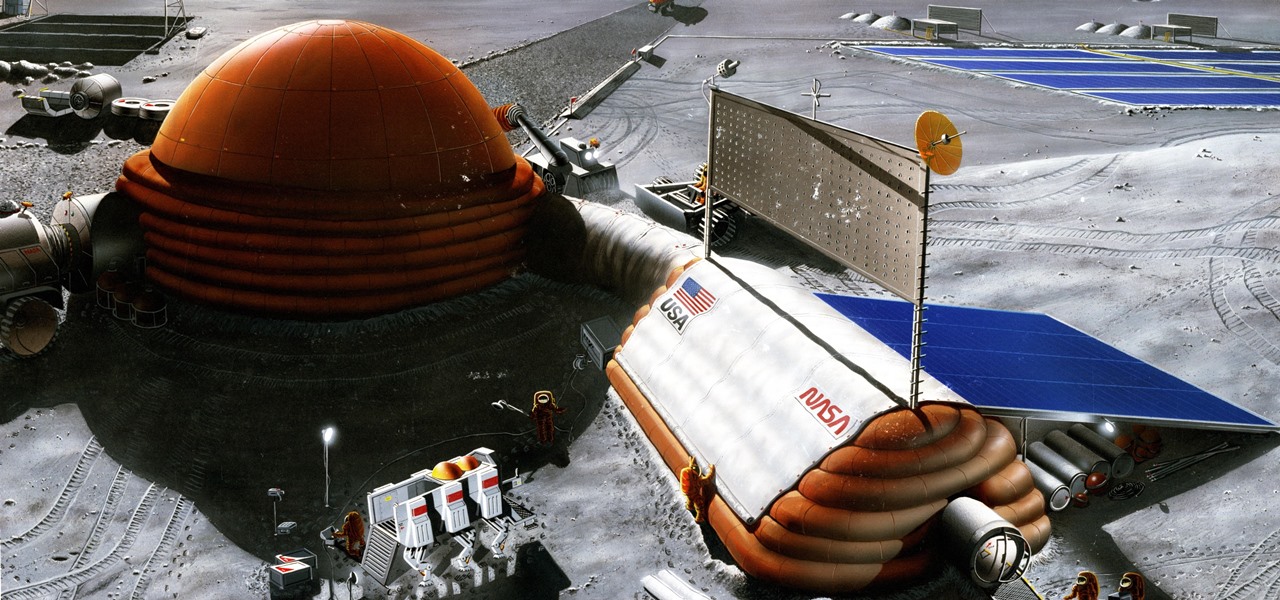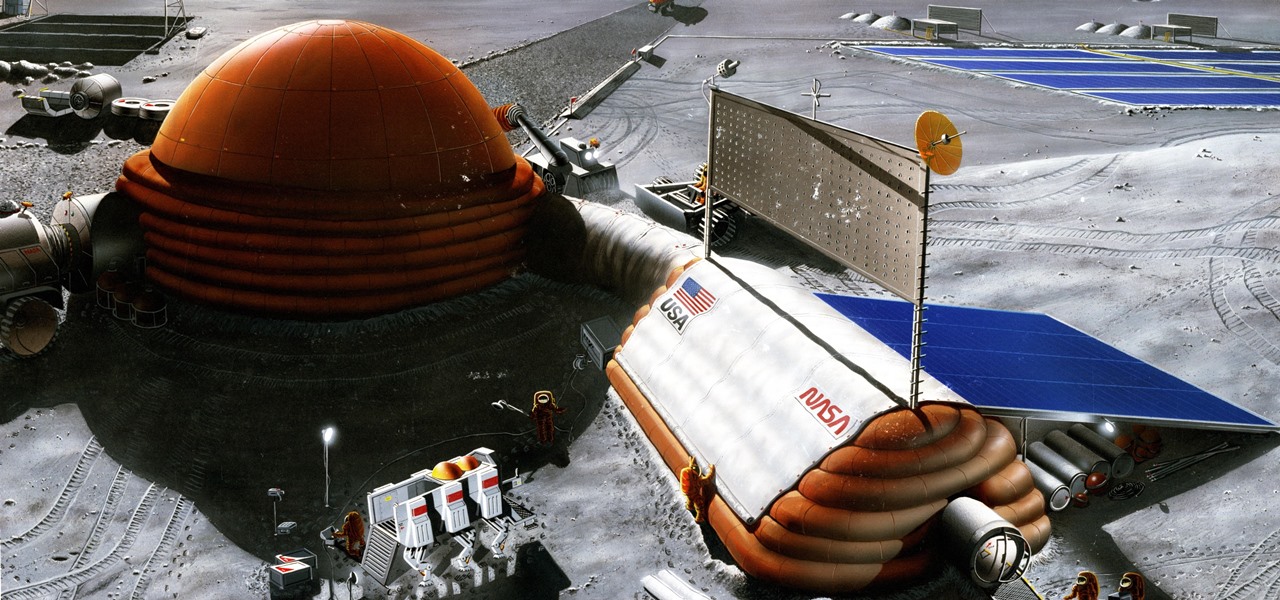
Wherever there are people, the party is sure to follow. Well, a party of microbes, at least. That is what scientists at NASA's Jet Propulsion Laboratory have found after a 30-day microbial observation of the inflatable lunar/Mars analog habitat (IMAH).

