Apple's latest updates to its operating systems add another security feature to its Find My service, so you have an even better chance at locating your lost iPhone, iPad, or Mac should it ever happen. As long as you have the option enabled, you can leverage other Apple users' devices to find yours on the map.

In order to increase the security and harden the integrity of an email account and its content, you'll want to use PGP on your Windows, macOS, or Linux computer. This is usually the first thing security analysts do to protect communications with encryption, and everyone else should consider it too, especially since there's an easy way to incorporate PGP that anyone can follow.
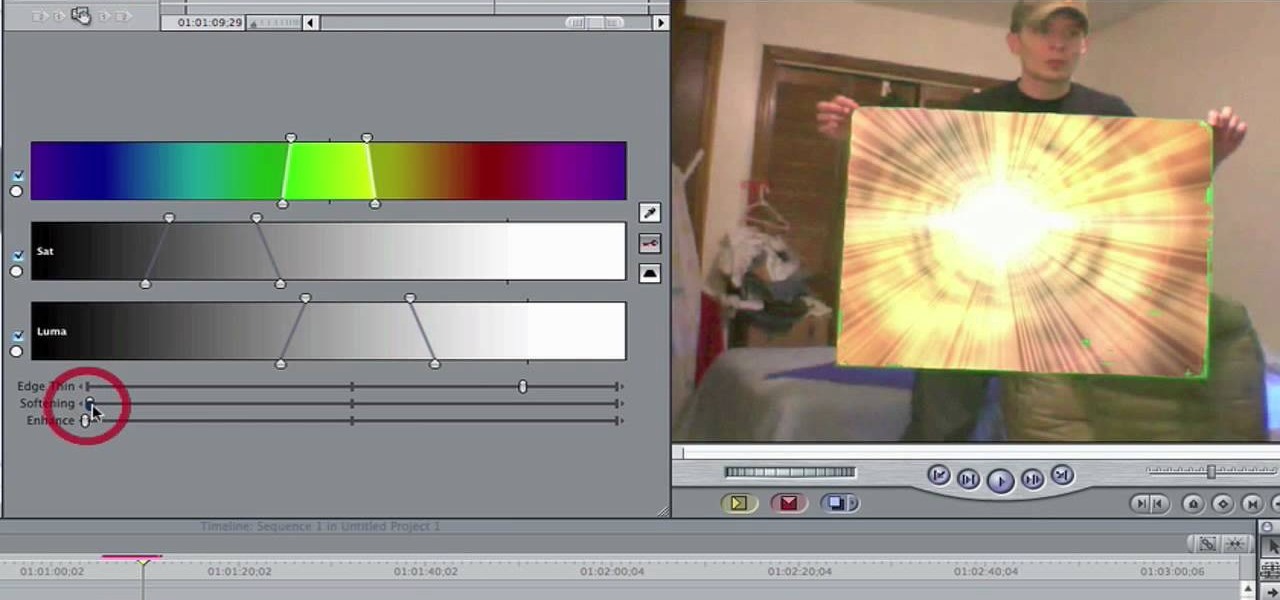
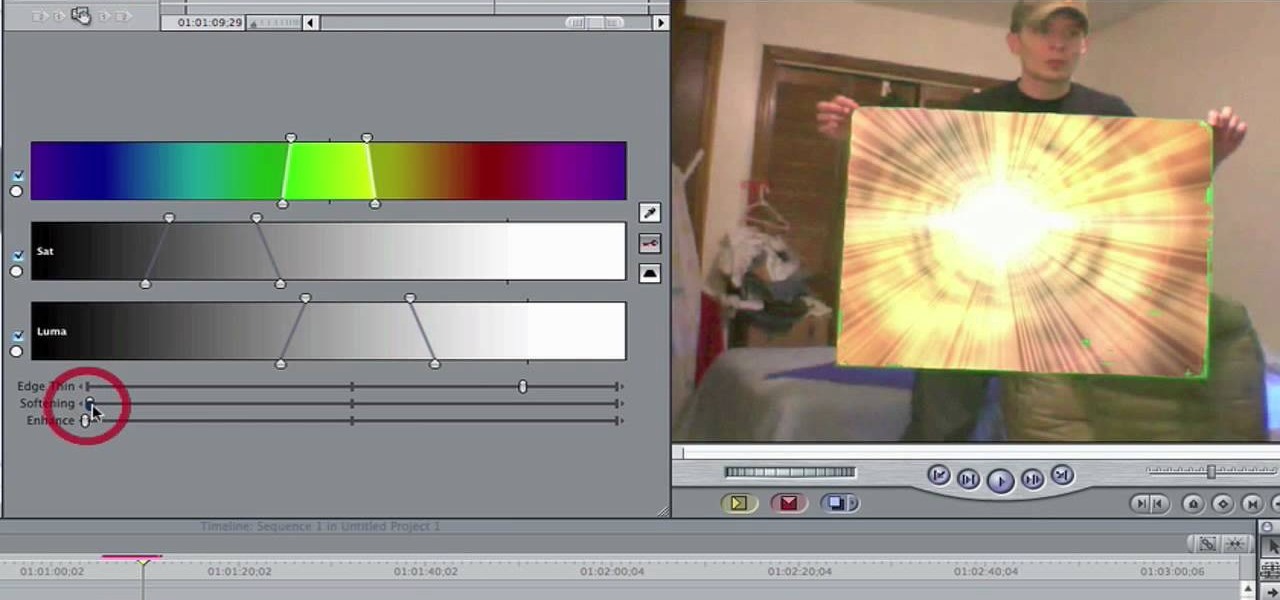
In this video, you'll learn how to key in Final Cut Pro with a do-it-yourself green screen that can be built for around a dollar. Whether you're new to Apple's Final Cut Pro non-linear video editor or just want to better acquaint yourself with the popular video editing program, you're sure to benefit from this video tutorial. For more information, including detailed, step-by-step instructions, watch this tutorial.

