Whether it's embarrassing pictures and videos on your smartphone, or files you just don't want anyone reading, there are plenty of ways to hide them. For most devices, that means installing third-party apps like Gallery Plus - Hide Pictures, Sectos - Photo & Video Vault, TimeLock, or Hi App Lock.

The creation of private browsing was brought upon by the backlash against ad tracking and other ways that sites and agencies take away users' privacy online. People were tired of getting spammed with ads for Vitamin C pills simply because they visited WebMD. Private browsing is now built into all of the major browsers and is used frequently. While private browsing is more infamously known as the "Porn Portal," and does prove to be a great way of keeping racy content out of the sight of others...
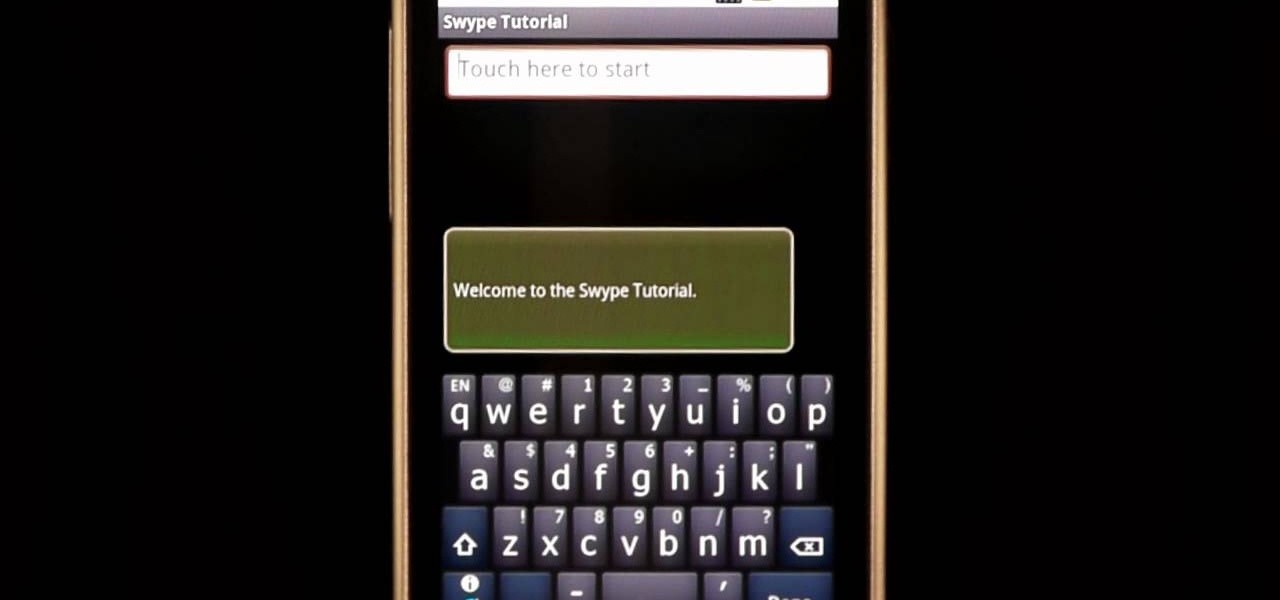
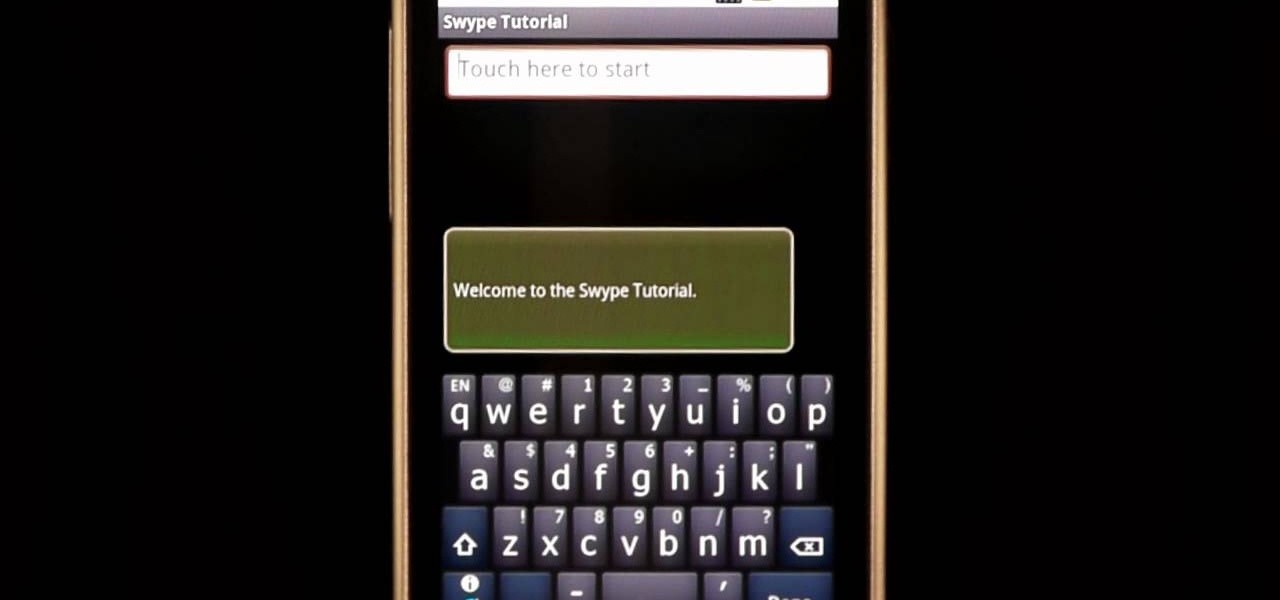
In this clip, learn how to use the Swype Key while texting with Swype on your cell phone. The Swype key is where all of your options are like dictionaries, tips and tricks, help menus and everything else you may need.

