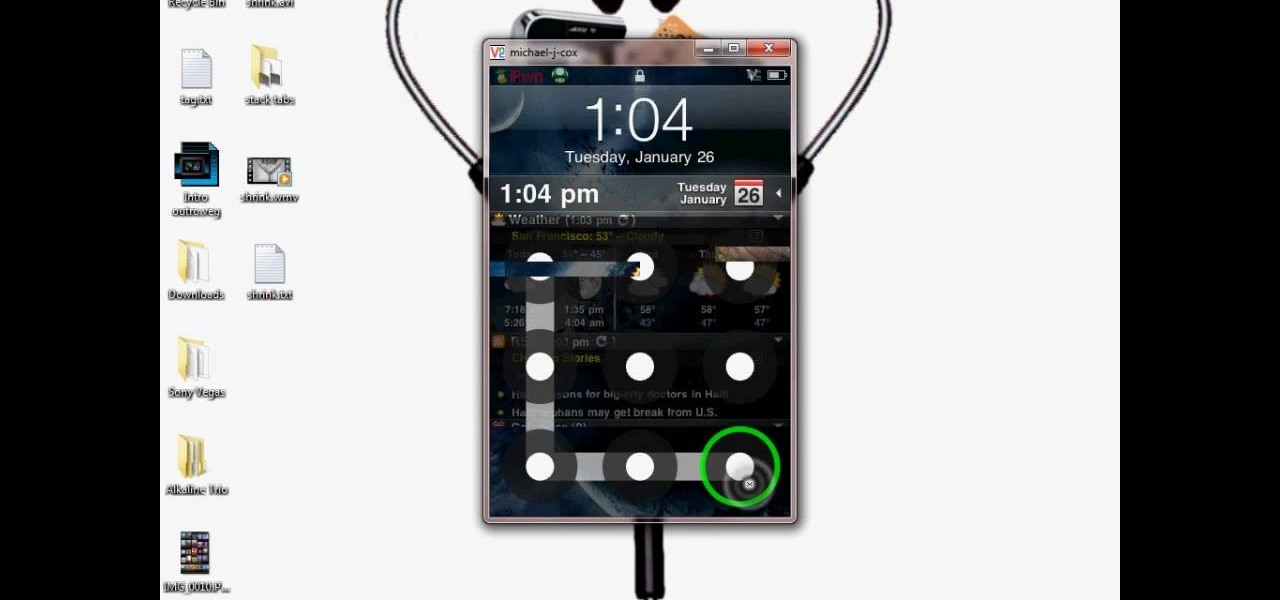
This video tutorial from DrJailbreak presents how to download and install Androidlock on your iPhone and iPod Touch.Androidlock is a type of application that locks screen to prevent unauthorized access. You have to draw a specific pattern on the screen to unlock your device. It is advisable not to create too difficult Androidlock pattern because you can forget it.You also can turn off Androidlock if you open subsettings, select More and then Mobile Substrate Add-ons option.To get Androidlock,...

This video tutorial shows you how to restore your iPhone or iPod to factory settings or to restore it to a specified firmware update. First you are shown how to enter the DFU mode or device firmware update mode on your device. Download the specific firmware you wish to restore to and make sure you already have iTunes installed as well. Open iTunes and connect your device to the computer via USB by putting it off and holding the home button while plugging it in. Click OK on the dialog that pop...

Starting today, you can experience all the unique feature of Samsung's next flagship device, the Samsung Galaxy S5, right on your Galaxy S3 or other Android device.

Windows 7 has a new feature called Device Stage. It's a powerful and handy hub for all of your electronic gadgets that connect to your PC. It's device management for the power user! Microsoft shows you the layout real quick, so watch and learn.

Learn how to delete photos from an iPod Touch, iPod, iPhone, or any kind of iTouch. The trick is to hook it up to your Windows PC or Mac and use iTunes to sync with it. You'll then be able to go to the photos tab to remove specific photos from your iPod/iTouch device.

When you're in a bind and need an internet connection for your laptop, look no further than your iPhone. Using the Personal Hotspot feature in iOS, you can share your iPhone's internet connection with other devices by way of Wi-Fi, Bluetooth, or even USB.