Hello people again, I wrote my last post about crypto about 10 months ago, now I will introduce something not fresh for the science, but fresh for the people who wants to learn. In my http://null-byte.wonderhowto.com/forum/cryptography-0161538/ post of crypto concepts, there is just basics, today we will see something that targets wide concepts like Symmetric crypto, Public Key Cryptography, Hashing, Keys etc...

Last time, we looked at archaic cryptography, so you should have a basic understanding of some of the concepts and terminology you'll need. Now, we'll discuss one of the most important advances in computer security in the 20th century—public key cryptography.
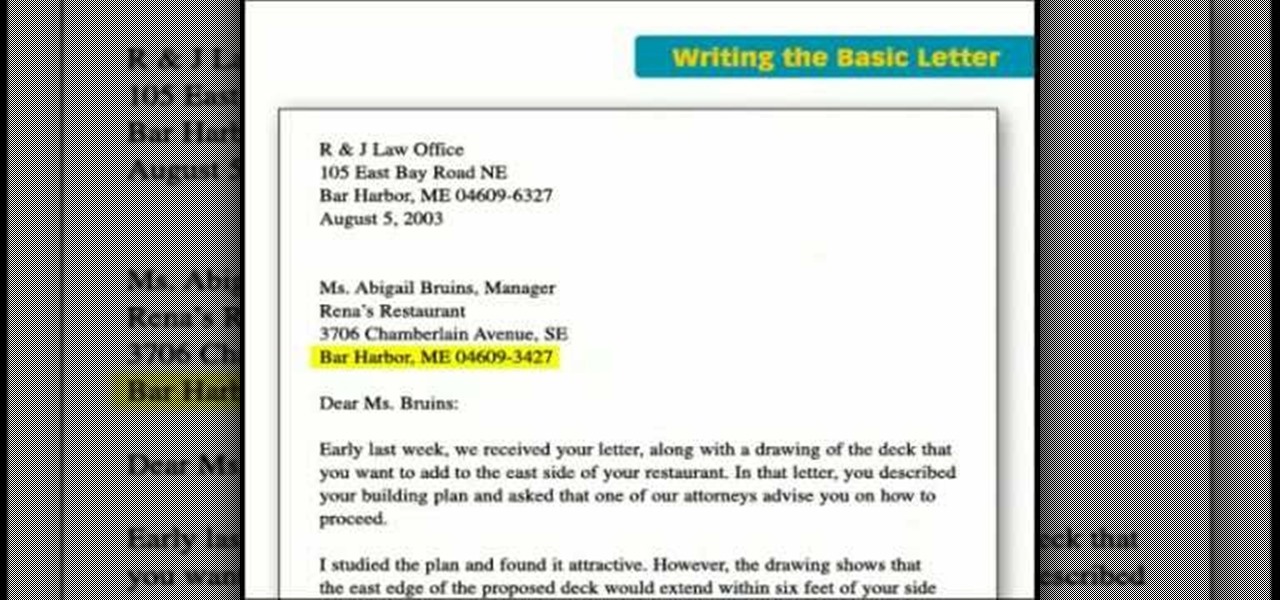
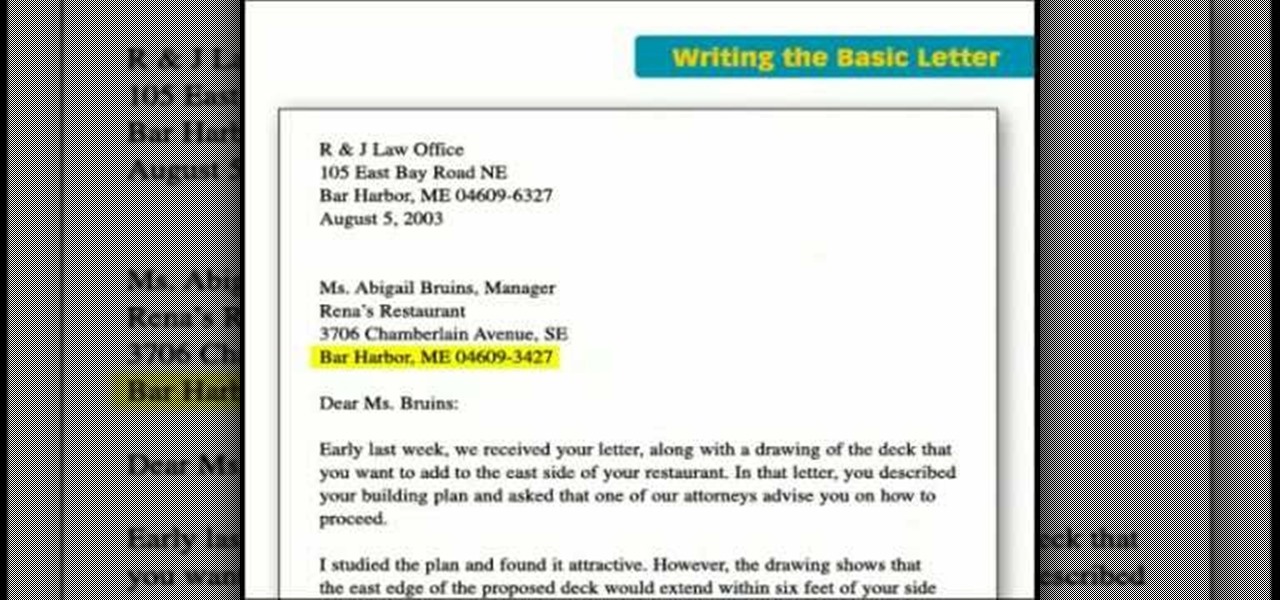
This incredible video breaks down the basic business letter into easy steps, going over some of the most key points in creating an effective business letter: make it straight, and too the point, non-confusing, and easy to read.

