Welcome back, my tenderfoot hackers! In some of my past articles, I've shown numerous ways of embedding a listener/rootkit on a remote system, including buffer overflows of the operating system, getting the victim to click on a link to our malicious website, and sending a malicious Microsoft Office and Adobe Acrobat file.

See the demo to learn how to take advantage of some of the advanced features of Office Communicator 2007, including rich-text formatting, transferring files, and escalating to a Live Meeting. If you use Office Communicator at your office for video conference calls or chatting, then this tutorial will explain some very useful advanced features.

David Wygant discusses how to flirt with women and make yourself rejection proof. If a man does everything right and a woman doesn't respond, don't have a temper tantrum. If you do that, you will not realize that your dividend may pay off in the long run and have instead shot yourself in a foot, which the woman will notice. As an alternative, kill her with kindness. Walk away and retain your power. You may run into her later and have a different outcome. Be okay if the attraction isn't escala...

You need to escalate the relationship, excite her mind and tease her. You don't want to be too pushy or too confident. You also shouldn't fall in the other extreme, of becoming too quiet and just listening to her. Make sure you remember what she says, so you can latch onto any piece of important information. You need to get into her moment, into her world. You can be goofy and fun and be an approachable person. Women will tend to be attracted by these type of men.

Abusive relationships are unhealthy and should be remedied immediately. There are many steps that can be taken to help end an abusive relationship.

Compulsive gambling is a recognized addiction, just like alcoholism or chemical dependency. Follow these steps to see if you might fit the profile. Recognize the signs of compulsive gambling with this guide from Howcast.

UAC is something we've all dealt with on Windows, either as a user, administrator, or attacker. It's a core feature of the Windows security model, and for the most part, it does what it's supposed to. But it can be frustrating as a hacker when attempting privilege escalation, but it's easy enough to bypass UAC and obtain System access with Metasploit.

Android Oreo may not be the flashiest release, but it's got tons of under-the-hood changes. We recently discovered documentation in the AOSP source code that outlines one of these understated features, which has been dubbed "Rescue Party."

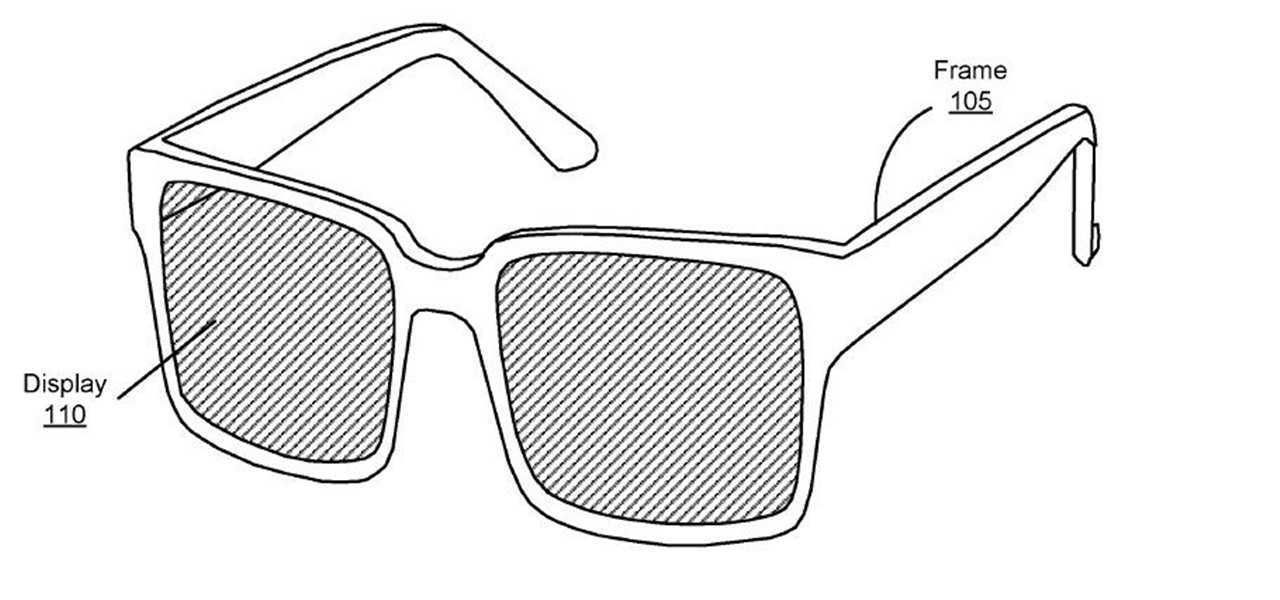
A patent application for waveguide-based smart glasses submitted by way of their subsidiary Oculus sheds light on Facebook's plans to escalate their augmented reality efforts.