How do you fare in a phone conversation? Are you a motormouth or are you constantly dominated by the other person? Or are you both eager to get it all out? If you have an iPhone, there's an application that will reveal just who is the better chatter and which of you is more soft spoken.

Washington State has a history of large earthquakes, as does California. More than 1,000 earthquakes are registered in Washington State each year. More than 10,000 are recorded in California each year. In an earthquake, non-structural elements, which is anything that does not actually hold the building up, may become unhooked, dislodged, thrown about, and tipped over. this can cause extensive damage, interruption of operation, injury and even death.

The presenter, John White, explains how to choose and transplant cold weather vegetables and flowers in this video. The first vegetable he identifies is spinach. He suggests ensuring that the plant has been "hardened off" when buying transplants from the nursery. Next John presents leaf lettuce, broccoli, Brussels sprouts, and Swiss chard as some additional vegetables. He does remind the watcher to consult the plant labels for all the spacing information they may need. Moving on to flowers, J...

There are many instances where a zipper on a bag, purse, coat, etc. will fail to function or jam. It may be that the zipper needs replacement, but oftentimes it can be fixed using a simple technique. YouTube user MediaMason shows how many zipper problems result from a simple change in the slider's structure, as well as how to fix this. He identifies the zipper (the "teeth") and the slider (the pulley). Normally, when the slider is pulled through the zipper, it closes the zipper together. Some...
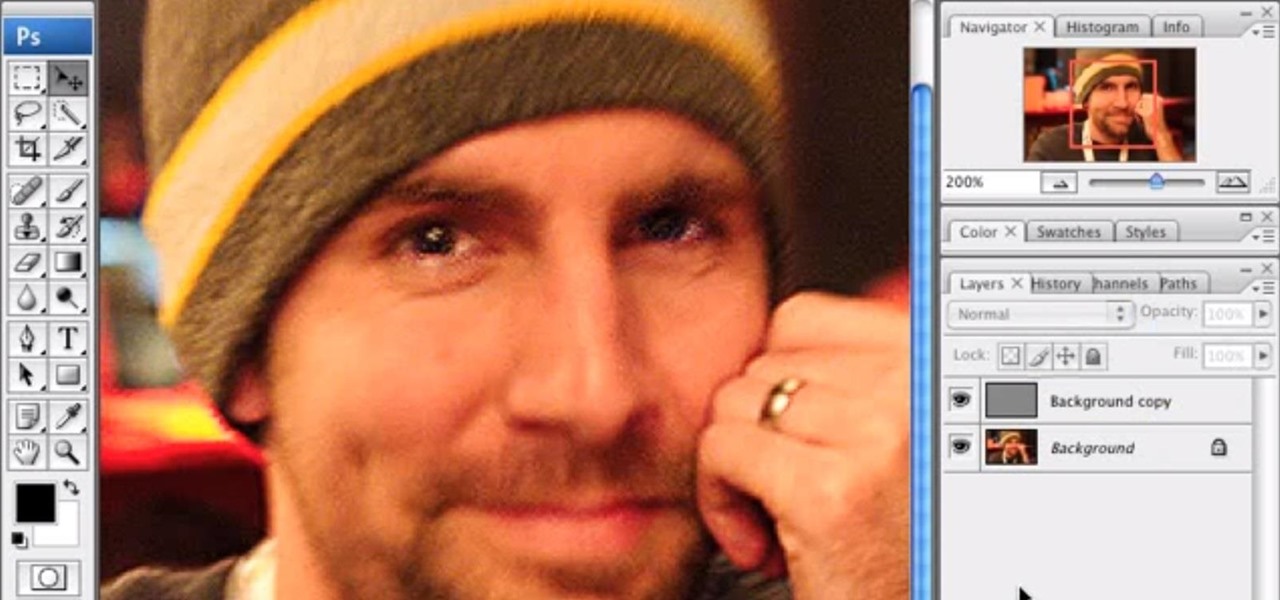
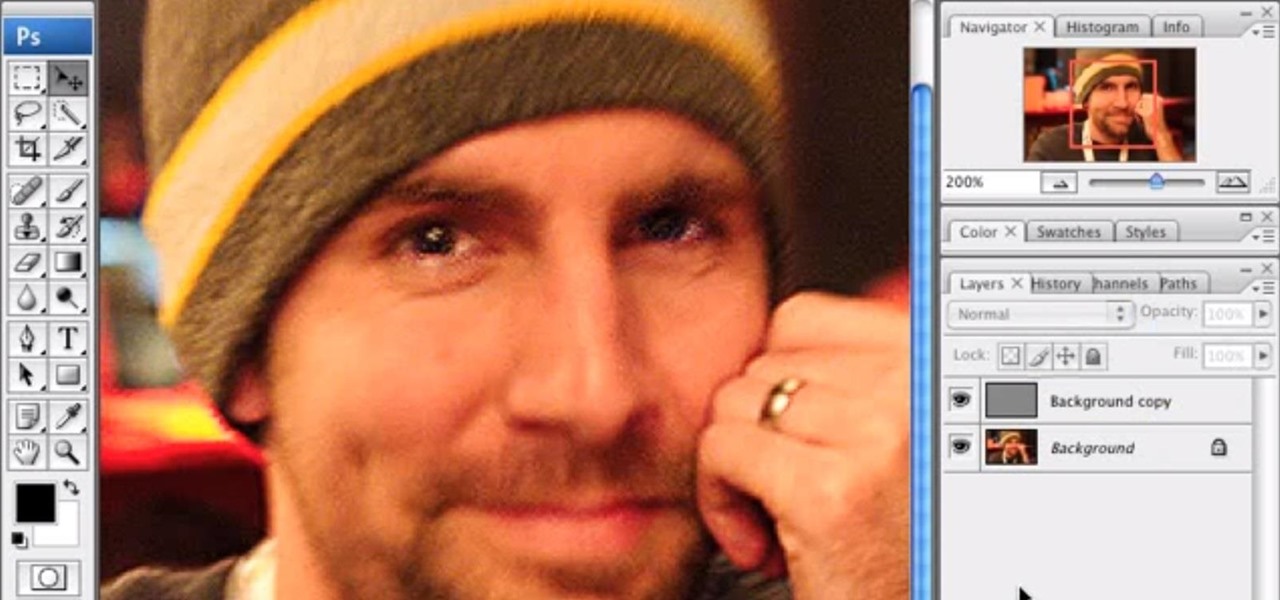
It's very easy to get a slightly blurry photograph due to a moving subject, camera shake, or just an incorrect auto-focus, but you don’t have to let that ruin an otherwise terrific picture. All it takes is a little finesse in Photoshop or another photo editing software. This guide covers sharpening a blurry image using Photoshop specifically.