The Samsung Galaxy Tab 2 (7.0) 4G LTE on Verizon has only been released for a couple months now with good reviews. It comes with dual cameras, memory expansion, and very quick 4G LTE speeds, without needing a contract. While most users are satisfied with the tablet as is, there are others that prefer rooting the tablet in order to install their own custom ROM. Now you can do it with the Samsung Galaxy Tab 2.

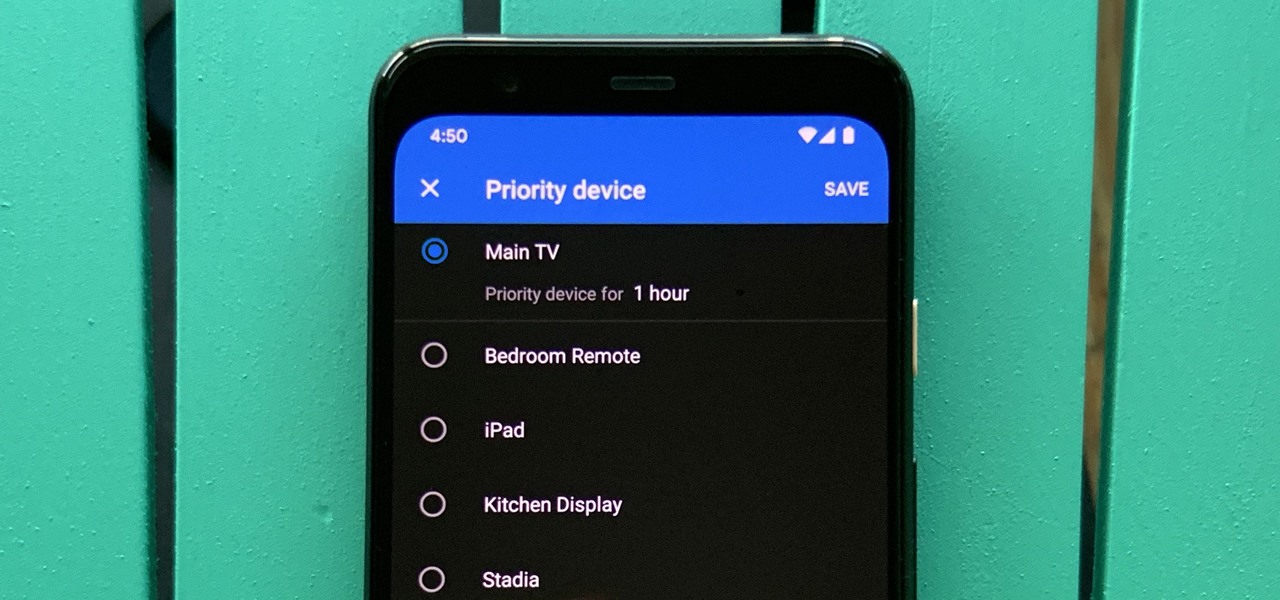
One of the main goals of Google Wifi (and Nest Wifi after it) is to make managing your internet connections as simple as possible. A great example of this is how easy it is to prioritize one device and allot it more bandwidth when your network is bogged down with other traffic.

Today in Santa Clara, California, at the Augmented World Expo, Scope AR revealed a major new update that will add markerless tracking for their remote assistance application, Remote AR, on standard devices.

There are many reasons to keep adult websites off your iOS device. They can pop up accidentally at the least opportune moments, can give your device malware, and are not welcome in a kid-friendly home.

While we're usually responsible for leaking our own private information through mediums like Facebook, there are other times when we mistakenly and unwillingly allow certain applications to scour through our personal data. Some apps may have enabled permissions for internet access, thus allowing it to share said data with its external servers.