iCloud can occasionally be the worst part of being an Apple user. It's useful for backing up your information, however, sometimes the problems that stem from Apple's cloud service are so tremendously frustrating they almost seem intentional. Well, buckle in, because it's possible there may be a widespread login issue.

We've seen plenty of good, bad, and weird things that have come out of the worldwide augmented reality game Pokémon GO, including murder and location-based bans, but nothing on a large scale. That was, of course, until Iran decided to ban the game country-wide.

The ukelele is a great little instrument that is easy to learn, sounds good, and is portable. How much better could it be? They work especially well for covering pop songs, since they're very simple and catchy, which is the essence of the ukelele. This video will teach you how to play the hit song "Best I Ever Had" by Drake on ukelele.

ShapeWriter is the iPhone version of Swype. With this app you can type texts extremely fast without ever lifting your finger off the keypad! In this tutorial, learn all about how to type at the speed of light using ShapeWriter and send messages so fast you'll wonder why you ever bothered to type things out in the first place. Have fun!

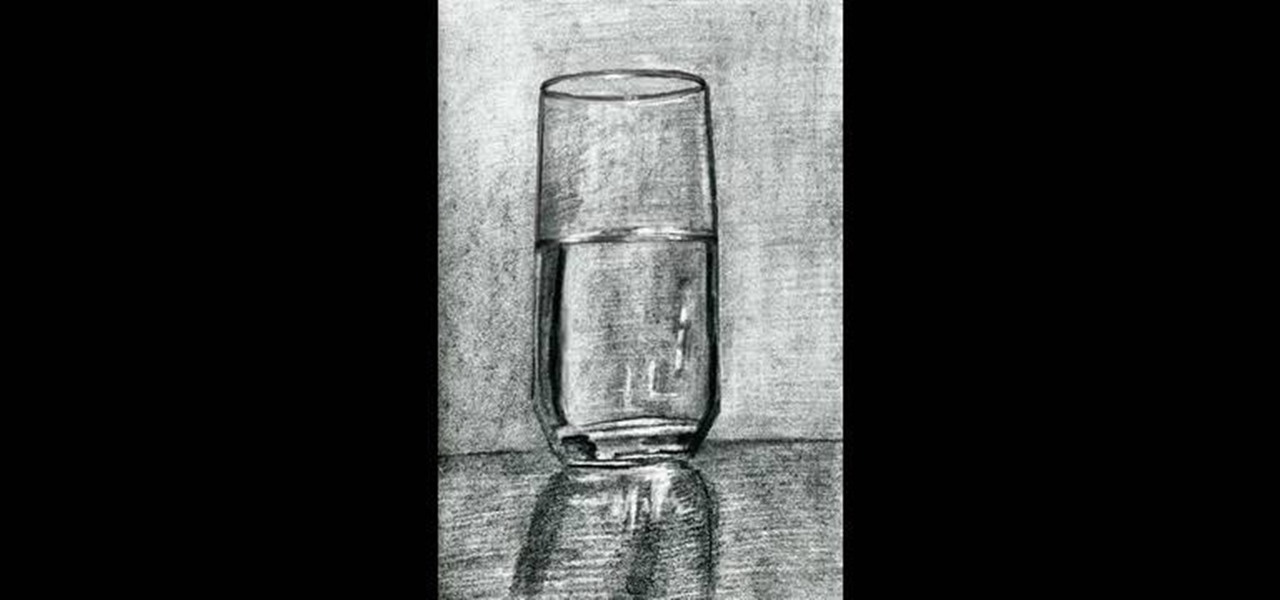
Drawing a glass of water is one of the most basic things you'll ever learn in art class, but it is also one of the most important studies you'll ever make about form, color, tone, and shape.