Dr. Jennifer Shu identifies some of the most common bad habits and tells you how to break them. See this tutorial to learn the tricks of fixing rude behavior.

John White and Rosemary Maddox address garden problems concerning heat and sun damage on their plants. Rosemary grows tomatoes that grow healthily, but are dry and cracked at the top. John identifies the problem as an excessive exposure to heat and sunlight, and recommends putting a netting over the plants to filter and moderate the sunlight. Rosemary also has a similar problem with her roses. The leaves on her rose plants become yellow and brown and eventually die off. John calls it "heat sc...

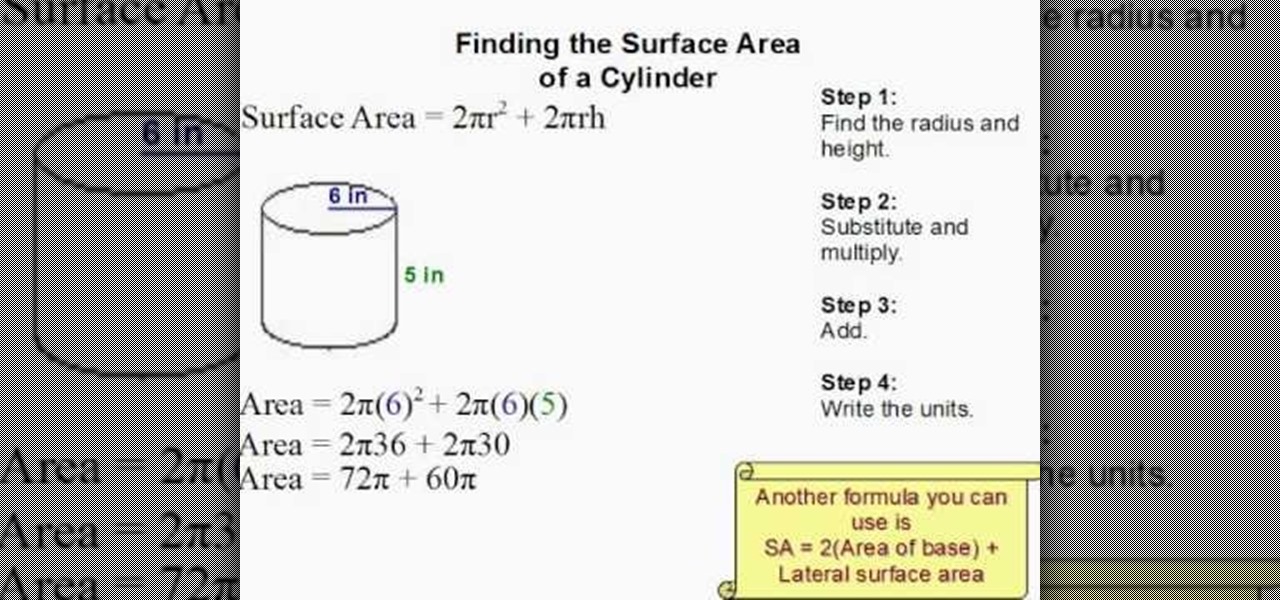
In this video tutorial the author shows how to find the surface area of a cylinder. He shows a four step approach to solve this problem. First he gives us a formula to find the surface area of a cylinder, where Surface area A = 2 * Pi * R * R + 2 * Pi * R * H, where R is the radius of the base of the cylinder and H is the height of the cylinder. Now he identifies those values and substitutes them in the formula giving the surface area of the cylinder. This video shows how to compute the surfa...