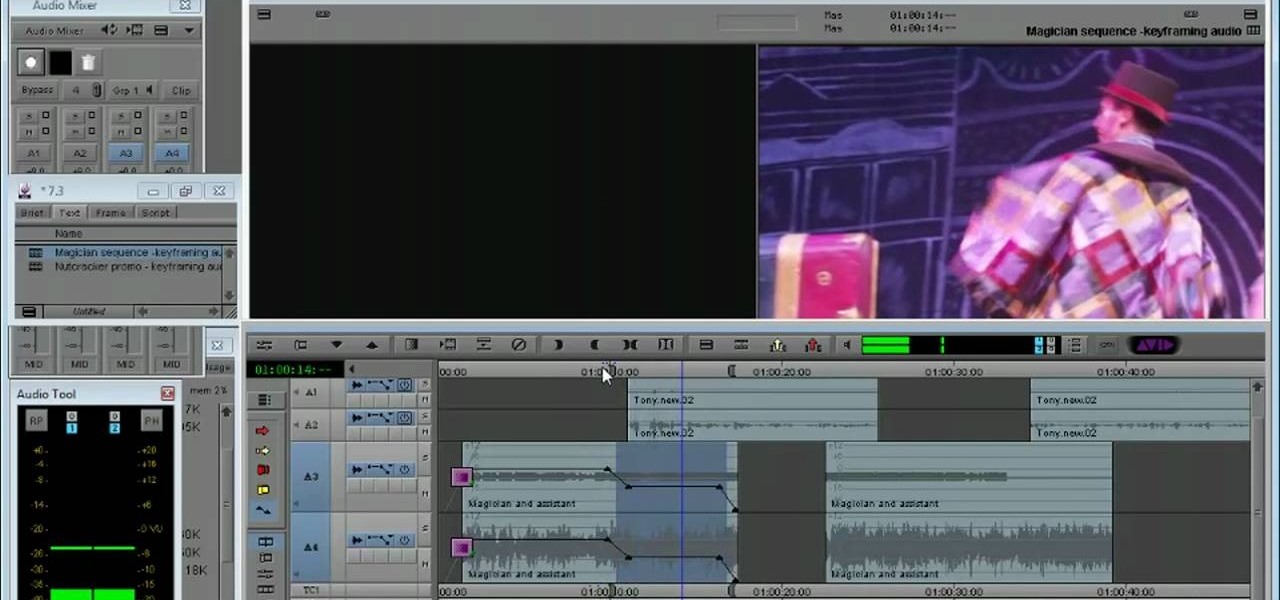
Need to know how to keyframe (or key frame) audio within Avid Media Composer 5? Never fear: this guide will show you precisely how it's done. Whether you're new to Avid's popular non-linear editor (also known as "The Avid") or are a seasoned digital video professional just looking to better acquaint yourself with Media Composer 5, you're sure to enjoy this free software tutorial. For detailed instructions, and to get started using Avid 5 yourself, take a look.

