EDGAR is a massive database of financial documents and filings maintained by the SEC. If you want to use EDGAR to research financial institutions, it's pretty easy to do with an FTP client. Watch this video to learn how you can download and use FTP software to access EDGAR.

In this video tutorial, Chris Pels will show how to share data in between JavaScript and server-side code by using a hidden field in an ASP.NET page. Next, learn how to use the RegisterHiddenField method in server-side code to programmatically create a hidden field on the client. In addition, see how to programmatically create a HiddenField server control for sharing data on an ASP.NET page. Finally, use the RegisterArrayDeclaration method to create a container in server code for storing mult...

Not every client or coworker likes to mine through a spreadsheet to find all the important data. So, with Excel 2008 for Mac, you can easily share that data without sending the entire Excel spreadsheet. To do this, all you need to do is to use the "copy as picture" option. The Microsoft Office for Mac team shows you just how to insert a spreadsheet snippet in this how-to video.

Austin Chau does a short tutorial about how to use the JavaScript Client Library with the Google Calendar Data API.

Some data can be very confidential. In such case you need to encrypt the data so that it does not go into the wrong hands. There are lots of encryption software available to encrypt the data. But to use them first you need to install then and this can take lot of time. You can also use Windows built in compression client to encrypt information. To use this feature you need not install any software and it is a fairly simple process. So select a file that you want to encrypt, right click on it ...

A torrent is a small file (usually less than 100 KB in size), which contains file details, URL details and other data, that enables peer-to-peer download using a torrent client.

NOTICE: Ciuffy will be answering questions related to my articles on my behalf as I am very busy. Hope You Have Fun !!!

Want to remotely connect to your iPhone or iPod Touch from your Mac OS X computer? With an SSH client, it's easy. So easy, in fact, that this 4-minute guide can present a complete overview of the process. For the specifics, and to get started transferring and manipulating data and applications on your iPhone & iPod from your primary computer, watch this free video guide.

How to Use Your Mac as a Server: Turn your Mac Mini into a server! Yes, that's right, with a little know-how and a little spunk, you can turn an inexpensive Mac Mini computer into a server to provide services over you network. You won't even need the Mac OS X Server, just the Mac OS X Client, so there is no extra software to buy, just the Mac Mini and it's operating system.

Last weekend, some unlucky Gmail users inadvertently had their email accounts wiped out. Actually, it was 0.02 percent of all Gmail users—or roughly 40,000 of the 200 million who use the email service, due to an "unexpected bug" which affected copies of the data. Gmail does make backup files of everything, so eventually everyone will reclaim their email history. In fact, as of yesterday, Google has successfully restored all information from their backup tapes and has started returning everyon...
Hello Strangers, This is my first article for null-byte and its about staying anonymous on the Internet. But the question is why would you want to stay anonymous online?

Welcome back everyone! It's been awhile hasn't it? Sorry for being so quiet, but my CCNA courses have really picked up recently. In the last article we covered how to import modules and how we can use them. In this article, we'll actually be covering a module that is essential to the hacking aspect of Python, sockets.

Welcome back, my budding hackers! We've spent a lot of time learning to compromise Windows systems, and we've successfully compromised them with Metasploit, cracked their passwords, and hacked their Wi-Fi. However, very little time was spent developing ways to extract the information from the system once inside.
Hello, I'm a new guy around here and since I'm not seeing much tutorials in C i thought of contributing with something relatively simple. This will be a short series.

Proxies can be quicker to use than a VPN for specific applications, like web browsers or torrent clients. Both services will hide your true IP address, but a VPN is slowed down because it encrypts all data through a VPN network, while a proxy just acts as a middleman for fetching and returning requests from a server on your behalf. When speed is needed, go proxy.