Forget about buying the store bought chicken stock, it has so much sodium. Why not make your own, it is so easy to do. CHOW contributor Daniel Duane identifies which parts of the carcass make a great stock in this cooking how-to video. Follow along and learn what parts of the chicken make great homemade stock.

Some Italian songs, like most of The Godfather soundtrack themes, are promptly recognized as Italian music by the flat second note, which identifies the Phrygian mode. Pete Sears teaches you all about this mode.

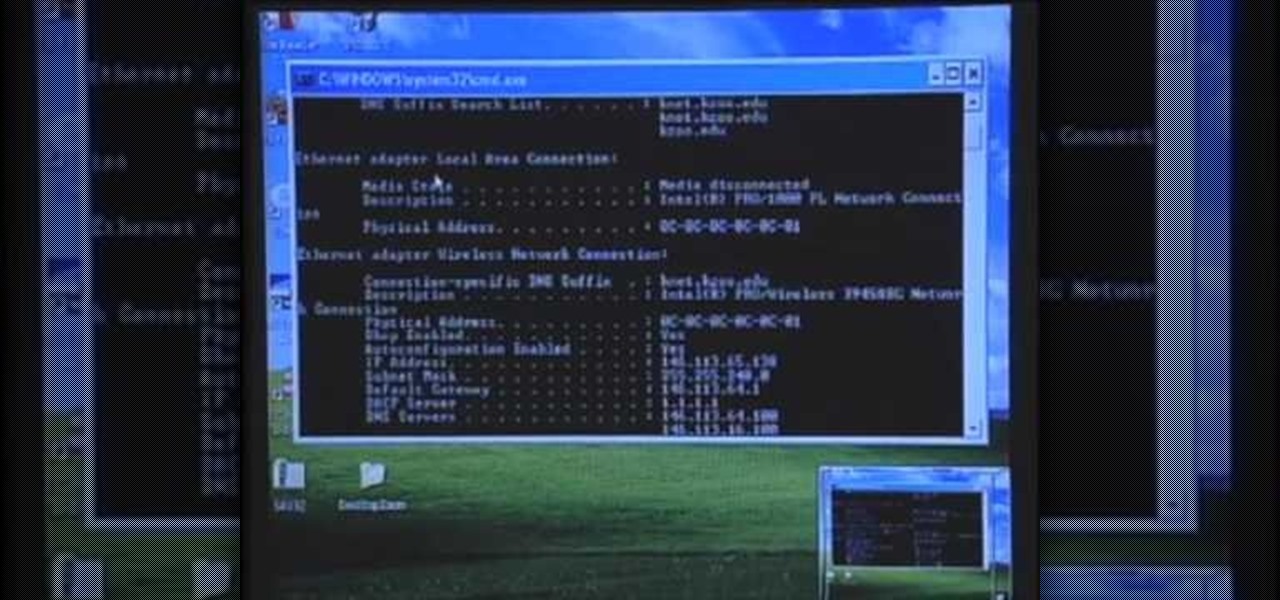
Your IP address is what identifies your personal computer while you are online. You may want to change your IP address for privacy, to bypass website settings, to download, or for various other reasons. This tutorial will take you through the steps you need to start surfing more anonymously.

In this tutorial, we learn how to quickly find your MAC address. This is the address that identifies your computer on a network. When you go to a campus, you will need to register your computer with a resnet so you can access the internet. To find the address, you will head to the Apple menu, then click 'about this MAC'. Click on the 'more' button and then click on 'network' and 'built in Ethernet'. This is the MAC address that you will need to register your computer, you may have a few of th...