Six steps to clean a membrane keyboard. IMPORTANT - NOT FOR LAPTOPS or NON-MEMBRANE KEYBOARDS

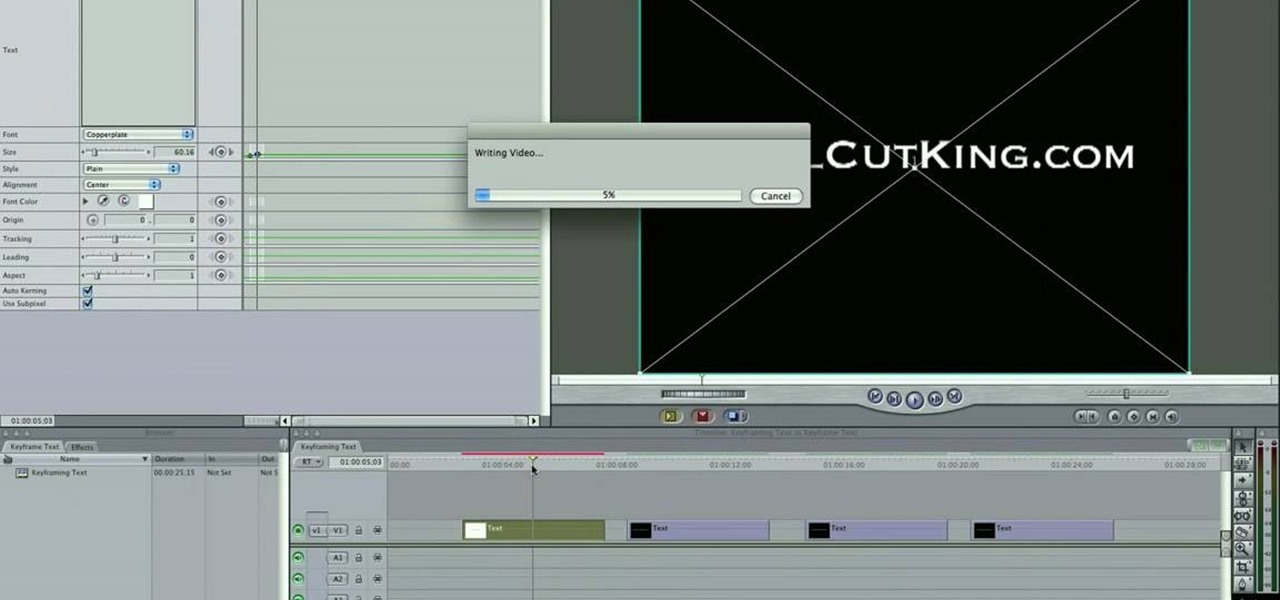
Interested in keyframing (or key framing) text in Final Cut Pro or Express? This clip will show you how it's done. Whether you're new to Apple's Final Cut Pro non-linear video editor or just want to better acquaint yourself with the popular video editing program, you're sure to benefit from this video tutorial. For more information, including detailed, step-by-step instructions, watch this tutorial.