This is a short explanation and tutorial on how to grab saved passwords from Google Chrome, ideally from a meterpreter session. The idea behind this is to understand how saved passwords work and how to keep them safe. Let's have some fun :D Understanding Google Chrome Saved Passwords

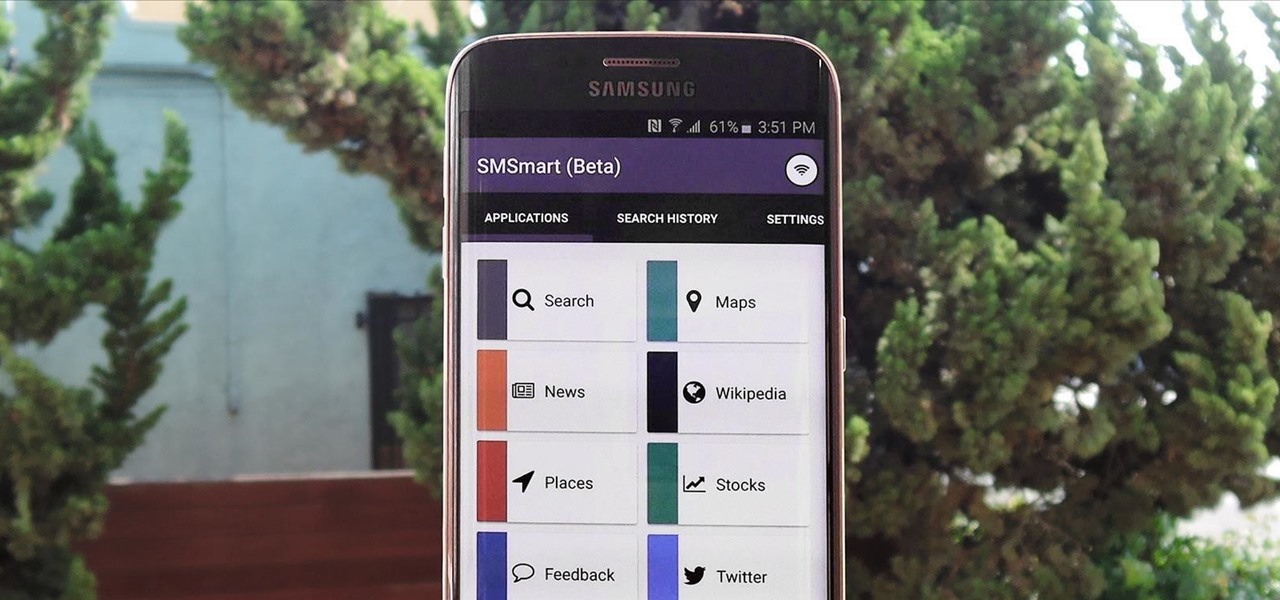
Recently, a group of Duke University students got together to tackle an age-old problem with mobile devices. You see, mobile data coverage isn't exactly ubiquitous, and many folks have restrictive mobile data plans, which means internet connectivity is not always an option.

Get a crash course on HScript Expressions, Variables, and Attributes in Houdini 10. If you don't even know what this means, then you probably need to check this video tutorial series out. Understanding how to massage data in Houdini is key to giving yourself the creative edge and allowing you to unleash mind-blowing visual effects. This 18-part video series covers a variety of simple yet essential weapons in your arsenal including Global, Standard and Custom Variables to Math and String Modif...