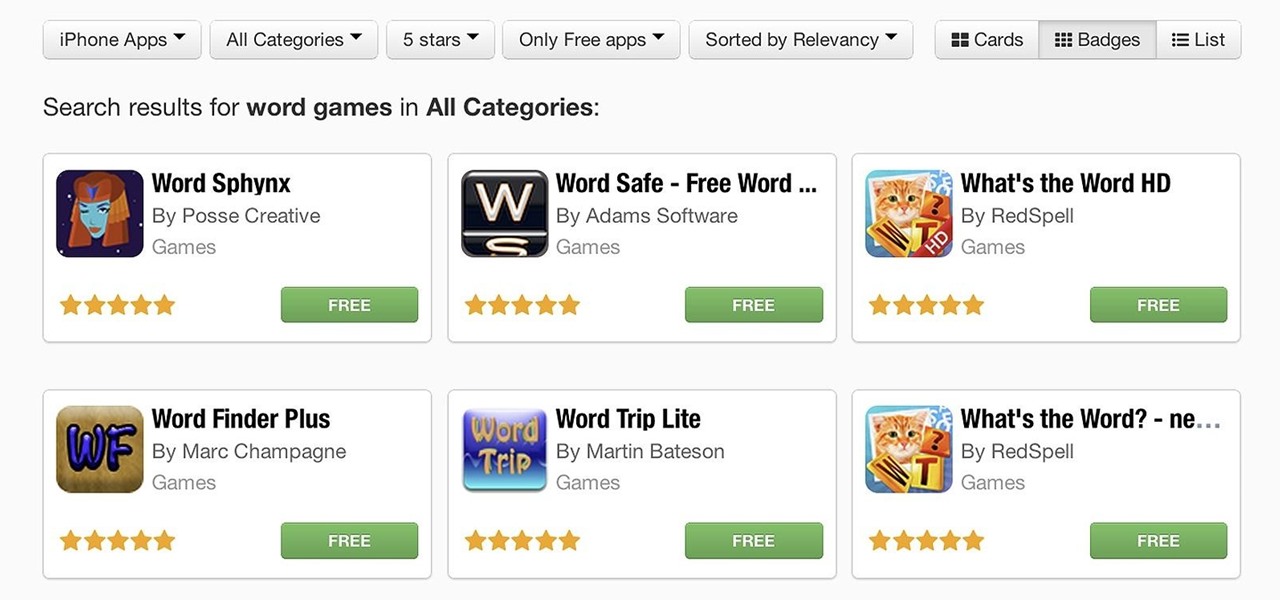
If you have an iOS device, chances are you've spent a decent amount of time in the App Store—without at least a few apps, smartphones are pretty boring. There's an app to do just about anything you could ask for, but the problem is finding them. Searching the App Store sucks.

Depending on what mobile device you own, you'll see something that says "via device name" next to the date of your post on Facebook. If you're device is not recognized, you'll simply see a "via Mobile" note, which is what happens when I post from my phone. If you allowed your iPhone to be called iPhone when you logged into the app, it'll show up as a recognized device on Facebook, and will post "via iPhone." Same thing goes if you have a Samsung Galaxy S3 or Nexus 7 or iPad. It could also jus...

If someone violates a protective order, there are — the remedy would be the police would be involved. You'll get arrested. So, basically, a protective order is usually good for two years, and it has all the specific things you cannot do. For instance, you can't go by that person's — within 200 feet of them or their residence or their employer. So it has some very specific things. A restraining order is different. It's a standard thing that's given that's a mutual thing where it just says be n...

Who doesn't love a refresh? Samsung's upcoming One UI makes it easier to use your device with one hand and adds a fresh coat of paint to the formally "Samsung Experience" skin. While you're probably looking forward to installing One UI on your phone, not all Galaxies are equal — your device could be one of the first to receive the update, or it could never see One UI at all.

On Wednesday, June 6, the people at Magic Leap finally (FINALLY) decided to give the public a dedicated, slow, feature-by-feature walkthrough of the Magic Leap One: Creator Edition. How was it? About as good as it gets without actually getting to see what images look like through the device when wearing it.

Sharing your Wi-Fi password is like giving an unlimited pass to snoop around your network, allowing direct access even to LAN-connected devices like printers, routers, and security cameras. Most networks allow users to scan and attempt to log in to these connected devices. And if you haven't changed the default password on these devices, an attacker can simply try plugging them in.

If you've ever owned an HTC device or anything in the Nexus line, odds are, you have typed the word "fastboot" into your command line at one time or another. That said, odds are, you have only just barely scratched the surface of what this handy little Android tool can do. Let's take a deeper look.

