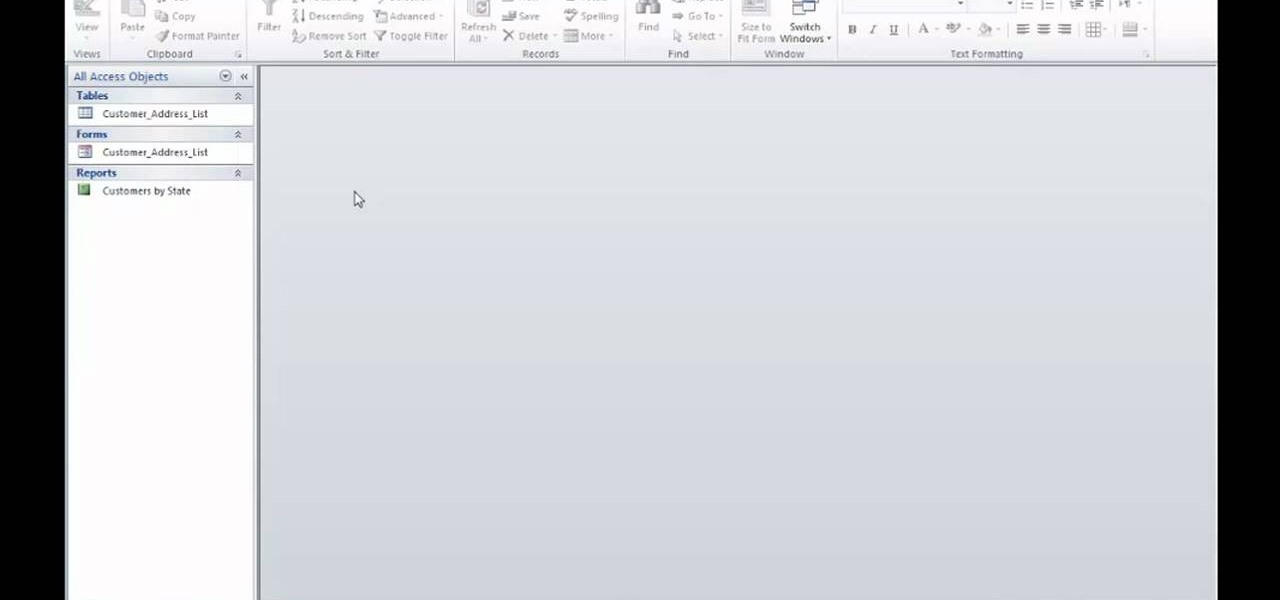
Check out this tutorial and learn how to get up to speed with the latest installment of Mircosoft Access 2007. Microsoft Office Access 2007 brings you a new look and new features designed to help you get your work done more easily than ever. You'll see differences right away, starting with the Getting Started with Microsoft Office Access page where you can open a blank or existing database, download a pre-built database template, and check out the offerings on Microsoft Office Online.
Databases allow you to store data in a systematic and organized format, making it easy for you to search, sort and edit.
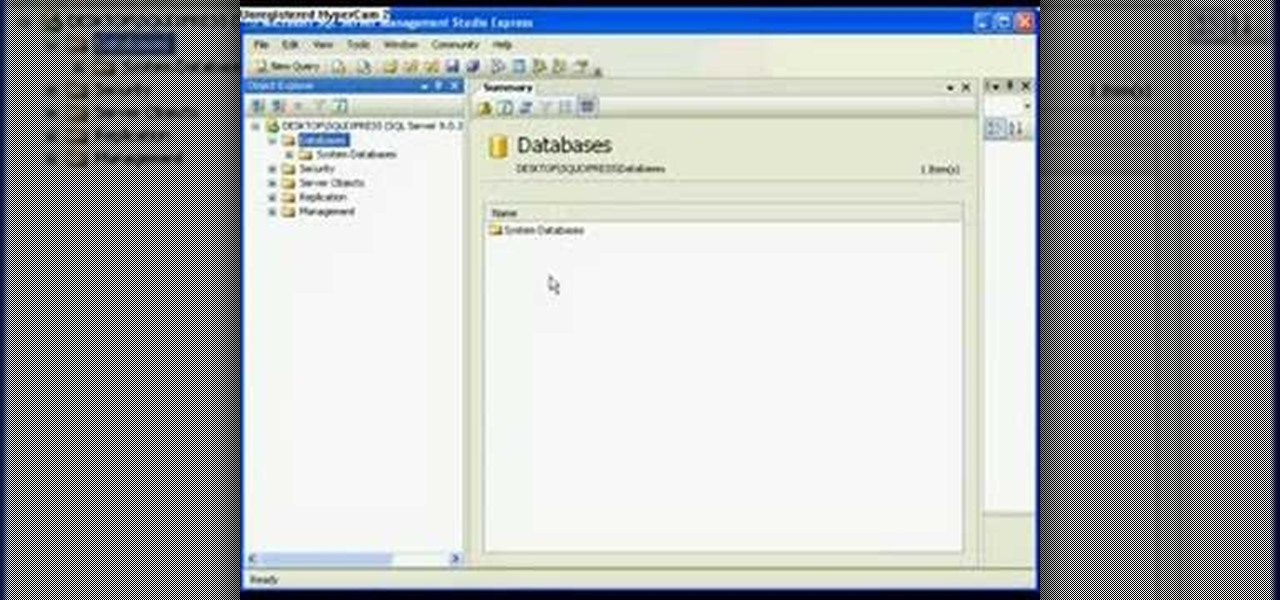
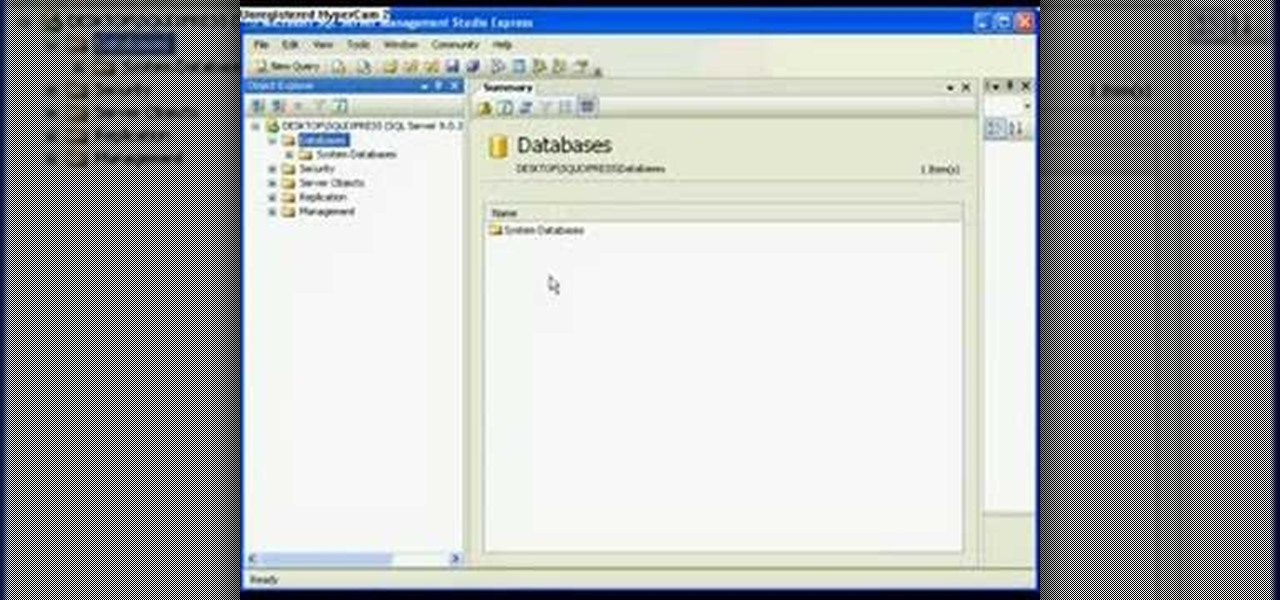
In this video tutorial, viewers learn how to detach and attach a database in SQL Server 2005. Microsoft SQL Server is a relational model database server. Begin by opening the Database and show all the tables. To detach the table, right-click the database and select Detach. Make sure that the database is not opened or it will not detach. To attach a database, right-click on Database and select Attach. Click on Add and find the table. Select the table and press OK. This video will benefit those...