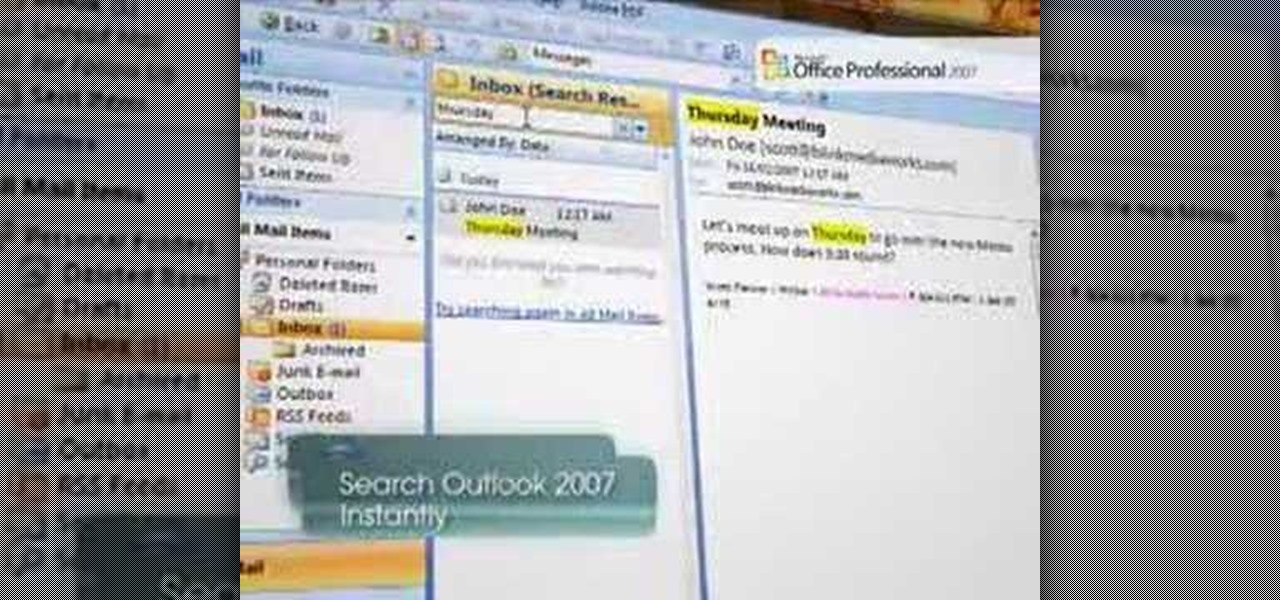
Microsoft Windows Vista Tips - Finding Information with Instant Search in Microsoft Office Outlook 2007 - Somewhere in the hundreds, or perhaps thousands of messages in your Microsoft Office Outlook 2003 mailbox is the one that has the information you need about that client meeting on Thursday. So how do you find it without reading through every one of your messages? The new Instant Search feature in Microsoft Office Outlook 2007 allows you to find the information you need instantly. For more...

Hak5 isn't your ordinary tech show. It's hacking in the old-school sense, covering everything from network security, open source and forensics, to DIY modding and the homebrew scene. Damn the warranties, it's time to Trust your Technolust. In this episode, see how to hide secret data inside a photo.

In a race to make self-driven cars mainstream, Intel announced today that they've bought Israeli microchip technology company Mobileye for $15.3 billion, setting the stage for Intel to dominate a large portion of the driverless market.

Torrents are a wonderful technology to share your files over the internet. If the data that you are sharing is confidential you may need to encrypt these files before sharing. To encrypt torrents in Azereus, go to tools and select options. From the left hand side menu select the connection option. Select the 'Transport Encryption' option from the connection sub menu. This section is intended for intermediate mode or higher and it is not available in beginner mode. So go to mode and select the...