Gaining access to a system is always exciting, but where do you go from there? Root or bust. Sure, a compromised host is a great way to run a botnet, or do some other boring, nefarious thing—but as hackers, we want root. We also want to take the easiest path possible, search out low-hanging fruit, and exploit them. SUID programs are the lowest of the low-hanging fruit.

Welcome back, my neophyte hackers! Many newbie hackers seem to be confused regarding the process or methodology to employ a successful hack. Most want to simply go straight to the exploit without doing the due diligence to make certain that the hack will work and you won't get caught.

You should always base your eyeshadow color choices on the color of your eyes, but there are in fact some colors that look amazing on everybody. One of these universally flattering hues is gold. Whether you have brown eyes or green, gold brings out the tiny golden flecks in your iris.

Never Have I Ever (or I Never, depending on which coast you're from) is a fantastic drinking game that requires no equipment or coordination. Just a preferably mixed group of drinkers with secrets to hide. This video will explain how to play this perfect ice breaker game and get to know your friends better than you ever wanted to.

With so many cars, vans, and suvs storage is important as ever. Taking seats out used to be the only way you could ever get enough space for big bulky objects, but thanks to innovation and some smart people, it's easier than ever. And you'll see just that in this tutorial for how to use the rear stow'n go on a 2010 Dodge Grand Caravan. Good luck and enjoy!

Place slip knot on hook. Hold yarn taut with 2 sets of 2 of fingers placed about 1½” apart, with tail in other hand. Create loop that crosses over bottom of 1st strand with loop toward right side. Fold loop over main strand going past tail. Insert hook below at tail strand. Pull up a loop using main strand for this loop. Pull 2 ends of yarn taut while leaving slip knot on hook. In 1st chain work 1 single crochet. Skip 2 chains; work 1 double crochet in 4thchain. Picot stitch by chaining 3 & a...

Getting angry makes you look weak, especially in an argument. Defuse your temper with these helpful tips.

This could quite possibly be the easiest and funniest prank you could ever pull off on someone, all you need is a cup, straw, and lid. It is so unpredictable, No one will ever suspect a thing till they're completely wet. Find out how to execute this Funny prank by watching this video. Use this as inspiration for one of your April Fools Day pranks!

A daring look for Halloween that'll work for a Lady Gaga costume or to complement a sexy salsa dancer costume, this Lady Gaga-inspired makeup look involves hot pink eye tones and a glued on lace eyepatch that's almost "Phantom of the Opera"-like.

With Disney's futuristic video game movie "Tron" arriving in theaters this December, the call for an edgy, avant garde makeup look is now stronger than ever. Take inspiration from Olivia Wilde's warrior woman look and create your own graphic eye.

The art of privilege escalation is a skill that any competent hacker should possess. It's an entire field unto itself, and while it's good to know how to perform the techniques involved manually, it's often more efficient to have a script automate the process. LinEnum is one such script that can be incredibly useful for privilege escalation on Linux systems.

