In this Champion Spotlight from Riot Games, Phreak builds Singed as an AP caster with a rod of ages, sunfire cape, and other tank and caster items. If you want to know how to play Singed, the Mad Chemist as your champion in League of Legends, take a look at this guide!

Using Adobe Dreamweaver CS4 to make your website can be an intimating challenge, but will give you really good looking sites if you learn to do it well. This tutorial features instructions on how to map images in the program, as well as use the Ap Div function, which used to be called layers, but Adobe wasn't satisfied with that name for some reason. If you thought that layers were gone completely in CS4 Dreamweaver, this video will help you to find them again.

It was a good weekend for OnePlus 5T rumors — it looks likely the 5T will be first appearing in New York, and we got a spec leak that supports the rumors we've already heard. However, perhaps the best 5T news came from OnePlus' CEO himself: The OnePlus 5T may cost $600 or less.

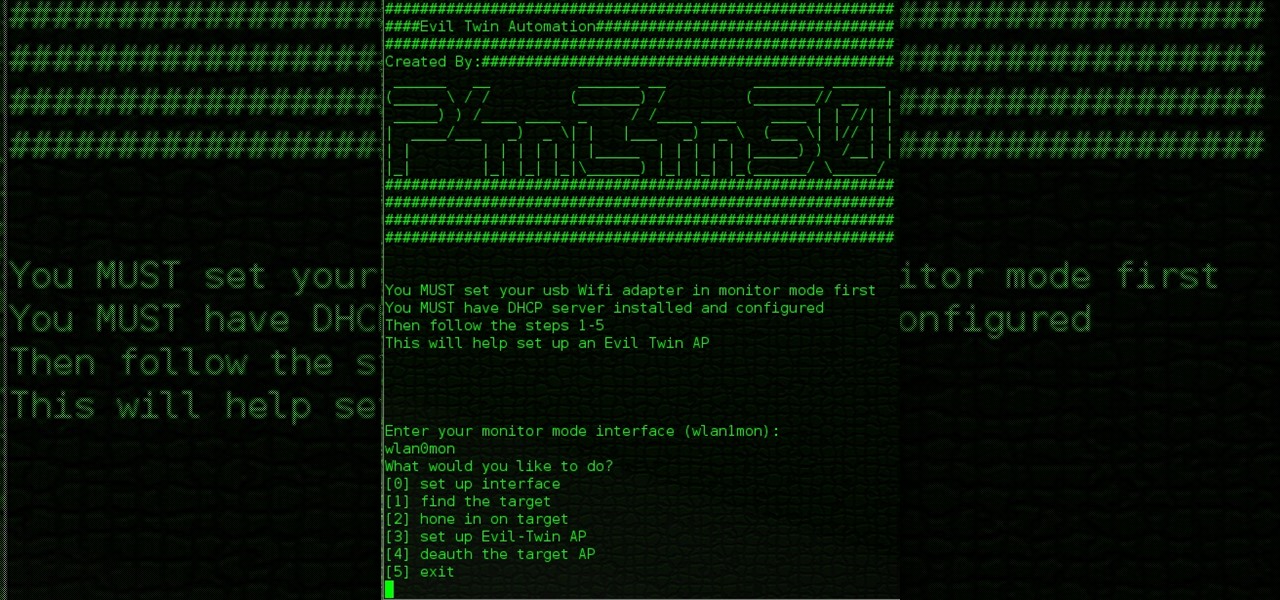
When I tried to set up an eviltwin for a MitM-constelation in kali 2.0, I couldn't provide internet to the victim. The origin was the brctl bridging. I have read many tutorials but all of them where explained in backtrack and older versions of kali. So i was searching for a solution without using brctl and this solution will be explained now. This will just work on unencrypted wireless-environments.

Welcome back, my rookie hackers! So many readers come to Null Byte to learn how to hack Wi-Fi networks (this is the most popular hacking area on Null Byte) that I thought I should write a "how-to" on selecting a good Wi-Fi hacking strategy.
Greetings null-bytians. Say you have been able to penetrate your neighbour's AP, and of course you had spoofed your MAC address. Now you go on and test to see with excitement if the password really works and the MAC is still spoofed. You login successfully and you browse the web forgetting to check what your current MAC is. Well, if you may do an ifconfig command, you will see that your permanent MAC is being used. Oh!! and guess what, ... your real MAC has been logged. Even though there is t...

Welcome back, my greenhorn hackers! Now that we're familiar with the technologies, terminology, and the aircrack-ng suite, we can finally start hacking Wi-Fi. Our first task will be to creating an evil twin access point. Many new hackers are anxious to crack Wi-Fi passwords to gain some free bandwidth (don't worry, we'll get to that), but there are so many other Wi-Fi hacks that are far more powerful and put so much more at risk than a bit of bandwidth.