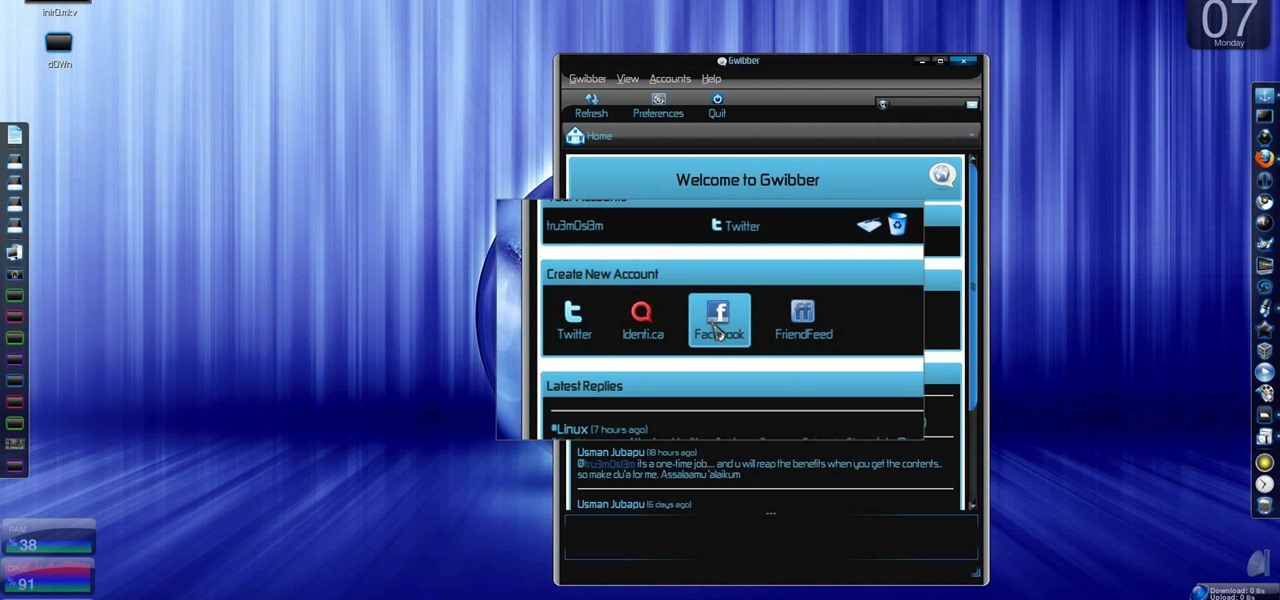
Twitter has consumed the world, so make sure you're up to date on your Tweets. One way to do that is with Gwibber 2.0 on Ubuntu Linux, the computer operating system that could be a bit tricky for beginners, but fret not, help is here. Check out this video tutorial on how to retrieve unlimited tweets with Gwibber 2.0 on Ubuntu Linux.

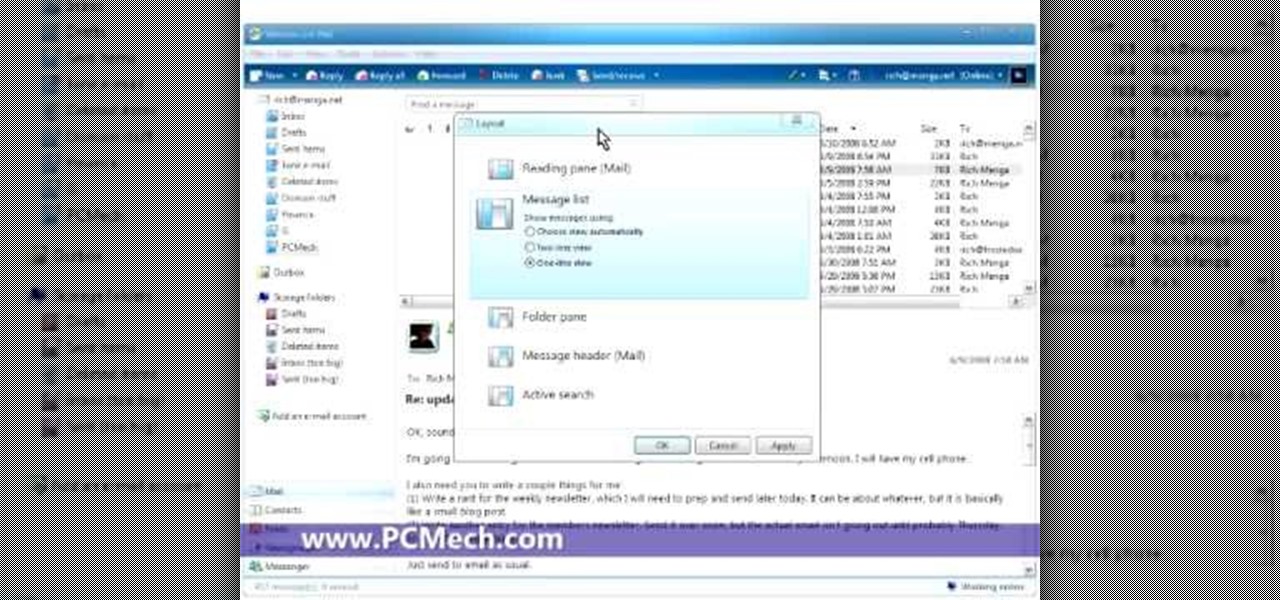
In this five-part video tutorial series from PCMech.com, you'll learn how to use the Windows Live Mail client. Learn, for example, how to set up your client with POP, IMAP, Gmail and, of course, Windows Live accounts like MSN and Hotmail. Take a look!