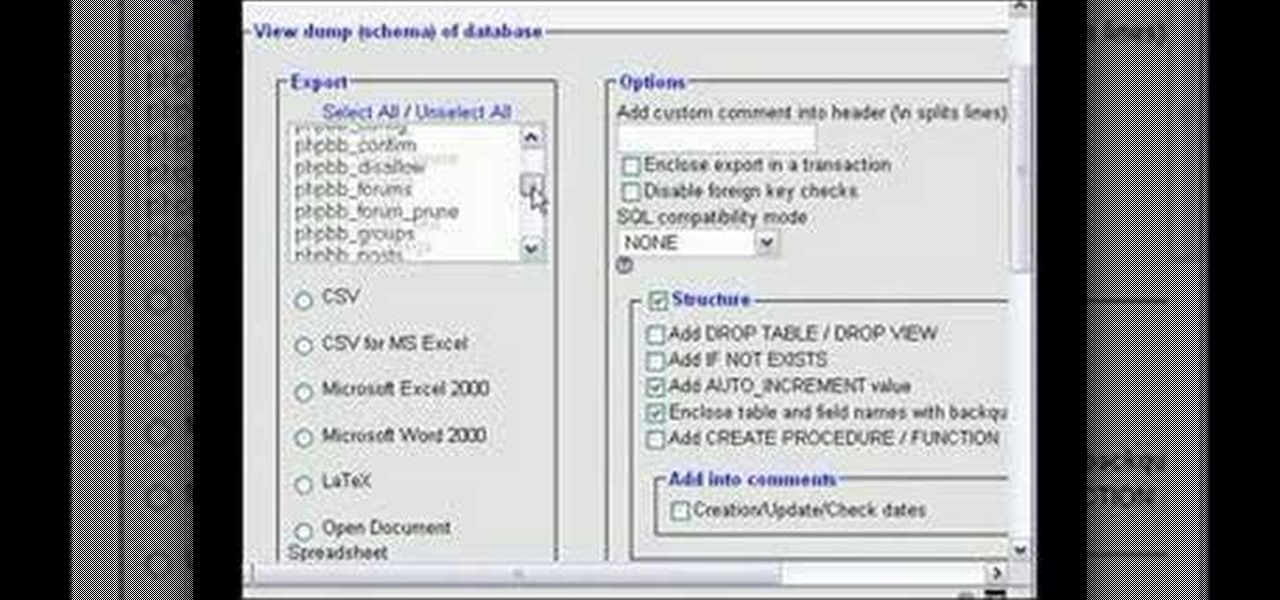
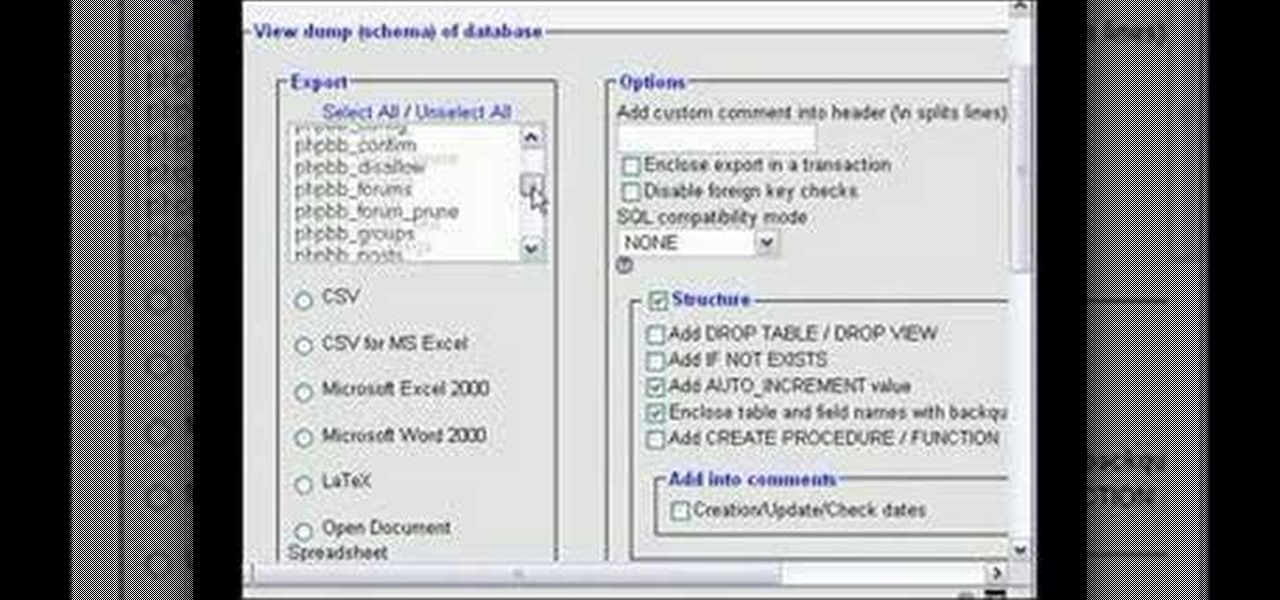
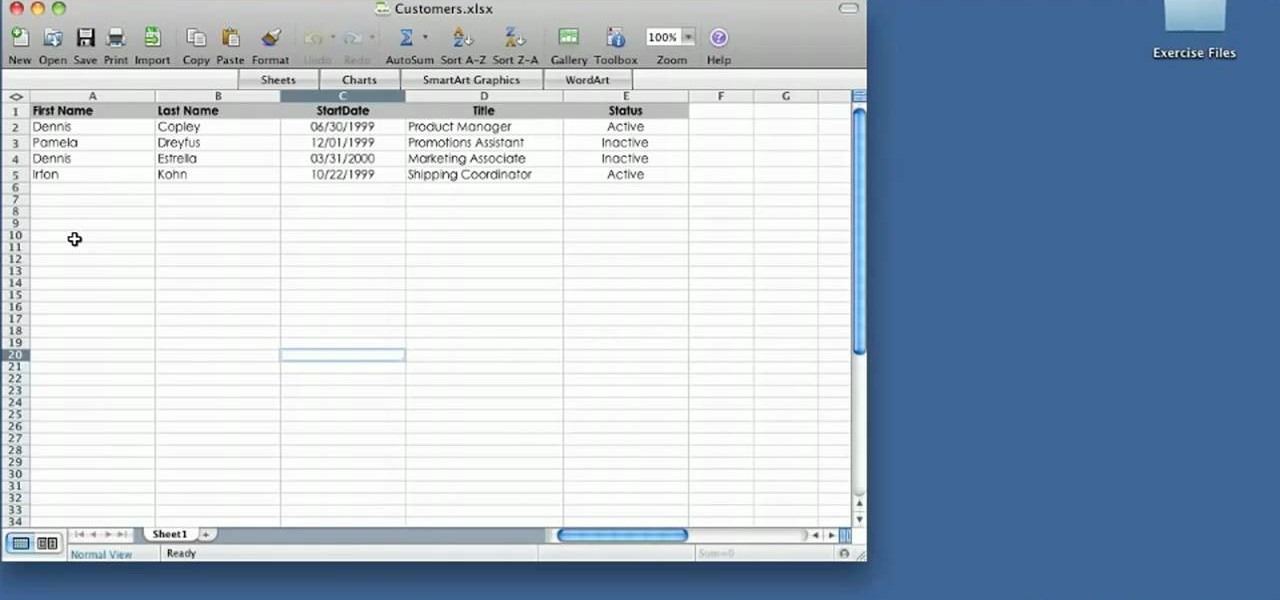
In this short video we export a MySQL database table to a Microsoft Excel 2000 spreadsheet using cPanel and phpMyAdmin. You will need to have your login information for cPanel. Once you are in cPanel, go to phpMyAdmin in the database section and find the database you need to export, and export the database as a spreadsheet! See how to customize the exportation of a MySQL database to an Excel spreadsheet in this tutorial.
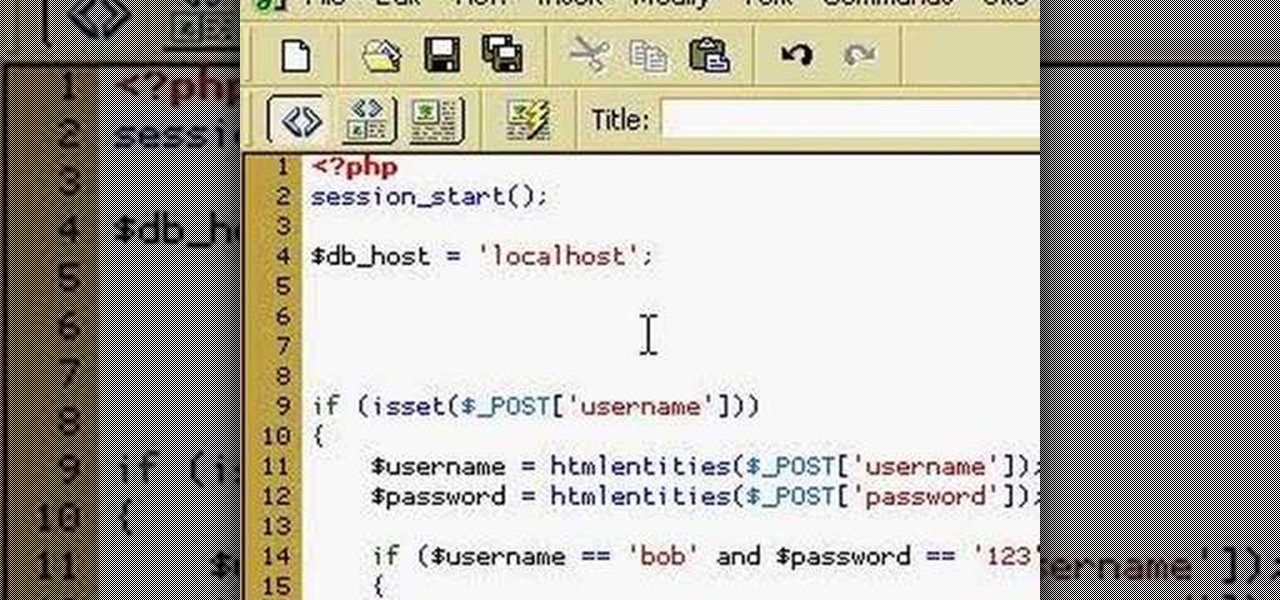
How to use PHP to login to a MySQL database. Part 1 of 4 - How to Use PHP to login to a MYSQL database.
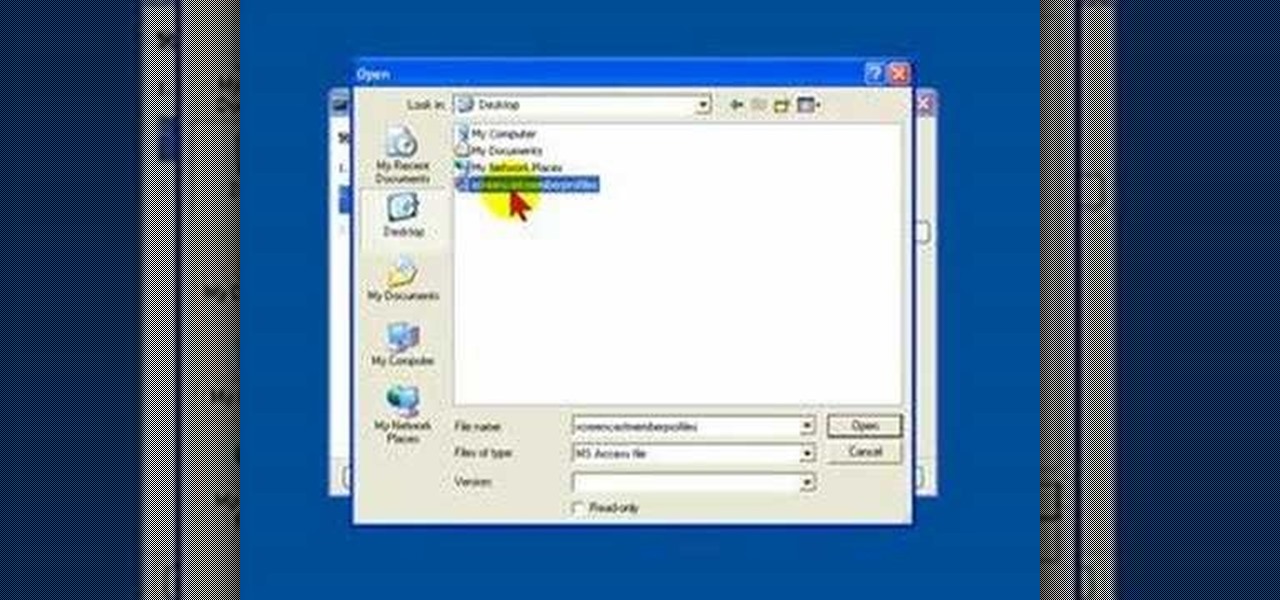
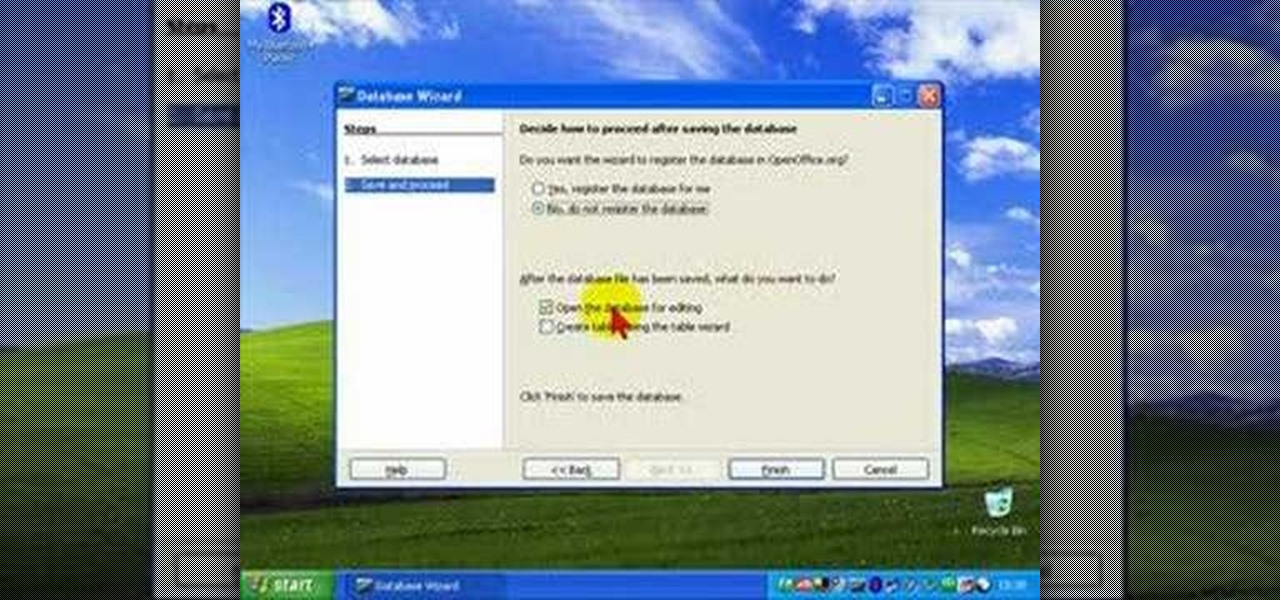
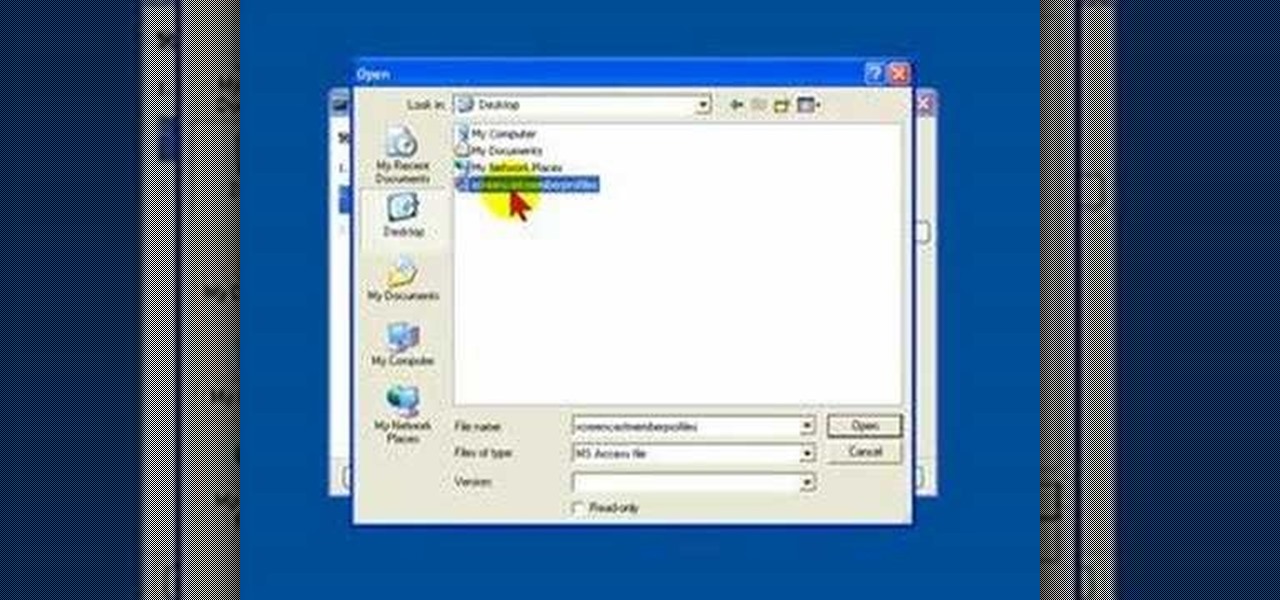
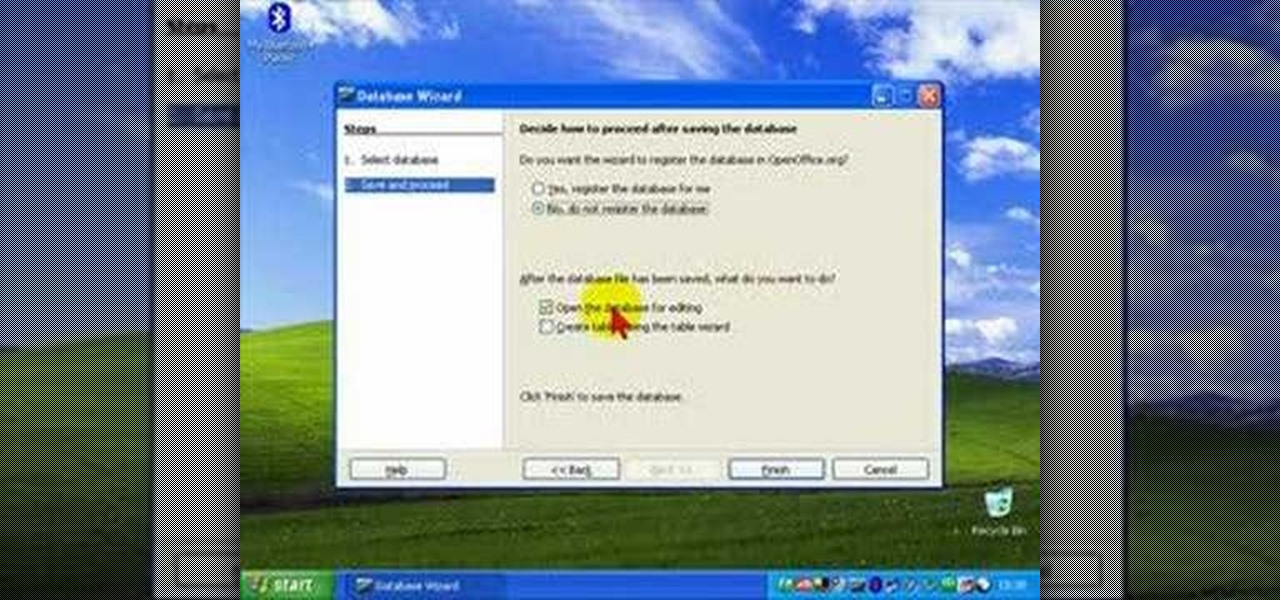
While you cannot directly open a Microsoft Access database file in OpenOffice Base, it is possible to connect Base to an Access database, and manipulate the data contained within it.