Welcome back, my rookie hackers! When Wi-Fi was first developed and popularized in the late '90s, security was not a major concern. Unlike wired connections, anyone could simply connect to a Wi-Fi access point (AP) and steal bandwidth, or worse—sniff the traffic.

In this web development software tutorial Paul Wyatt shows you how to use repeat images for Dreamweaver backgrounds. You’ll learn how to use AP (absolutely positioned) Divs in Dreamweaver, and create tiled backgrounds with ease. If you don't know how to use repeat images for Dreamweaver backgrounds, this tutorial will explain it all.

For those of you that prefer a soft-baked cookie that is fluffy in the middle, using cake flour instead of regular all-purpose (AP) flour is your secret baking weapon. "But I don't have cake flour," you protest. Fear not: if your kitchen is sans cake flour, you can easily whip some up by mixing together AP flour and a little bit of cornstarch for the same results.

Welcome back, my nascent hackers! In previous tutorials for my Wi-Fi Hacking series, I have shown you how to crack WEP and WPA2 passwords, break a WPS PIN, and create Evil Twin and Rogue access points. In this continuation of the series, let's look at slightly different approach to attacking wireless.

Welcome back, my nascent hackers! Like anything in life, there are multiple ways of getting a hack done. In fact, good hackers usually have many tricks up their sleeve to hack into a system. If they didn't, they would not usually be successful. No hack works on every system and no hack works all of the time.

Welcome back, my greenhorn hackers! Continuing with my Wi-Fi hacking series, this article will focus on creating an invisible rogue access point, which is an access point that's not authorized by the information technology staff and may be a significant security vulnerability for any particular firm.

Welcome back, my neophyte hackers! As part of my series on Wi-Fi hacking, I want to next look at denial-of-service (DoS) attacks, and DoSing a wireless access point (AP). There are a variety of ways to do this, but in this tutorial we'll be sending repeated deauthentication frames to the AP with aircrack-ng's aireplay. Remember, hacking wireless networks isn't all just cracking Wi-Fi passwords! Our Problem Scenario

The threat of an evil access point has been around for a long time, and with the rise of open public Wi-Fi, that threat is often overshadowed by how comfortable we are using third-party Wi-Fi hotspots at coffee shops and public spaces. While we've shown an evil twin attack using the Aircrack-ng suite of tools, MitmAP is a Python tool to configure custom APs for many types of wireless attacks.

Hello again, ***UPDATE: Adding links to the other Two articles****

Welcome back, my greenhorn hackers. When Wi-Fi was first developed in the late 1990s, Wired Equivalent Privacy was created to give wireless communications confidentiality. WEP, as it became known, proved terribly flawed and easily cracked. You can read more about that in my beginner's guide to hacking Wi-Fi.

Do you ever thought that you can't control an Internet disconnected system? I saw a funny video in Chema Alonso's youtube channel (A well-known hacker of my country and creator of Fingerprinting Organizations with Collected Archives among other security tools), and decided to post something similar.

Hi Elite Hackers! Welcome! to my 4th post. This tutorial will explain, how to extend a (hacked) AP's range with a wireless adapter. I made this guide because after hacking an AP it was difficult to connect to it (poor connection) and further exploit it. You can also use this:

A beginner's guide - learn all about creating layers (or AP Divs in Dreamweaver CS3). Learn about applying properties to custom CSS rules and using stacked Divs to create interesting effects with images.

Hi, dear co-apprentices and wise masters. I've been recently trying to learn the basics to hacking here, and I've read all guides on Wi-Fi hacking and noticed no word is dedicated to this awesome script that comes bundled with Kali!

A man-in-the-middle attack places you between your target and the internet, pretending to be a Wi-Fi network while secretly inspecting every packet that flows through the connection. The WiFi-Pumpkin is a rogue AP framework to easily create these fake networks, all while forwarding legitimate traffic to and from the unsuspecting target.

This is a simple recipe that just uses regular AP flour. You can, of course, use a mixture of semolina flour like many pasta recipes suggest. But, this recipe is very user friendly, and if you’ve never made your own pasta before, this would be a good place to start. By the way, those pasta machines are surprisingly affordable at your local mega-store

If you consider yourself a "laser" man, then you probably know all about front-surface mirrors. But do you know how to make an FS mirror? This video from AP Digital light will show you how to make cheap first surface mirrors.