Twitter's official iOS app is adequate if you're not much of a tweeter, but if you are, there's a lot of useful features that are missing. Luckily, there are plenty of free Twitter clients available that you can use on your iPhone. These third-party apps have features such as customizable interfaces, post scheduling, and different browser options for opening links, to name just a few.

Recently, I've been learning Ruby as a second scripting language. But one topic I never covered with the many lessons online were sockets. So I did some research and came up with a very simple client/server connection that sends a string over the socket.

In this video tutorial, viewers learn how to create drop down menus in Microsoft Excel. This task is very easy, fast and easy to do. Begin by highlighting a desired cell. Then click on the Data tab and click on Data Validation under Data Tools. When the Data Validates window opens, click on the Error tab and deselect "Show error alert after invalid data is entered". Then click on OK. Now simply type in the data into the selected cell. This video will benefit those viewers who use Microsoft Ex...

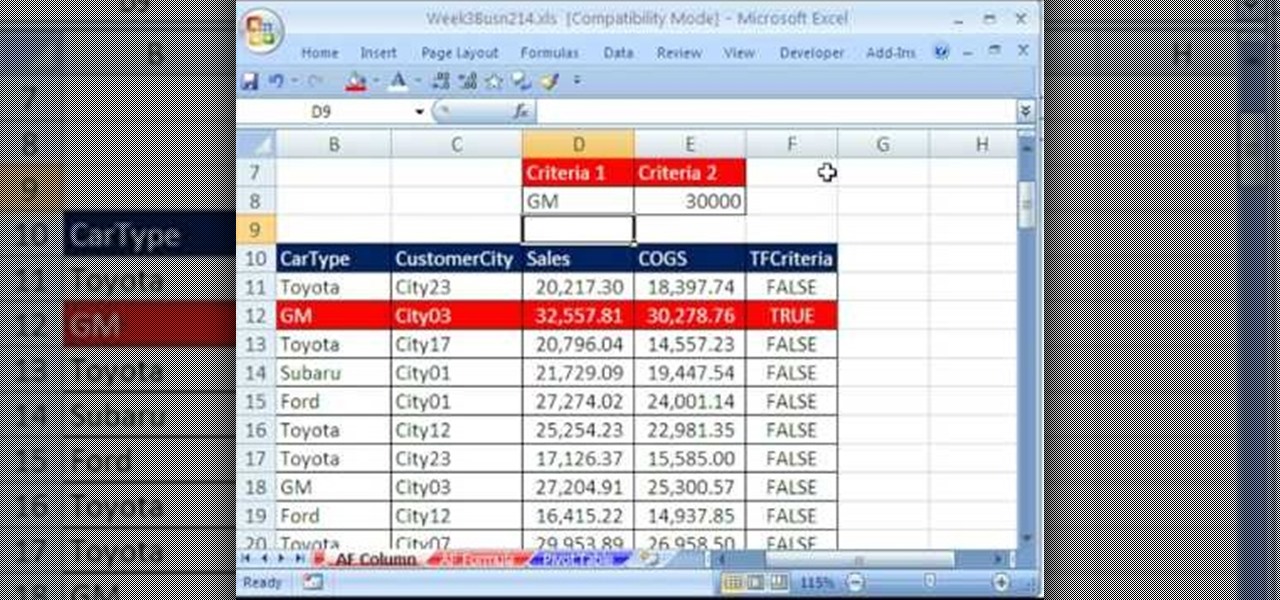
Whether you're interested in learning Microsoft Excel from the bottom up or just looking to pick up a few tips and tricks, you're in the right place. In this tutorial from everyone's favorite digital spreadsheet guru, ExcelIsFun, the 19th installment in his "Highline Excel Class" series of free video Excel lessons, you'll learn about using Advanced Filter to extract data from an Excel List/Table/Database. See these 7 Advanced Filter examples:

Adding clients to your network is a quick and easy process in Mac OS X Leopard Server. In this video tutorial, you'll find step-by-step walkthrough for the client adding process. For more, or to get started adding clients to your own Leopard Server, watch this video tutorial.

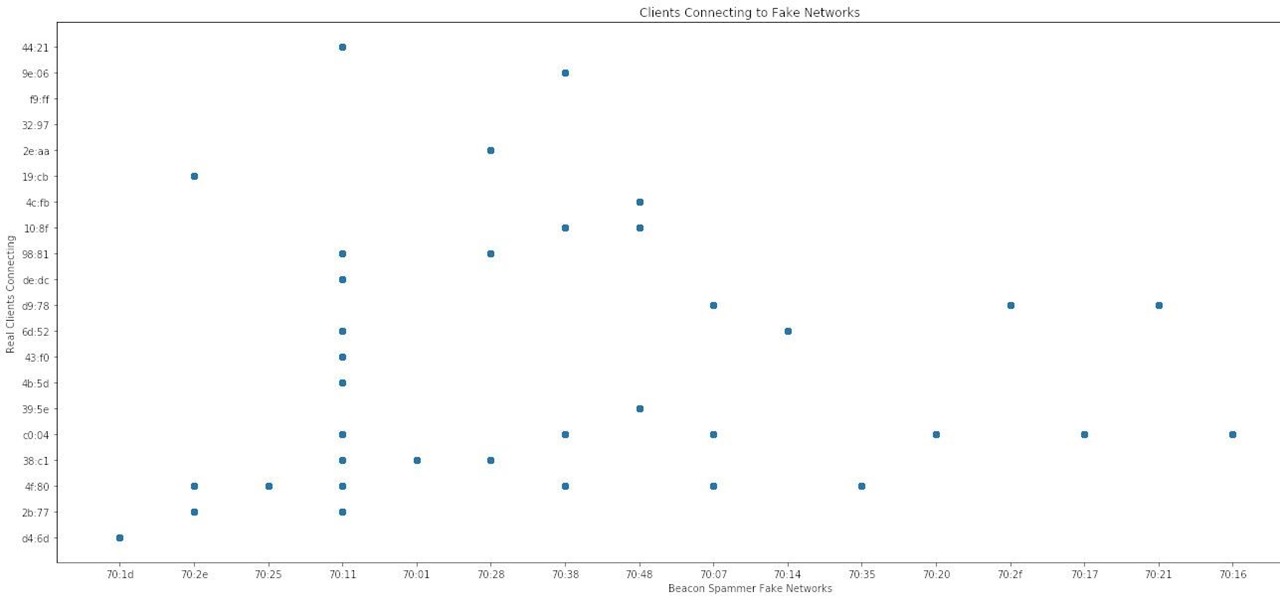
After finding and monitoring nearby wireless access points and devices connected to them, hackers can use this information to bypass some types of security, like the kind used for Wi-Fi hotspots in coffee shops, hotels, and in flights high above the ground. By swapping their MAC address for that of someone already connected, a hacker can bypass the MAC filter and connect freely.

Snapchat is attempting to take over the world via augmented reality technology. Well, it's more of a virtual makeover than a takeover, but still ...

This five-part series on C# programming covers many things. First, you learn how to save to the Microsoft SQL Server. Then, you'll learn how to retrieve that data. You'll also learn how to navigate the DataSet, edit SQL data, and delete data. If you have Microsoft Visual Studio and SQL Server, give this lesson a try.

