In their first head-to-head major contract clash, Microsoft has emerged victorious over Magic Leap, as the US Army has awarded a $480 million contract to the HoloLens maker.

When we talk about driverless technology, the go-to companies are usually Waymo, Uber, or Tesla. However, traditional automakers like Ford and GM are also staking claims to the driverless and advanced driver assistance spaces.
Definition Declare is a card game played by 3 or more people. If 4 people are playing the game, then one pack of 52 cards (without the jokers) is sufficient. For 4 to 8 people, two packs of cards are required, without jokers.

Welcome to my tutorial where Voidx and I will be expanding on my previous article to provide more clarity into the logic of the code.
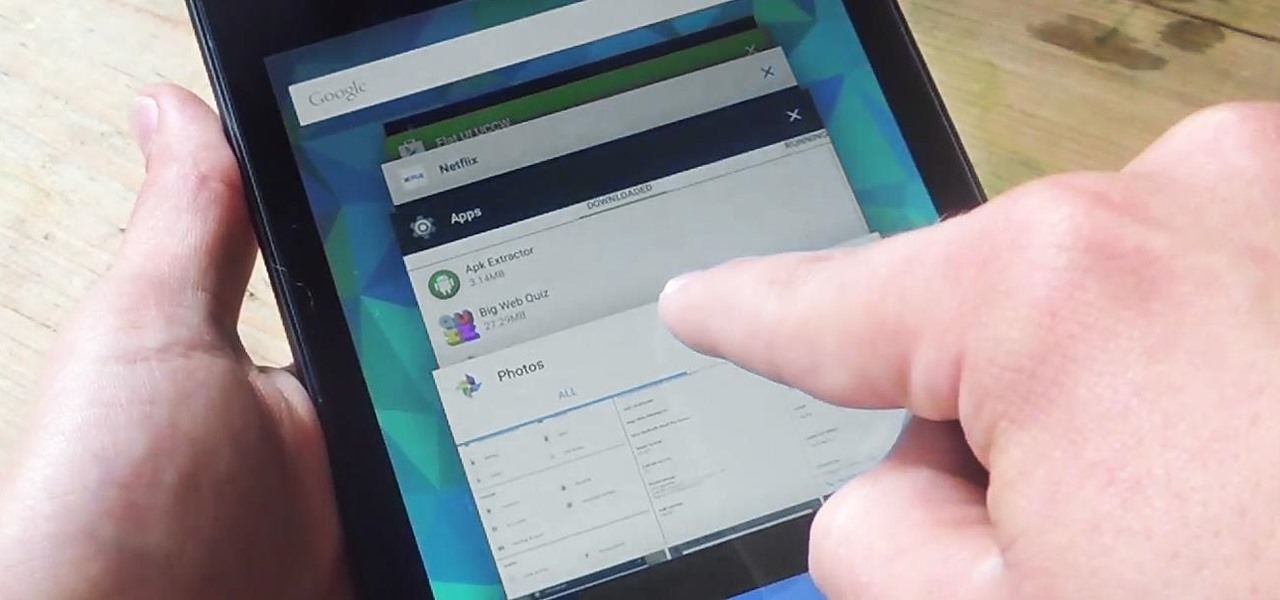
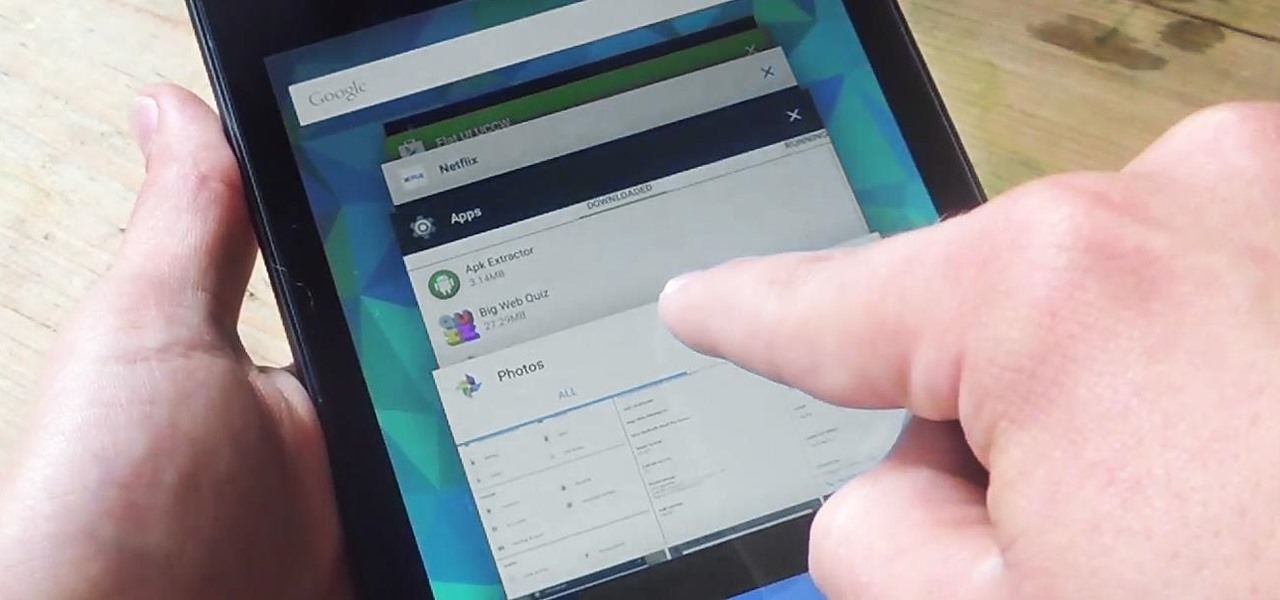
On earlier Android versions, you were able to hold down on an app's icon in the recent apps menu (aka app switcher) and jump straight to the app's info page. From there, you could easily uninstall the app, force-stop its activity, or clear its cache and data.