If you haven't made your own PCB (printed circuit board) yet, perhaps you we're just missing the proper instructions. But now, watch and learn from AP Digital light! They show you a fast and easy prototyping technique using a laster printer, photo paper, and a regular household iron. It's the heat toner transfer method of making PCBs.

Hello All, So to recap in part 1 I went through setting up the dchp server. Part 2 detailed the bash script. Now in part 3 I will post the entire bash script. I am doing this in its own post because Part 2 is just way to much info on one post IMO.

Attentions all science nuts: Check out this video tutorial on human cardiac action potential. If you are interested in anatomy, biology, and especially physiology, then you have to watch these educational videos.

Arduino is a language that's easy to learn and supported on many incredibly low-cost devices, two of which are the $2 Digispark and a $3 ESP8266-based board. We can program these devices in Arduino to hijack the Wi-Fi data connection of any unlocked macOS computer in seconds, and we can even have it send data from the target device to our low-cost evil access point.

If you like homemade light shows, this is one hell of a way to do it. AP Digital light shows you how you can hack a small fan into a special mirror used to create a poor man's PIC-based laser show. It's an experimental method of balancing a fan-mounted acrylic mirror for spirograph project.

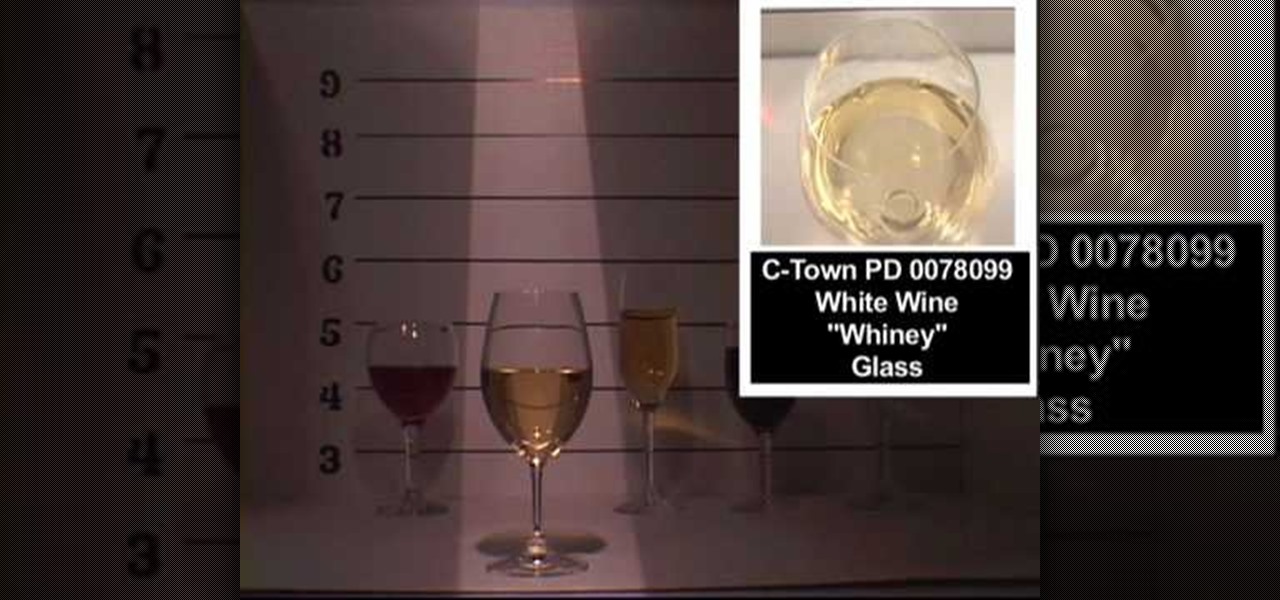
Don't know much about the dinner table? You know the basics: you eat from a plate, you use silverware to shovel it in and you drink from glassware. But what about if you're at a fancy dinner? Would you be able to distinguish a juice cup from a champagne glass? A white wine glass from a martini glass? If not, these two videos will show you which ones are which.

While Snap's third quarter financial reports disappointed Wall Street, China's Tencent took the opportunity to expand its investment in the social media company.

We've been following the rumors surrounding the OnePlus 5 for a while, and we are more than excited to get our hands on it. That excitement has only increased today, as we learn OnePlus has included a feature in its newest device that resembles the iPhone 7 Plus — real dual cameras.