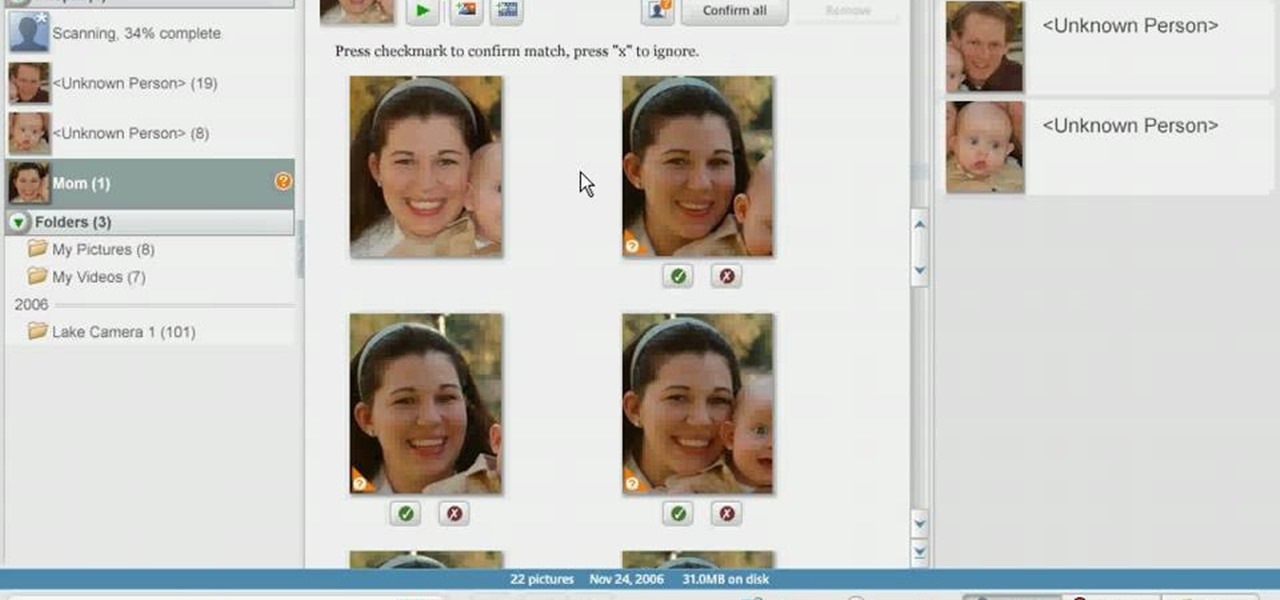
In order to use Picasa's face recognition feature double click on an image that you would like to edit. It will automatically identify each person. Then label the first person that it identifies. Then hit the enter key, and click on the new person button then click on the okay button. Now go back to your library and on the left hand side of your library you should see the label that you made for your first photo. Click on that label and Picasa will automatically find all of the photos that th...

Some times malicious programs can infect your registry and fill it with lots of unwanted information. You may need to clean it to prevent the virus from causing any further damage to your computer or to even disable the virus. It is a very lengthy and complex process to do this manually. So you will need to use one of the powerful free tools available online. Hijack This is one of the most powerful program that can be used for this purpose. So go the website and download this free tool. Insta...

Learn to play the harmonica and jam with your friends. Step 1: Hold the harmonica properly

Welcome back, my fledgling hackers! A short while ago, I did a tutorial on conducting passive OS fingerprinting with p0f. As you remember, p0f is different from other operating system fingerprinting tools as it does not send any packets to the target, instead it simply takes packets off the wire and examines them to determine the operating system that sent them.

If you read my article on the OSI model, you got a good overview on communications from that model's perspective, but how does that relate to TCP/IP? We're going to take it a step further, getting into the idea behind the two address concept. How does an IP address and a MAC address work together? If you want to hijack sessions and all sorts of lulz like that, you need to understand these concepts. Let's get into it, mates!

Have you ever had a burning sensation when you urinate? Low fever, back pain, and maybe cloudy urine? Male or female, it could have been a urinary tract infection. If it lasted long enough, the chances are good you went to the doctor for help. For about 20% of women, standard testing for a UTI does not reveal the presence of infection-causing bacteria, even though bacteria may be causing their symptoms. Well, a new test may provide better answers.

Colorado State University scientists have developed new tech that quickly identifies the presence of Zika virus in mosquito populations — and in human body fluid.

As Android's de facto virtual assistant, Google Now lets us speak directly to our phones in plain English to answer our questions and perform many basic tasks. With the app open, just say "Okay Google," then wait for the beep, and ask almost any question.

There's an iOS feature that benefits many users, but it's absolutely vital if you wear AirPods or other headphones models connected to your iPhone. A large number of iPhone users don't even know about it, especially since it's disabled by default and hidden deep in the system settings.

In recent years, unwanted calls have become a top priority for the FCC. In 2016, analysts estimated that US customers received over 2.4 billion robocalls per month. As a result, the FCC has provided carriers new tools to combat this problem.