Influenced by the growth of augmented and virtual reality technology as well as 3D computer vision, Ericcson Ventures invested in Matterport, whose hardware and software help companies create AR/VR experiences.

A new survey shows that the majority of companies have an interest in using augmented reality, though adoption remains low. Meanwhile, two companies with support roles in the augmented reality industry are seeing positive financial results.

It may seem strange to find the director of engineering at a question-and-answer site all of a sudden pick up and lead a new driverless startup, but to Kah Seng Tay, both engineering tasks require building the right infrastructure to handle large amounts of AI data.

Mercedes-Benz's parent company, Daimler, announced their intention today to put self-driving taxis on the road in three years or less in a partnership with Bosch.

When computers have vision but people don't, why not have the former help the latter? That's the gist behind the Cognitive Augmented Reality Assistant (CARA), a new HoloLens app developed by the California Institute of Technology.

Udacity, the online education startup that set out to train a school of self-driving car engineers, is now spinning off into its own autonomous tech company called Voyage.

Is "Last Resort" Steampunk? Well, no. I mean, how could it be?

Ford's appointment of Jim Hackett as its new president and CEO reflects how the company is largely pinning its long-term survival hopes on its driverless business. Following his previous role as head of Ford's Smart Mobility division, which overseas Ford's autonomous driving activity, Hackett will help the company take a more self-driving direction as a whole.

Alright, NB community! Here we go... Bubble Sort. What Is Bubble Sort?