Welcome back, my rookie hackers! "How can I travel and communicate over the Internet without being tracked or spied on by anyone?" It's a question many Null Byteans have asked me, so I have decided to write a comprehensive article addressing this issue.

The primary purpose of hot keys in StarCraft 2: Wings of Liberty, is so that you can control the command card in the bottom-right portion of your screen, without using a computer mouse. But the hot keys have other uses, too. The first video covers the basics, and the second video covers using these shortcuts to building control groups. The third video shows you the other remaining hotkeys available for StarCraft 2.

Ever wanted to learn how to make a rekey a lock? Well, there's no better time than now to start learning the craft of so many locksmiths out there... key making. Just watch this video tutorial to see how to properly make a replacement key for a lock.

In this ten-step video tutorial, you'll learn how to quickly copy keys using a camera, printer and Dremel tool. With this ten-step process you'll learn the necessary steps to copy almost any key... even if you only have access to it for a brief period of time.

Whether you're a celebrity or someone with something to hide, Facebook allows you to keep your "friends list" private so you can protect the identities of your Facebook friends. But it only kind of protects them.

Welcome back, my novice hackers! In a recent tutorial, I showed how the SNMP protocol can be a gold mine of information for reconnaissance on a potential target. If you haven't already, I strongly suggest that you read it before progressing here, as little of this will make much sense without that background.

Stay secure on public wireless networks by making your own FREE virtual private network (VPN). This tutorial shows you how to set up an OpenVPN server and connect to it from your laptop.

Woodturning is creating items out of wood on a lathe. Learn how to create key chains and light pulls from a woodturning expert in this free crafts video series.