Welcome back, my hacker noviates! In a recent post, I introduced you to Shodan, the world's most dangerous search engine. Shodan crawls the globe from IP to IP address, attempting to pull the banners of each web-enabled device and server it finds.

Let me paint a picture for you. You're on a long flight home, and while listening to music on your Samsung Galaxy S10, a great song comes on. You want your friend to hear it too, who's also listening to music using a pair of Bluetooth headphones. Thanks to Dual Audio, you can easily share your experience.

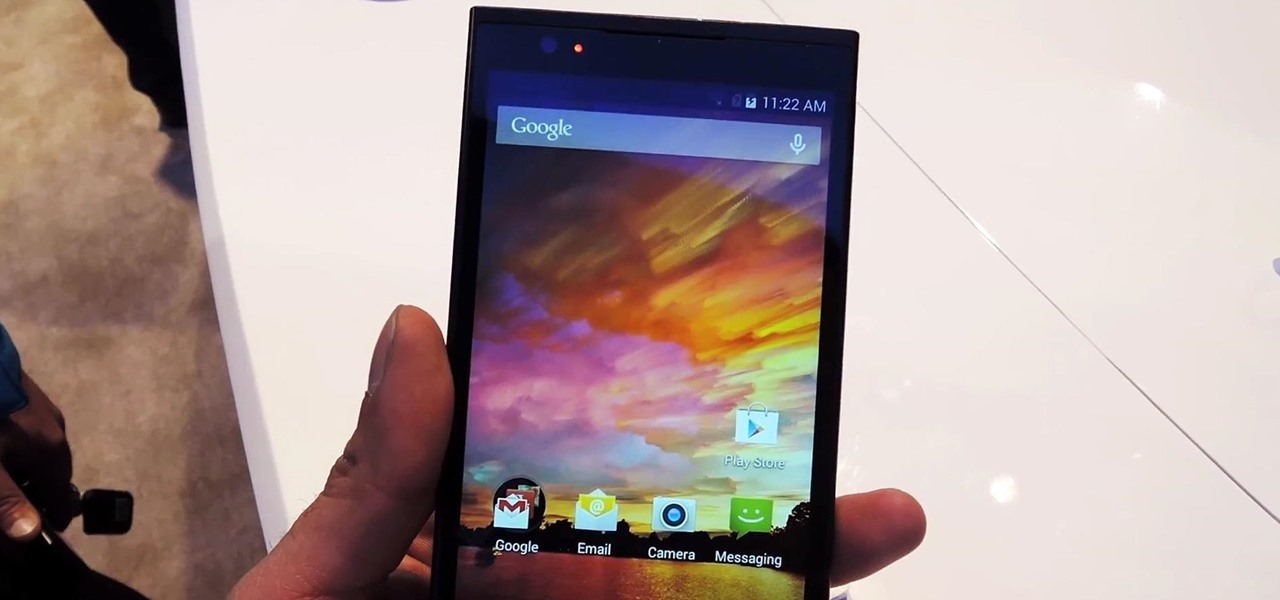
Sometimes specs aren't everything, especially if you prefer value over the bleeding-edge. Enter the ZTE ZMAX, an Android phone that you can get right now for less than $200—cheaper than even the Nexus 5 or OnePlus One. If you're looking for a cheap high-end phone, it's hard to go wrong with one that sports a 5.7-inch display, expandable storage, and a massive 3400mAh battery that'll easily get you through a full day of use.

While the majority of America was watching the Super Bowl yesterday, the crew over at the evad3rs was finishing its work on their untethered iOS 6.1 jailbreak called evasi0n. Well, the wait is finally over!

Any electronic equipment is bound to accumulate dust, slight moisture, dirt or any combination of the above on its sensitive parts over time. The delicate nature of items also means further care is required.

This is a presentation of different types of immune responses in human body. There are two types of immune systems i.e., non specific and specific or adaptive immune system. Again, non specific immune system is sub- divided into barriers. It is the first line of defense. The second line of defense is the inflammatory response. They are phagocytes. These are all products of white blood cells. It is also called as leukocytes. Lymphocytes are another type of white blood cells which are carriers ...