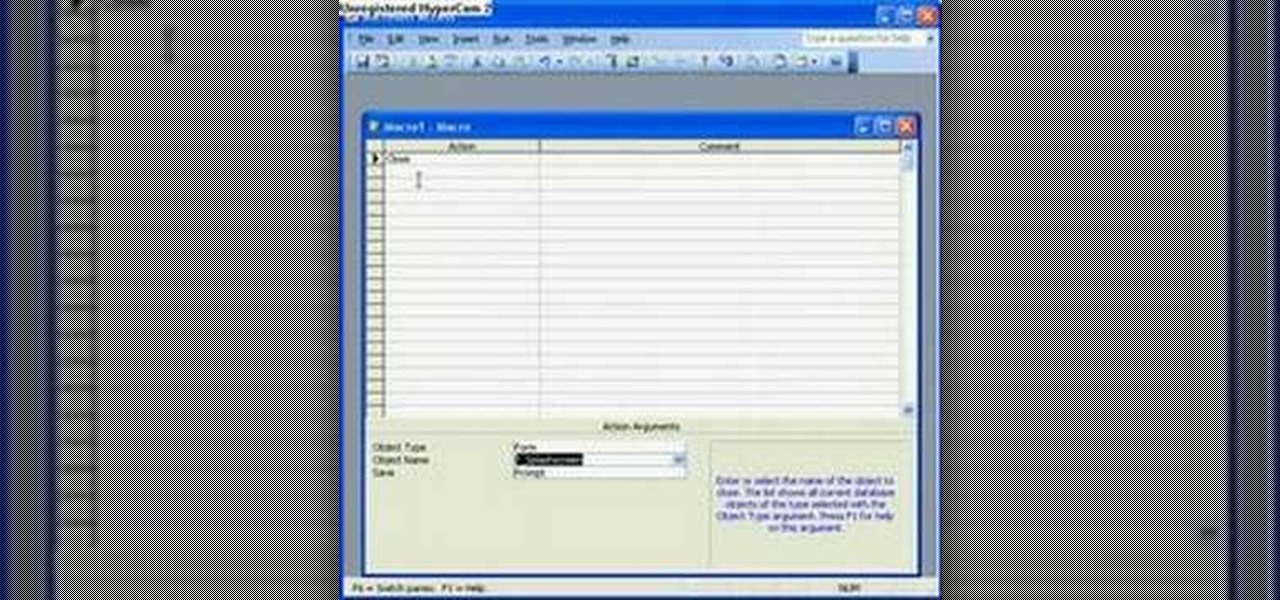
In this six-part video tutorial, learn how to create an access database. The following six parts go over the following:

This data management tutorial shows you how to take a Microsoft Excel Spreadsheet and import it into a MySQL Database using CSV files and PHPMyAdmin in cPanel. Being able to move data from Excel to MySQL is an important part of database content management, so if you use cPanel to manage your databases, you'll want to watch and learn how to import Excel spreadsheets into your MysQL databases.

How to manage user logins by creating a MySQL user login database with PHP. Part 1 of 3 - How to Create a MySQL user login database with PHP.

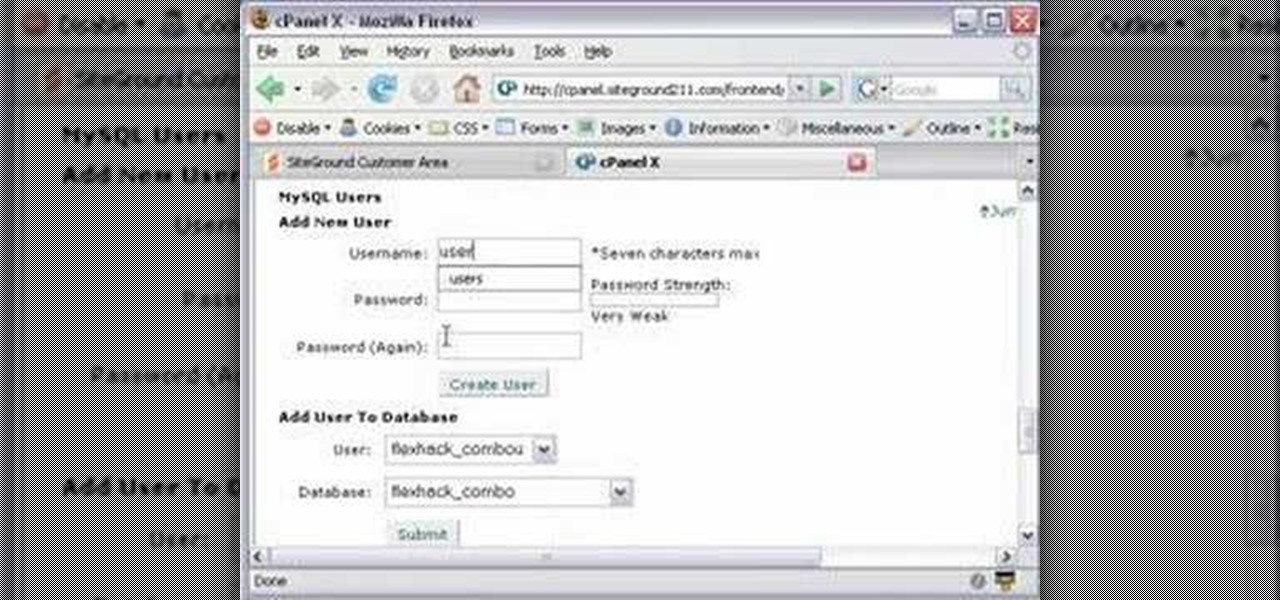
This CoffeeCup Web Form Builder software tutorial shows how to create a MySQL database to be used in CoffeeCup Form Builder to build web forms. Mike Lively shows you how to do this using cPanel and the Site Ground server for hosting since it allows an unlimited number of MySQL databases. Start by creating your database in cPanel and then upload the results to CoffeeCup Form Builder.

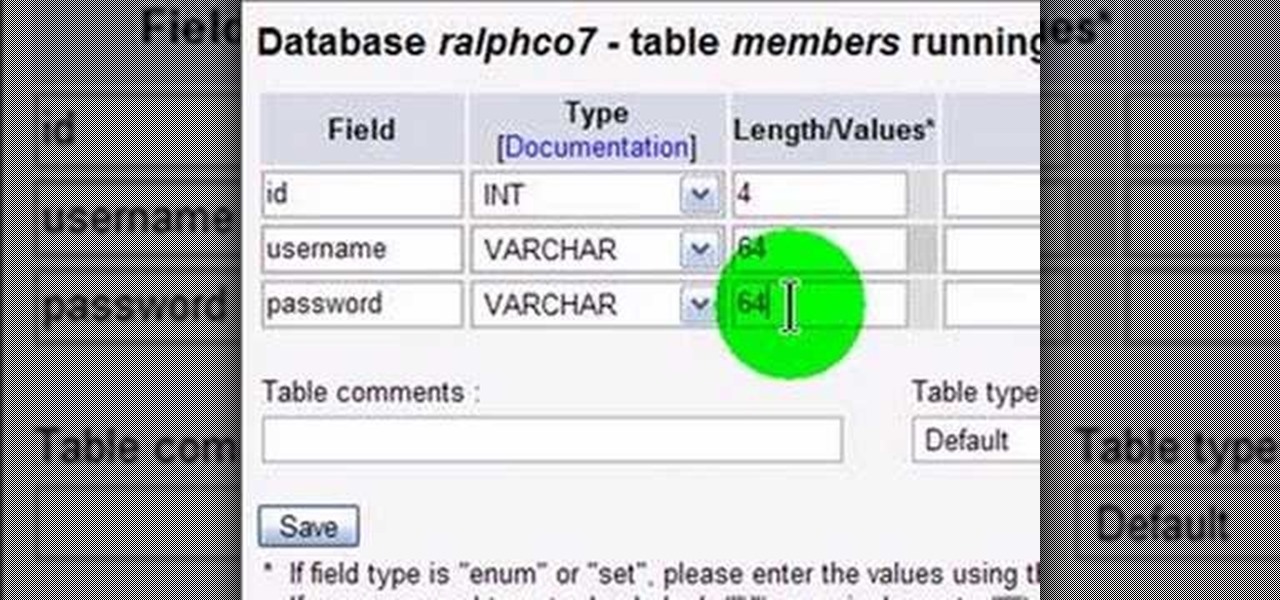
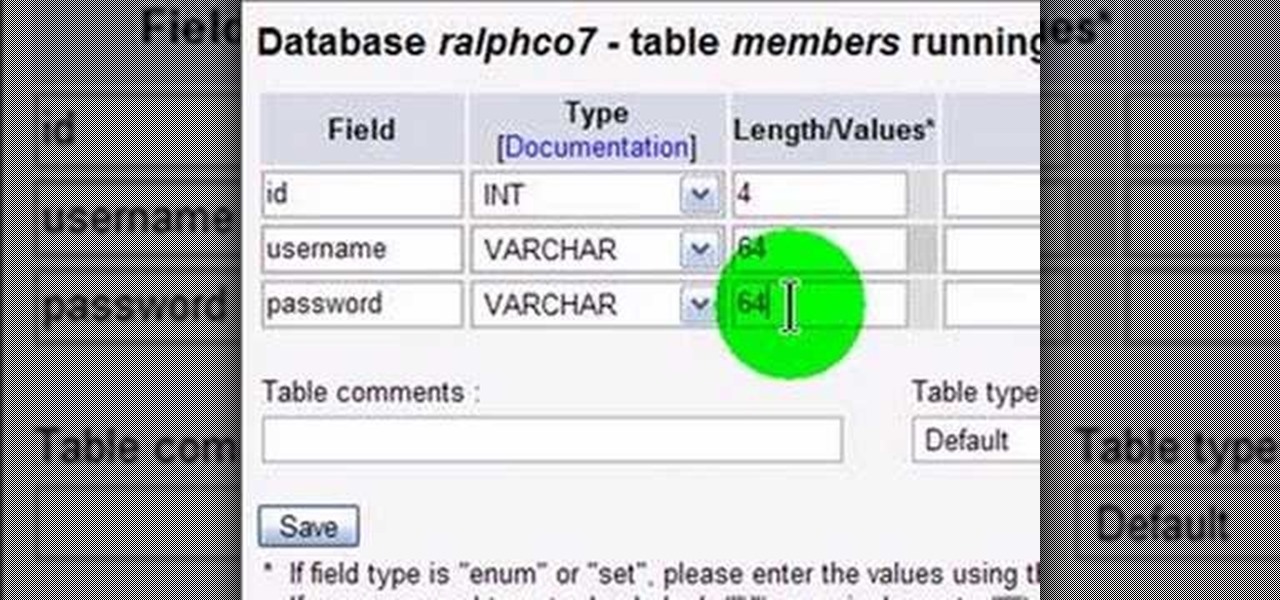
MySQL is a database for serving data on the web. This video teaches viewers how to connect to a database and add data in PHP & MySQL. PHPMyAdmin is an interface that allows you to interact with MySQL more easily. Use the form in the program to create a database; choose the name for your database and select 'create'. Next you can create tables within your database, also using the forms provided. Within the tables you can set your variables; PHPMyAdmin has fields that allow you to choose the ty...

Learn how to open up your old Access 2003 databases in MS Access 2010. Whether you're new to Microsoft's popular database management application or a seasoned MS Office professional just looking to better acquaint yourself with the Access 2010 workflow, you're sure to be well served by this video tutorial. For more information, and to get started using the Backstage view in your own Access projects, watch this free video guide.