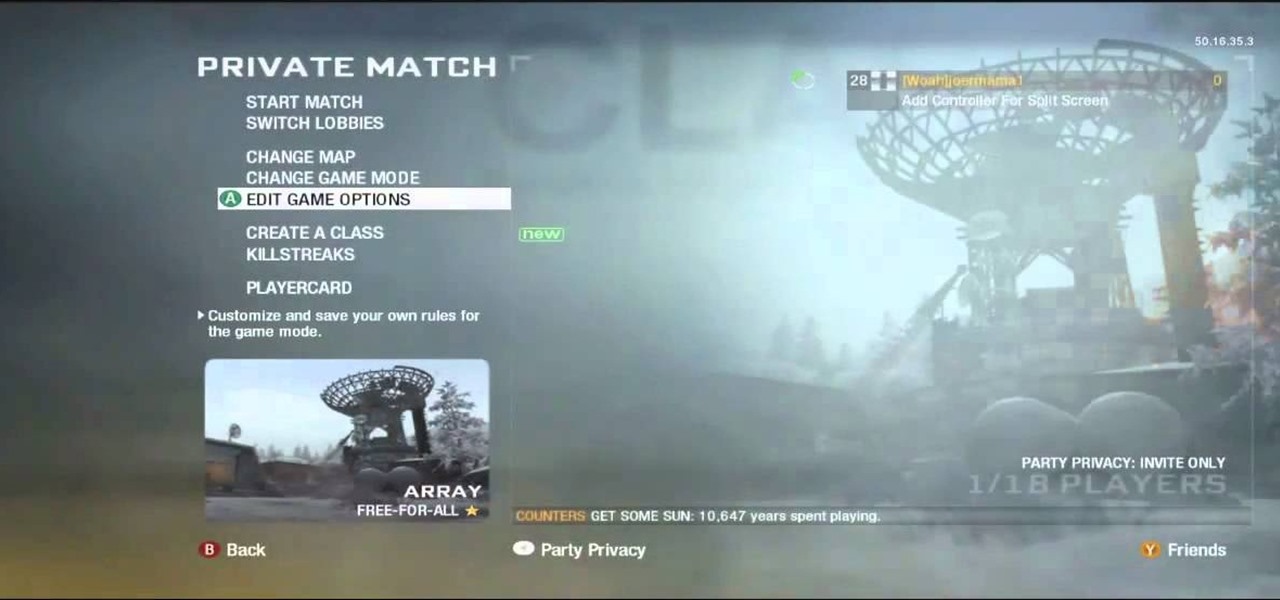
This video shows the viewer how to boost, gain XP very easily, on ‘Call of Duty: Modern Warfare 2’. The first stage is to get a friend to join your game. Then search for the Team Tactical game mode until domination appears. Then back out and go to a private match. Change your clan tag to ‘aaaa’ and hover over Ground War until the game starts. The map usually used for this is Rust as it is so small. The game will behave like a private match but you will be gain XP for all kills. This g...

In just a few simple steps, you'll have your piano keys sparkling like new. You Will Need

Always losing your keys? A big bulky key chain might feel annoying in your pocket, but it's not likely to get lost in your purse or in all that trash you carry around. This video tutorial shows a real simple key chain ring you can make and keep those keys easy to find. All you need is the key ring, two shoelaces, a pair of scissors, and a lighter.

