News: Augmented Reality App Maker Houzz Reveals Major Data Breach
In the realm of internet security, it's becoming clear that augmented reality is not immune to the increasing wave data breaches plaguing users.

In the realm of internet security, it's becoming clear that augmented reality is not immune to the increasing wave data breaches plaguing users.
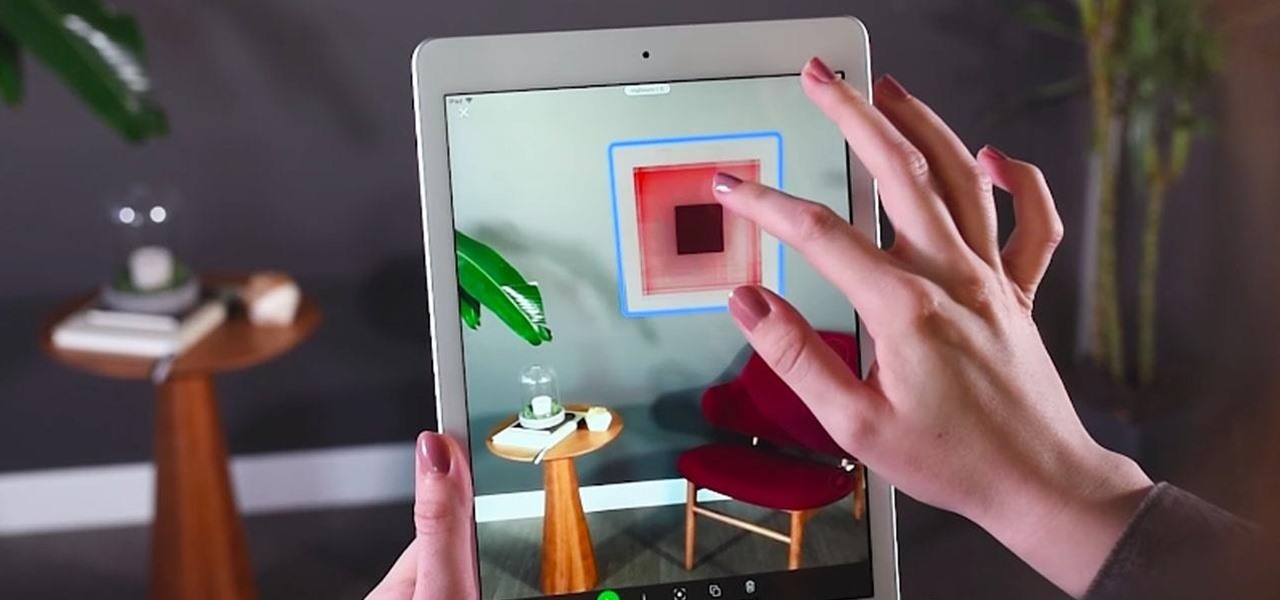
Everything lives online these days, so it's not uncommon to have hundreds of credentials for different accounts on apps and websites. That's why a password manager is a must, and your iPhone has one built right into iOS that you can start using today. In iOS 14, it's gotten even more useful since it can now monitor your passwords regularly to see if any match leaked password lists online.
Adobe, eBay, and iCloud have been hacked...now add Spotify to that list. The company has stated that on May 27th, they became aware of "some unauthorized access to [their] systems and internal company data" but that "only one Spotify user's data has been accessed and this did not include any password, financial or payment information."
Data breaches are all too common now, and the latest one you need to know about involves Timehop, a mobile app that makes it easy to reminisce over old photos. The breach, which took place on July 4, was revealed on Sunday, July 8. At the time, Timehop disclosed that 21 million users had been affected by the breach, but it now appears that all users were impacted in some way.

The easiest way around a security policy is to find users who don't follow it. The Have I Been Pwned database identifies accounts with information breached by major third parties like Yahoo and LinkedIn. With Maltego, hackers can locate breached accounts created using company email addresses, potentially giving attackers access to a company account if the employee reuses a compromised password.