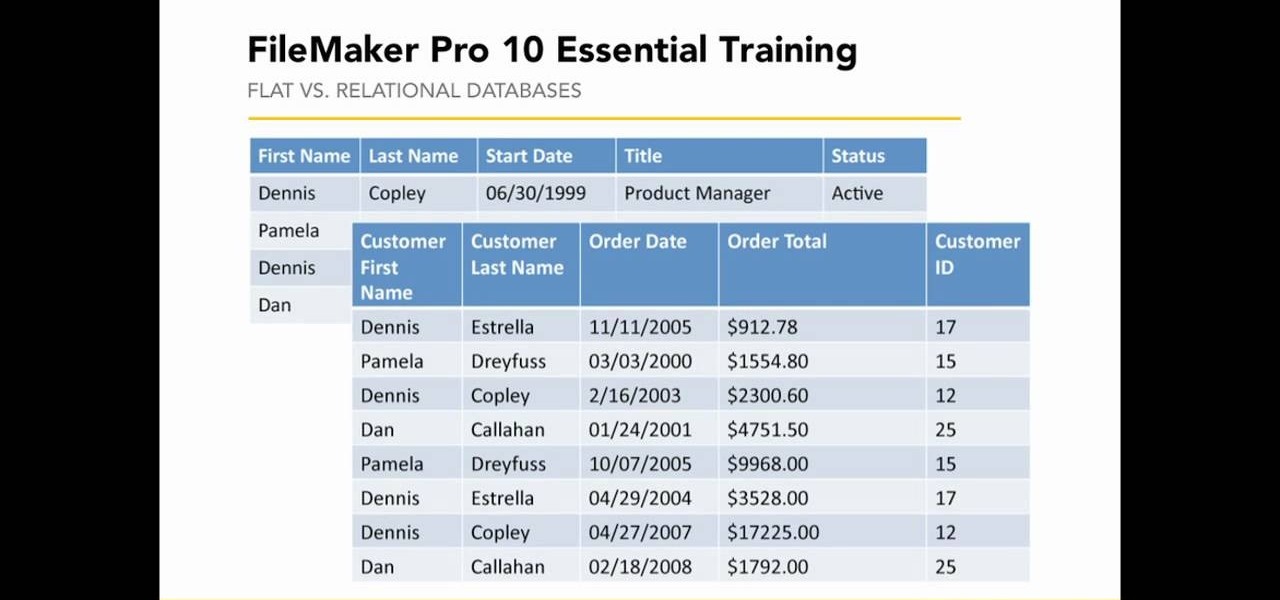
Learn how to create (and tell the difference between) flat and relational databases in FileMaker Pro 11. Whether you're new to the FileMaker Pro database management program or just want to learn how to take advantage of FileMaker Pro 11's new features, you're sure to benefit from this free video tutorial from the folks at Lynda. For more information, including detailed, step-by-step instructions, take a look.

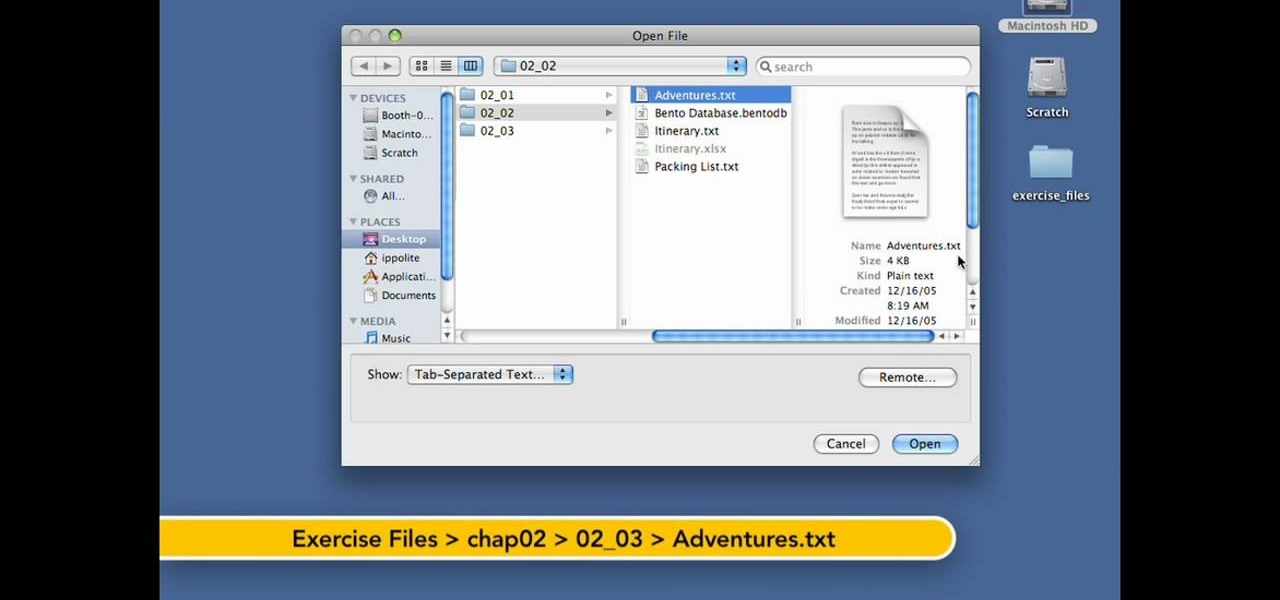
Want to create a database from an existing file within FileMaker Pro? Whether you're new to FileMaker Pro database management program or just want to learn how to take advantage of FileMaker Pro 11's new features, you're sure to benefit from this free video tutorial from the folks at Lynda. Specifically, this software tutorial provides a complete overview of how to quickly generate databases from existing files.

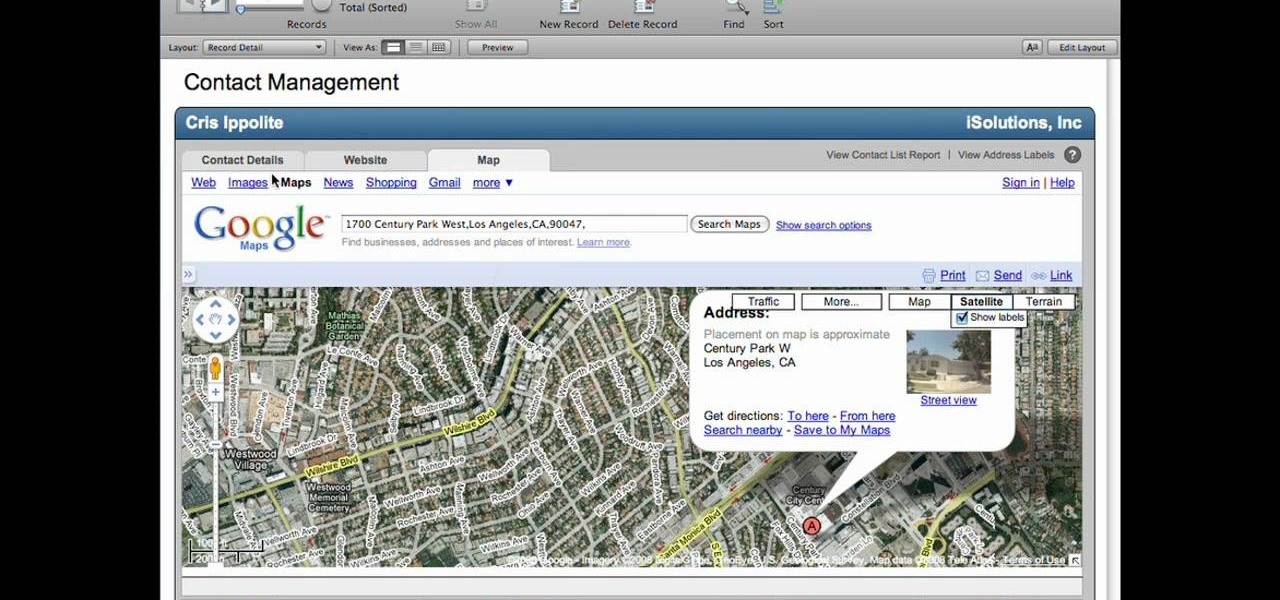
Lyndapodcast teaches you how to create a database using FileMaker Pro 10. You can link one contact with multiple addresses and information and store that into a single database. You can also add content from the web into your FileMaker layout, including maps, pictures and music. You have a security module where you can set permissions for the users using the database. You can also publish the FileMaker database to the web. For this go to File - Sharing - Instant Web Publishing. Another featur...

This video, presented by Cris Ippolite, makes a comparison between flat files and relational databases made with FileMaker Pro 10. It starts by showing that programs like Microsoft Excel uses, what in the databases circles, are called flat files. This flat files have a big disadvantage: it cannot communicate with other files even those have related data. So, instead of using those, if you want to ease your job, you should use relational databases. With databases, the tables communicate betwee...

The Microsoft Office Access 2007 relational database manager enables information workers to quickly track and report information with ease thanks to its interactive design capabilities that do not require deep database knowledge. In this Microsoft Access video tutorial, you'll learn about what queries are, and scratches the surface on what they can do, For more information, and to get started running your own database queries in Access, take a look.

In this tutorial we show you where to download MySQL Query Browser and how to access and edit your databases. MySQL Query Browser is an easy way to access database information remotely from your desktop without having to log in to your server. Learn where to get MySQL Query Browser, and how to use it to access and edit your databases.