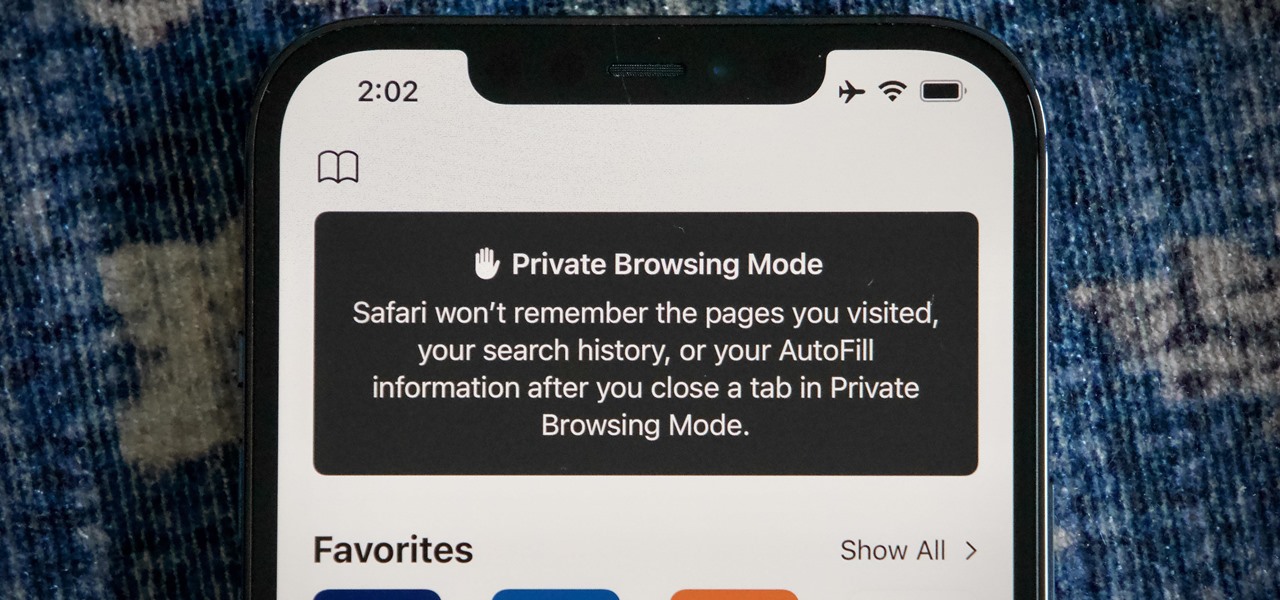
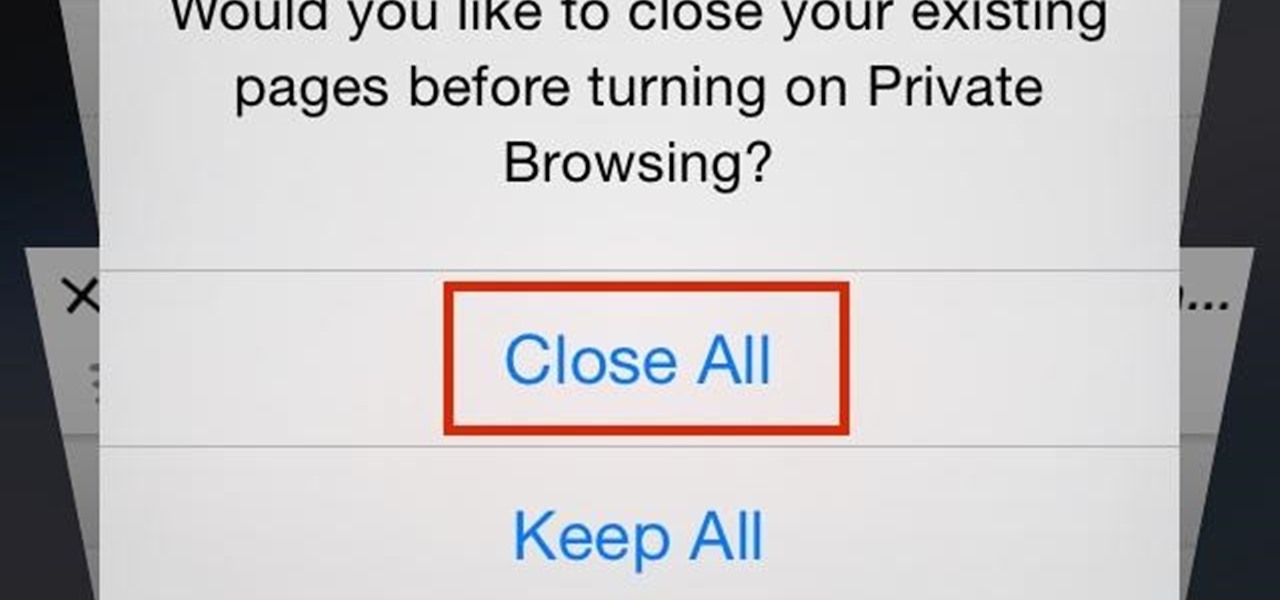
When you open Safari for the first time after updating to iOS 15, you'll instantly notice its search bar is now at the bottom, and its Page Settings menu has moved with it. For tabs, moving between them is as easy as swiping on the Tab Bar or selecting one from the new grid view, but you may get confused whenever it's time to open a private window.

While most of us don't think twice about dragging a pattern or using Touch ID to open our phones, or entering a password in for our email and bank accounts, these features are there to protect some of our most private information. Only problem is, they don't do a good job of it.

Closing all of your tabs open in Safari is not an exceptionally quick task—you have the choice of either tapping the X on the left edge of each page or swiping each tab to the left of the screen. If you have a load of tabs open, you'll have to swipe or tap through all of them. Instead of wasting time, I'm going to show you the quick way of closing all of the open tabs in Safari.