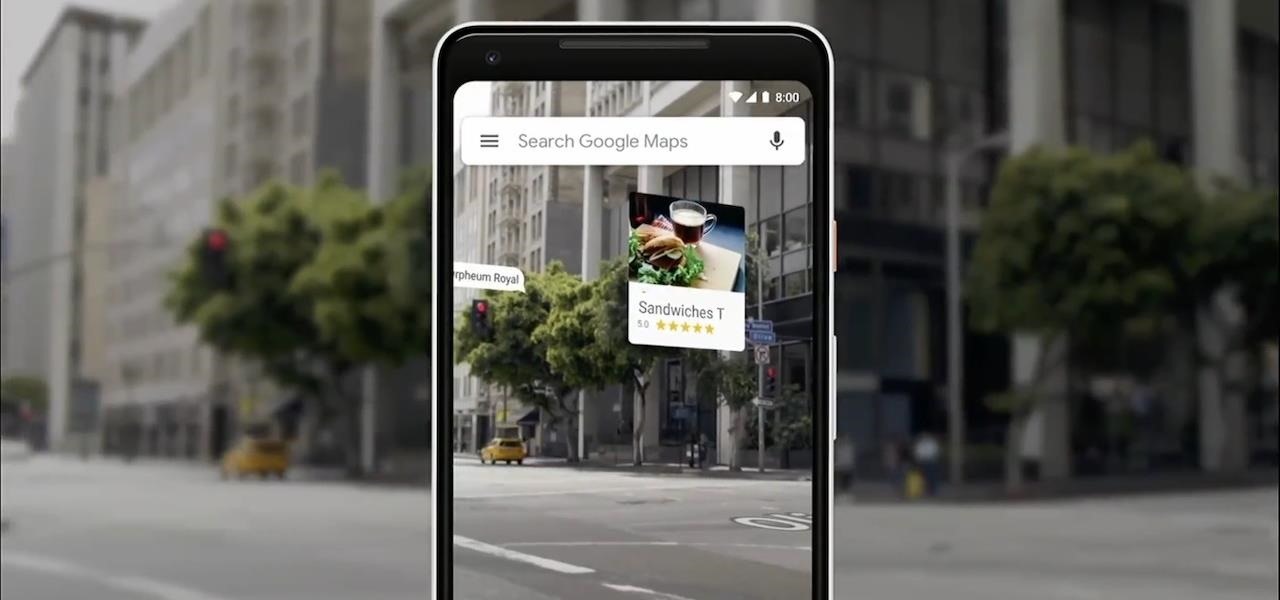
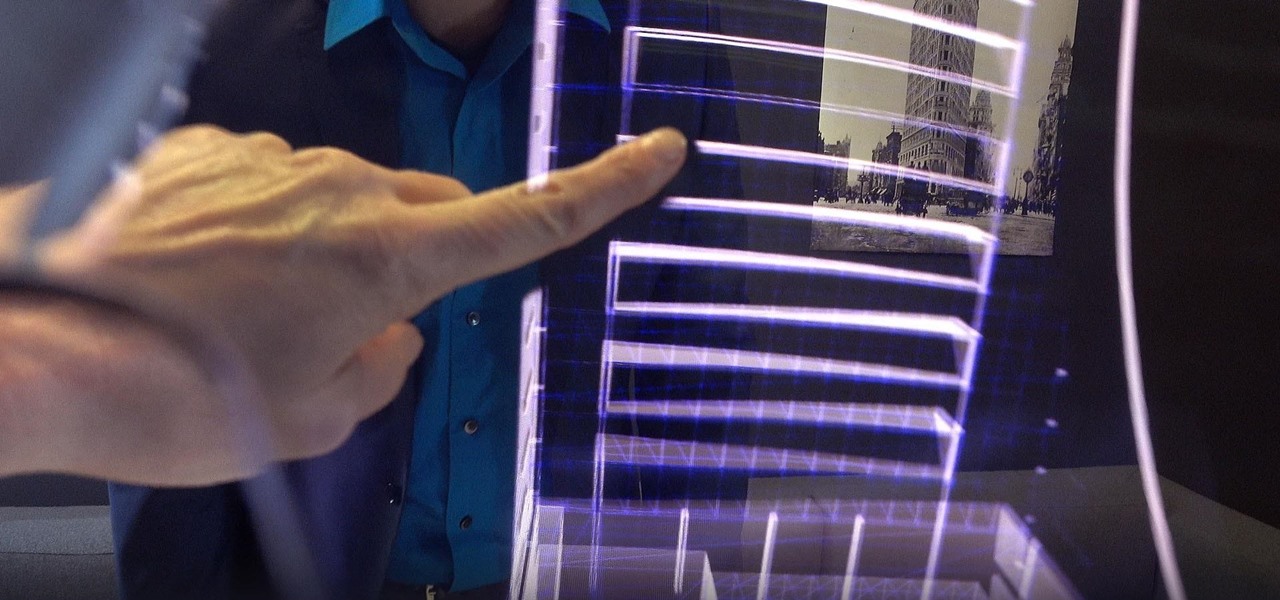
The augmented reality walking navigation mode for Google Maps appears to be closer to an upcoming release for the general public.

A market research report, posted on February 27, 2017, forecasts that the image recognition market will grow to nearly $40 billion worldwide by 2021. The market, which includes augmented reality applications, hardware, and technology, generated an estimated $15.95 billion in 2016. The report estimates the market to grow by a compound annual growth rate of 19.5% over the next five years.

If you've used Twitter on your smartphone sometime in the past two weeks, you've probably noticed that tweets from users you don't follow have been popping up on your timeline.