Many online users worry about their accounts being breached by some master hacker, but the more likely scenario is falling victim to a bot written to use leaked passwords in data breaches from companies like LinkedIn, MySpace, and Tumblr. For instance, a tool called H8mail can search through over 1 billion leaked credentials to discover passwords that might still be in use today.

Attention all Redditors: Between June 14 and June 18, Reddit experienced a data breach. The popular website claims it discovered the breach on June 19 and has since made the necessary moves to contain and eliminate the threat. Unfortunately, there isn't much they can do about the data was that accessed and stolen — your user data.

So much information exists online that it's easy to get lost in data while researching. Understanding the bigger picture can take a lot of time and energy, but narrowing the question to one that's easy to answer is the first step of any investigation. That's why analysts use open-source intelligence (OSINT) tools like Maltego — to help refine raw data into a complete understanding of a situation.
T-Mobile's credit-checking system was recently hacked, and this one is about as bad as it gets. The names of 15 million customers, their date of birth and social security number, as well as driver's license numbers and additional information was illegally accessed, meaning the potential for identity theft here is huge.

Modern Warfare 2 is considered to be one of the best FPS games of all time, so its no wonder why you are interested in how-to videos for it! Released for the Xbox360, Playstation 3, and PC, Modern Warfare 2 provides an excellent gaming experience for action lovers. Whether you are new to the game or have completed it on Veteran, there's a good chance you'll find some useful information in some of these how-to videos.

New statements from Apple make it clear that they do not believe a hacker, or group of hackers, breached any of their systems. This comes after a recent report from Motherboard that a hacker gang called the "Turkish Crime Family" is threatening to remotely wipe up to 559 million iPhones by April 7.

Welcome back, my neophyte hackers! Digital forensics is one of the fields often overlooked by aspiring hackers. In a rush to exploit every and any system they can, they often ignore learning digital forensics—the field that may lead to them being traced.
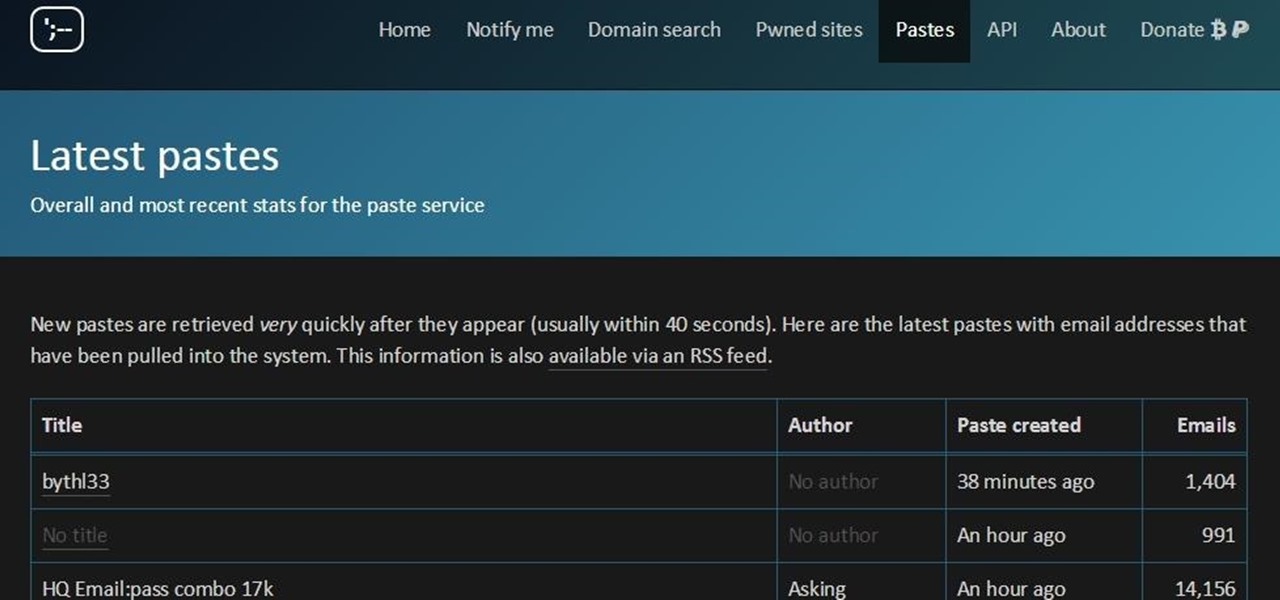
You must have read news about hackers dumping the data online, recent one was Ashely Madison. It's only the big companies' data, which gets noticed once it is out. There are many other small leaks which don't even get a mention. So this article is the first one of my series which will help you to find hacked accounts. Some of you must already know about this, but this post is intended for the new learners. This also serves as an example of my learning how a good service can be used in other w...