Core Data is a powerful data-management framework introduced with Mac OS X v10.4 Tiger. When you take advantage of Core Data, it slashes the amount of custom code you need to write in order to manage application data. Opening, saving and undo management can all be handled by Core Data, freeing you to concentrate on creating unique features for your application. This video tutorial, which presents a general introduction to using Core Data, will walk you through the process of building a simple...

Even Halo: Reach on the Xbox 360 has hidden collectable items! All in the convenient (for the people hiding them) size of a small data pad! Earlier you got access to the first 9 data pads that you can get on any difficulty. Next, you will get a look on the next 9 data pads that you can only acquire while being on Legendary difficulty!

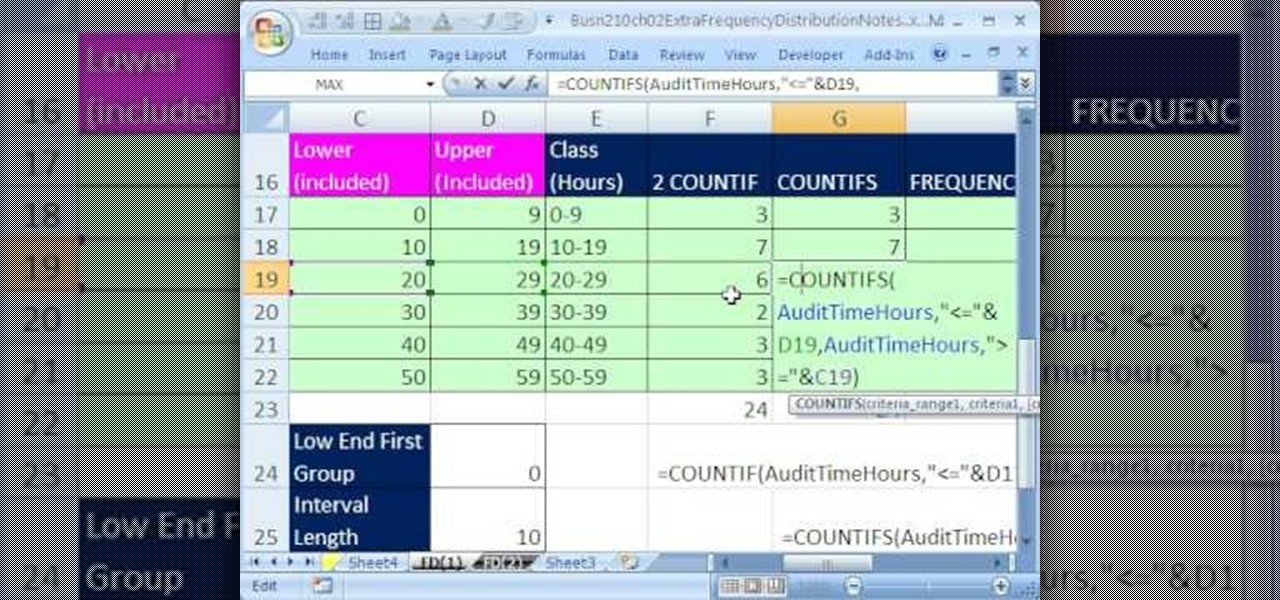
If you use Microsoft Excel on a regular basis, odds are you work with numbers. Put those numbers to work. Statistical analysis allows you to find patterns, trends and probabilities within your data. In this MS Excel tutorial from everyone's favorite Excel guru, YouTube's ExcelsFun, the 32nd installment in his "Excel Statistics" series of free video lessons, you'll learn how to group when the quantitative data are whole numbers, integers or discrete data and how to group when the quantitative ...

New to Microsoft Excel? Looking for a tip? How about a tip so mind-blowingly useful as to qualify as a magic trick? You're in luck. In this MS Excel tutorial from ExcelIsFun, the 255th installment in their series of digital spreadsheet magic tricks, you'll learn how to create a two-variable data table in Excel for what-if analysis. See the PMT function and learn about the formula equivalent to a data table.