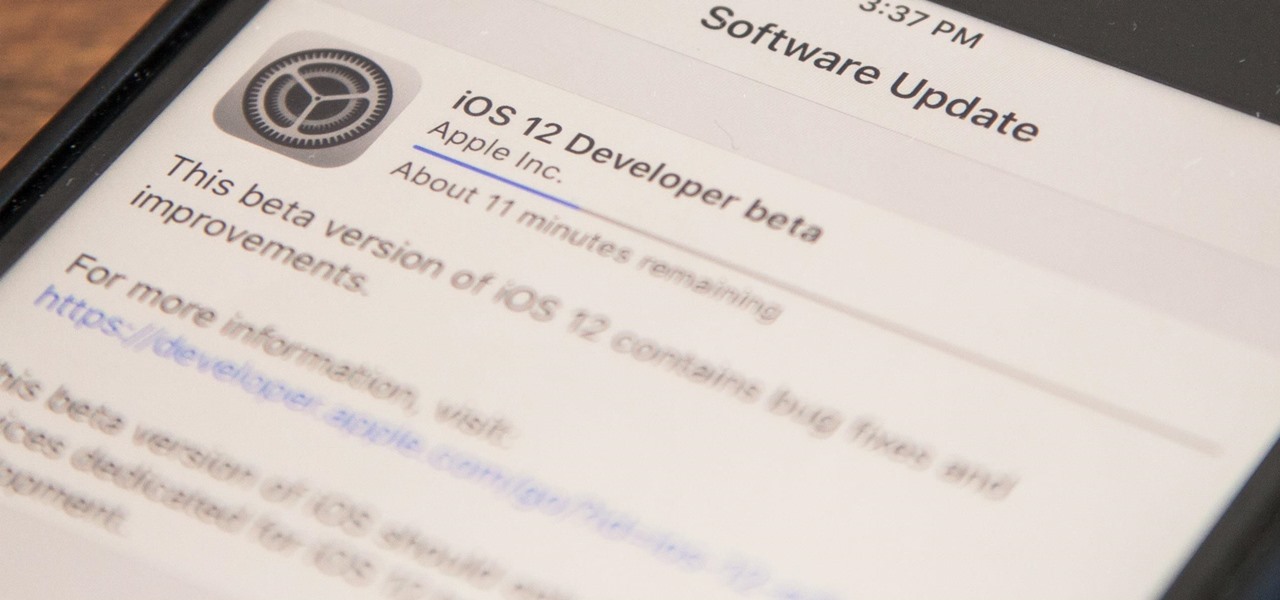
Apple released iOS 12 on Sept. 17, and most of the announced features have been released for the iPhone's latest available operating system. However, some brand new features can be accessed with Apple's latest beta, iOS 12.4. If you want to try out all its new features before everyone else, you can install the developer or public beta on your iPhone right now.

Welcome back to control structures, part two featuring the three types of loops. Here we go! What Is a Loop?

Welcome back, my fledgling hackers! Scripting skills are essential is ascending to the upper echelons of the hacker clique. Without scripting skills, you are dependent upon others to develop your tools. When others develop your tools, you will always be behind the curve in the battle against security admins.

In this simple tutorial you will be shown step-by-step how to write local shellcode for use on 64-Bit Linux systems. Shellcode is simple code, usually written in assembly that is used as payload in exploits such as buffer overflow attacks. Payloads are the arrow head of an exploit: though the rest of the arrow is important for the delivery of the attack, the arrow head deals the killing blow. In reality, payloads are slightly less exciting yet far more interesting and intelligent than medieva...

Analysis of photographs and social connections can be a huge component of social engineering. Understanding who a person is, as well as who they know, can establish links within a company. This information could be used by hackers to execute elaborate social engineering attacks.

TCP/IP Client / Server Application Hello! Today's blog post will be about coding a very rudimentary Client and Server application duo, which will communicate by using TCP Sockets.

» ‘Obama Truth Team’ Orders GoDaddy To Shut Down Website. A political website that contained stinging criticism of the Obama administration and its handling of the Fast and Furious scandal was ordered to be shut down by the Obama campaign’s ‘Truth Team’. » Former Bush Attorney General Alberto Gonzales Confronted On Torture.

The widely used expression "free as a bird" intimates an enviable existence: delicate, yet mighty wings transporting to destinations no human could so breezily venture. But despite their fanciful, superhero ability, in truth, the avian race leads one of the most difficult existences in the animal kingdom. Yes, birds have existed for eons—they likely evolved from small dinosaurs of the Jurassic period—but for these creatures, life can be ruthless.