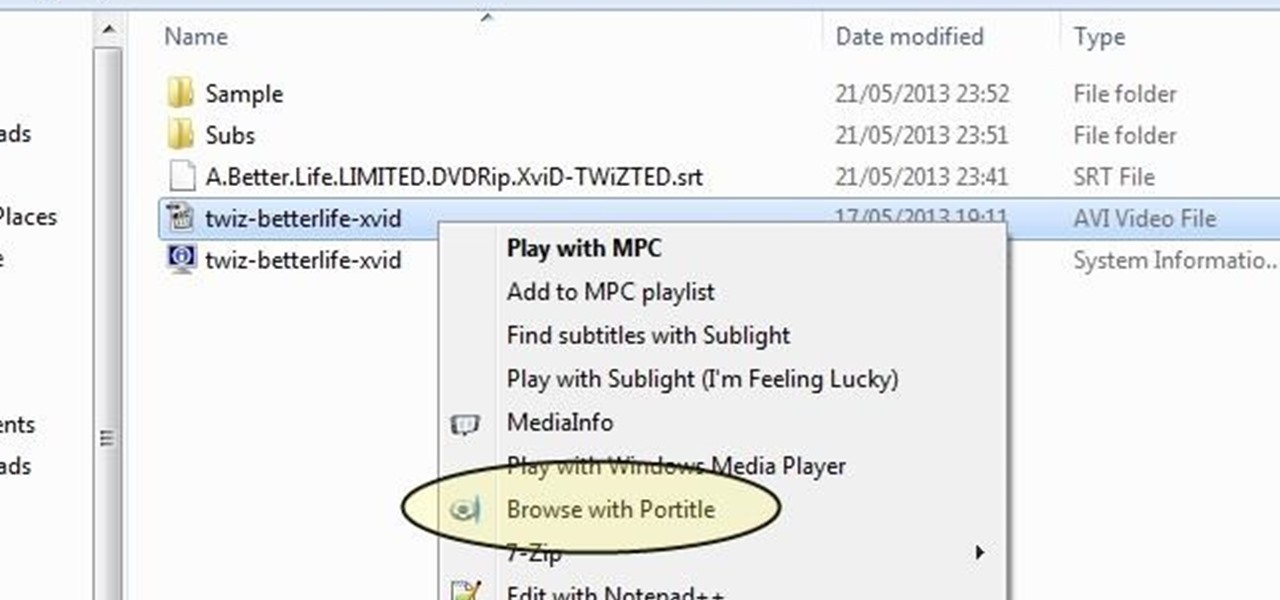
Understand the Problem of Couch Potatoes I have a lot of movies stored on my PC and when I have to finally have the time to watch something, I do not always remember which movie is which. So now I have to google for each movie with the keyboard or search in IMDB.

As deeply as smartphones are integrated into our daily lives, it's no surprise that people are finding ways to use them to stay healthy. From detecting cancer and radiation to diagnosing STDs, phones have come a long way, baby.

The macOS 10.14 security update tried to make parts of the operating system difficult for hackers to access. Let's take a closer look at how its new feature works and what we can do to spoof the origin of an application attempting to access protected data.

For Snapchat users wondering if that selfie is ready to send to their crush, independent Lens Studio creator Andrew Mendez created a handy tool called the Smile Rater.

Royal Dutch Airlines (KLM) is making it easier for its passengers to travel by employing an incredibly practical new augmented reality feature included an update to its iOS app.

For some, going to the dentist can be a terrifying experience, but a new use of augmented reality could go a long way toward making the trip feel more like it's worth the orthodontic angst.

If you've ever wanted to be a graffiti artist, but you also frown upon vandalism, then augmented reality is for you.

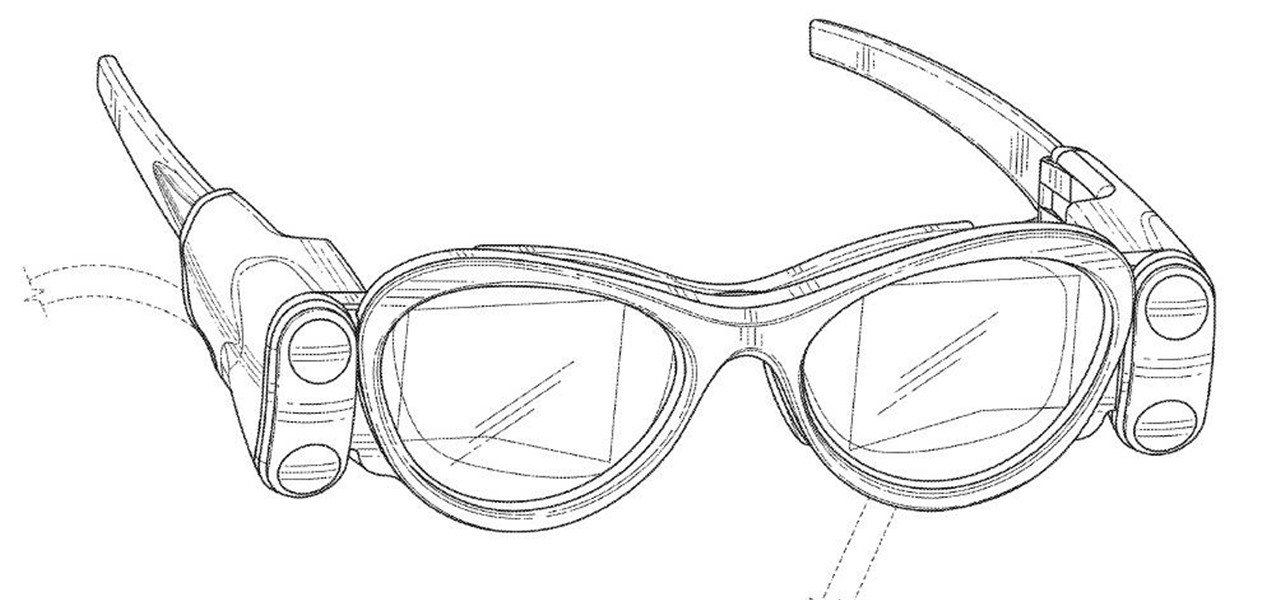
In June at the eMerge Americas investors conference, Magic Leap founder (and NR50 member) Rony Abovitz proclaimed that the launch of their flagship product was "not far away."