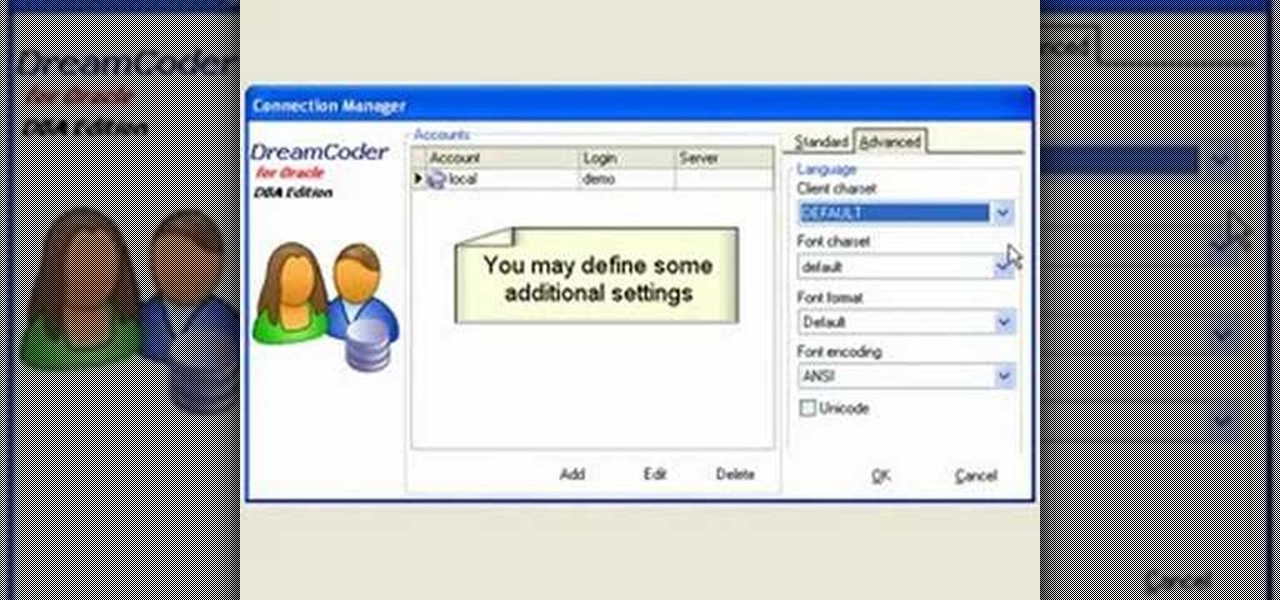
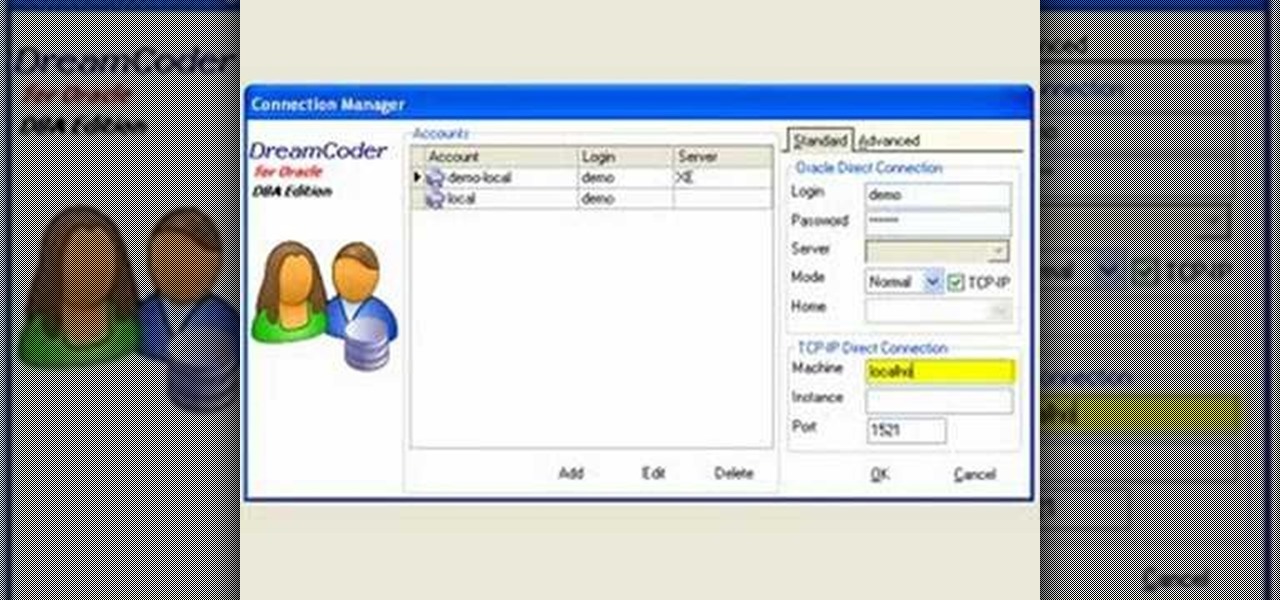
If you're new to DreamCoder for Oracle, one of the very first things you'll almost certainly want to know how to connect to a remote Oracle database. Happily, this tutorial will walk you, step by step, through the process. To learn how to establish a connection between a given Oracle database and the DreamCoder for Oracle, take a look!

A PHP programming tutorial on how to set up a user database. Part 1 of 2 - How to Create a phpMyAdmin user database.

As a web developer, I often read articles about hackers (from the lowly to the knowledgeable) infiltrating websites via the dreaded 'SQL Injection' method and completely taking control, changing, gaining access, or destroying the owner's data. As a fellow web developer, I'm sure you want to know how to protect against it. Well, here it is! In this article, you will find out what SQL Injection is, what you can do to protect against it, and additional recommendations that are easy to do and onl...

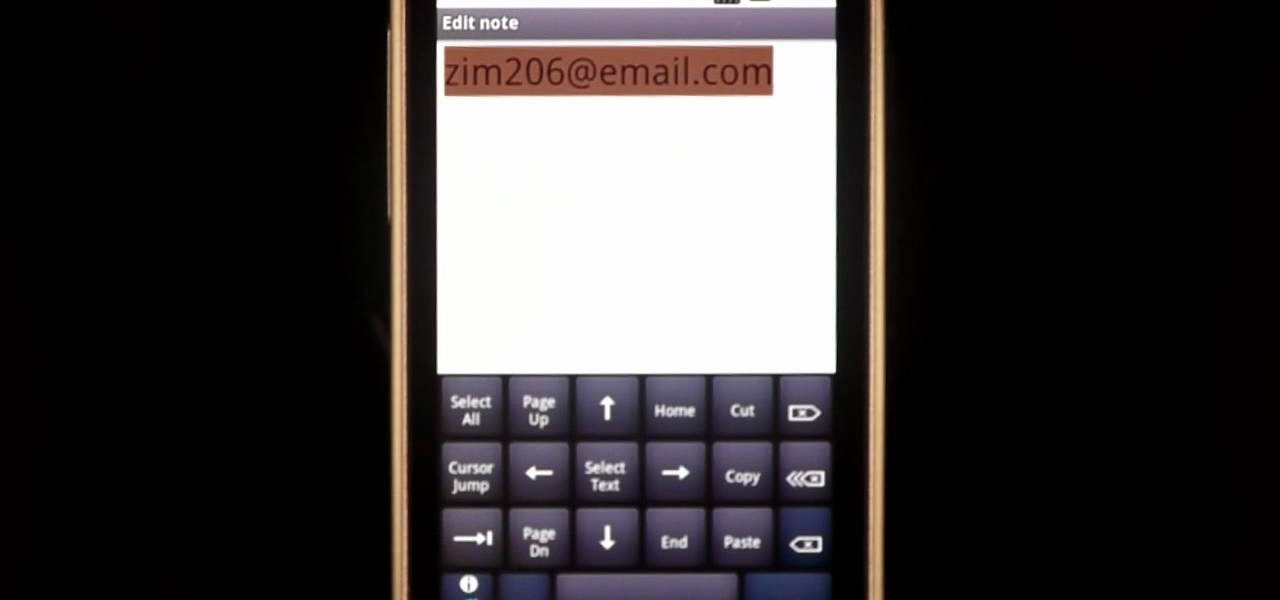
If there are words that you use often but Swype doesn't know them yet, you can easily add them to the database of your texting program. In this clip, learn all about adding uncommon or unique words to your Skype dictionary so that you can text even faster. You can even add web addresses, e-mails, nicknames and anything else you use often and don't want to tap out.

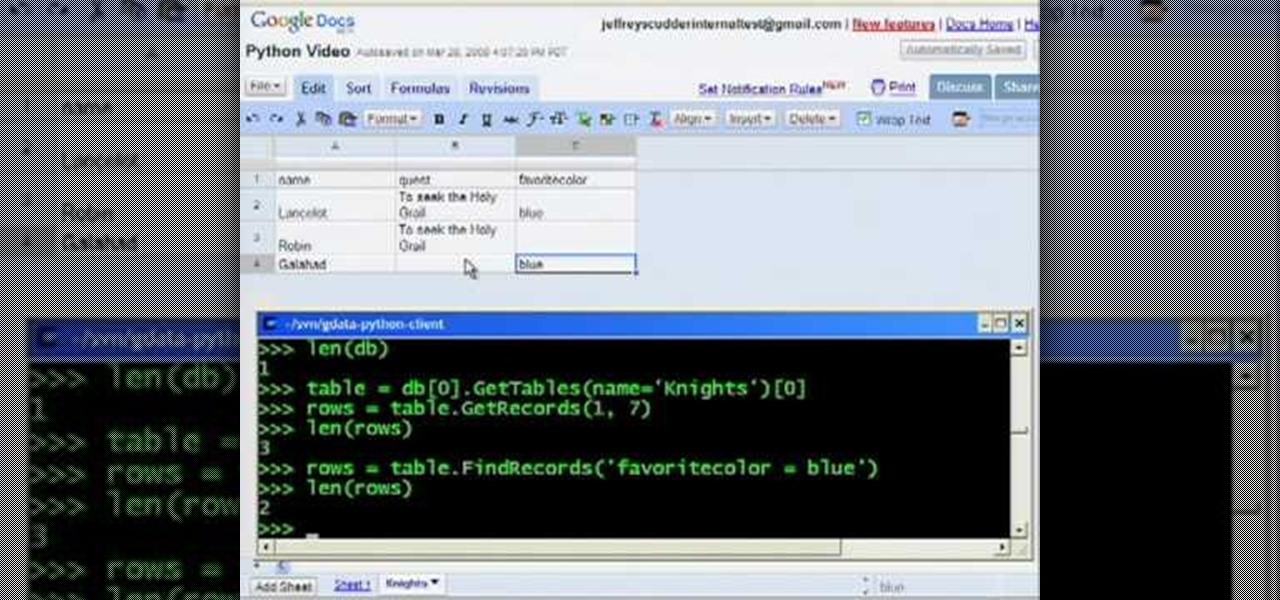
Watch Jeffrey Scudder demonstrate his GData Python Client Library extension that makes it easy to use Google Spreadsheets as a database in the information cloud.

Learn how create a Point Of Interest (POI) database using Google Earth and KML2CSV. You can upload this file to your GPS or GPS-enabled phone to create custom tracking searches.

Learn how to modify your old databases for use in Microsoft Access 2007. Whether you're new to Microsoft's popular data management application or a seasoned MS Office professional just looking to better acquaint yourself with the Access 2007 workflow, you're sure to be well served by this video tutorial. For more information, and to get started using old databases in Access 2007 yourself, watch this free video guide.