Leaked databases get passed around the internet and no one seems to notice. We've become desensitized to the data breaches that occur on a daily basis because it happens so frequently. Join me as I illustrate why reusing passwords across multiple websites is a truly awful practice — and compromise hundreds of social media accounts in the process.
The Breach is one of the many popular online games available from Kongregate Games. Like any game, it can be rendered more enjoyable in the long-term by cheating at it. This video will show you how to use Cheat Engine 5.6 to hack the game and give yourself more experience points, making your character nearly indestructible. Don't let the zombies win, watch this video!

Equifax reported on Sept. 7 that it discovered a breach on July 29 which affects roughly half of Americans, many of whom don't realize they have dealings with the company. Hackers got away with social security numbers, addresses, and driver's license numbers, foreshadowing a "nuclear explosion of identity theft." Let's explore what really happened and what you and those around you can do to protect yourselves.

Stuck in the middle of Memorial Valley? Need for Speed: Hot Pursuit is the newest and highest rated racing game, where you can play as either a street racer or a cop. This video shows you how to get through the Breach of the Peace mission.

Make sure the sliding shafts for your horse and buggy work correctly.

Kipkay has developed a shoplifting prank, and all you need is a little electromagnetic strip to play this prank at Walmart (or wherever). You also need to bring a magnet. You swipe the strip thirty times with the magnet and this will actually magnetize the strip. Use this as inspiration for one of your April Fools Day pranks!
In this tutorial for the hit game, Red Dead Redemption, you'll be going after the Austin Overpowered achievement. It nets you a sweet 25 points to add on to your gamerscore must be completed by doing three things. You must beat the Twin Rocks, Pike's Basin, and Gaptooth Breach hideouts. They seem pretty easy, but for the untrained cowboys it could be difficult. So good luck and enjoy!

Our future technology has a lot of amazing possibilities, and few have more promise than augmented and mixed reality headsets. But these advancements come with several concerns over privacy, and if we don't understand them, we may lose control of our own data without even knowing.

In a letter dated February 16th, Apple CEO Tim Cook responded to the FBI's demand that Apple create a "backdoor" to bypass the encryption on an iPhone used by one of the perpetrators of last year's terrorist attack in San Bernardino, CA. Cook began the letter by stating that Apple has "no sympathy for terrorists" and has cooperated in giving the FBI all of the information that it has available.

As it turns out, your Android apps are pairing together to share your data without asking for your permission first. Researchers from Virginia Tech developed a tool called DIALDroid to monitor exchanges of data between Android apps over the last three years, and what they've found is quite alarming.

Keeping your online data and identity private is an uphill battle, but with the anonymity network Tor, you have a pretty decent line of defense from prying eyes.

It seems like there's a cyber security scare every day. Consumers are growing increasingly concerned about the safety of their accounts, and they have reason to be. Hackers will maliciously attack you anywhere — and we mean anywhere — they can to get your private information.