In this video, we learn how to clear browsing history and cache in Firefox and Internet Explorer. First, while in Firefox, go to the tools menu, then click on clear private data. In the new window, click on the items that you want to have cleared, then click "clear private data now". After this, the computer will clear out all the internet files. Next, while you're in Internet Explorer, go to the tools menu, then click on "internet options". Once in here, click the appropriate sections to cle...

In this video tutorial, viewers learn how to use the Slow Keys access tool in a Mac OS X computer. The Slow Keys feature is located under the Keyboard tab in the Universal Access window. Once Slow Keys is turned on, users also have the option of using key click sounds as additional feedback when a key is pressed . Users are able to set the Acceptance Delay to determine how this feature behaves. The delay of the sound can be set from long to short. This video will benefit those viewers who use...

In this video tutorial, viewers learn how to use the Sticky Keys feature in Microsoft Windows 7. To use the Sticky Keys, click on the Start menu and open Control Panel. In the Control Panel window, double-click on Ease of Access and click on Change how your keyboard works under the Ease of Access Center. Then click on Set up Stick Keys and check the option Turn on Sticky Keys. This video will benefit those viewers who have limited dexterity and find it difficult to use complex keyboard shortc...

There aren't a lot of games with 3D maps where you can't break out of the levels in some way, and Black Ops is not different. This video will teach you a barrier breaker that you can use to get out of every multiplayer map in the game. Only use this in private matches unless you want it to go away!

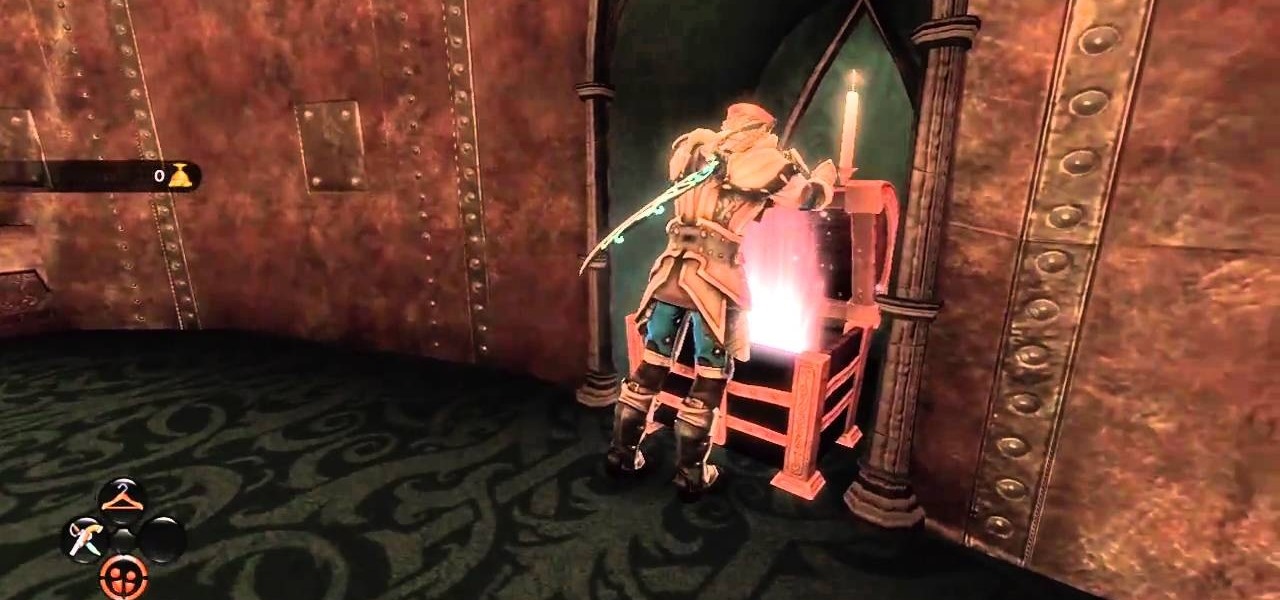
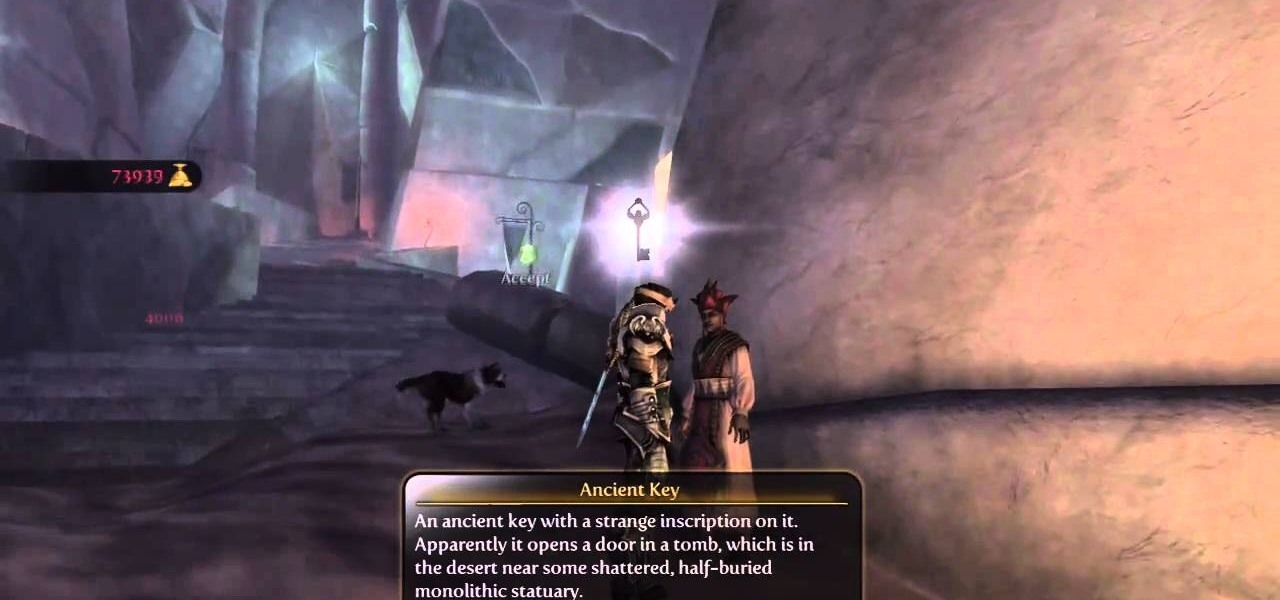
The Sanctuary menu system in Fable 3 has spawned some controversy, but it's pretty novel when you consider that there are a hidden Gold Chest and Gold Key right there in your pause menu! Watch this video to learn how to unlock and find the Gold Key and then the Gold Chest in your sanctuary.