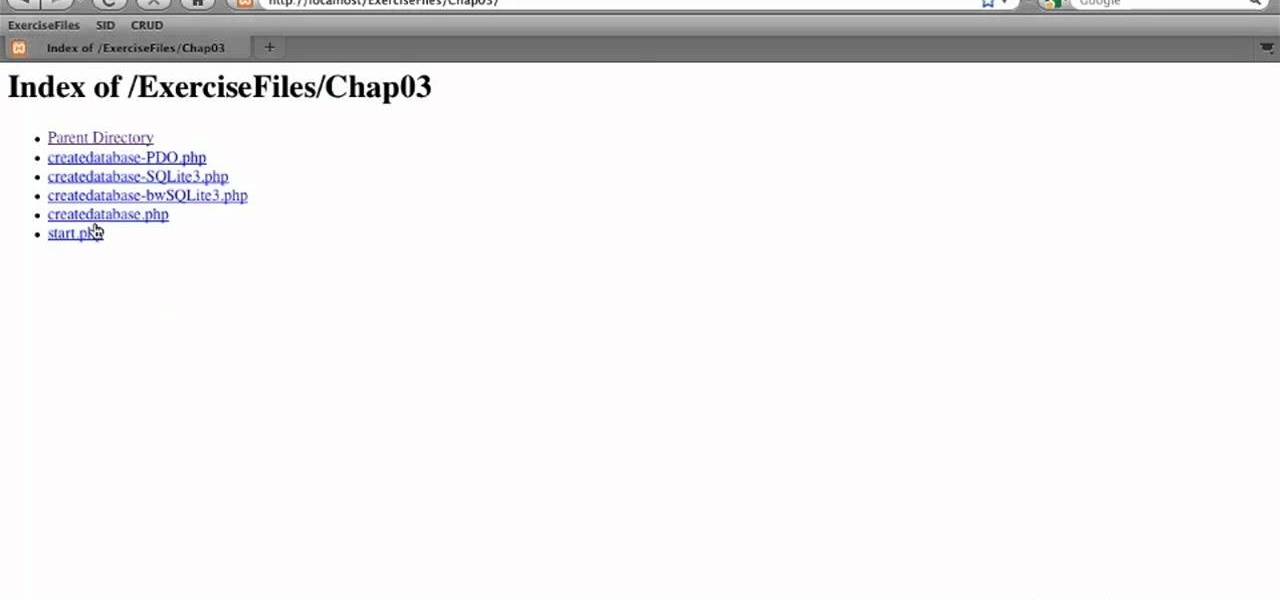
In this clip, we learn how to create a new database when using SQLite 3. Whether you're entirely new to the SQLite embedded relational database management system or are a seasoned developer merely looking to brush up on a few of the basics, you're sure to find much to take away. For more information, take a look!

In this installment from the Unorthodox Hacking series of Internet security tutorials, you'll learn how to get a shell on an Oracle database. To see how to pop a shell from within Oracle or even perform a port scan from the database itself, watch this hacking how-to.

The Microsoft Office Access 2007 relational database manager enables information workers to quickly track and report information with ease thanks to its interactive design capabilities that do not require deep database knowledge. In this Microsoft Access video tutorial, you'll learn about using Access to add a splashscreen to your database that runs when the file is opened. For more on using custom splashscreens within Access, watch this MS Office how-to.

The Microsoft Office Access 2007 relational database manager enables information workers to quickly track and report information with ease thanks to its interactive design capabilities that do not require deep database knowledge. In this Microsoft Access video tutorial, you'll learn about hiding the backend of the database and opening the switchboard automatically. For more information, watch this MS access video tutorial.

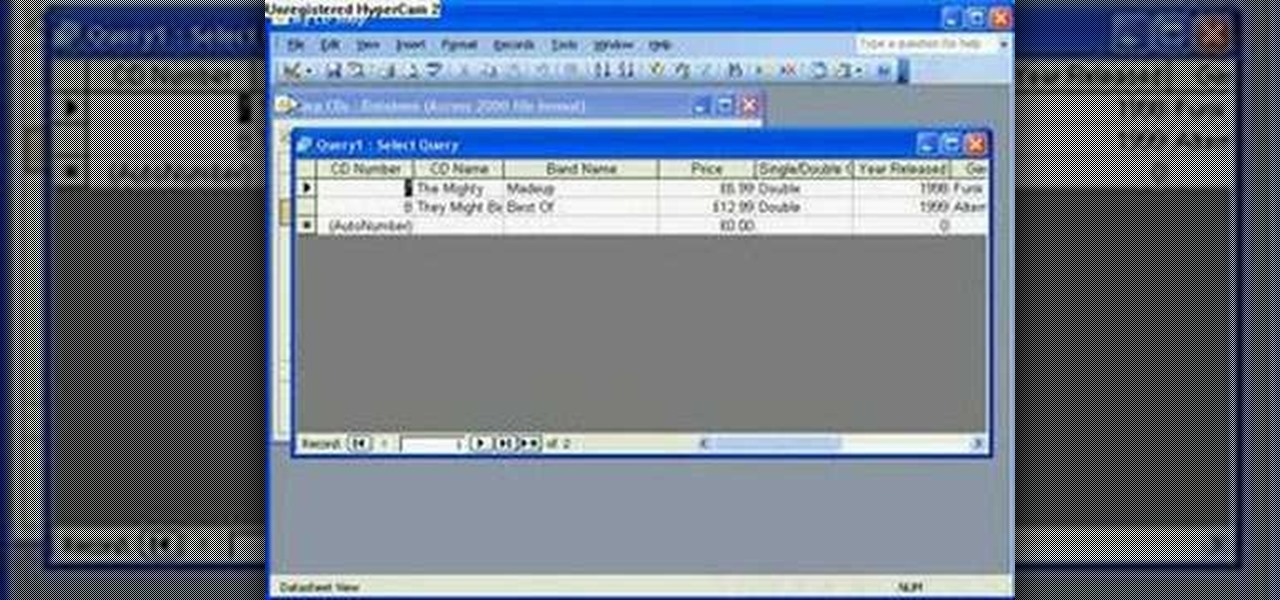
The Microsoft Office Access 2007 relational database manager enables information workers to quickly track and report information with ease thanks to its interactive design capabilities that do not require deep database knowledge. In this Microsoft Access video tutorial, you'll learn about using simple select queries on one or more fields. For more information, or to get started using simple queries in your own Microsoft Access databases, watch this how-to.

Did you know that OnTime includes tools to help you backup and restore your OnTime database? This installment from Axosoft's own series of video tutorials on the OnTime Project Management Suite covers the basics of restoring and backing up a database through the OnTime system. Take a look.

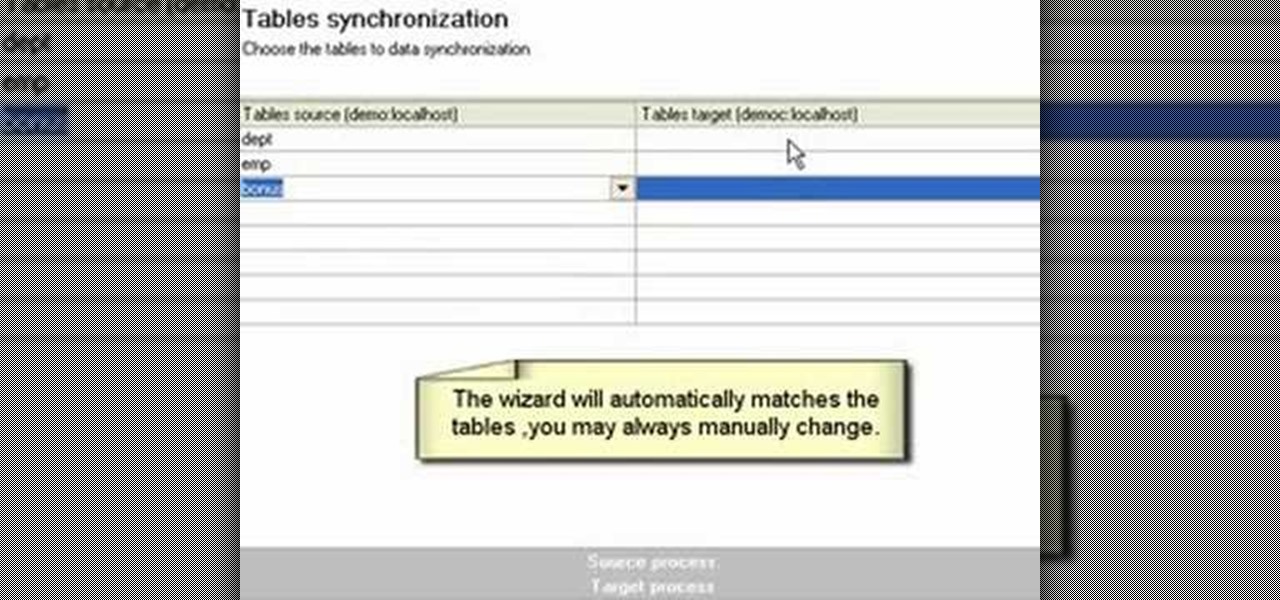
If you're new to DreamCoder for MySQL, one of the first things you may want to know how to do is synchronize two remote MySQL database. Happily, this tutorial will walk you, step by step, through the process. If you need to synchronize databases with DreamCoder for MySQL, take a look!