Breaking a lease is almost always considered a legal breach of contract, even if a tenant has a good excuse. Here are some exceptions to the rule

WhatsApp sneakily made some security changes to iCloud backups without your knowledge, ladies and gents. Not that strengthening security is a bad thing, but still!
Get a crash course on HScript Expressions, Variables, and Attributes in Houdini 10. If you don't even know what this means, then you probably need to check this video tutorial series out. Understanding how to massage data in Houdini is key to giving yourself the creative edge and allowing you to unleash mind-blowing visual effects. This 18-part video series covers a variety of simple yet essential weapons in your arsenal including Global, Standard and Custom Variables to Math and String Modif...

Welcome back, my fledgling hackers! As nearly everyone has heard, Target Corporation, one of the largest retailers in the U.S. and Canada, was hacked late last year and potentially 100 million credit cards have been compromised. Happening just before Christmas, it severely dampened Target's Christmas sales, reputation, and stock price (the company's value has fallen by $5B).
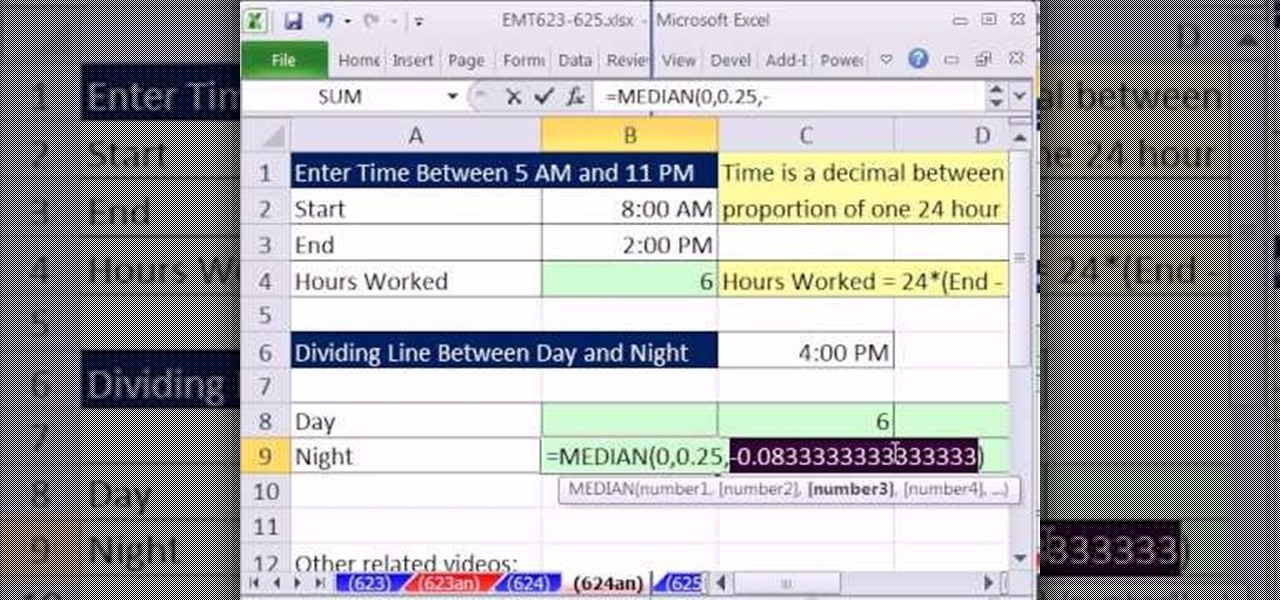
New to Microsoft Excel? Looking for a tip? How about a tip so mind-blowingly useful as to qualify as a magic trick? You're in luck. In this MS Excel tutorial from ExcelIsFun, the 624th installment in their series of digital spreadsheet magic tricks, you'll learn how to break apart the hours worked in a given day into one part for the day shift and a second part for the night shift using the MEDIAN function instead of the IF function. The MEDAIN function can be used when there are different ca...