Freelance web developer and Internet marketer David Frosdick offers some tips and tricks in this video tutorial on how to secure your Gmail account.

This tutorial will show how to use GPG and the FireGPG plug-in to encrypt and decrypt messages in Gmail. GPG is an open source implementation of OpenPGP (Pretty Good Privacy) , a public-key-encryption system. With public key encryption you don?t have to give away the secret key that decrypts data for people to be able to send you messages. All senders need is the public key which can only be used to encrypt, this way the secret key never has to be sent across unsecured channels. Encrypt Gmail...

In this video tutorial, you'll learn how to create simple keying effects in Final Cut Pro. Whether you're new to Apple's Final Cut Pro non-linear video editor or just want to better acquaint yourself with the popular video editing program, you're sure to benefit from this video tutorial. For more information, including detailed, step-by-step instructions, watch this tutorial.

Learn how to use the new Ultra Keyer tool in Adobe Premiere Pro CS5. This clip will show you how it's done. Whether you're new to Adobe's popular non-linear editor or a seasoned video professional just looking to better acquaint yourself with the program and its various features and filters, you're sure to be well served by this video tutorial. For more information, including detailed, step-by-step instructions, watch this free video guide.

Learn how to recreate the COPS face blur effect using Apple's Final Cut Pro 6 in this video editing tutorial. Whether you're new to Apple's Final Cut Pro non-linear video editor or just want to better acquaint yourself with the popular video editing program, you're sure to benefit from this video tutorial. For specifics, and to get started using this Track Matte key effect in your own FCP projects, give this guide a gander.

Speed up your Final Cut Pro workflow by using key commands when playing, creating, deleting and moving in and out points in both the viewer and the timeline. Whether you're new to Apple's Final Cut Pro non-linear video editor or just want to better acquaint yourself with the popular video editing program, you're sure to benefit from this video tutorial. For specifics, and to get started using these useful shortcuts in your own projects, watch this FCP lesson.

A Facebook page formatted specifically for non-profits can be created in a matter of minutes with this video tutorial from John Haydon. The first step you need to take is to search for any page. In this tutorial, Haydon searches for the page "Facebook Pages/Public Profiles" to use as the example. On the bottom left (of any Facebook page), you will notice that there is a link for "Create a Page for My Business." Click on that link, which allows you to begin the page creation process. Non-profi...

In this how to video, you will learn how to tell the difference between a tunable and non-tunable bodhran. A tunable bodhran has a tuning mechanism to allow you to adjust the skin tension. A non-tunable bodhran is actually tunable, but it just needs more time to do so. A tunable drum has the tuning mechanism in the inside. They are lugs pressing on an inner hoop. When the key is turned clockwise, this will make it tighter. Make sure to go crisscross rather than around the circle when tuning. ...

As you progress in the world of information security, you'll find yourself in situations where data protection is paramount. No doubt you will have files to hide and secrets to share, so I'm going to show you how to use the GNU Privacy Guard (GnuPG or GPG for short) to encrypt and decrypt as you need. GPG is a great open-source version of Pretty Good Privacy (PGP), a similar application used for encryption, but licensing and patent problems led to the development of GPG in its wake.