While two augmented reality companies were recently recognized for their innovative technologies, other companies have turned to augmented reality to innovate in their respective fields. Over the past week, use cases have ranged from selling snacks and video games to raising awareness for public health issues.

The HoloLens opens up new, digital locales within our physical world, so it was only natural for the HoloLens Challenge to ask developers to create a portal into one. One developer rose to the task and gave life to wall art, turning it into an interactive game called Future Boy.

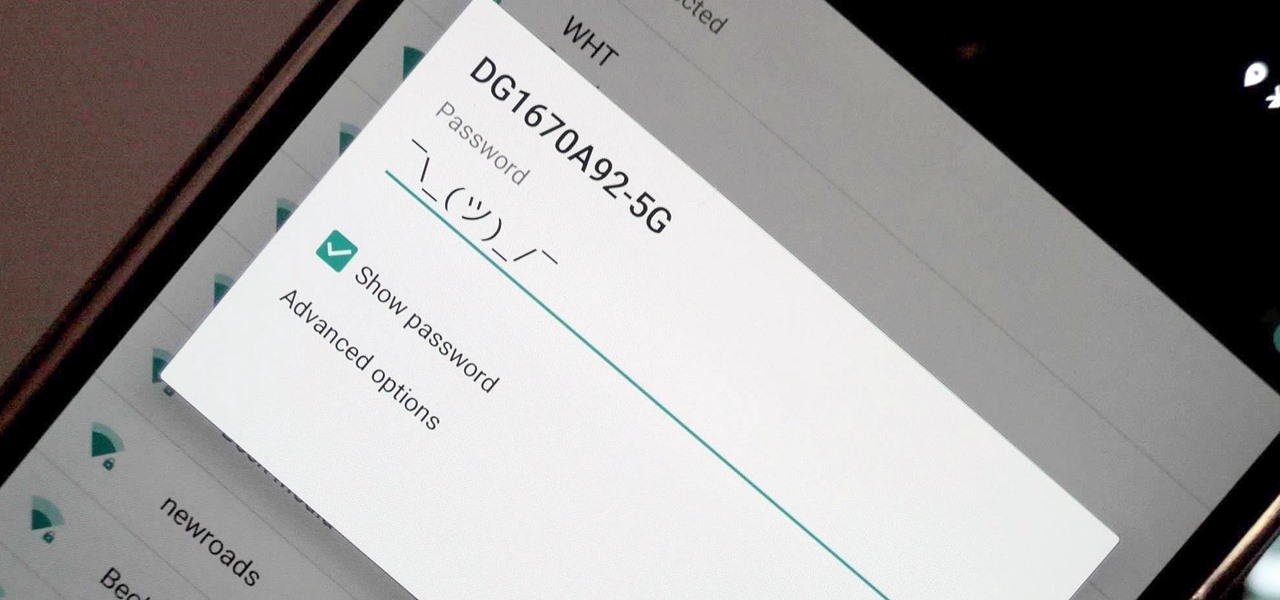
Researchers at MIT's Computer Science and Artificial Intelligence Laboratory have created Wi-Fi technology that identifies where you are, which may eliminate the need for passwords.

Step 1: What Exploit Development Is and Why Should I Be Interested on About This Topic

Change is something everyone needs every now and then. President Obama used it as his campaign slogan and adult movie stars use it to hide their real identifies. Change is in itself versatile. You never want to have the same thing day in and day out, and that's why us Android users appreciate the massive amount of customization available.

It used to be that you only had to worry about maids rummaging through your belongings in your locked hotel room. But now anyone with 50 bucks of hardware and some programming skills can hack their way in—as long as it's locked by keycard.