The Gold Keys in Fable 3 are needed for unlocking all sorts of fun legendary weapons and such, but finding them all is appropriately challenging. If the tedium of searching for them has gotten to you, watch this video to learn where to find and unlock each and every one of the gold keys.

In this video, we learn how to find your Windows product key. Start off by going to Magical Jellybean Keyfinder. This website has a download that will find your product key for your Windows program. This is a great and necessary tool if you happened to loose the product key that came with your computer. This is also great for computers that already had Windows installed, and you never had the product key in the first place. Once you install this on your computer, you just open it up on your d...

Flash Actionscript 3 is a wonderfully powerful, but somewhat obtuse, tool for creating websites. This video will teach you how to use one particular function in the language, creating a class that has multiple key detection enabled. This will allow you to create a website where users can key in multiple inputs and the website will respond appropriately.

Ever wish there were a way to upload a video to YouTube without making it available to anyone with an Internet connection? While you might know about the option to make your uploaded clips private, limiting their viewing to 25 users of your choosing, you might not know about the newly introduced "Unlisted" status, which allows your videos to be viewed by only those people who know the video's direct URL. For more information, watch this free video guide from Tekzilla.

A bump key is a method crooks use to pick locks. This idea is not new, professional theives have been using it for years, and now you can make your own.

Learn how to do red eyeshadow with MAC Key Artist Chris D Par. Pursebuzz is a YouTube makeup star. Her makeup tutorials are widely watched and favorited. Pursebuzz delivers beauty tutorials on makeup application and hairstyling. Search Pursebuzz on WonderHowTo for all of of her beauty how to's, including skincare, hair, makeup and celebrity looks.