Due to the overnight success of smartphones, millions of people are connecting with others. Currently, over 15 million text messages are sent every minute worldwide. Most of this communication is happening in the open where any hacker can intercept and share in the discussion unbeknownst to the participants. However, we don't need to communicate insecurely.
Cool tips and tricks on Facebook give you some extra edge on others. This trick will demonstrate that how to talk to your special loved ones that no one else can understand.

Today's bikes are tough, but they're held together by fasteners that mustn't be stressed. Many components come with recommended torque settings. Breach these settings and you may void your warranty. It now makes sense to use torque wrenches. Torque is a measurement of torsion, a twisting force. A "torque wrench" has a spring-loaded indicator that gives a numerical readout of the amount of torque being applied through it.

In this video tutorial, viewers learn how to create drop down menus in Microsoft Excel. This task is very easy, fast and easy to do. Begin by highlighting a desired cell. Then click on the Data tab and click on Data Validation under Data Tools. When the Data Validates window opens, click on the Error tab and deselect "Show error alert after invalid data is entered". Then click on OK. Now simply type in the data into the selected cell. This video will benefit those viewers who use Microsoft Ex...
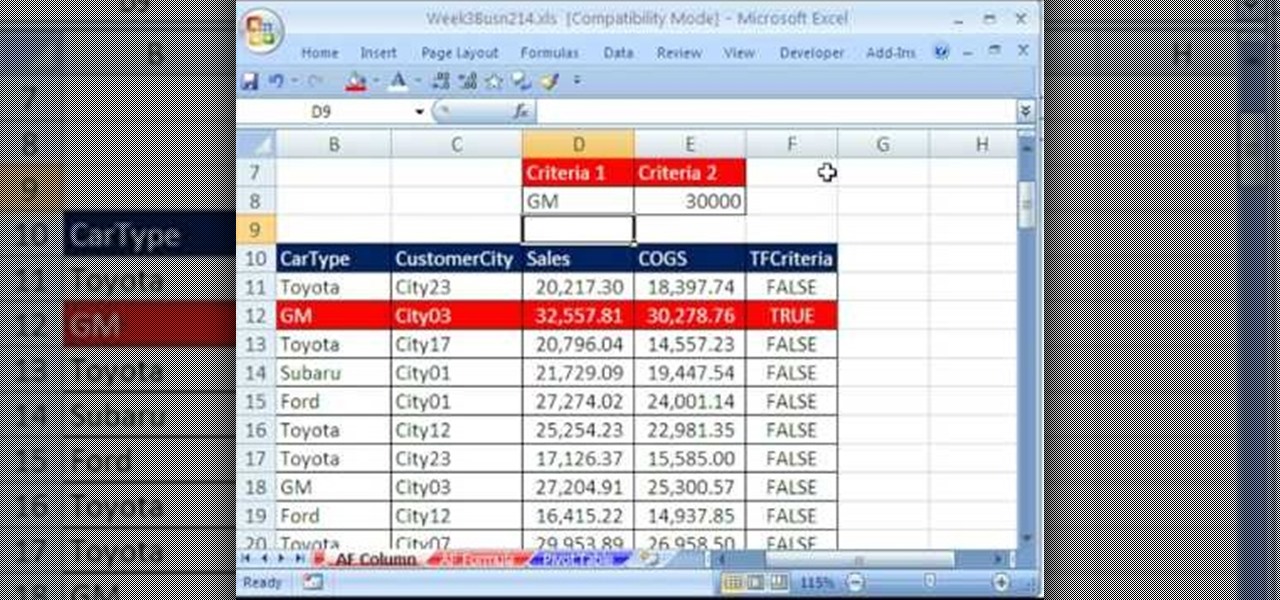
Whether you're interested in learning Microsoft Excel from the bottom up or just looking to pick up a few tips and tricks, you're in the right place. In this tutorial from everyone's favorite digital spreadsheet guru, ExcelIsFun, the 19th installment in his "Highline Excel Class" series of free video Excel lessons, you'll learn about using Advanced Filter to extract data from an Excel List/Table/Database. See these 7 Advanced Filter examples:

Even Halo: Reach on the Xbox 360 has hidden collectable items! All in the convenient (for the people hiding them) size of a small data pad! Earlier you got access to the first 9 data pads that you can get on any difficulty. Next, you will get a look on the next 9 data pads that you can only acquire while being on Legendary difficulty!