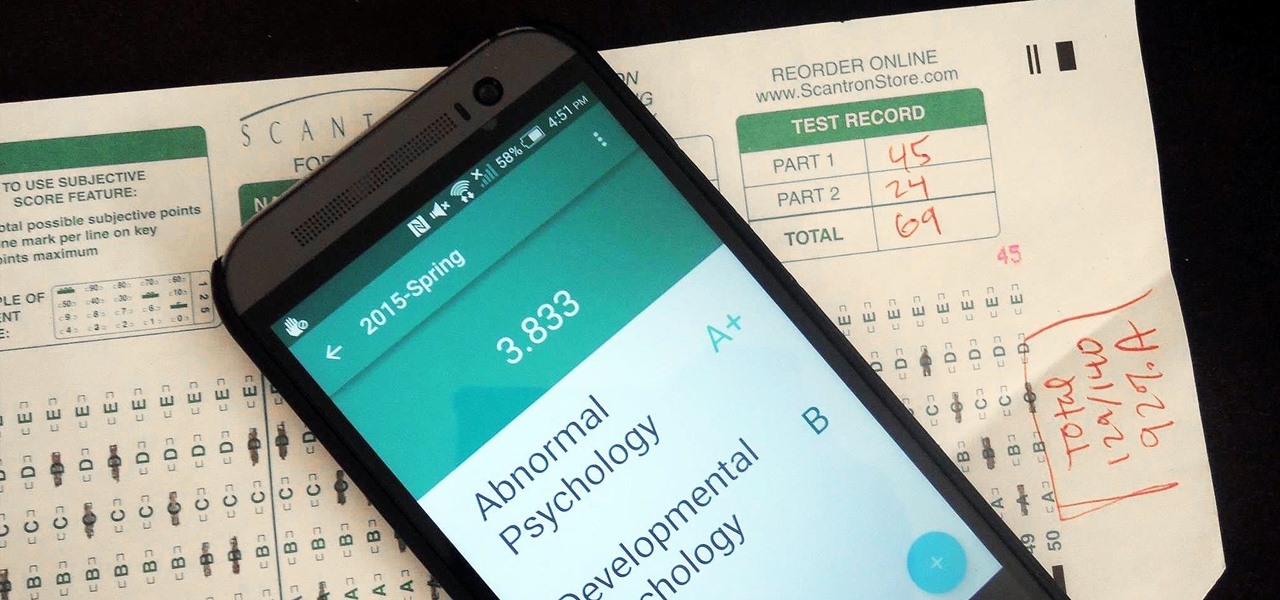
Even though my high school days are long behind me, I still find myself waking up in a cold sweat worrying about what my GPA is and what college I'm going to be able to get into. During those days I had to rely on coming up with my own equations to figure out my GPA between grading periods—including AP and honors course, as well as weights for pluses and minuses—but now there are smartphones to do all that thinking for me.

Welcome back, my tenderfoot hackers! We have looked at a number of ways that we sniff traffic on the network with such tools as Wireshark, tcpdump, dnsiff, and others, but each of these tools is only capable of pulling packets off the wire.

Unless you're a music theory buff or taking AP Music Theory in school (forced or otherwise), then the only word in "diatonic circle chord progressions" that makes sense to you is "circle." But the fancy schmancy term is just an elaborate way of saying you're playing chord progressions based on the circle of fifths.

A flaw in WPS, or WiFi Protected Setup, known about for over a year by TNS, was finally exploited with proof of concept code. Both TNS, the discoverers of the exploit and Stefan at .braindump have created their respective "reaver" and "wpscrack" programs to exploit the WPS vulnerability. From this exploit, the WPA password can be recovered almost instantly in plain-text once the attack on the access point WPS is initiated, which normally takes 2-10 hours (depending on which program you use).

With tools such as Reaver becoming less viable options for pen-testers as ISPs replace vulnerable routers, there become fewer certainties about which tools will work against a particular target. If you don't have time to crack the WPA password or it's unusually strong, it can be hard to figure out your next step. Luckily, nearly all systems have one common vulnerability you can count on — users!

Welcome back, my aspiring hackers! As I mentioned in earlier posts, the best hackers (or at least those not behind bars) have a keen understanding of digital forensics. If I am tasked to intrude upon an enemy's file server to retrieve war plans, such as in this tutorial, it is essential to my country's (and my own) well-being that it not be traced back to me. Understanding digital forensics helps us to leave without a trace and never have a trail back to us or our employer.

Welcome, my hacker novitiates! As part of my series on hacking Wi-Fi, I want to demonstrate another excellent piece of hacking software for cracking WPA2-PSK passwords. In my last post, we cracked WPA2 using aircrack-ng. In this tutorial, we'll use a piece of software developed by wireless security researcher Joshua Wright called cowpatty (often stylized as coWPAtty). This app simplifies and speeds up the dictionary/hybrid attack against WPA2 passwords, so let's get to it!