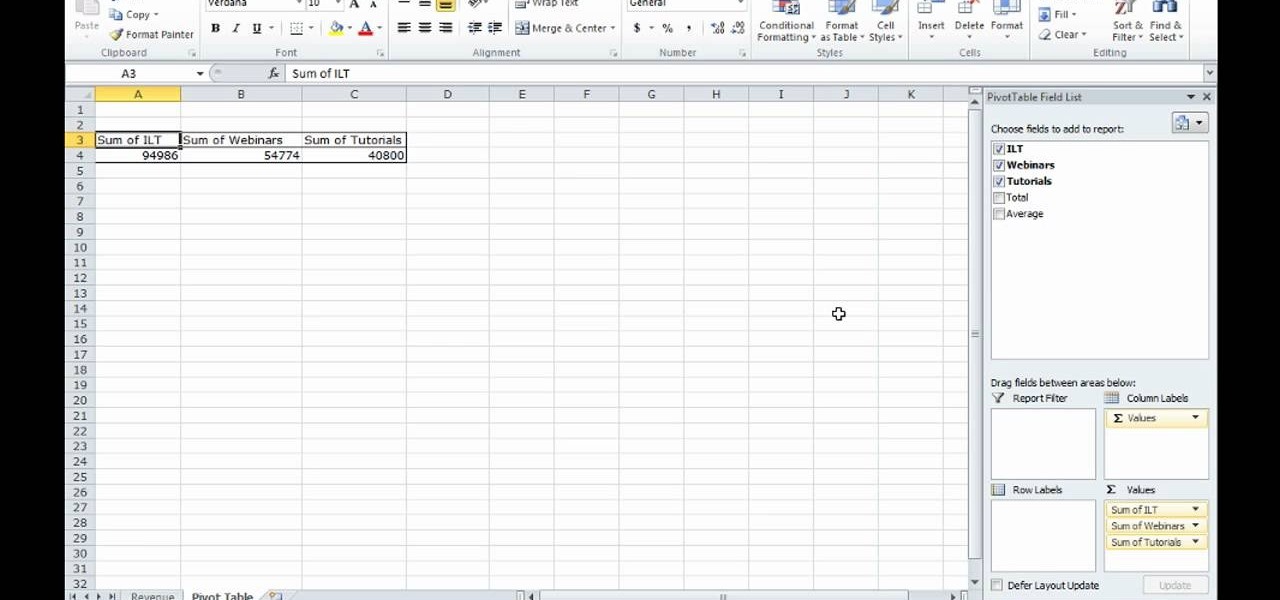
This video shows how to make a quick pivot table data filtering by using Excel 2010's ‘Slicer’ functionality. ‘Slicer’ delivers enhanced visual filtering method to allow you to get the data you need more quickly. When selecting a cell in the pivot table you will find ‘Slicer’ in the filter group of the ‘Insert’ tab. Click on ‘Slicer’ and an 'Insert Slicer' dialogue shows up where you can pick particular data fields from the slider list. Once you click on ‘OK’, the ‘Slicer’ objects with filter...

Data thieves don't have to be programming wizards to get their hands on your personal information. They often find hard drives that contain financial and other sensitive data at flea markets, charity shops, the city dump—even on eBay. In this video tutorial, PC World explains how to completely erase sensitive data from old drives before recycling or discarding them. Wipe your old hard drives with this how-to.

When it comes to sniffing Wi-Fi, Wireshark is cross-platform and capable of capturing vast amounts of data. Making sense of that data is another task entirely. That's where Jupyter Notebook comes in. It can help analyze Wi-Fi packets and determine which networks a particular phone has connected to before, giving us insight into the identity of the owner.

We're all aware that Google collects a notable portion of our data. Thanks to the increasing awareness, Google has added a number of privacy controls to limit data collection. But Google doesn't just collect personal data for no reason — many of your favorite apps will use this info to improve their services and add new features.