This video is for true beginners with no hip hop dance experience. People with no dance skills come to me all the time wanting to learn how to dance. In addition to classes, I teach private lessons, mostly to guys who don't want to look dumb when they go to a dance with a girl. The key is to learn how to feel the music and move to it like a hip hop dancer does.

Want to play Canned Heat's "On the Road Again" but your harmonica's in the wrong key? No problem: in this elaborate instructional video you'll learn how to tune your harmonica to the key of A by raising the pitch in draw hole 6. And remember: before attempting to adjust the tuning on your favorite harp, it might be wise to practice pitch adjustments on an old, used, broken or cheap harmonica.

Can you trust every user you come across on TikTok? The answer to that may depend on how use the service, but the real question is — can you trust every user that sees your content? Not everyone on TikTok is someone you want viewing or interacting with your content, and there's a way to prevent them from doing so.

Hi all, Pro Hackers/Crackers, Let's see how we can use batch for our own Protection instead of exploiting someone with it.

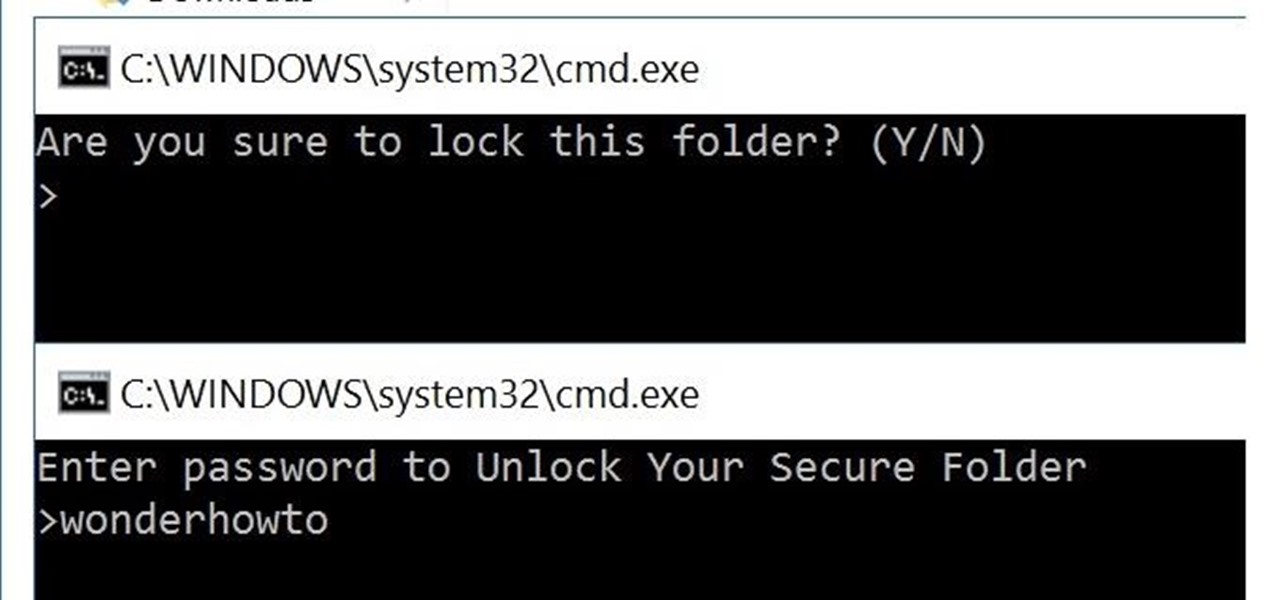
You can easily lock any folder on your Windows computer with a simple Notepad hack. By creating a batch file, you can hide a folder and require a password be entered before it becomes visible and accessible. This is a great tool for locking sensitive information, like pictures, financial statements, and a lot more.

Megaupload was one of the very first file-sharing sites I ever used. But since 2005, the beloved (and pretty gangster) Kim Dotcom, has been in a legal battle with the U.S. Justice Department over copyright infringement.

In this tutorial, Brian teaches us how to make your wireless network secure. First, go to the start menu, then go to run and type in "cmd", then type in "iconfig /all". Now a new window will pop up and you will look for the default gateway. Find the IP address to log onto the routers you have. Now, type in your IP address into your address bar on your internet browser. You will be asked to log into your account with your password and user name, which you can find at the manufacturers website....