If your vehicle does nothing (doesn't crank over) when you turn the key in the ignition, then you might need a new starter. In this video, Scotty shows you how to check your starter and how to replace it if it's bad. Your first reaction for a non-starting car may be to jump start it, due to a dead battery, but if your battery is brand new, or if jump starting doesn't work, you'll need to get a starter tester to check out the starter. If it's bad— replace it with a new one! See how!

Do you need to email your wife your Social Security number? Send confidential business plans to your partner in Thailand? Send your hacker buddies the recovered hashes from last night's breach? Try using GPG, a valuable and easy to use open-source encryption program.

It can be hard to get all of your friends, family, coworkers, and acquaintances to jump on board with the more-secure email system ProtonMail, but that doesn't mean you can't still send them encrypted emails. Best of all, they won't even have to install any other apps or extensions to read or reply to the messages.

With the Power key located on the back of the device, LG included a convenient "double-tap to sleep" function in their G2 and G3 devices. The function allows users to simply double-tap the display to put their device to sleep instead of picking it up and pressing the Power key.

Many guides on Null Byte require using the Secure Shell (SSH) to connect to a remote server. Unfortunately for beginners, learning to use SSH can become a confusing mix of third-party programs and native OS support. For Chrome OS users, using SSH is even more difficult. We'll fix this by using the Chrome Secure Shell to establish an SSH connection from any device that can run a Chrome browser.

One of the biggest gripes I initially had with the LG G3 was the lack of options for the Shortcut keys, which are the volume keys that allow you to launch the camera or the QuickMemo+ app directly from the lock screen. I never use QuickMemo+, so having it as a shortcut was a complete waste of functionality.

Due to the overnight success of smartphones, millions of people are connecting with others. Currently, over 15 million text messages are sent every minute worldwide. Most of this communication is happening in the open where any hacker can intercept and share in the discussion unbeknownst to the participants. However, we don't need to communicate insecurely.

You may remember the recipe for a basic non-Newtonian fluid from grade school science experiments (one part water to one and one third part corn flour or cornstarch), but those trials probably stopped at squeezing the mixture in your hands. While a regular fluid's viscosity wouldn't allow you to walk on it, a little bit of technique and the magic of physics will have you walking on a non-Newtonian fluid as well as Jesus. This video science experiment shows how to use 50kg of corn flour/cornst...

This video is specifically for the C530 Slate cell phone from AT&T, though this procedure will probably work on similar models of phone. You can hack, or jailbreak, your phone to allow you to use third party apps or switch to a different service provider. You will need a non-AT&T sim card for this hack to work (T Mobile is shown in the video). Then turn it on, hit the unlock key and then enter in your unlock code. Make sure you get it right!

Broccoli doesn't have to be your kid's death sentence. In fact, with the right tweaks, you can actually get your child to ENJOY eating this cruciferous green vegetable, and we really do mean that. When it comes to veggies, flavoring is key.

I love cryptography. It is like a great gigantic puzzle for me to solve. However, it is more important than that. It is also how we keep secrets safe. Not just sorta safe either, but really safe.

Apple seeded public testers the second beta for iOS 13.3 eight days ago. That update mainly added stability patches to iOS as a whole, as did the public releases of iOS 13.2.2 and iOS 13.2.3. Now, following the release of iOS 13.3 developer beta 3 earlier today, Apple seeded the same beta to public testers.