Cordelletes, slings and prusicks are three of the more specific-use elements of rock climbing equipment. Learn how to use prusicks, slings and cordelettes in this climbing video tutorial. Take action: slings can be used to clip gear or set up anchors, prusicks are back-up descending device, and use a cordelette for anchor or for prusick. Josh, the instructor of this how-to video from Live Strong, is an avid climber that resides off the coast in central California. He has managed for a mountai...

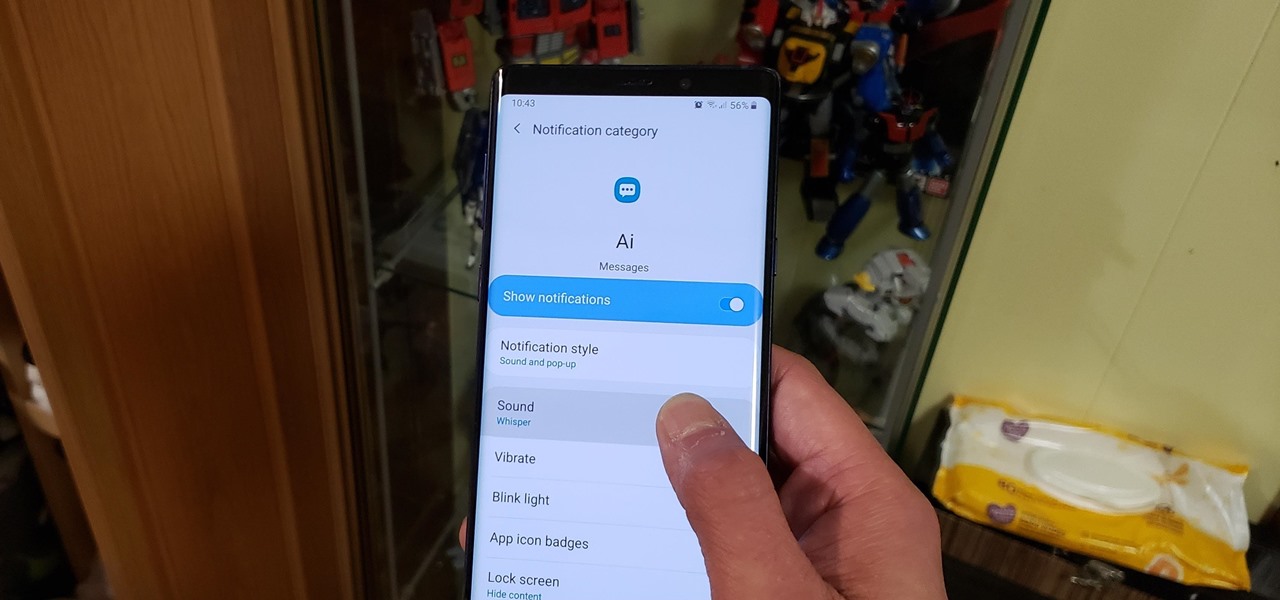
Some messages take precedence over others, so having the same notification tone for all your threads isn't always the best solution. Fortunately, Samsung Messages has a simple option you can tweak to set custom sounds for specific chats to help you stay on top of priority conversations and reply much faster.

We're still weeks away from a probably HoloLens 2 release, but Microsoft's immersive computing team is still hard at work on other aspects of its "mixed reality" ecosystem.

When BlackBerry made the move to Android OS, they were aware of the limitations it presented. Unlike with BB10, they didn't create the operating system and would have to deal with the vulnerabilities already included. As a result, they added numerous security enhancements, and at the heart of this is DTEK.

Microsoft recently announced that they're producing HoloLens units fast enough to keep up with demand, which means you can acquire up to five dev kits right now—if you've got the $3,000 fee for each one.

infosecinstitute posted a handy article about what to expect in the new year for cyber security, along with highlighting major game changers from 2015; 2016 Cyber Security Predictions: From Extortion to Nation-state Attacks - InfoSec Resources.

Whether you are sending your phone in for repairs or finally selling it to upgrade to a new flagship, you are going to need to make sure all of your personal data is removed from your device.

When security firm Zimperium discovered Android's biggest security risk in years, it sent shock waves through the ecosystem. As a result, Google, LG, and even Samsung decided to change the way they issue updates to their devices, by pledging to release monthly security patches to plug up loopholes exactly like this one. Yeah, it's that big of a deal.