Data thieves don't have to be programming wizards to get their hands on your personal information. They often find hard drives that contain financial and other sensitive data at flea markets, charity shops, the city dump—even on eBay. In this video tutorial, PC World explains how to completely erase sensitive data from old drives before recycling or discarding them. Wipe your old hard drives with this how-to.
The increasingly important world of white hat or "ethical" hacking is getting competitive. Thanks to growing salaries and opportunities for talented and trained coding pros who can infiltrate servers and safeguard networks against digital threats, demand for intrepid cyber warriors is through the roof, and it shows no signs of slowing down any time soon.

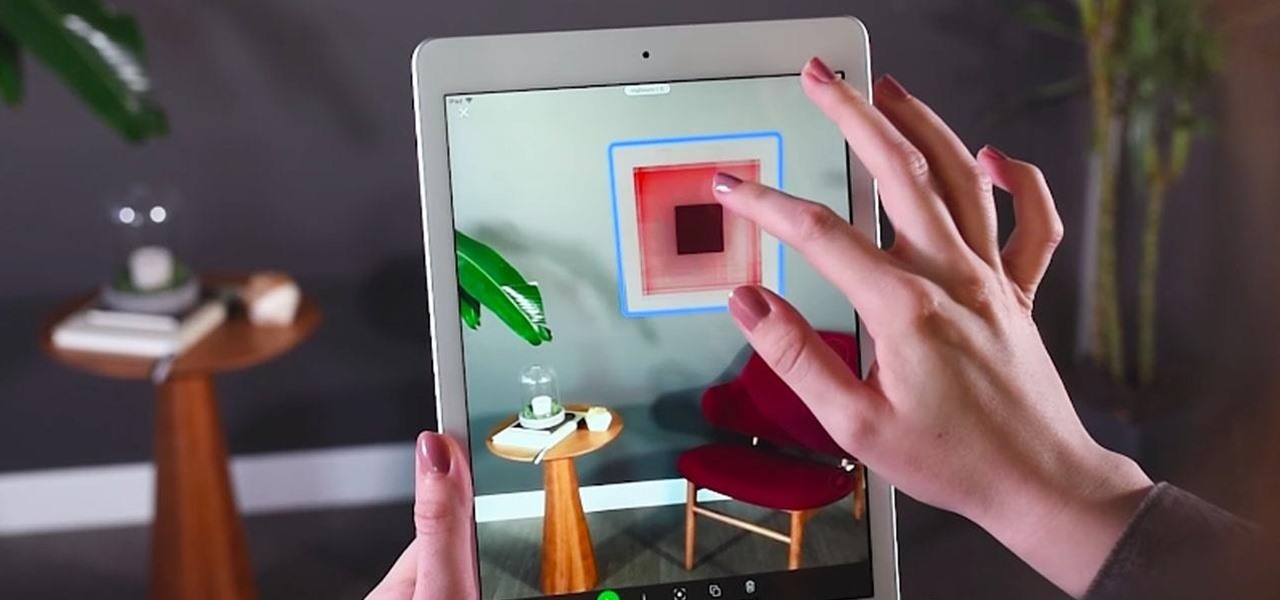
Apps that can display virtual furniture in the home are one of the most popular applications of mobile AR today, but Houzz has decided to raise the stakes with its latest update.

It looks like Chris Urmson has spent the six months since he left Google's Self Driving Car Project trying to build a get-rich-quick self-driving unicorn, along with Sterling Anderson, formerly with Tesla Motors. At least that is one of several scandalous accusations in a Tesla lawsuit aimed at the pair, and their secretive startup Aurora Innovation, LLC.