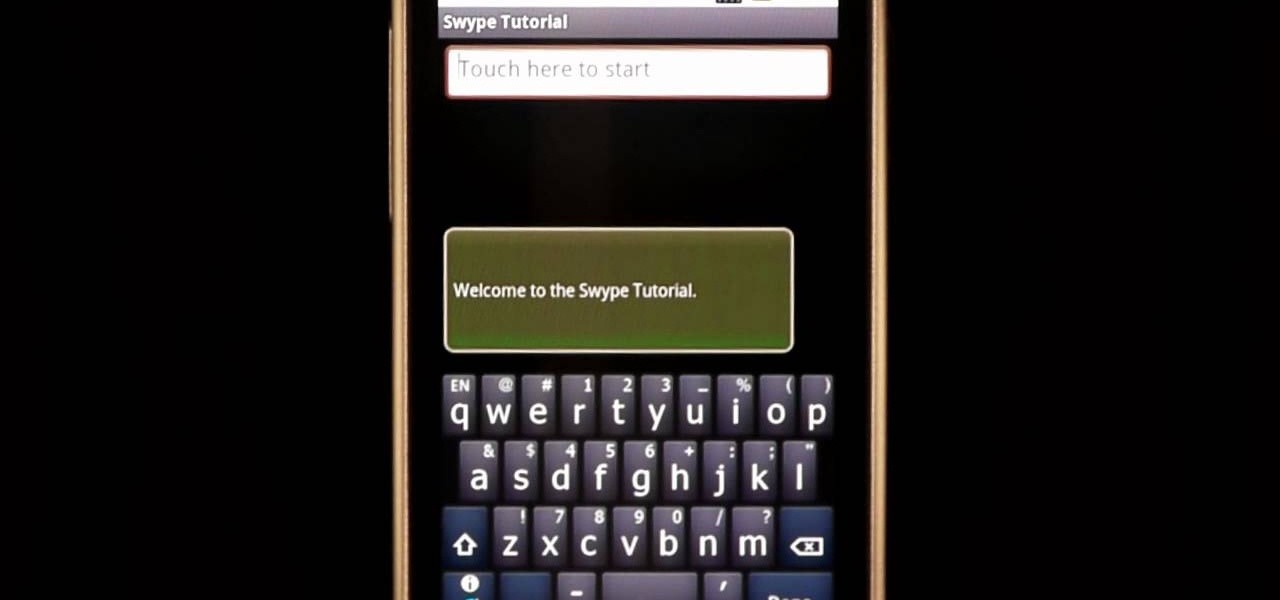
In this clip, learn how to use the Swype Key while texting with Swype on your cell phone. The Swype key is where all of your options are like dictionaries, tips and tricks, help menus and everything else you may need.

The primary purpose of hot keys in StarCraft 2: Wings of Liberty, is so that you can control the command card in the bottom-right portion of your screen, without using a computer mouse. But the hot keys have other uses, too. The first video covers the basics, and the second video covers using these shortcuts to building control groups. The third video shows you the other remaining hotkeys available for StarCraft 2.

Apple is often unpredictable when it comes to beta releases, especially with public betas. Developers receive their updates first, then public testers have to wait and see if Apple will do the same for us. Sometimes, the iPhone OEM makes us wait until the following day, but not with iOS 13.3 public beta 2. This update is now available to download and install.

Unlike other Android devices with soft keys, the LG G3 actually comes stocked with a few different styles, as well as the ability to adjust the button layout and combination. But while the customization options are great, the styles you can switch between don't add much flair or personality to your device.

Ever wanted to learn how to make a rekey a lock? Well, there's no better time than now to start learning the craft of so many locksmiths out there... key making. Just watch this video tutorial to see how to properly make a replacement key for a lock.

Taking pictures, sharing your location, and making calls are easy enough to do with an Android device, but for the most part, they all require your screen to be on with some sort of swiping and pressing actions. Dedicated shortcut keys are virtually non-existent on any modern day phone, but their utility is something that can be very useful.

Welcome back, my rookie hackers! As hackers, we are often faced with the hurdle of cryptography and encryption. In some cases, we use it to hide our actions and messages. Many applications and protocols use encryption to maintain confidentiality and integrity of data. To be able to crack passwords and encrypted protocols such as SSL and wireless, you need to at least be familiar with the concepts and terminology of cryptography and encryption.

As you may have already heard, the worst bug in OpenSSL history went public yesterday, dubbed Heartbleed. While we can go deeper into the technical details of it later, the short version is that OpenSSL, the library used to encrypt much of the web running on Linux and Apache has been vulnerable for up to two years.

Apple's just released a new beta of iOS 7.1 for developers, Beta 5, which fixes some small bugs and adds some minor feature enhancements. With previous reports stating that the final version of 7.1 was slated for a public release in March, these early leaks are indications that the final will be released in the following weeks, shortly after the Golden Master version hits developers.

In this ten-step video tutorial, you'll learn how to quickly copy keys using a camera, printer and Dremel tool. With this ten-step process you'll learn the necessary steps to copy almost any key... even if you only have access to it for a brief period of time.