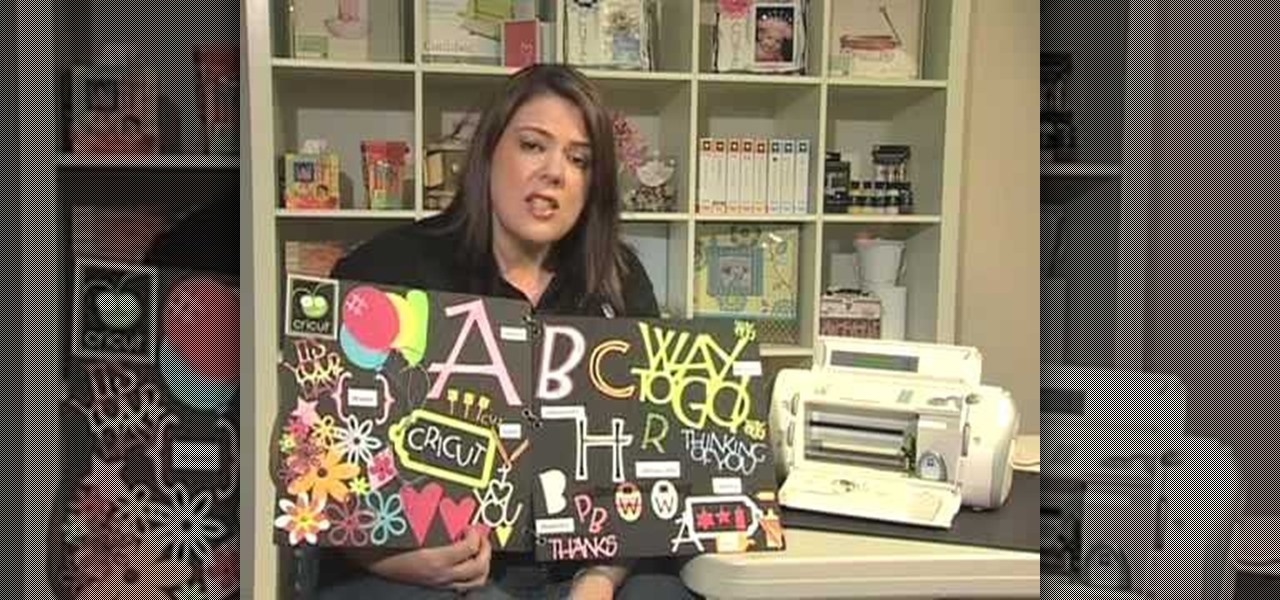
In this tutorial, we learn how to use the feature keys for your Cricut machine. There are six feature keys on every cartridge. The first is the shadow feature key that create a matte to highlight your letter. The shadow blackout key creates a solid matte that doesn't cut out the holes in between the letters. The charm feature key puts a charm top on the top of letters. The sign feature key puts letters inside of a small sign post, making it one inch from top to bottom. The slotted feature key...

If you need to add some decoration to your keys, a key fob is the way to go. Key fobs are decorative items that many people carry with their keys. There are many different ways to go when creating a key fob, but one of the best ways is to make your own using fabric from the store.

Lady Gaga is one of the most secretive women in show business, hiding behind her stage performer mask and outrageous costumes so often that we can hardly believe there's a real person underneath all that fluff.

If you're worried about having your private information taken away from you by hackers and other malicious people, this tutorial may help you. This tutorial will help show you how to easily use and understand the phishing filter in Internet Explorer 8. It only takes a couple of clicks to activate and can be the difference between making sure your private information is secure or out in the open for others to use. Good luck and enjoy!

In this video tutorial, viewers learn how to use the Sticky Keys feature in a Mac OS X computer. The Sticky Keys feature is found in the Keyboard tab in the Universal Access menu. To turn on the sticky keys, check the On option. Underneath, users are able to set some options for how the modifier keys are treated. Sticky Keys will allow users to press the keys in a sequence, instead of all at once. This video will benefit those viewers who use a Mac computer and would like to learn how to conf...