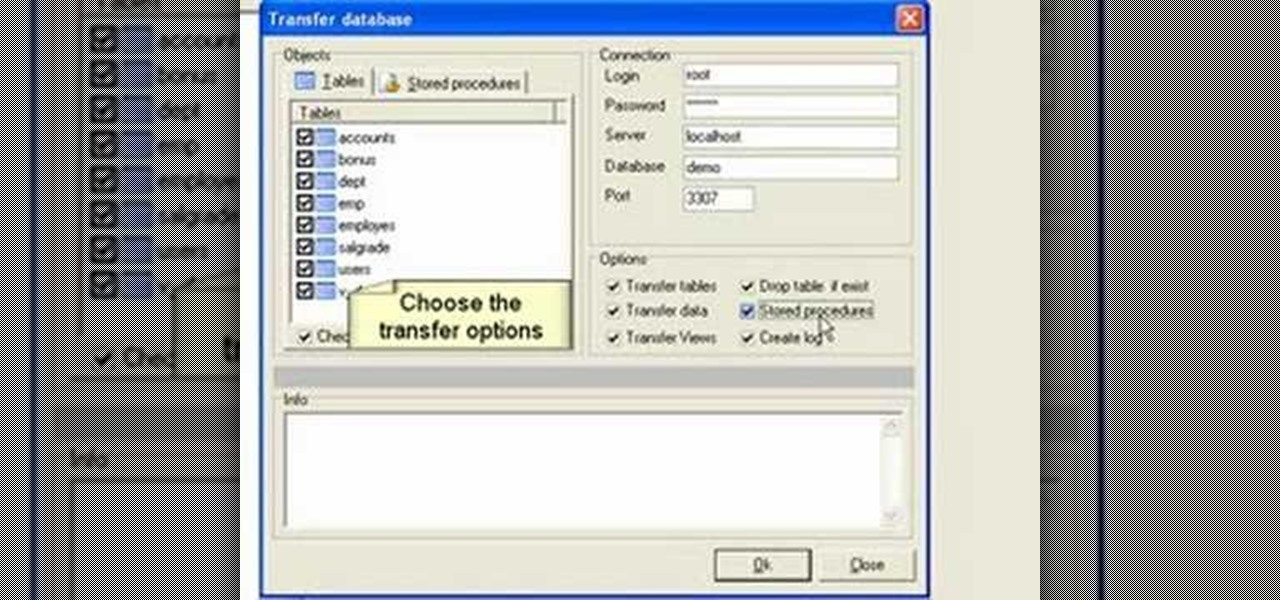
If you're new to DreamCoder for MySQL, one of the things you may want to know how to accomplish is how to exchange information between two remote MySQL databases. Happily, this tutorial will walk you, step by step, through the process. To learn how to transfer data between two MySQL databases simultaneously within DreamCoder for MySQL, take a look!

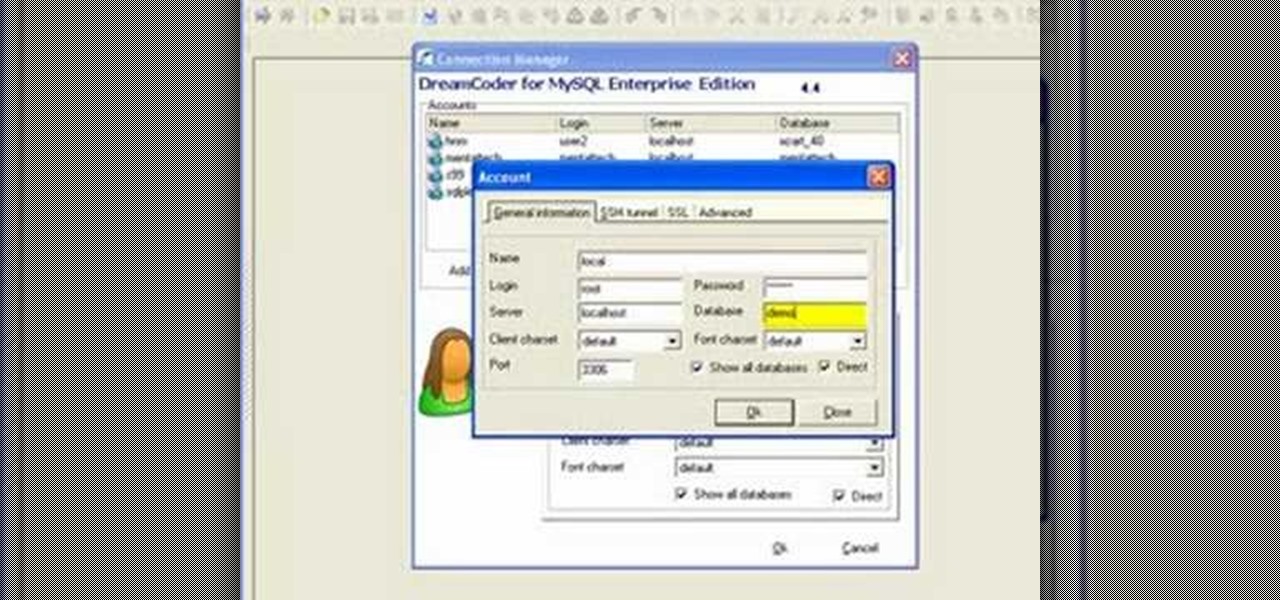
If you're new to DreamCoder for MySQL, one of the first things you may want to know how to accomplish is to connect to a remote MySQL database. Happily, this tutorial will walk you, step by step, through the process. To learn how to establish a connection between a given MySQL database and the DreamCoder for MySQL, take a look!

This tutorial will walk you, step by step, through, the process of establishing a connection between Oracle database server and DreamCoder for Oracle using the TCP-IP Direct connection option. To learn more about connecting to an Oracle database without an OCI client, press play!

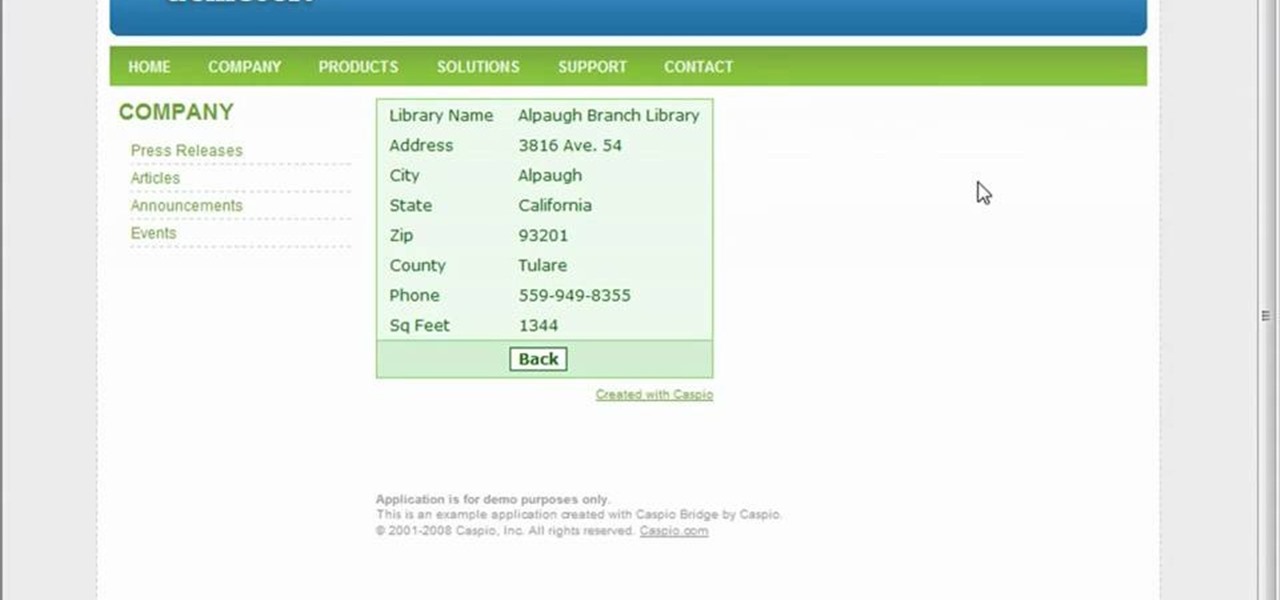
To start off the process of publishing your access database online we first look at a sample MS ACCESS database with typical formats and a online searchable application where users can search by library name or city and get details of the library. There are 3 steps to publish the database. The first step is importing data which can be done through clicking on the file menu and then click on import data through a Microsoft Access Database. Now select the file you want to import through the bro...

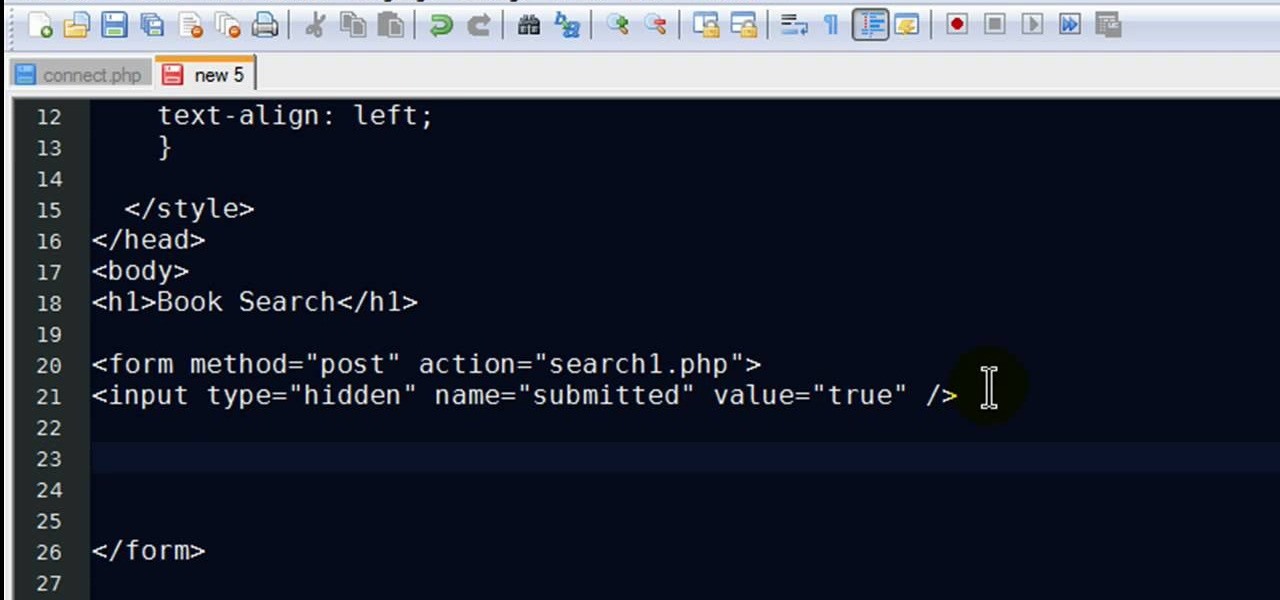
New to PHP? There's no better way to learn a scripting language than to code with it. And this two-part video guide, which demonstrates how to use a web form to retrieve data from a database with PHP, will get you started on your way.

Welcome back, my greenhorn hackers! In a previous tutorial on hacking databases, I showed you how to find online databases and then how to enumerate the databases, tables, and columns. In this guide, we'll now exfiltrate, extract, remove—whatever term you prefer—the data from an online database.