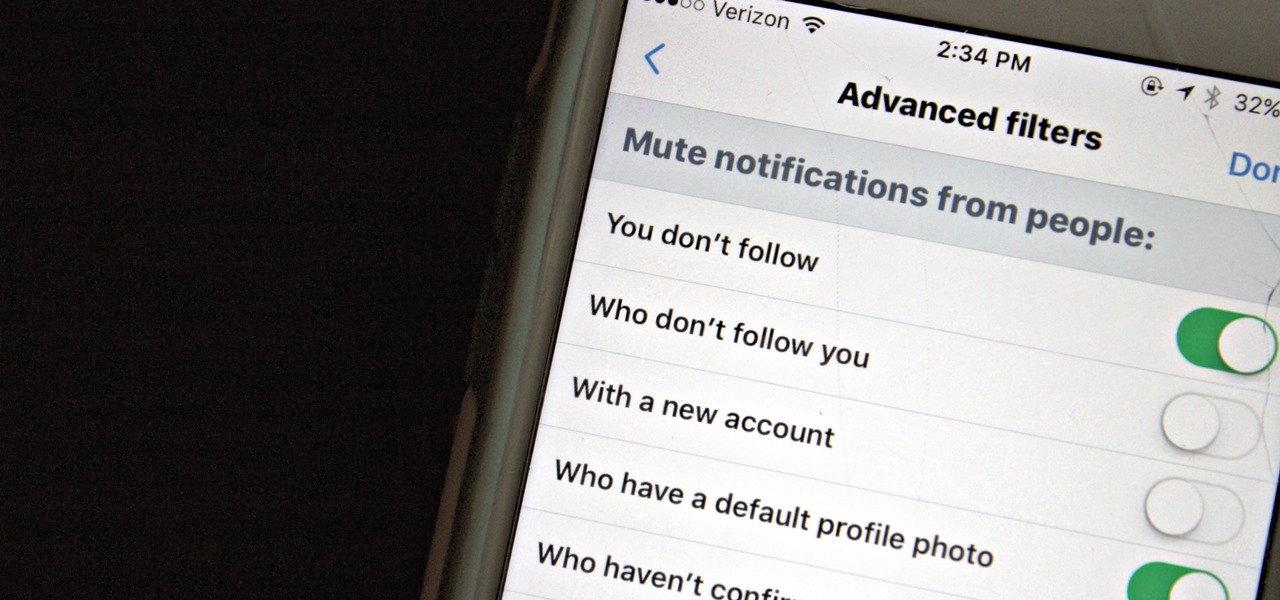
Twitter is a hotbed for abusive accounts. Because it's such an open app, strangers from all over the world can see your tweets. Obviously, not everyone agrees on everything, but sometimes things can escalate to the point where it's considered harassment from people you don't even know.

Although there has been much speculation about how much damage could be done if hackers were to take control of a country's SCADA systems, there have been few examples - until a few months ago, with the power outage in Ukraine caused by hackers.

Have you ever wondered if you can really ever beat addiction fully? If you've ever been addicted to a substance, it is so easy to become addicted to something else.

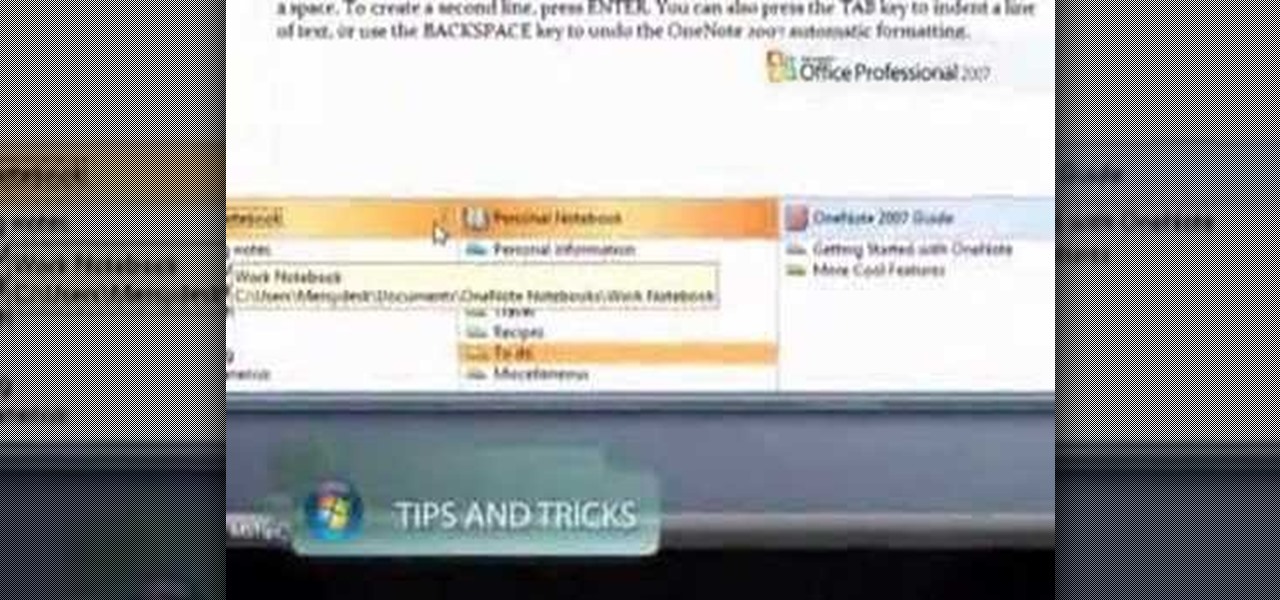
Do you ever wish you had a way to jot down an idea, and then illustrate it with a page from a document, a photo and a sound clip, all without opening multiple applications? Microsoft Office OneNote 2007 note-taking program is that advanced notepad, and is better than ever with new additions to the interface that make it even easier to organize yourself. For more on using MS Office OneNote, watch this video tutorial.

Without a doubt this is the biggest bow you can ever wear on your body - ever. And best of all, it's not slightly tackly like a Lady Gaga hair bow or bow clip-on accessory. In fact, this bow is so big it barely looks like a bow at all.

Ever wanted to hack your friends' Facebook accounts? With the Firesheep Mozilla Firefox browser add-on, it's easier than ever. Before you can use Firesheep to sniff account cookies, however, you'll need to download and install it. This clip will teach you everything you'll need to know.

This handy instructional video teaches the budding paper-design-enthusiast how to construct a three-dimensional paper word design. All you need is paper, an Exacto knife, a ruler, and a pen. Now you can make any word you've ever wanted to make stand up do it more quickly and easily than ever before. Ideal for teachers. Christmas lights optional.

You know that question your girlfriend asks that you never ever say "yes" to? "Does this (insert article of clothing) make me look fat?"

Have you ever used custom brushes in Photoshop? Have you ever created your own? Maybe you don't know how to use custom brushes or don't want to waste time making them from scratch. Don't worry, you don't have to! Watch this tutorial and learn how to find custom Photoshop brushes online and then download and install them in Photoshop.

In this cooking how-to video tutorial we show you how to smoke any chicken in a smoker with marinade. Watch and learn to make the best smoked chicken wings ever. All the ingredients you need to start smoking some poultry is: Blackening seasoning, garlic, Durkee chicken seasoning, soy sauce, celery salt, Italian seasoning, olive oil and of course chicken.

This is not magic but a very useful and very easy way to tie two pieces of rope together without them ever slipping apart. This simple how-to shows how to tie two pieces of rope together without them ever coming apart. This could be very helpful for sailing or anything you need to tie a knot.

After winning the 2015 FIFA Women's World Cup, the USA Women's National Soccer Team is ready to defend its title in the 2019 tournament.

Now that the NCAA Basketball Tournament is underway, 7-Eleven has decided to launch an augmented reality experience to remind basketball fans where they can quench their thirst throughout March Madness.

If two hands are better than one, then two hand-tracking SDKs must be better than one as well. After uSens announced its Hand Tracking SDK at the Augmented World Expo in Santa Clara on Thursday, ManoMotion unveiled the latest version of its own SDK. Both technologies give apps the ability to track hand gestures with just a smartphone camera.

Last week, I tried out StackAR, a puzzle app updated to support ARKit where the AR features felt mostly unnecessary.